Featured News
-

 3.7KMalware
3.7KMalware‘eXotic Visit’ Spyware Campaign Targets Android Users in India and Pakistan
An active Android malware campaign dubbed eXotic Visit has been primarily targeting users in South Asia, particularly those in India and Pakistan,...
-

 4.3KMalware
4.3KMalwareRaspberry Robin Returns: New Malware Campaign Spreading Through WSF Files
Cybersecurity researchers have discovered a new Raspberry Robin campaign wave that propagates the malware through malicious Windows Script Files (WSFs) since March...
-
 4.9KMalware
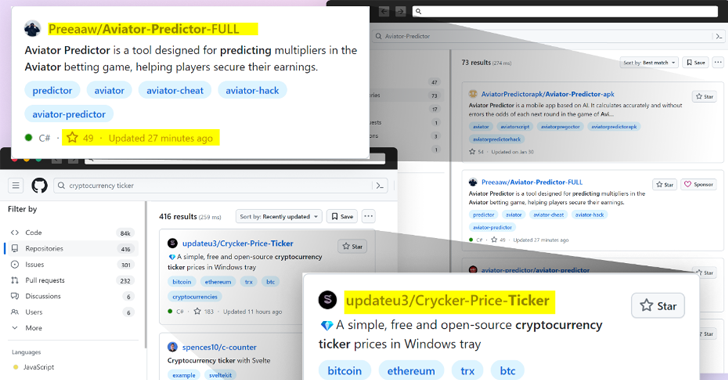
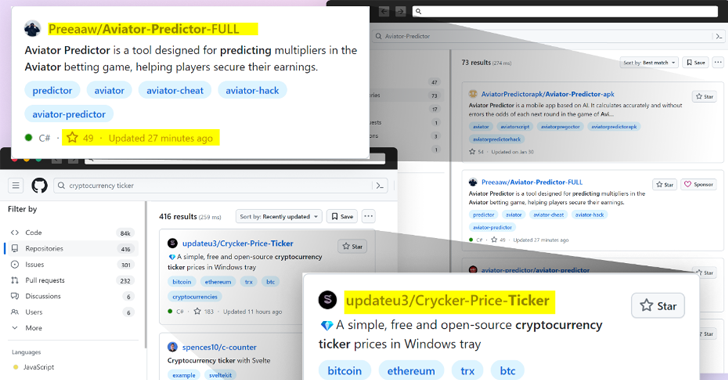
4.9KMalwareBeware: GitHub’s Fake Popularity Scam Tricking Developers into Downloading Malware
Threat actors are now taking advantage of GitHub’s search functionality to trick unsuspecting users looking for popular repositories into downloading spurious counterparts...
-
 670Vulnerabilities
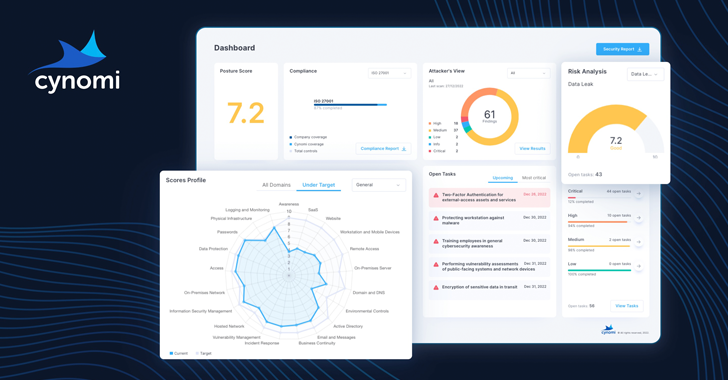
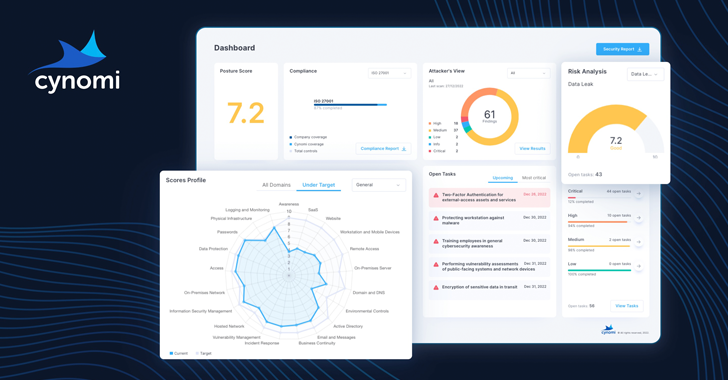
670VulnerabilitiesHands-on Review: Cynomi AI-powered vCISO Platform
The need for vCISO services is growing. SMBs and SMEs are dealing with more third-party risks, tightening regulatory demands and stringent cyber...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
