What is SSRF vulnerability?
Installation
git clone https://github.com/ariya/phantomjs.git
cd phantomjs
chmod +x build.py
./build.pyUsage
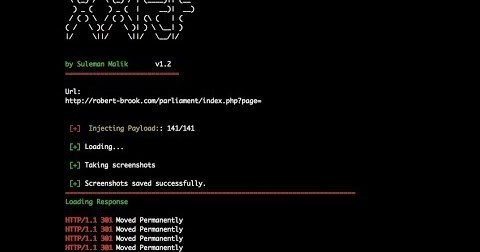
./xxrf.shEnter the url with vulnerable parameter and hit return key. The script is designed to perform two different tasks. At first it will inject the payload next to the vulnerable parameter and process the request to another python script written by @maaaaz. The python script requires phantomJS to perform screenshot function. It uses the list of injected payload and screenshots them and places them in a screenshot directory.
Example:
https://www.example.com/index.php?url=