Search results for "USB"
-

 290Hacked
290HackedUSBHarpoon: How “Innocent” USB Cables Can Be Manipulated To Inject Malware
A researcher from SYON Security has managed to build a modified USB charging cable that will enable hackers to transfer malware on...
-

 382Geek
382GeekHow To Enter BIOS Utility (UEFI Settings) On All PCs And Boot From USB?
Let’s get real. For at least once in our life, we have all gone through the hassle of searching around the web...
-
 299Geek
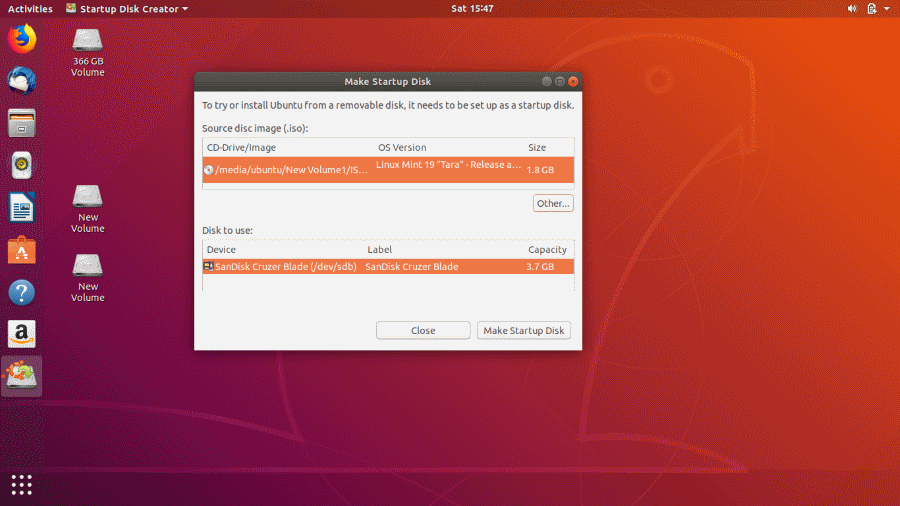
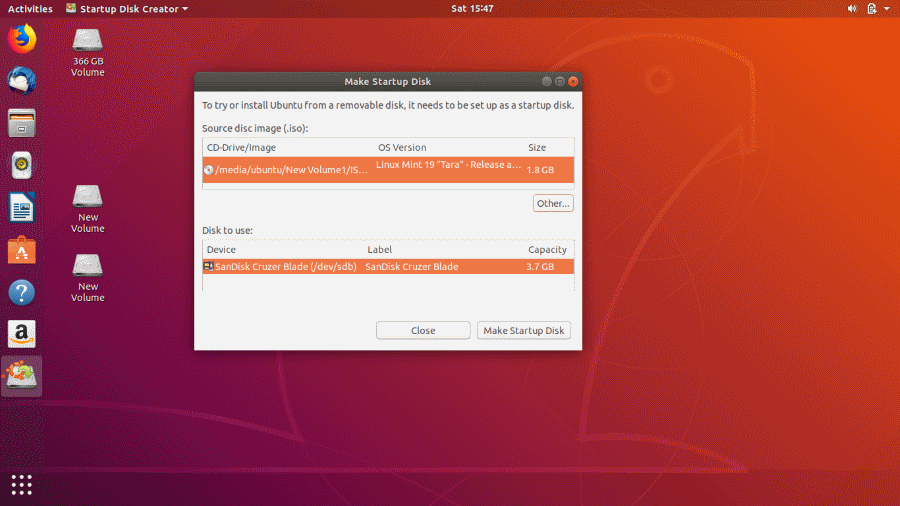
299Geek3 Easy Ways To Create Bootable USB Media From ISO In Ubuntu Linux
We have already given the complete guide for using Rufus to create bootable USB media. Interestingly, RUFUS application only supports Windows and...
-