We all know passwords and firewalls are important, but what about the invisible threats lurking beneath the surface of your systems? Identity...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesMicrosoft Fixes 149 Flaws in Huge April Patch Release, Zero-Days Included
Microsoft has released security updates for the month of April 2024 to remediate a record 149 flaws, two of which have come...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesCritical ‘BatBadBut’ Rust Vulnerability Exposes Windows Systems to Attacks
A critical security flaw in the Rust standard library could be exploited to target Windows users and stage command injection attacks. The...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesHow to hack a LG Smart TV via vulnerabilities in LG WebOS?
In a recent disclosure, cybersecurity firm Bitdefender has revealed a series of critical vulnerabilities within LG’s WebOS, the operating system used in...
-
 3.4KVulnerabilities
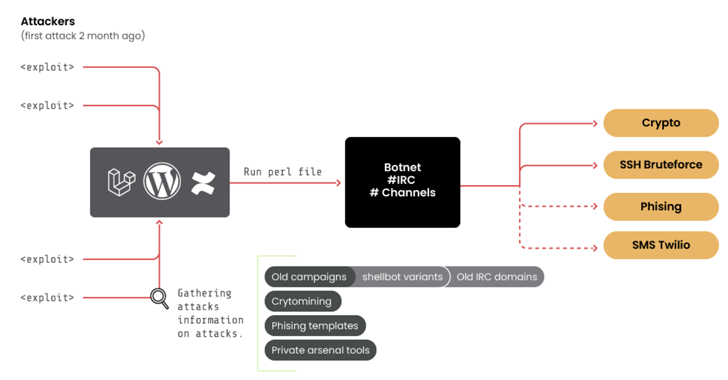
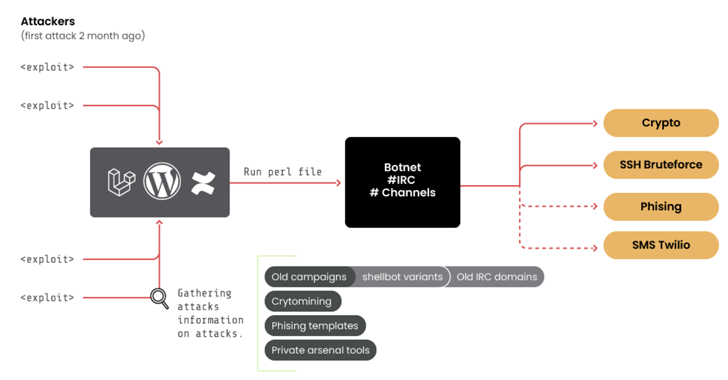
3.4KVulnerabilities10-Year-Old ‘RUBYCARP’ Romanian Hacker Group Surfaces with Botnet
A threat group of suspected Romanian origin called RUBYCARP has been observed maintaining a long-running botnet for carrying out crypto mining, distributed...
-

