Search results for "Access"
-

 170Incidents
170IncidentsHacking on PDQ, attackers get access to credit card data
Fast food franchise PDQ has informed its customers that information of the cards with which they have made their purchases could be...
-

 401Data Security
401Data SecurityThe Pirate Bay is offline: this is how you can access their domain in Dark Web
Last week, the torrent portal The Pirate Bay was put offline and more than five days have passed without the website being...
-

 319Geek
319GeekThe Pirate Bay stays down – Here’s how to access its Dark Web domain
Last week, the torrenting giant The Pirate Bay went offline and it has been over five days that the website has not surfaced...
-

 251Hacked
251HackedCortana Flaw Lets Hackers Access Data, Reset Password On Locked Windows 10 PCs
Security researchers have found a critical flaw in Windows 10 where Cortana can be manipulated into executing Powershell commands on locked devices. Attackers can...
-
 270DDOS
270DDOSCloudflare DDoS Mitigation System Launch DDoS Attack on its Own Infrastructure & 1.1.1.1 DNS 17 Min Globally Inaccessible
Cloudflare owned DNS service faced a Critical issue during the new interaction and goes down for 17 Minutes that lead to 1.1.1.1 DNS...
-

 140Incidents
140IncidentsAccess all the information Apple has about you in a single portal
For all of us who have been curious to know what data has been collected and stored by Apple about us, it...
-

 319News
319NewsHacker access critical code of British cell operator EE
EE, a British mobile network giant owned by BT Group has been accused of leaving a critical code repository on an open-source tool protected...
-

 304Vulnerabilities
304VulnerabilitiesVulnerability in Oracle Access Manager exploited to bypass authentication and control the account of any user
Wolfgang Ettlinger of SEC Consult Vulnerability Lab, information security expert, found vulnerability in Oracle Access Manager that can be exploited remotely to bypass authentication...
-
 327Malware
327MalwareGravityRAT – A Powerful Remote Access Trojan Conducting an APT Cyber Attack in India, US and UK
A newly uncovered APT Malware called GravityRAT deployed by a hacking group to attack various sectors in India, US, and UK. This...
-

 184Data Security
184Data SecurityFacebook’s way to access hospital patient records
According to CNBC, Facebook had a secret plan. It wanted to capture data from hospitals about their most vulnerable patients, and match...
-
 316Malware
316MalwareNew Android Remote Access Trojan(RAT) Steals Photos, Contacts, SMS & Recording Phone Calls
Newly Discovered two new Android RAT Compromising Victims Mobile and steals various sensitive information such as Photos, Contacts, SMS and it can also...
-
 301Data Security
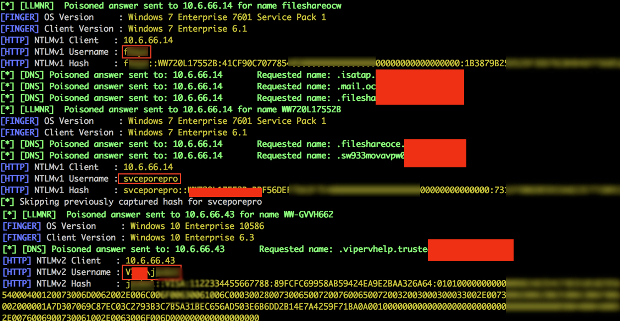
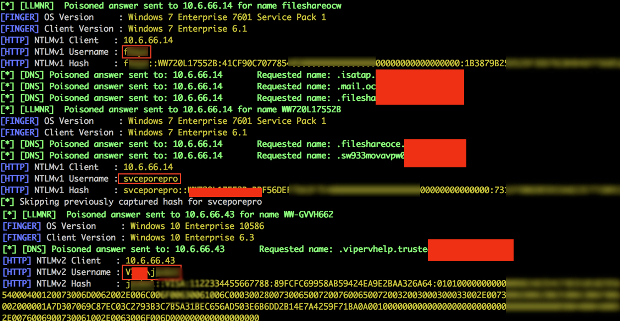
301Data SecurityTop Five Ways I gained access to Your Corporate Wireless Network (Lo0tBo0ty KARMA edition)
While performing penetration and red team services , I have always enjoyed the challenge of gaining access to a well fortified wireless network....
-

 381Geek
381GeekFacebook Secretly Provided Analytic Firm Access to Million of Profiles
Controversies and scandals on Facebook don’t seem to end anytime soon. Reportedly, the social network is facing its largest data breach scandal...
-

 257Infosec
257InfosecSteps to Remotely Access Your Laptop from Mobile
A Remote access can help you in a lot more ways to reduce your time frame. In this super speedy workaholic world...
-
 337Geek
337GeekWorld’s Top VPN Provider, Private Internet Access (PIA), Goes Open Source
In the past decade, the market for VPN services has grown at a rapid pace. There many reputed services available that provide...
-
 222Malware
222MalwareResearchers bypassed Windows 10 Lock Protection and Access Cortana Voice Commands that leads to Install Malware
The researcher discovered a new flaw in Windows 10 lock Protection that allows attackers to access the Cortana Voice Commands in the...
-

 243Wifi Hacking
243Wifi HackingThe Rogue Toolkit – Targeted Evil Twin Wireless Access Point Attack
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP) for...
-
 265Malware
265MalwareHackers Attacked Public Sector using Remote Access Trojan that was Entirely Written in Python
A newly emerging Remote access Trojan called CannibalRAT that completely written in Python language targeting and impacting the Brazilian public sector management school. Python...
-

 284Wireless Attacks
284Wireless AttacksThe Rogue Toolkit – Targeted Evil Twin Wireless Access Point Attack Toolkit
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP) for...
-

 309Incidents
309IncidentsA Boon for Privacy: Android P will Prevent Idle Background Apps from Accessing the Camera
Android P, the next major version of Android, could be weeks away from an official unveiling, and although its core user-facing features are still unknown to...
-

 346Malware
346MalwareHow to hack using PARAT- Remote Access Trojan (RAT)?
According to cyber security specialist; a Remote Access Trojan (RAT) is a type of malware that controls a system via a remote network connection...






