Search results for "Access"
-

 279Data Security
279Data SecurityApple MDM tool weakness allows access to sensitive information
Lack of authentication in Apple’s device enrollment program would allow attackers to get WiFi and VPN configuration passwords According to specialists in...
-

 349News
349NewsFacebook hacked: Hackers steal access tokens of 50 million accounts
Hackers exploited a vulnerability in the “View As” feature of Facebook. The social media giant Facebook has announced that it has suffered a...
-

 202Hacked
202HackedMobile Websites Can Access Your Smartphone’s Sensors Without Permission
Your mobile has a swathe of sensors that are used for adjusting your phone’s orientation, movement, detecting IR light, and biometric authentication....
-

 248Data Security
248Data SecurityCritical Linux kernel vulnerability gives attackers root access
Vulnerability persists in different Linux distros Multiple Linux distributions (distros), including all current versions of Red Hat Enterprise Linux and CentOS, contain...
-

 220Hacked
220Hacked“OwnMe” Android Spyware Can Access Your WhatsApp Texts, Call Logs, Browsing History
A security researcher from ESET has announced that he has unearthed new Android-based spyware that is capable of accessing the Whatsapp database...
-
 204Hacked
204HackedmacOS Mojave Has A Security Flaw That Lets Hackers Access Your Contacts
A security flaw has been unearthed in macOS Mojave, Apple’s latest desktop OS update, by a well-known security researcher Patrick Wardle. As reported by Bleeping...
-

 303Vulnerabilities
303VulnerabilitiesVulnerability in macOS Mojave allows access to protected files
The flaw allows malicious actors to avoid privacy measures An expert in cybersecurity and ethical hacking was able to demonstrate that Apple’s...
-

 306Hacked
306HackedGoogle Admits: Third-Party Apps Can Still Access Your Gmail Data
Back in July 2018, it was reported that Google shares Gmail user data with third-party apps and US lawmakers had asked the...
-
 323Data Breach
323Data Breach3000 Hacked Websites Access comes to Sale in Russian Underground Dark Web Marketplace
Cybercriminals listed 3000 Hacked websites access for sale in Russian based underground marketplace that sells for less than $50. The underground marketplace...
-

 262Vulnerabilities
262VulnerabilitiesZero Day vulnerability allows access to CCTV cameras
Firmware used in up to 800k cameras is vulnerable to attacks thanks to a buffer overflow vulnerability Between 180k and 800k CCTV...
-

 347Malware
347MalwareFive Eyes Group demands access to crime suspects data through encryption backdoors
The group threatens to take legal action Five Eyes alliance member countries have threatened to implement legislation if technology providers do not cooperate...
-

 246Vulnerabilities
246VulnerabilitiesA Cisco software vulnerability could allow unauthorized access to sensitive information
The company is already working on a security update A recently discovered vulnerability in the Cisco Data Center Network Manager software could allow a...
-
 261Malware
261MalwareHackers Selling HTTP Remote Access Trojan via Weaponized Word Documents in Underground Market
Cyber Criminals selling Parasite HTTP RAT (Remote Access Trojan) on the underground marketplace that distributed via Email to the victims using Weaponized...
-

 453Data Security
453Data SecurityFlaw in Swann smart security cameras allows access to user’s live stream
Security cameras and other IoT devices have been frequently identified to be incompetent and plagued with a variety of built-in flaws that...
-

 382Cyber Crime
382Cyber CrimeDark web marketplace found selling access to airport’s security system
Dark Web has become the hub of illegal activities over the Internet. Everything from credit card numbers to personal information and even...
-

 296Data Security
296Data SecurityDo third-party apps can access your Gmail inbox?
Google is pronounced on the investigation of email scanning made by third-party apps Google has responded to a recent research on apps...
-

 154Incidents
154IncidentsHackers gain access to gas pump in Detroit, steal 600 gallons
Gas robbery at Marathon’s station. Two thieves used a remote device to hack the system of a gas pump, thus they managed...
-

 299How To
299How ToHow To Know If A Third Party App Is Reading Your Gmail Inbox? How To Disable Gmail Access?
Last year, Google was criticised for accessing users’ inbox to show them relevant ads. In the time that followed, the search giant stopped...
-
 289Hacked
289HackedGoogle Slammed For Giving Gmail Access To Third Party Developers (Humans)
There are many third-party apps that require access to your Gmail account. For instance, the ones that help you plan trips or...
-

 247Hacked
247HackedNSA Deletes Hundreds Of Millions Of Call Records It Wasn’t ‘Authorized’ To Access
On May 23rd, The American intelligence agency NSA started the process of deleting the call records it has obtained from US telecom companies since 2015....
-
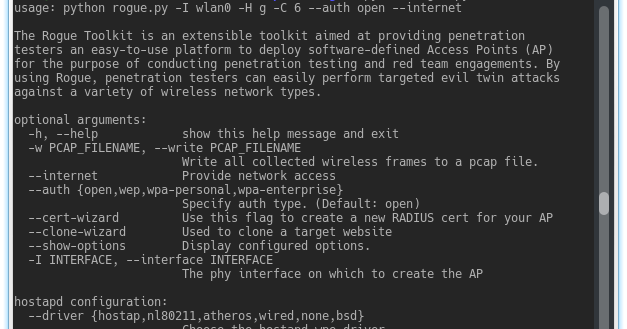
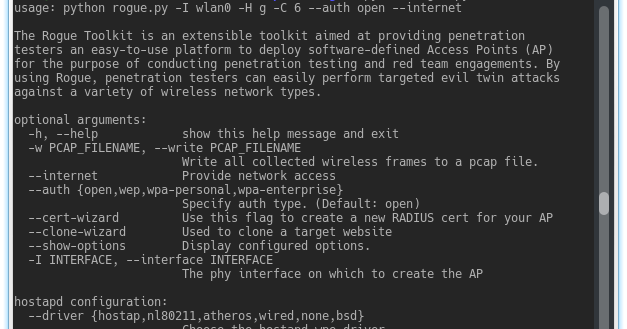 266Wireless Attacks
266Wireless AttacksThe Rogue Toolkit – An Extensible Toolkit Aimed At Providing Penetration Testers An Easy-To-Use Platform To Deploy Access Points
The Rogue Toolkit is an extensible toolkit aimed at providing penetration testers an easy-to-use platform to deploy software-defined Access Points (AP)...






