Search results for "Botnet"
-
 1.6KCyber Crime
1.6KCyber CrimeBotnet found using YouTube to illegally mine cryptocurrency
Hundreds of botnets operate internationally to achieve various malicious objectives. One such botnet named Stantinko which has been operating since 2012 in...
-

 638Malware
638MalwareStantinko botnet adds cryptomining to its pool of criminal activities
ESET researchers have discovered that the criminals behind the Stantinko botnet are distributing a cryptomining module to the computers they control
-
 1.1KDDOS
1.1KDDOSRoboto Botnet Exploiting Linux Webmin Server RCE Vulnerability To Perform DDoS Attack
A new wave of Roboto Botnet activities being discovered that attack the Linux Webmin servers by exploiting the RCE vulnerability using vulnerability...
-
 2.6KRansomware
2.6KRansomwareHackers Changing the Main Attack Vector from RDP Compromise to Botnets For Network Breach
The ransomware evolution re-shaping the cyber domain, starting from 2019 the ransomware attacks against high-profile public and corporate networks by making criminal...
-

 553Cyber Attack
553Cyber AttackPhorpiex Botnet Sending Out Millions of Sextortion Emails Using Hacked Computers
A decade-old botnet malware that currently controls over 450,000 computers worldwide has recently shifted its operations from infecting machines with ransomware or...
-
 379Data Security
379Data SecurityMasterMana botnet hits users by evading detection with URL shorteners
MasterMana botnet is part of an ongoing malware campaign. The IT security researchers at Prevailion have discovered an active botnet that has...
-

 372Geek
372GeekNew Android banking botnet ‘Geost’ hits thousands of devices
Currently, users mostly from in Eastern Europe & Russia are being targeted by this botnet. Recently, researchers from the Czech Technical University,...
-

 351Botnets
351BotnetsAura Botnet – A Portable Botnet Framework with a Django-based C2 server
A super portable botnet framework with a Django-based C2 server. The client is written in C++, with alternate clients written in Rust,...
-

 443Hacked
443HackedDestructive Malware Botnet “Emotet” Is Making A Comeback
Emotet, a deadly malware botnet, has started a new spam email campaign after being underground for nearly four months, a security researcher...
-
 327Data Security
327Data SecurityMeet Retadup botnet that was infected by another malware
Avast and French authorities have now dismantled the nasty Retadup botnet. With the advent of cryptocurrencies, we have seen a gold rush...
-
 338Malware
338MalwareFrench Cops Hijacked Retadup Botnet & Remotely Wipe The Malware From 850,000 Infected Computers
Team of French Cops from Cybercrime Fighting Center (C3N) takedown the Retadup worm command & control servers to block the further infection...
-

 391Hacked
391HackedNasty Botnet Neutrino Caught Hacking Other Hackers’ Web Shells
A crypto mining botnet operation, going for almost a year, is hijacking web shells of other hackers, according to report from Positive...
-
 539Malware
539MalwareMultistage Attack Delivers BillGates/Setag Backdoor to Turn Elasticsearch Servers into DDoS Botnet
A new multistage attack exploiting Elasticsearch servers using the old unpatched vulnerability to invoke a shell with a crafted query and encoded...
-
 401DDOS
401DDOSMassive DDoS Attack on Streaming Service with 292,000 RPS (Requests Per Second) From 402,000 Different Botnet IP’s
An unrevealed streaming site hit with massive DDoS attack from 402,000 different IoT(Internet of Things) Botnet IPs, which directed a peak flow...
-
 267Malware
267MalwareLinux Botnet Adding BlueKeep-Flawed Windows RDP Servers to Its Target List
Cybersecurity researchers have discovered a new variant of WatchBog, a Linux-based cryptocurrency mining malware botnet, which now also includes a module to...
-
 407Data Security
407Data SecurityNew malware attack turns Elasticsearch databases into DDoS botnet
The malware attack involves two stages including one in which existing cryptomining malware is removed. The IT security researchers at Trend Micro...
-

 750Malware
750Malware4 Most Memorable Botnet In History
What is Botnets? Botnets are artificial networks created by malware, which can be controlled by the virus author remotely. Here in Hackercombat.com,...
-