 390How To
390How ToHow To Use The New USB Restricted Mode In iPhone? (It’s Not Foolproof!)
Apple devices have amassed a reputation for being safe and tough for hackers to hack. With the help of the passcode, TouchID...
-
 469Geek
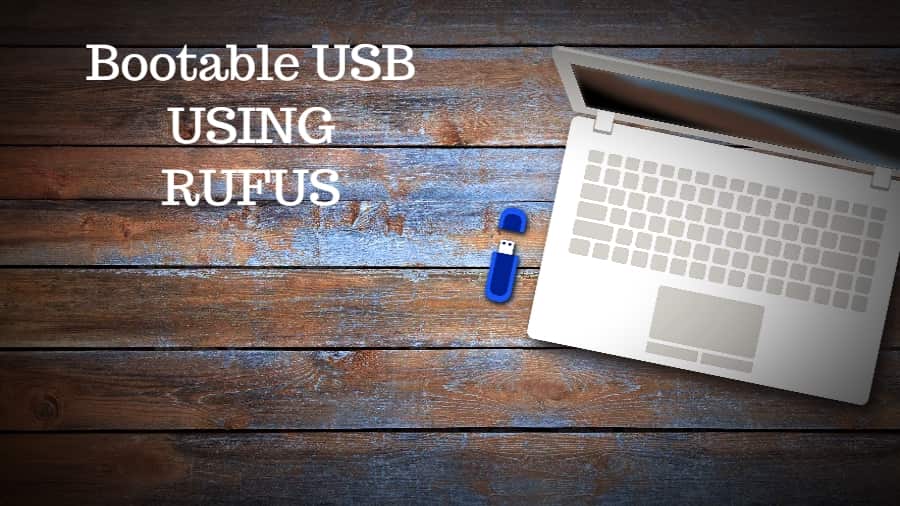
469GeekHow To Create A Bootable USB Media Using Rufus For Installing Linux/Windows
USB Drives are the most convenient go-to devices nowadays when the need to prepare a Bootable media arises. For a reason being...
-

 514How To
514How ToHow To Create Bootable USB Without Any Software In Windows 10 (Using Command Prompt)
These days very few people who burn ISO images on disks and use them as bootable media. Now, USB drives have replaced...
-

 430Data Security
430Data SecurityHow a USB could become security risk for your device
A flash drive or USB may provide a capacity as large as 2TB or could have a small space of 256 MB...
-

 190Hacked
190HackedHackers May Have Already Defeated Apple’s USB Restricted Mode For iPhone
It seems that the cat and mouse chase between Apple and people who want to get access to iPhone is never going...
-

 171Incidents
171IncidentsTrump and Kim USB fan lauches information security alert
Information security experts express surprise at the fact that journalists covering the meeting between US President Donald Trump and North Korean leader...
-
 356How To
356How ToHow To Speed Up Windows Using ReadyBoost And USB Drive? Does It Still Work?
Microsoft first introduced the functionality to use a USB drive or SD card as a memory cache in Windows Vista in the...
-

 333Data Security
333Data SecurityIBM improves its security and prohibits the use of USB drives throughout the company
IBM recently banned all removable storage, throughout the company; this is a new policy that aims to avoid financial and reputational damage...
-
 281Hacked
281HackedThis Code On USB Can Trigger BSOD Even On Locked Windows PCs
In the past, we’ve told you about the perils of picking any random USB drive and using it. It might contain malware...
-
 424How To
424How ToHow To Put Multiple ISO Files In One Bootable USB Disk | Create Multiboot USB Disk
Creating a bootable USB disk comes handy when we have to reinstall our operating system in the case of a system failure....
-

