Search results for "Access"
-

 464News
464News7 Essential Features of a Perfect Privileged Access Management Solution
Privileged accounts have access to the most valuable corporate information, which is why they are often targeted by attackers. As a result,...
-
 719Cyber Crime
719Cyber CrimeNASA astronaut accused of accessing ex-wife’s bank account from space
Outer space’s first-ever cyber crime? It seems so. The US space agency NASA (National Aeronautics and Space Administration) has confirmed that it...
-

 282Data Breach
282Data BreachHostinger Hacked – Hackers Gained Access to the 14 Million Customers Internal Systems Data
Hostinger announced a major data breach that affected nearly 14 million customers, and it reset all the client’s password as a precaution...
-
 205Ransomware
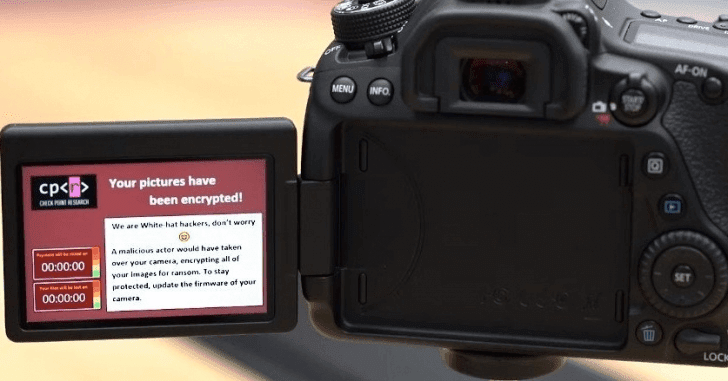
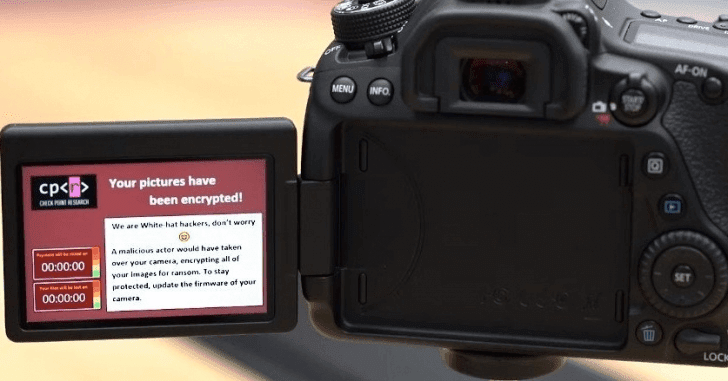
205RansomwareMultiple Bugs in Canon DSLR Camera Let Hackers Infect with Ransomware Over a Rouge WiFi Access Point
Researchers discovered multiple critical vulnerabilities in Picture Transfer Protocol (PTP) that allows attackers to infect the Canon DSLR camera with ransomware to...
-

 302News
302NewsNew ‘Snowflake’ Proxy Helps Censored Users Access Tor Network
While we take internet access for granted, there are several regions in the world where people have little or censored access to...
-

 294Vulnerabilities
294VulnerabilitiesNew iOS 13 vulnerability allows access to passwords stored on your iPhone
Web application security specialists have reported the finding of a new vulnerability in Apple’s new operating system iOS 13 beta version which,...
-

 324Data Security
324Data SecurityHackers used Samsung website to access Sprint’s customer data
Sprint Corporation, an American telecommunications company has announced that it has suffered a data breach after unknown hackers accessed customer accounts credentials...
-

 282Vulnerabilities
282VulnerabilitiesNew exploit allows hackers to access shared files via WhatsApp and Telegram
Ethical hacking specialists from cybersecurity firm Symantec reported the discovery of a vulnerability that, if exploited, would allow a hacker to access...
-