 3.7KMalware
3.7KMalwareHackers Targeting Human Rights Activists in Morocco and Western Sahara
Human rights activists in Morocco and the Western Sahara region are the targets of a new threat actor that leverages phishing attacks...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesResearchers Discover LG Smart TV Vulnerabilities Allowing Root Access
Multiple security vulnerabilities have been disclosed in LG webOS running on its smart televisions that could be exploited to bypass authorization and...
-

 3.3KMalware
3.3KMalwareCL0P’s Ransomware Rampage – Security Measures for 2024
2023 CL0P Growth Emerging in early 2019, CL0P was first introduced as a more advanced version of its predecessor the ‘CryptoMix’ ransomware,...
-

 2.5KMalware
2.5KMalwareAttackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
Cybersecurity researchers have discovered an intricate multi-stage attack that leverages invoice-themed phishing decoys to deliver a wide range of malware such as...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesCritical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks
Threat actors are actively scanning and exploiting a pair of security flaws that are said to affect as many as 92,000 internet-exposed...
-
 3.1KMalware
3.1KMalwareWatch Out for ‘Latrodectus’ – This Malware Could Be In Your Inbox
Threat hunters have discovered a new malware called Latrodectus that has been distributed as part of email phishing campaigns since at least...
-

 292Data Breach
292Data BreachThe Drop in Ransomware Attacks in 2024 and What it Means
The ransomware industry surged in 2023 as it saw an alarming 55.5% increase in victims worldwide, reaching a staggering 5,070. But 2024...
-

 3.8KMalware
3.8KMalwareCybercriminals Targeting Latin America with Sophisticated Phishing Scheme
A new phishing campaign has set its eyes on the Latin American region to deliver malicious payloads to Windows systems. “The phishing...
-

 1.2KMalware
1.2KMalwareGoogle Sues App Developers Over Fake Crypto Investment App Scam
Google has filed a lawsuit in the U.S. against two app developers for allegedly engaging in an “international online consumer investment fraud...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesHackers Exploit Magento Bug to Steal Payment Data from E-commerce Websites
Threat actors have been found exploiting a critical flaw in Magento to inject a persistent backdoor into e-commerce websites. The attack leverages...
-
 3.1KMalware
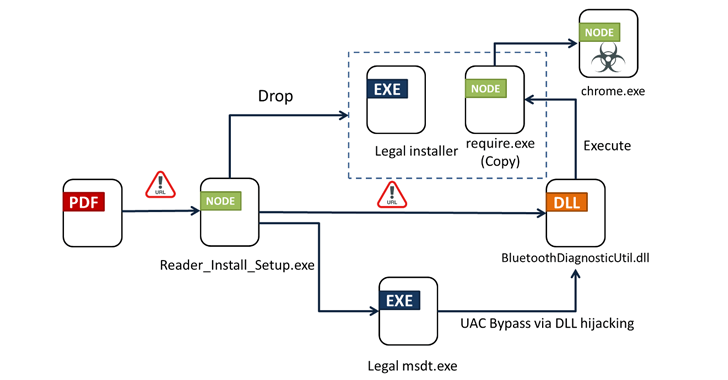
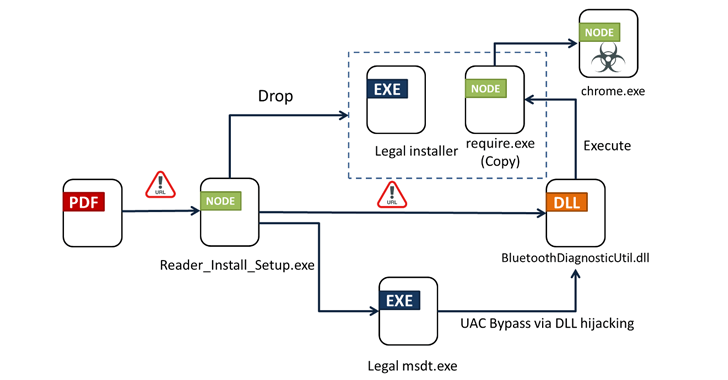
3.1KMalwareFrom PDFs to Payload: Bogus Adobe Acrobat Reader Installers Distribute Byakugan Malware
Bogus installers for Adobe Acrobat Reader are being used to distribute a new multi-functional malware dubbed Byakugan. The starting point of the...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




