Search results for "USB"
-
 294Vulnerabilities
294VulnerabilitiesExperts can hack most CPUs since 2008 over USB by triggering Intel Management Engine flaw
Intel’s management engine – in most Positive Technologies plans to demonstrate at the next Black Hat conference how to hack over USB...
-

 145Vulnerabilities
145VulnerabilitiesLinux security: Google fuzzer finds ton of holes in kernel’s USB subsystem
A Google-developed kernel fuzzer has helped locate dozens of Linux security flaws. Google researcher Andrey Konovalov has revealed 14 flaws in Linux...
-
 309Vulnerabilities
309VulnerabilitiesMultiple Denial of Service Vulnerabilities Discovered in Linux kernel USB Subsystem
Multiple vulnerabilities found in Linux USB drivers that included with Linux kernel USB subsystem. It can be triggered by an attacker who...
-

 240Hacked
240HackedLinux Security Alert: Tons Of Linux Kernel USB Flaws Found By Google Hacker
The general perception of the public is that Linux and macOS operating systems are far more secure as compared to Windows. While...
-

 291Data Security
291Data SecurityUSB Stick with Heathrow Security and Queen’ Data Found on London Street
According to reports from the Sunday Mirror, a USB device was found lying on the street in West London having sensitive data...
-

 106Hackers Repository
106Hackers RepositoryKeyGrabber – Hardware Keylogger – WiFi USB hardware keyloggers
KeyGrabber products are hardware keyloggers. KeyGrabber keystroke recorder has up to 2GB of memory, stored on a FAT file system. The device...
-

 99Hackers Repository
99Hackers RepositoryKeyGrabber – Hardware Keylogger – WiFi USB hardware keyloggers
KeyGrabber products are hardware keyloggers. KeyGrabber keystroke recorder has up to 2GB of memory, stored on a FAT file system. The device...
-

 232Hacked
232HackedYour “Innocent” USB Port Could Be Leaking Personal Data To Hackers
Short Bytes: The USB ports on your laptop or desktop computer can be used to steal your sensitive information. According to a...
-

 323News
323NewsCrosstalk Flaw: Hackers can steal sensitive data with unsecure USBs
University of Adelaide School of Computer Science’ research team led by Dr. Yuval Yarom has identified that about 90% of external USB...
-

 321Hacked
321HackedBrutal Kangaroo: How CIA Hacked Offline Computers Using Infected USB Drives
Short Bytes: Brutal Kangaroo malware is the latest addition to the ongoing WikiLeaks Vault 7 leaks. Published earlier this week, the leaked...
-
 329Malware
329MalwareCIA Hacking Tool “Brutal Kangaroo” Revealed to Hack Air-Gapped Networks by using USB Thumb Drives -WikiLeaks
Wikileaks Revealed Next CIA Hacking Tool called “Brutal Kangaroo” under Vault 7 Projects that Consists of 4 Powerful Malware Components which targets...
-

 232Data Security
232Data SecurityVault 7: CIA Has Malware for Hacking Air-Gapped Networks via USB Thumb Drives
WikiLeaks dumped today the manuals of several hacking utilities part of Brutal Kangaroo, a CIA malware toolkit for hacking into air-gapped (offline)...
-

 271Hackers Repository
271Hackers RepositorySEToolkit – Hacking Windows Machines Using USB/CD Infectious Media Generator
SEToolkit – Hacking Windows Machines Infectious Media Generator Requirements Linux based Operating System (In this tutorial we are using Kali Linux) SEToolkit...
-

 209Vulnerabilities
209VulnerabilitiesYou Can Hack Some Mazda Cars with a USB Flash Drive
EXCLUSIVE — Mazda cars with next-gen Mazda MZD Connect infotainment systems can be hacked just by plugging in a USB flash drive...
-
 596How To
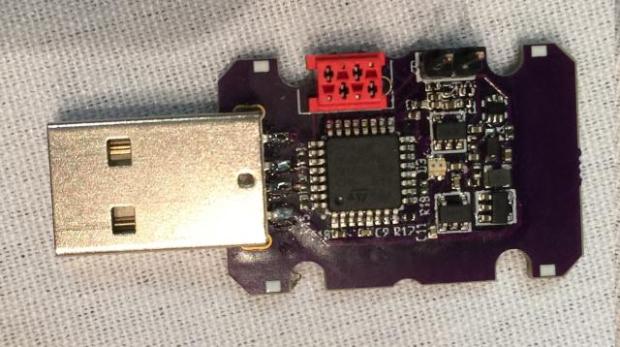
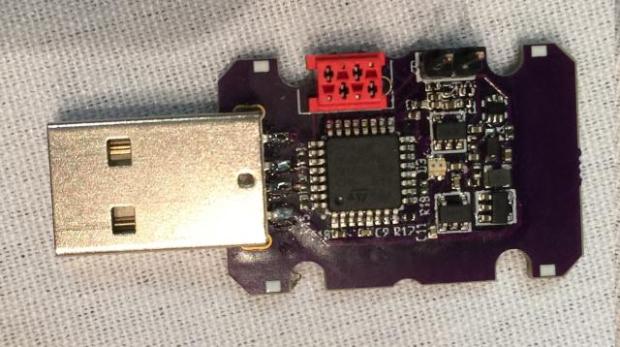
596How ToWhat Is USB Rubber Ducky and How Does It Works?
With regard to simplicity, injections and key injections are ideal. With the tools available in today’s market of cyber security execution a...
-

 312News
312NewsMazda cars hacked with just a USB
It seems that Mazda car owners have discovered a hack that allows them to tweak the Mazda’s MZD Connect infotainment system by...
-

 167Malware
167MalwareIBM Warns Customers That Some of Its USB Flash Drives May Contain Malware
IBM has issued a security alert last week, warning customers that some USB flash drives shipped with IBM Storwize products may contain...
-

 371Data Security
371Data SecurityIBM Sent Off USB Sticks Infected with Malware
A new warning has been issued by IBM and the situation seems to be rather serious. According to the firm, there are...
-

 205Hacked
205HackedUSB Canary: This Open Source Tool Sends SMS If A Hacker Connects A USB Device
Short Bytes: USB Canary is an open source tool that monitors for any suspicious activity on a computer. Written in Python language,...
-

 115How To
115How ToHow To Hack Passwords Using A USB Drive – USB Drive Hacks
As we all realize, home windows stores maximum of the passwords which are used on an each day foundation, together with instantaneous...
-
 237Vulnerabilities
237VulnerabilitiesUSB Killer now lets you fry most Lightning and USB-C devices for $55
Plus a new, stealthy “anonymous” stick, because that’s what the world really needed. Remember the USB Killer stick that indiscriminately and immediately...