Search results for "Access"
-
 410Vulnerabilities
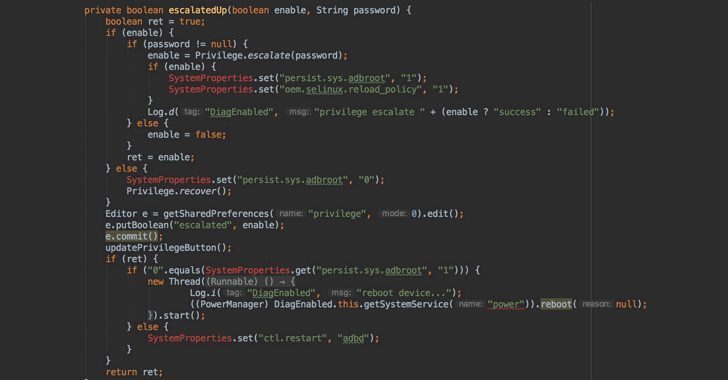
410VulnerabilitiesAndroRAT – A Remote Access Trojan Compromise Android Devices and Inject Root Exploits
A Newly discovered Android Remote Access Trojan called AndroRAT targeting unpatched Android Devices that exploit the publicly disclosed critical privilege escalation vulnerability and...
-
 236Information Gathering
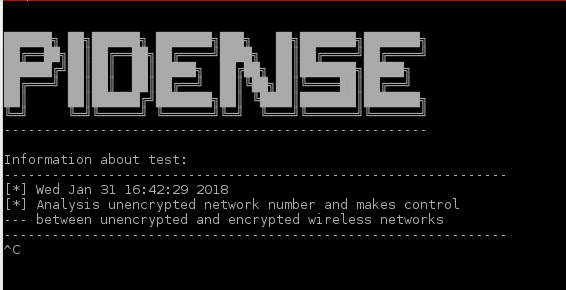
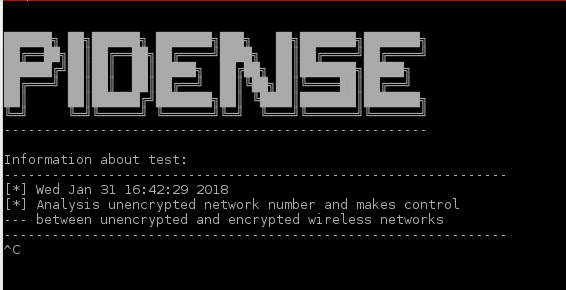
236Information GatheringPiDense – Monitor Illegal Wireless Network Activities (Fake Access Points)
Monitor illegal wireless network activities. Similar SSID broadcasts Same SSID broadcasts Calculates unencrypted wireless networks density Watches SSID broadcasts at the blacklist. Capabilities...
-

 392How To
392How ToHow To Access Google Drive Files Offline On Your PC, Android, iOS Device?
Google Drive is a massive cloud storage service that offers 15 GB of free space across Google Drive, Gmail, and Google Photos. It...
-
 340News
340NewsCrackas with Attitude’ hacker posed as CIA Chief to access secret data
Remember the infamous Crackas with Attitude (CWA) hacking group? If you don’t then these were the same hackers who hacked Verizon My...
-

 154Tricks & How To's
154Tricks & How To'sHow to Access Facebook Full Site Desktop version on Android/iPhone Mobile browser
Facebook has recently crossed 2 Billion user base and is still growing at rapid pace. Actually the issue is whenever you try...
-

 225News
225NewsPrivate Details of 240,000 DHS Employees Accessed after Data Breach
A data breach targeted towards the Department of Homeland Security (DHS) has resulted in the exposure of personally identifiable information of over...
-

 373Vulnerabilities
373VulnerabilitiesTrackmageddon – Location Tracking Services (GPS) Vulnerabilities Allow to Access Unauthorized GPS Location Data
Security researchers discovered multiple vulnerabilities dubbed “Trackmageddon” which affects GPS services and online location tracking devices. The vulnerabilities with GPS location tracking...
-

