Search results for "apt"
-

 2.0KCyber Attack
2.0KCyber AttackU.S. Warns of APT Hackers Targeting ICS/SCADA Systems with Specialized Malware
The U.S. government on Wednesday warned of nation-state actors deploying specialized malware to maintain access to industrial control systems (ICS) and supervisory...
-
 4.0KMalware
4.0KMalwareMicrosoft Disrupted APT28 Domains Used by Russian Spies to Target Ukraine
In an attempt to eliminate the infrastructure used to launch attacks against Ukrainian targets, Microsoft has taken down seven domain names used...
-

 834Data Security
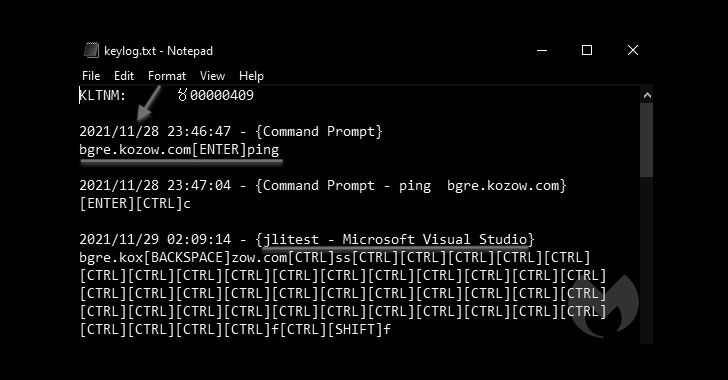
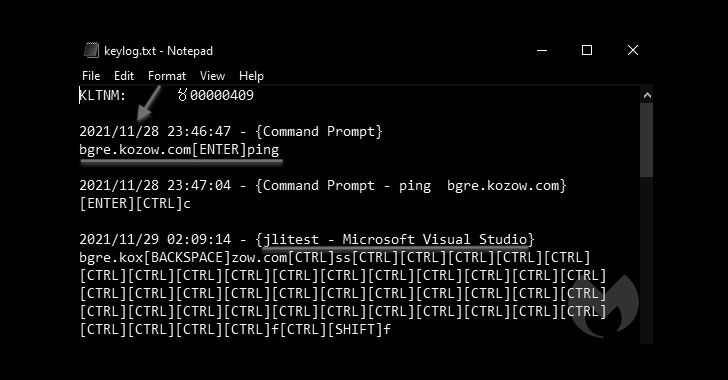
834Data SecurityHow this APT group is hacking Indian government officials to spy on their activities
Cisco Talos researchers reported detecting a new hacking campaign by the group identified as Transparent Tribe and targeting government organizations in India....
-

 4.6KVulnerabilities
4.6KVulnerabilitiesCritical vulnerabilities in Dell laptops’ UEFI allow them to be hacked forever, even when removing the hard drive
Researchers from firmware security firm Binarly confirmed the detection of some critical flaws in the Unified Extensible Firmware Interface (UEFI) of multiple...
-

 821Malware
821MalwareRussian Ransomware Gang Retool Custom Hacking Tools of Other APT Groups
A Russian-speaking ransomware outfit likely targeted an unnamed entity in the gambling and gaming sector in Europe and Central America by repurposing...
-

 2.0KMalware
2.0KMalwareResearchers Find New Evidence Linking Kwampirs Malware to Shamoon APT Hackers
New findings released last week showcase the overlapping source code and techniques between the operators of Shamoon and Kwampirs, indicating that they...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesMillions of HP laptops, points of sale machines and servers affected by 16 critical vulnerabilities
A report by cybersecurity firm Binarly points to the detection of 16 critical vulnerabilities in various implementations of Unified Extensible Firmware Interface...
-

 2.3KMalware
2.3KMalwareAPT group TA2541 has been targeting thousands of organizations across aviation, aerospace, transportation, manufacturing, and defense industries worldwide
A report by security firm Proofpoint details the finding of a hacking campaign employing phishing and social engineering tactics aimed at distributing...
-

 733Cyber Attack
733Cyber AttackRussian APT Hackers Used COVID-19 Lures to Target European Diplomats
The Russia-linked threat actor known as APT29 targeted European diplomatic missions and Ministries of Foreign Affairs as part of a series of...
-

 948Incidents
948IncidentsFox News, Wall Street Journal and New York Post employees hacked by Chinese APT group
News Corp, one of the world’s media agencies, has confirmed that its systems were compromised by what they defined as a “persistent...
-
 895Malware
895MalwareChinese APT Hackers Deploys MoonBounce Implant In UEFI Firmware
Kaspersky Lab experts have recently discovered a security vulnerability in UEFI firmware, and this vulnerability was detected while studying the Firmware Scanner...
-

 1.9KData Security
1.9KData SecurityBlueNoroff APT that hacked Bangladesh Bank is now only focusing on hacking cryptocurrency businesses and exchanges
For almost five years, SecureList researchers reported the identification of an Advanced Persistent Threat (APT) group apparently linked to the infamous Lazarus...
-
 3.6KMalware
3.6KMalwareBADNEWS! Patchwork APT Hackers Score Own Goal in Recent Malware Attacks
Threat hunters have shed light on the tactics, techniques, and procedures embraced by an Indian-origin hacking group called Patchwork as part of...
-

 3.2KMalware
3.2KMalwareAPT Groups Register Domain Used for C&C Long Before The Attack To Prevent Detection
The APT groups are massively exploiting the long before registered domains for C&C to prevent detection. Exceedingly the higher numbers of malicious,...
-

 4.2KCyber Attack
4.2KCyber AttackChinese APT Hackers Used Log4Shell Exploit to Target Academic Institution
A never-before-seen China-based targeted intrusion adversary dubbed Aquatic Panda has been observed leveraging critical flaws in the Apache Log4j logging library as...
-
 4.6KVulnerabilities
4.6KVulnerabilitiesLenovo Laptop Flaws Let Attackers Gain Admin Privileges
Privilege elevation bugs have been detected recently by the security analysts at NCC Group in the ImControllerService service of Lenovo laptops including...
-

 3.6KData Security
3.6KData SecurityFBI issues flash alert after APT groups exploited VPN flaws
With this flaw, FatPipe joins the list of VPN providers that have faced a similar situation in the past, including Fortinet, Cisco,...
-

 4.8KMalware
4.8KMalwareAPT C-23 Hackers Using New Android Spyware Variant to Target Middle East Users
A threat actor known for striking targets in the Middle East has evolved its Android spyware yet again with enhanced capabilities that...
-

 4.7KMalware
4.7KMalwareMicrosoft Warns of Iranian Hacker Group That Rapidly Adapts New Tools & Techniques
At the CyberWarCon 2021 conference, the cybersecurity experts of Microsoft Threat Intelligence Center (MSTIC) has presented an analysis of the activities and...
-
 1.3KVulnerabilities
1.3KVulnerabilities3 critical BIOS vulnerabilities affect Intel microchips in laptops and IoT devices
Intel security teams announced the detection of two critical vulnerabilities in a wide variety of products and whose exploitation would allow threat...
-

 1.1KIncidents
1.1KIncidents7-Eleven stores capture images of their customers’ faces without their consent
The Office of the Australian Information Commissioner (OAIC) confirmed that convenience store chain 7-Eleven violated the privacy of thousands of customers by...