 456Geek
456GeekNew cryptomining botnet malware hits Android devices
The new malware exploits Android Debug Bridge (ADB) ports. In a research conducted by the Tokyo-based cybersecurity and threat defense firm Trend...
-
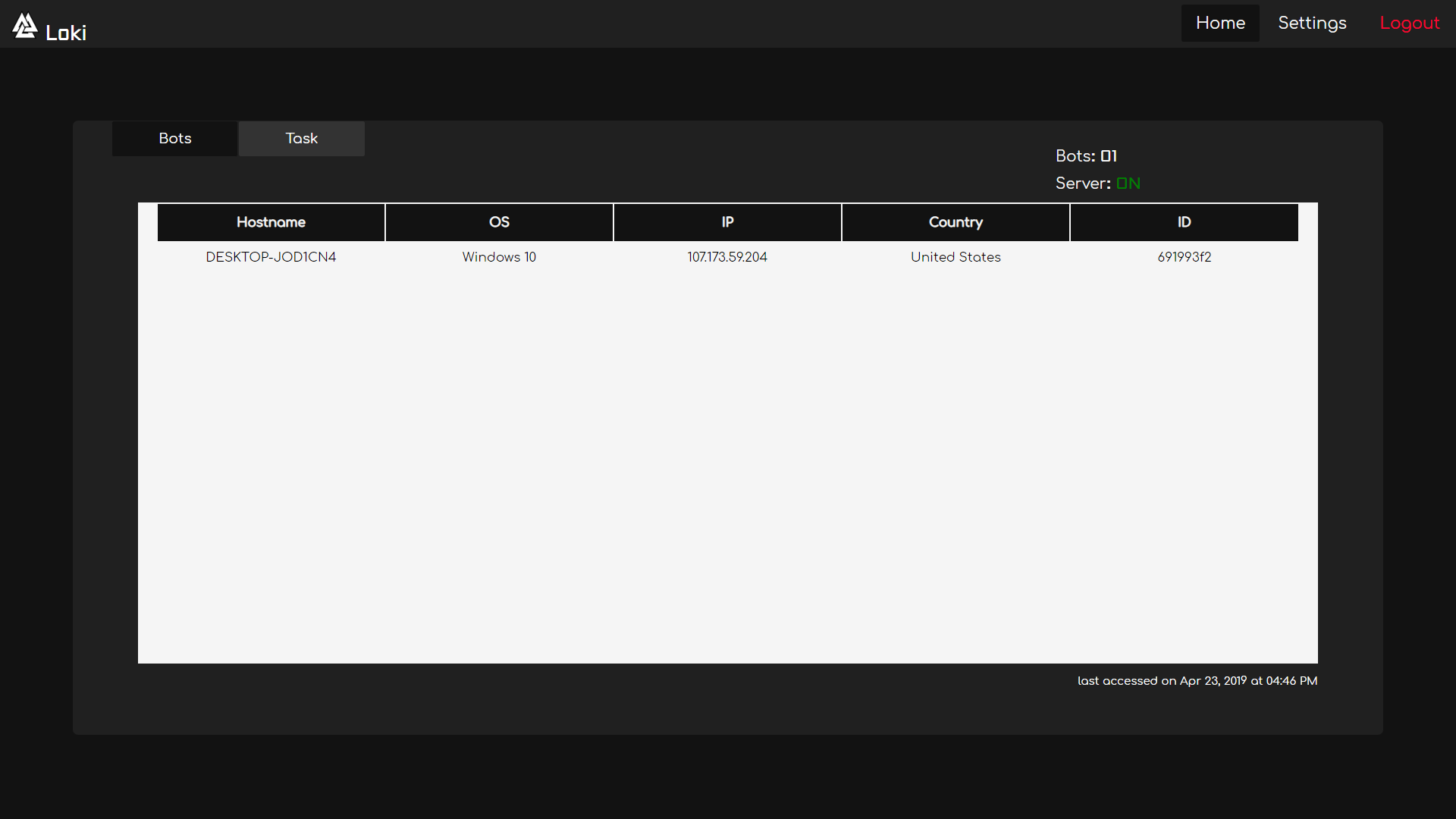
 305Remote Administration Tools
305Remote Administration ToolsLoki – Remote Access Tool / Botnet
Loki is a Remote Access Tool/Botnet & uses RSA-2048 with AES-256 to keep your communication secure. Requirements Python 3.6.x | 3.7.x Server...
-

 385Malware
385MalwareTwenty years in prison for hackers/founders of Mariposa botnet and Bitcoin platform NiceHash
According to digital forensics specialists, the Federal Bureau of Investigation (FBI) is trying to charge some hackers, including the founder of NiceHash...
-
 394Data Security
394Data SecurityNew Electrum DDoS botnet steals $4.6M after infecting 152,000 hosts
The majority of the bots are located in Brazil and Peru but the number of victims is constantly increasing across diverse regions....