 247News
247NewsAndroid Apps Can Access Your Data Even If You Refuse Permission: Study
We have seen how many of the Android apps have been caught indulging in malicious practices and the most recent study reveals...
-
Malware
TA505 APT Hackers using New AndroMut Malware to Drop FlawedAmmyy RAT and Gain Remote Access
Researchers uncovered a new malware dropper called AndroMut from one of the infamous APT group TA505 to drop the FlawedAmmyy Remote Access...
-

 534News
534NewsMultiple Facebook Pages Caught Spreading Remote Access Trojans Since 2014
Researchers from cybersecurity firm Check Point have uncovered a Facebook campaign that has been spreading malware since 2014. The campaign was operating...
-

 3.5KPrivacy
3.5KPrivacyDefining Role-Based Access Control, or RBAC
Role-Based Access Control, or what is simply known as RBAC, provides the ability to restrict access to certain systems based on the...
-

 302Incidents
302IncidentsTech companies IBM, HP, Fujitsu, TCS, NTT Data, Dimension Data and CSC were hacked to access client networks & data
Network security specialists claim that a hacker group working for China’s Ministry of State Security hacked the networks of eight of the...
-

 282Vulnerabilities
282VulnerabilitiesCisco DNA allowed unauthorized users access to enterprise networks for a long time
IT systems audit specialists reported a critical vulnerability in the Cisco Digital Network Architecture Center (DNA) that, if exploited, could allow a...
-
 251Malware
251MalwarePlurox Modular Malware Spreads Over Local Network and Provide Access to Attackers for Installing Additional Malware
