Search results for "Access"
-

 93Vulnerabilities
93VulnerabilitiesADVANTECH PATCHES WEBACCESS REMOTE CODE EXECUTION FLAWS
Advantech has published a new version of its WebAccess product to address vulnerabilities that put installations at risk to remote code execution...
-

 262Data Security
262Data SecurityFBI’s facial recognition system can access 411 million photos including foreigners
Today the federal Government Accountability Office (GAO) finally published its exhaustive report on the FBI’s face recognition capabilities. The takeaway: FBI has...
-

 301Data Security
301Data SecurityHackers Can Steal Mitsubishi Outlander Hybrid Car By Exploiting WiFi Access Point
Mitsubishi’s Outlander Hybrid Car’s Alarm Vulnerable to Hack due to Wi-Fi access point issue Researcher and security expert Ken Munro has revealed...
-
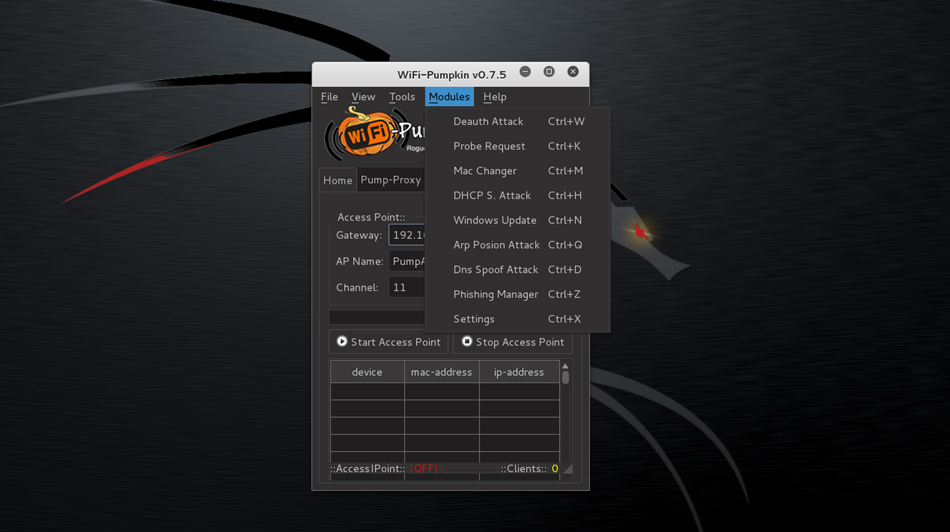
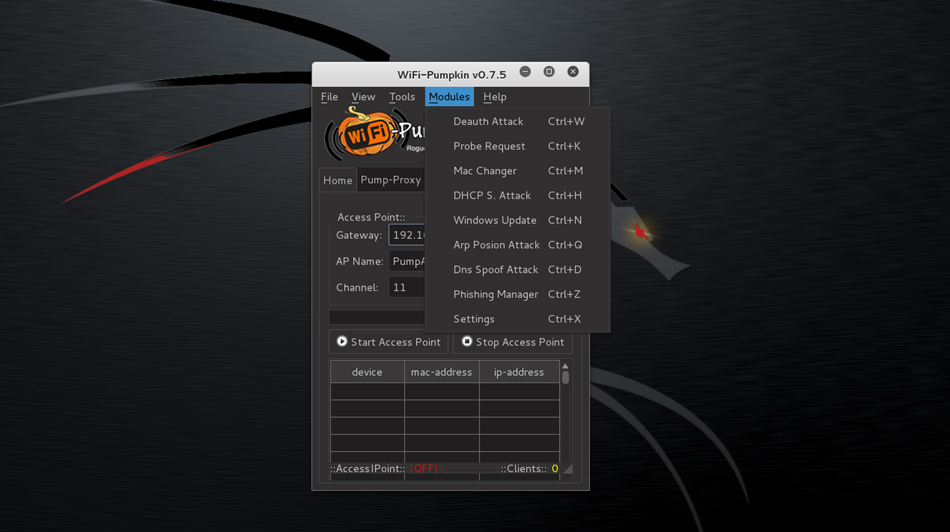 108Hack Tools
108Hack ToolsWIFI Pumpkin – Framework for Rogue Wi-Fi Access Point Attack
WiFi-Pumpkin is a security tool that provides the Rogue access point to Man-In-The-Middle and network attacks. Installation Kali 2.0/WifiSlax 4.11.1/Parrot 2.0.5 Python...
-
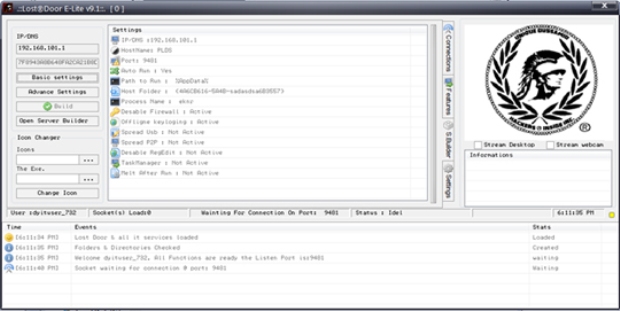
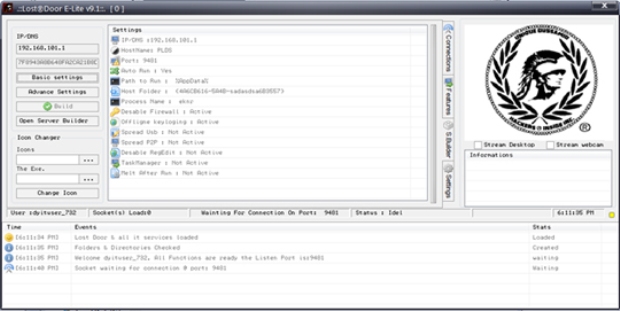 163Data Security
163Data SecurityLost Door RAT: Accessible, Customizable Attack Tool
We recently came across a cyber attack that used a remote access Trojan (RAT) called Lost Door, a tool currently offered on...
-
 321Geek
321GeekHere’s Your Chance to Use IBM’s Remotely Accessible Quantum Computer
Quantum Computing- No More a Thing of Distant Future — IBM wants us all to use it remotely accessible Quantum Computer… for free!...
-