 387Geek
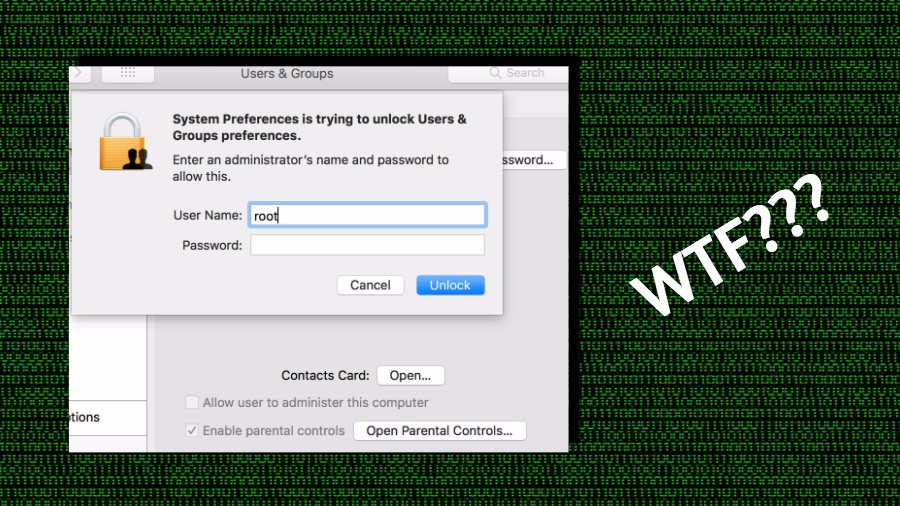
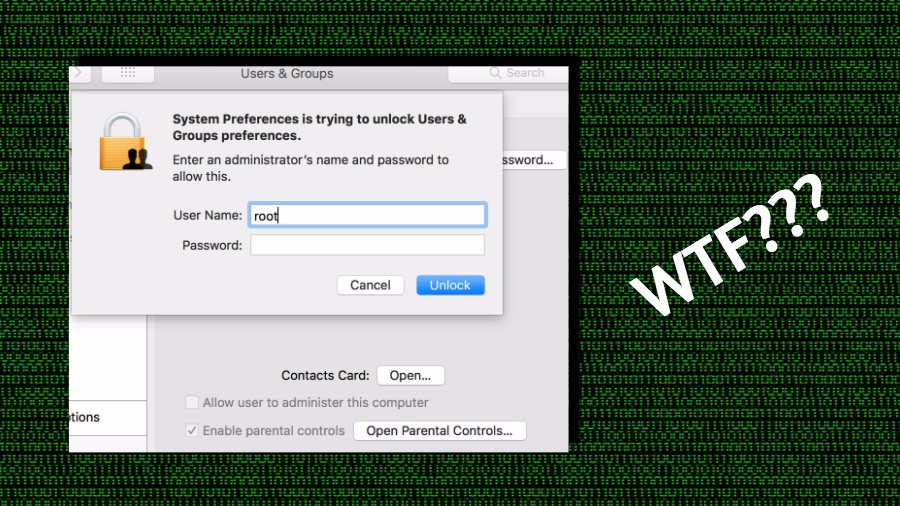
387Geek15-year-old Unpatched Root Access Bug found in Apple’s macOS
An IT security researcher has leaked details on an unpatched Apple’s macOS bug which lets attackers gain root access and take complete control...
-

 206Articles
206ArticlesUnpatched vulnerability affect all versions of macOS, allows code execution and Root access
A security researcher (@s1guza) has published the details of an unpatched vulnerability in macOS that can be exploited to gain full control...
-
 370Reviews
370ReviewsPrivate Internet Access (PIA) Review 2018: A Fast And Cheap VPN Service You Can Buy
What are the different ways to protect yourself digitally? As the most basic level, you should have some security software to safeguard...
-
 248Hacked
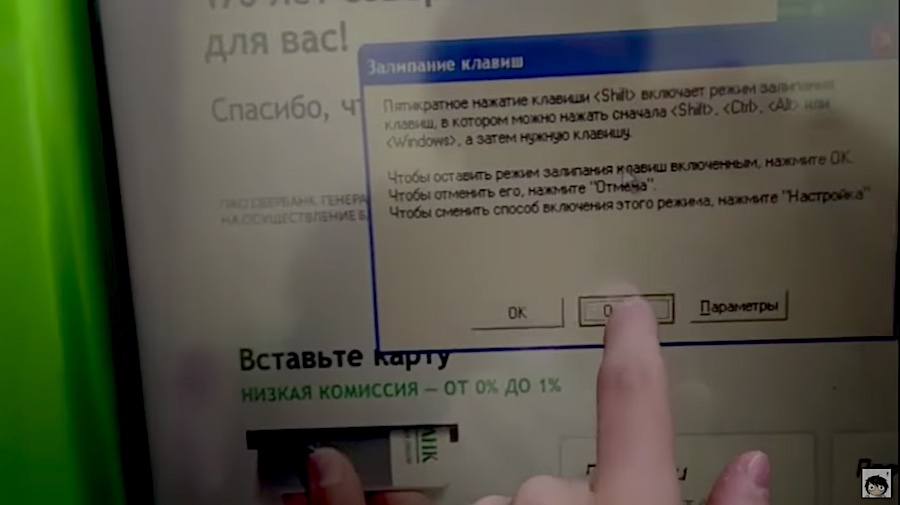
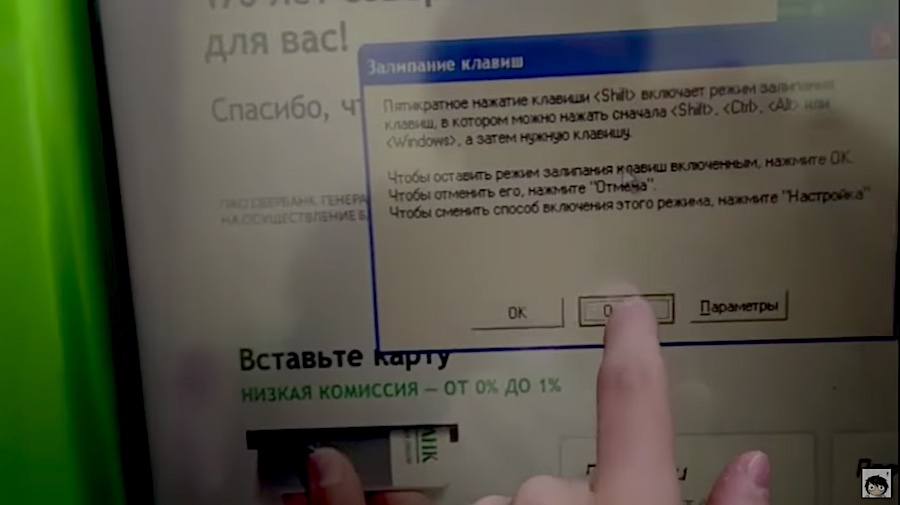
248Hacked“I Just Pressed Shift Key 5 Times” — User Gains Full Access On A Windows XP ATM Machine
When you’re running Windows XP in today’s times, you shouldn’t expect your machine to fully bulletproof against different kinds of malware attacks....
-