 233Data Security
233Data SecurityThe state of USB data protection
Data protection, whether related to personal customer or patient information, is critical across virtually all industries. A survey made by information security trainingresearchers...
-
 406Shop
406ShopThetis FIDO U2F Security key – Universal Two Factor Authentication USB
FIDO U2F Security key is a personal encryption method which individualizes your online security by providing a secondary layer of encryption via...
-
 303Computer Forensics
303Computer Forensicsusbkill – An Anti-Forensic Kill Switch
usbkill is an anti-forensic kill-switch that waits for a change on your USB ports and then immediately shuts down your computer. To run:...
-

 336Data Security
336Data SecurityPolice distributed malware infected USBs as cybersecurity quiz prizes
The Police are supposed to protect and serve but Taiwanese police in the news for distributing malware-infected USB sticks to the winners of a cybersecurity-related quiz during...
-

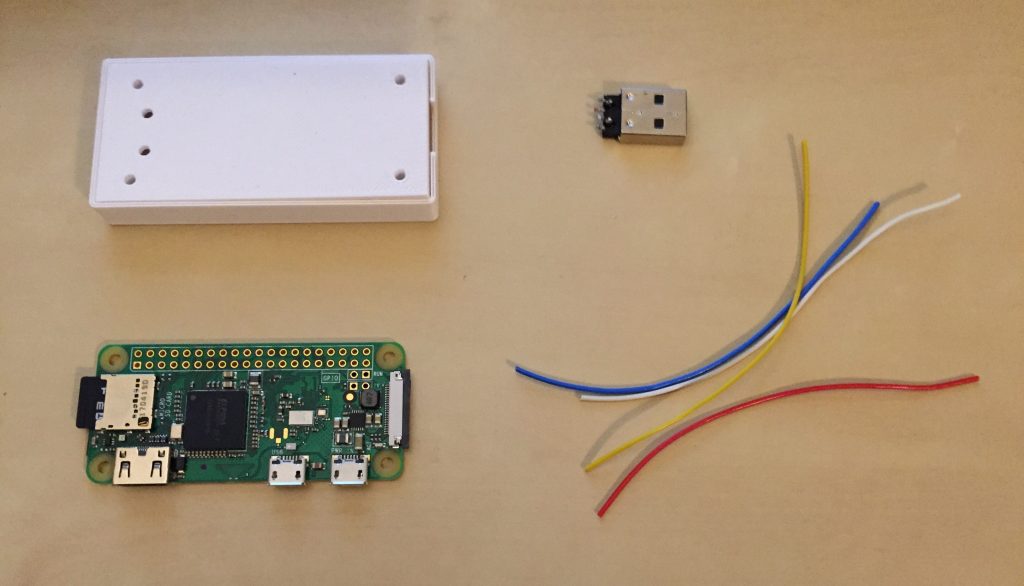
 257Hardware & Embedded