 172Hacked
172HackedUsage of Tor Browser To Access Facebook Crosses 1 Million Mark
Short Bytes: Number of people using the Tor browser for maintaining their privacy and anonymity has crossed one million mark this month,...
-

 118Data Security
118Data SecurityA million people now access Facebook on the “dark web” every month
The number of people accessing Facebook via the “dark web” now stands at 1 million per month, the tech giant announced today...
-

 277Vulnerabilities
277VulnerabilitiesHow to easily bypass iPhone 6s Lockscreen to access to Photos and Contacts
iPhone 6s and 6s Plus running the latest iOS version are plagued by a vulnerability that can be exploited to bypass the...
-
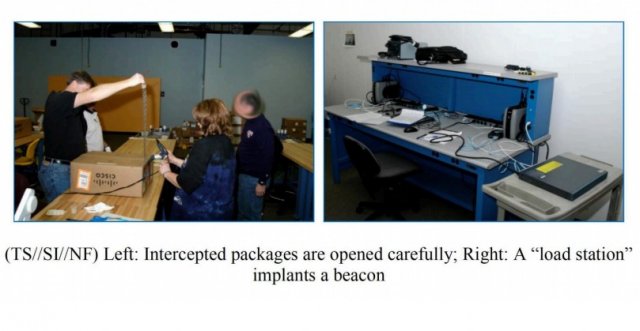
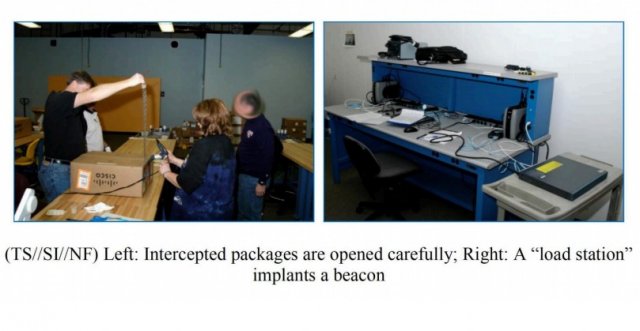 158Malware
158MalwarePhotos Show How NSA Implants Trojan In Routers For Hidden Access And Spying
ShortBytes: In a recent find out, it has been revealed how NSA implants trojan firmware in the networking devices being delivered to...
-
 109Incidents
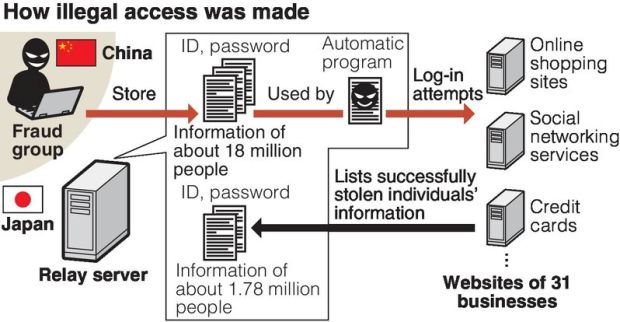
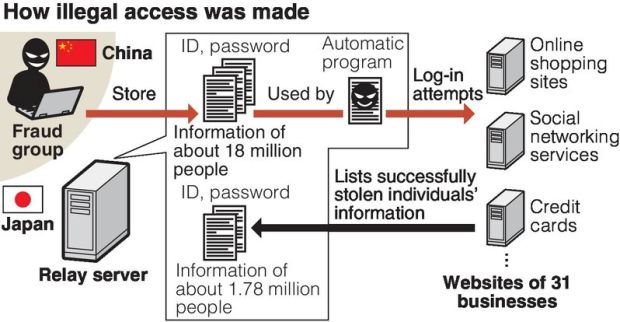
109Incidents18 million stolen IDs discovered on server / Criminals in China got illegal access
The IDs and passwords of about 18 million Internet users have been found on a computer server set up by a Tokyo...
-

 130Geek
130Geek“Accessibility Malware” puts 65% percent of old version Android devices at risk
Android is the most vulnerable OS in the world but the “Accessibility Malware” threatens 65% of the old version Android devices An...
-

 197Vulnerabilities
197Vulnerabilities‘Accessibility Clickjacking’ malware could impact 500 million Android devices
Researchers at threat defense company Skycure have uncovered an Android proof of concept malware that uses accessibility services to allow attackers to...
-

 276Opinion
276OpinionApple and ‘exceptional access’ to crypto protection
Apple is the latest in a host of technology players to be requested to allow exceptional access, that is, access in exceptional...
-

 346Geek
346GeekApple defiant in San Bernardino Shooting Case; says no to backdoor access
Judge Issues Order to Apple to Unlock iPhone Vital in the San Bernardino Shooting Case — Apple refuses to follow orders The...
-

 177How To
177How ToHow To Access Your Chrome Passwords Remotely From Any Browser?
Short Bytes: Google has introduced a new online feature where a user can sync its passwords to Google and access Chrome passwords...
-

 233Incidents
233IncidentsAvast SafeZone Browser Lets Attackers Access Your Filesystem
Another antivirus maker decides to mess around with Chromium default security features and gets it totally wrong. Just two days after Comodo’s...
-
 166Vulnerabilities
166VulnerabilitiesAndroid and Linux Zero-Day Gives Attackers Root Access
A new zero-day vulnerability allows Android or Linux applications to escalate privileges. Security researchers have discovered a new zero-day vulnerability in Linux kernel that...
-

 108Data Security
108Data SecurityChina passes controversial anti-terrorism law to access encrypted user accounts
China’s legislature unanimously passed a controversial anti-terrorsim law on Sunday despite months of objections from major tech firms and Washington alike. Among...
-

 270Data Security
270Data SecuritySteam Fail: Cache Issue Allowed Access to Other People’s Accounts
Steam has been caught providing access to one user’s personal account to another user — It is unclear if the service was hacked...
-

 337News
337NewsInstagram Hacked: Security Researcher Gets Admin Panel Access
Wesley Wineberg, an independent security researcher, participating in Facebook’s bug bounty program, managed to crack his way through Instagram defenses and almost...