 147Vulnerabilities
147VulnerabilitiesZero-day iOS HomeKit vulnerability allowed remote access to smart accessories including locks, fix rolling out
A HomeKit vulnerability in the current version of iOS 11.2 has been demonstrated to 9to5Mac that allows unauthorized control of accessories including smart locks and...
-
 283Hacked
283HackedALERT: Anyone Can Access Your Mac As Root With No Password — Here’s How To Fix
If you’re currently working on a macOS-powered machine, there are good chances that you might be running the latest macOS High Sierra operating...
-

 203Malware
203MalwareAdwind remote access Trojan makes a comeback and it’s got smarter
The Adwind cross-platform, malware-as-a-service Trojan has been around since 2012. Spread by phishing emails claiming to be invoices, purchase orders, and requests...
-
 188Articles
188ArticlesOnePlus Left A Backdoor That Allows Root Access Without Unlocking Bootloader
Just over a month after OnePlus was caught collecting personally identifiable information on its users, the Chinese smartphone company has been found...
-

 91Hackers Repository
91Hackers RepositoryBlackOrphan – Tool built with Bash/nodeJs mainly for gaining a remote shell access to a Linux Box
BlackOrphan is a tool built with Bash/nodeJs mainly for gaining a remote shell access to a Linux Box BlackOrphan is a tool...
-
 157How To
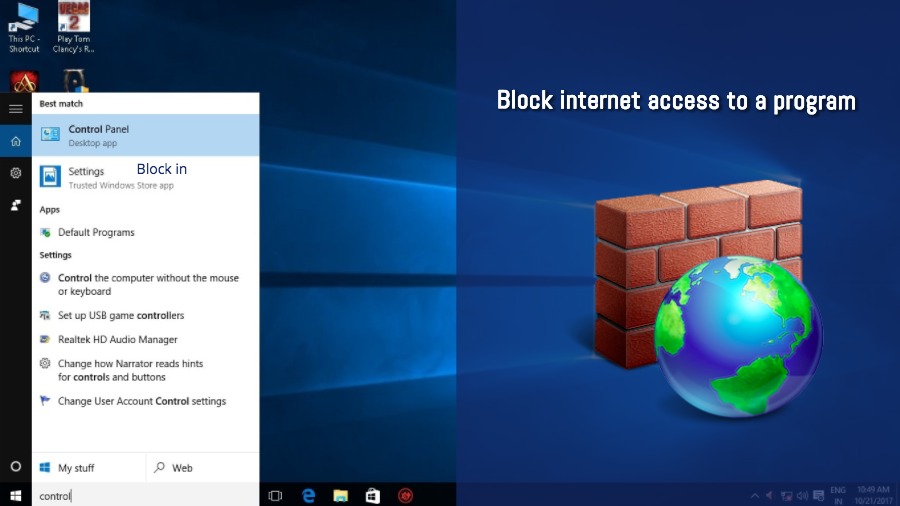
157How ToHow To Block A Program From Accessing The Internet In Windows?
Most of the third-party software that resides on your computer can access the internet and there are few offline-only programs being developed....
-

 285Articles
285ArticlesApple iPhone X is Providing Developers access to Facial Data
Apple’s privacy signs do not spread to the thousands of app developers who will gain access to facial data in order to...
-

 372Geek
372GeekiPhone apps can access cameras to secretly take photos and record videos
There was a time when Apple devices were considered secured when compared to Android devices. Although the situation is not as worse...
-

 208Vulnerabilities
208VulnerabilitiesT-Mobile Website Allowed Hackers to Access Your Account Data With Just Your Phone Number
The bug exposed customers’ email addresses, their billing account numbers, and the phone’s IMSI numbers. T-Mobile has patched the bug. Until last...
-
 211Data Breach
211Data BreachT-Mobile Website Bug Allowed Hackers to Access Millions of customer’s Personal Data
A bug on T-Mobile Website allows hackers to steal customers personal data such as email addresses, T-Mobile customer account numbers and their...






