Search results for "apt"
-

 4.8KVulnerabilities
4.8KVulnerabilitiesCritical privilege escalation vulnerability in ASUS laptops with ROG Armoury Crate app installed
A security report published by an Italian researcher notes that the abuse of a severe vulnerability in the ROG Armory Crate hardware...
-

 2.9KMalware
2.9KMalwareRussian Turla APT Group Deploying New Backdoor on Targeted Systems
State-sponsored hackers affiliated with Russia are behind a new series of intrusions using a previously undocumented implant to compromise systems in the...
-
 1.5KCyber Attack
1.5KCyber AttackA New APT Hacker Group Spying On Hotels and Governments Worldwide
A new advanced persistent threat (APT) has been behind a string of attacks against hotels across the world, along with governments, international...
-

 4.3KCyber Crime
4.3KCyber CrimeThreat actors using CAPTCHA to evade phishing, malware detection
According to researchers, cybercriminals are abusing legitimate challenge and response services like Google’s reCAPTCHA or deploying customized fake CAPTCHA-like validation. Palo Alto...
-

 3.4KMalware
3.4KMalwareFIN8 APT Hackers Attacks Financial Institutions Using Sophisticated Backdoor
The security analysts from the cybersecurity firm Bitdefender have recently noted the new backdoor BADHATCH malware that was being used by the...
-
 4.5KMalware
4.5KMalwareRussian APT29 Used 30+ C&C Servers Uncovered Linked to “WellMess” Malware
Researchers from RISKIQ uncovered more than 30 commands & control server infrastructure actively serving malware known as “WellMess/WellMail”. These C2 servers belong...
-

 1.0KCyber Attack
1.0KCyber AttackAPT Hackers Distributed Android Trojan via Syrian e-Government Portal
An advanced persistent threat (APT) actor has been tracked in a new campaign deploying Android malware via the Syrian e-Government Web Portal,...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesCVE-2021-3452 privilege escalation vulnerability affects BIOS of 60 Lenovo laptops and 2 desktop computer models
Lenovo security teams announced the detection of three vulnerabilities affecting the BIOS of approximately 60 models of laptops and notebooks. In its...
-
 1.0KMalware
1.0KMalwareWildPressure APT Hackers Uses New Malware to Attack Both Windows & macOS Operating Systems
WildPressure has been attacking Windows for a long time, that’s why this is not the first time when Windows and macOS operating...
-
 2.7KCyber Attack
2.7KCyber AttackWildPressure APT Emerges With New Malware Targeting Windows and macOS
A malicious campaign that has set its sights on industrial-related entities in the Middle East since 2019 has resurfaced with an upgraded...
-

 642Malware
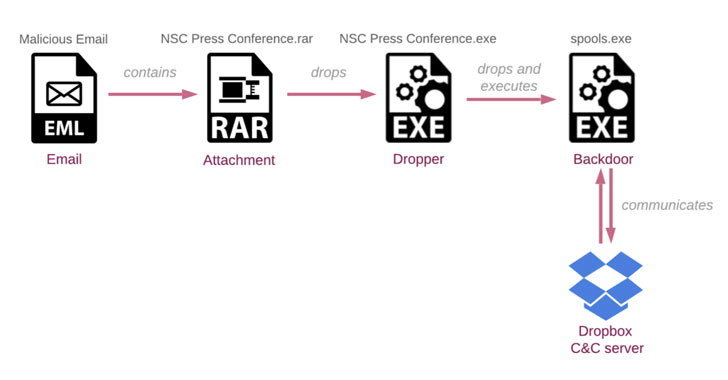
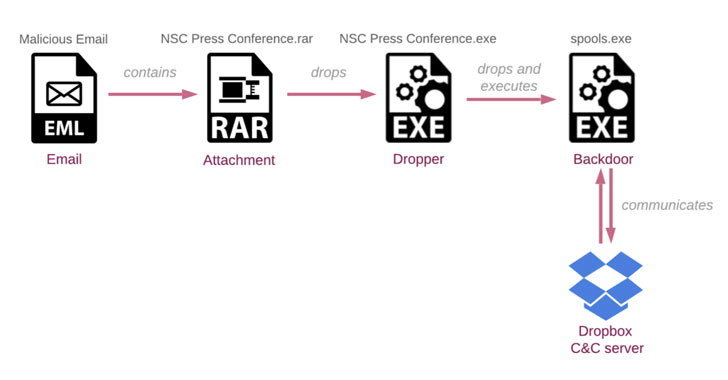
642MalwareIndigoZebra APT Group Uses Dropbox Service to Target Government Entities
During a routine investigation, the security analyst of Check Point research has identified a spear-phishing campaign. According to the experts, this campaign...
-