257Hardware & EmbeddedPoisonTap – Raspberry Pi Zero Malicious USB Attack
Exploits locked/password protected computers over USB, drops persistent WebSocket-based backdoor, exposes internal router, and siphons cookies using Raspberry Pi Zero & Node.js....
-
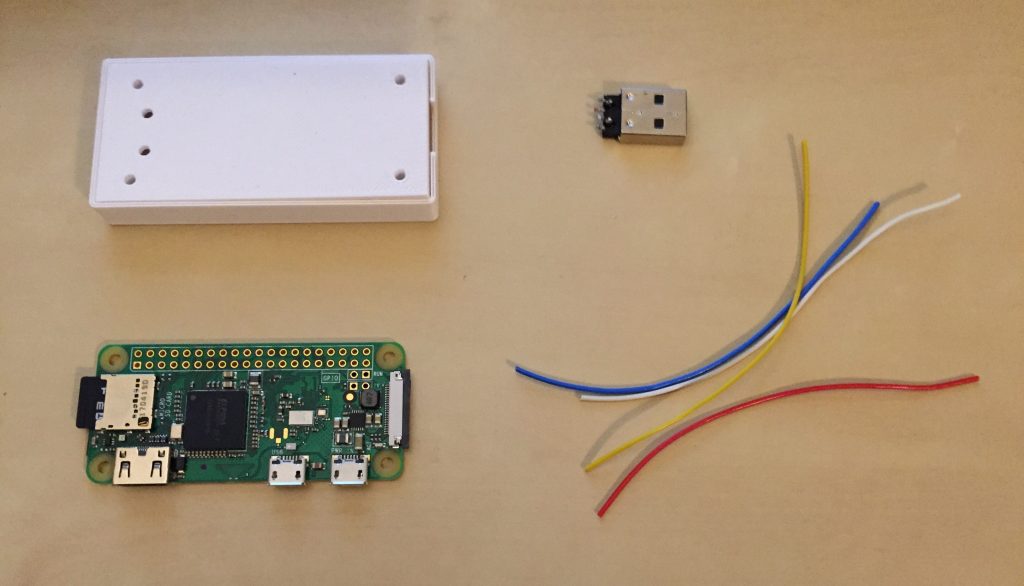 396Hardware & Embedded
396Hardware & EmbeddedP4wnP1 – Raspberry Pi USB Attack Platform
P4wnP1 is a highly customizable USB attack platform, based on a low cost Raspberry Pi Zero or Raspberry Pi Zero W (required...
-
 308Hacked
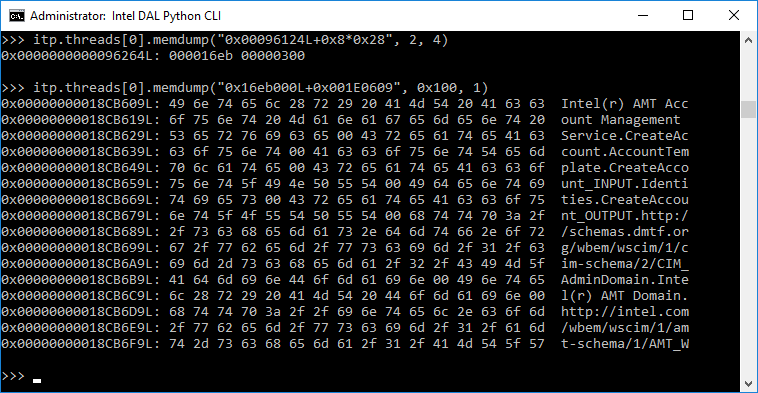
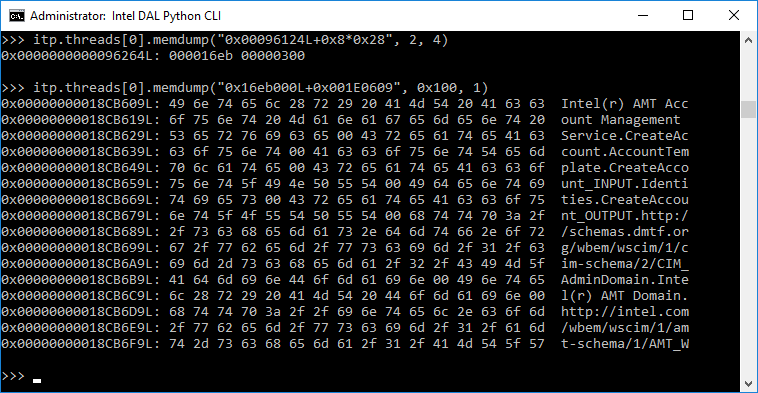
308Hacked“Game Over!” — Intel’s Hidden, MINIX-powered ME Chip Can Be Hacked Over USB
Even the creator of MINIX operating system didn’t know that his for-education operating system is on almost every Intel-powered computer. He is okay...
-
 315Data Security
315Data SecurityIntel’ Management Engine Tech Just Got Exposed Through USB Ports
Back in September 2017, Positive Technologies’ experts had expressed interest in the development of a technique that can attack the yet secretive...