 3.0KMalware
3.0KMalwareRussian APT Hackers Launched A Mass Global Brute Force Attack to Hack Enterprise & Cloud Networks
Recently, in a joint warning, the cybersecurity agencies of the US and UK have released a set of large-scale brute-force attacks escorted...
-
 4.9KMalware
4.9KMalwareIndigoZebra APT Hacking Campaign Targets the Afghan Government
Cybersecurity researchers are warning of ongoing attacks coordinated by a suspected Chinese-speaking threat actor targeting the Afghanistan government as part of an...
-

 4.2KData Security
4.2KData SecurityVulnerabilities in Dell laptops’ software allow hackers to execute code remotely in millions of devices
Cybersecurity experts reported the detection of at least four flaws in Dell SupportAsist’s BIOSConnect feature, the exploitation of which would allow threat...
-
 4.8KMalware
4.8KMalwareBackdoorDiplomacy APT Group Attacks Telecommunications & Organizations Worldwide
The cybersecurity research team of ESET has recently identified a very new APT group named as BackdoorDiplomacy, attacking telecommunications and diplomatic organizations...
-

 4.2KMalware
4.2KMalwareChinese APT Group Leverage Microsoft Office Vulnerabilities To Attack Government Agencies
The cybersecurity researchers of the Check Point research team have recently detected that the threat actors of the Chines APT hacking group,...
-

 2.3KMalware
2.3KMalwareAPT Hacker Group FIN7 Uses A Pentesting Tool to Infect Windows Machines
In the recent era, cyber crimes are happening quite often, and this is not the first time that a cybercriminal group pretending...
-

 1.2KMalware
1.2KMalwareLazarus APT Hackers are now using BMP images to hide RAT malware
A spear-phishing attack operated by a North Korean threat actor targeting its southern counterpart has been found to conceal its malicious code...
-

 3.8KTutorials
3.8KTutorials50 CTF(CAPTURE THE FLAG) & PENTESTING WEBSITES TO PRACTICE YOUR HACKING & CYBERSECURITY SKILLS IN 2021
As with any other professional activity, in the world of ethical hacking practice makes perfect. Today there are thousands of ethical hackers...
-

 4.0KMalware
4.0KMalwareExchange servers under siege from at least 10 APT groups
ESET Research has found LuckyMouse, Tick, Winnti Group, and Calypso, among others, are likely using the recent Microsoft Exchange vulnerabilities to compromise...
-
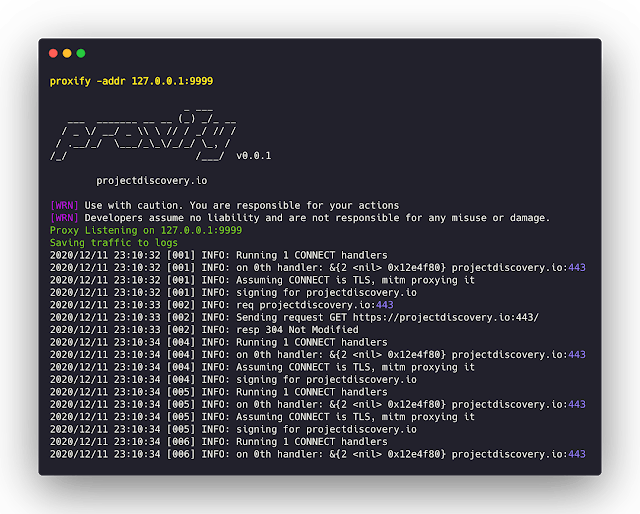
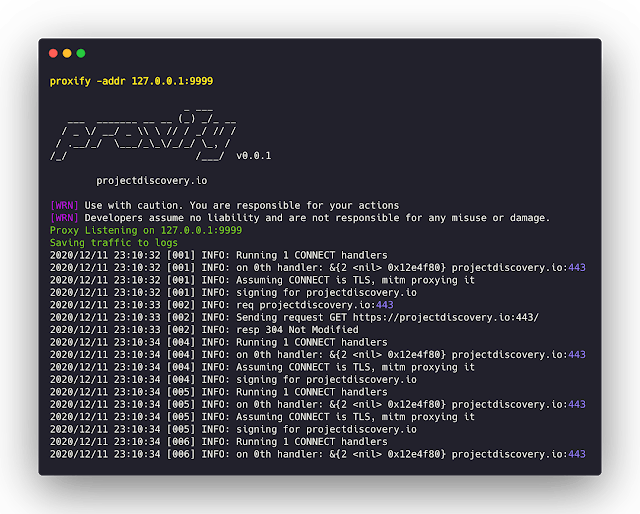 4.9KNetwork Tools
4.9KNetwork ToolsProxify – Swiss Army Knife Proxy Tool For HTTP/HTTPS Traffic Capture
Swiss Army Knife Proxy for rapid deployments. Supports multiple operations such as request/response dump, filtering and manipulation via DSL language, upstream...