A new malware dubbed Plurox spread itself over the local network using EternalBlue exploit and let attackers gain access to the network...
-
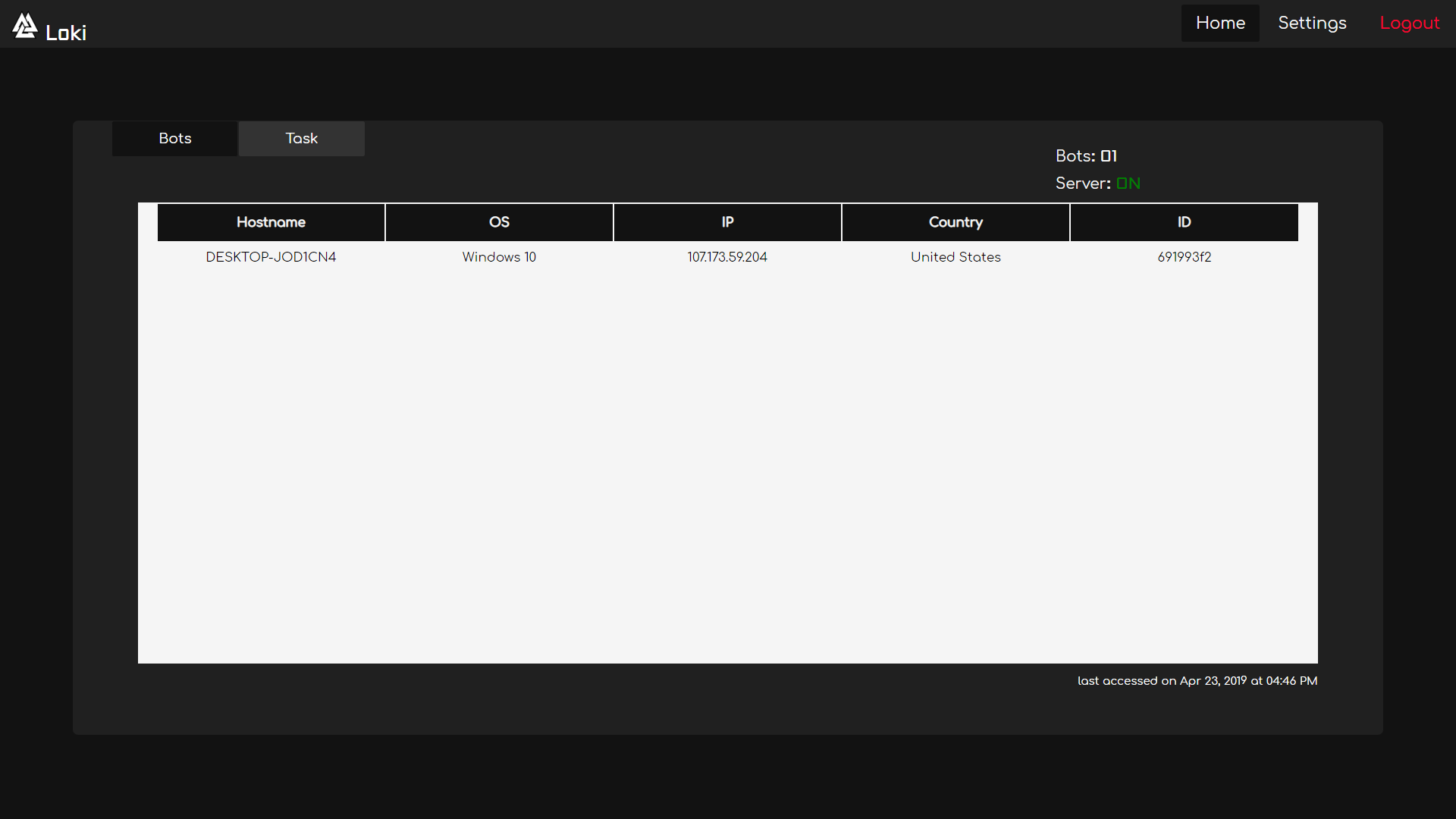
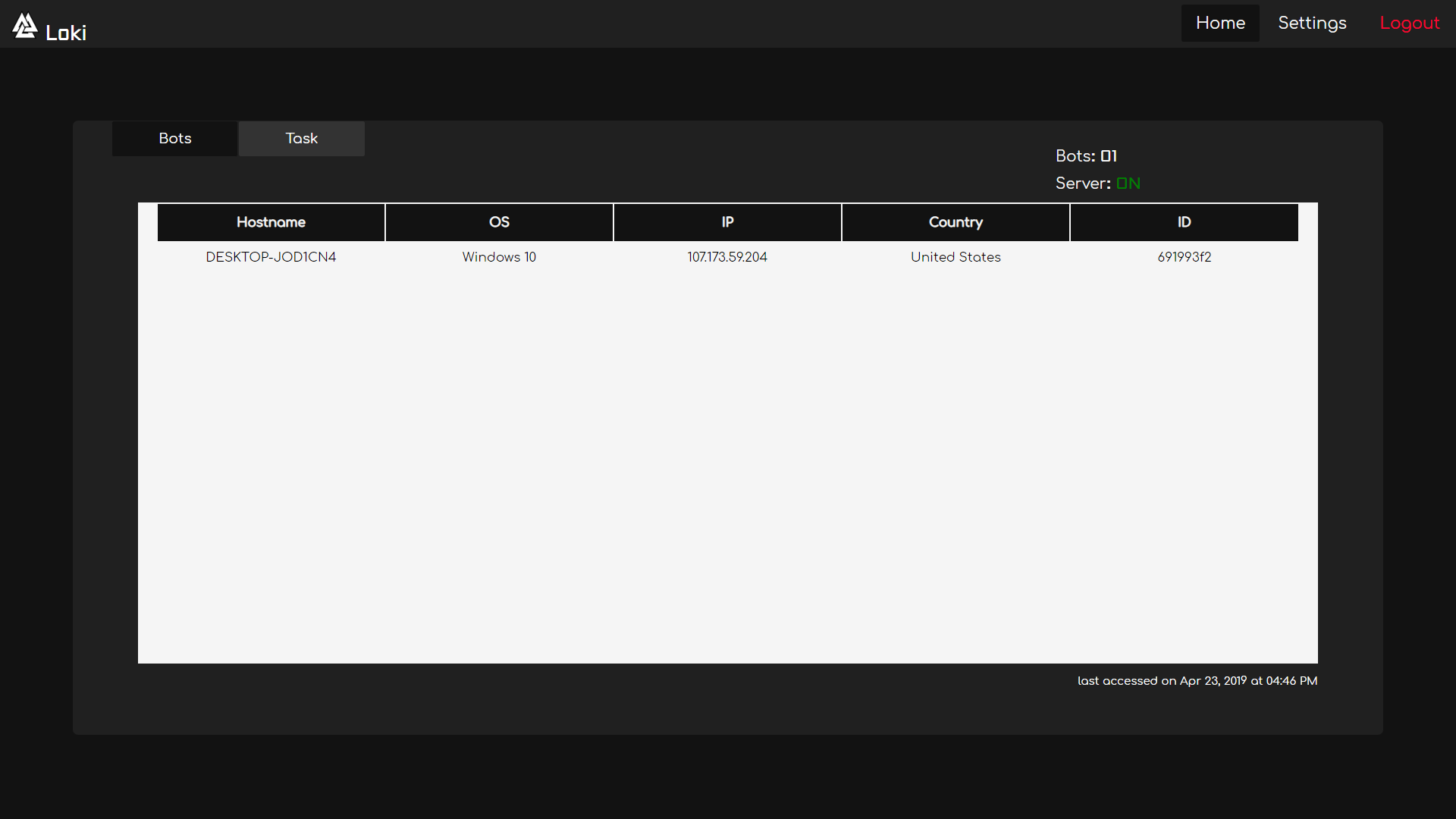 295Remote Administration Tools
295Remote Administration ToolsLoki – Remote Access Tool / Botnet
Loki is a Remote Access Tool/Botnet & uses RSA-2048 with AES-256 to keep your communication secure. Requirements Python 3.6.x | 3.7.x Server...
-
 274News
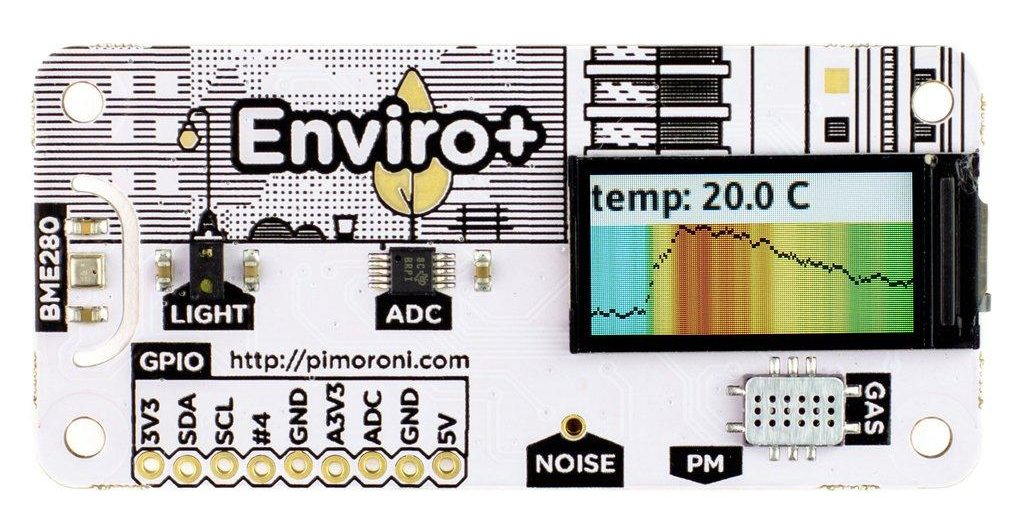
274NewsEnviro+ Is A Raspberry Pi Accessory To Monitor Air Quality
There are many Raspberry Pi accessories available in the market but there are very few boards that are as cool and useful...
-
 302Data Security
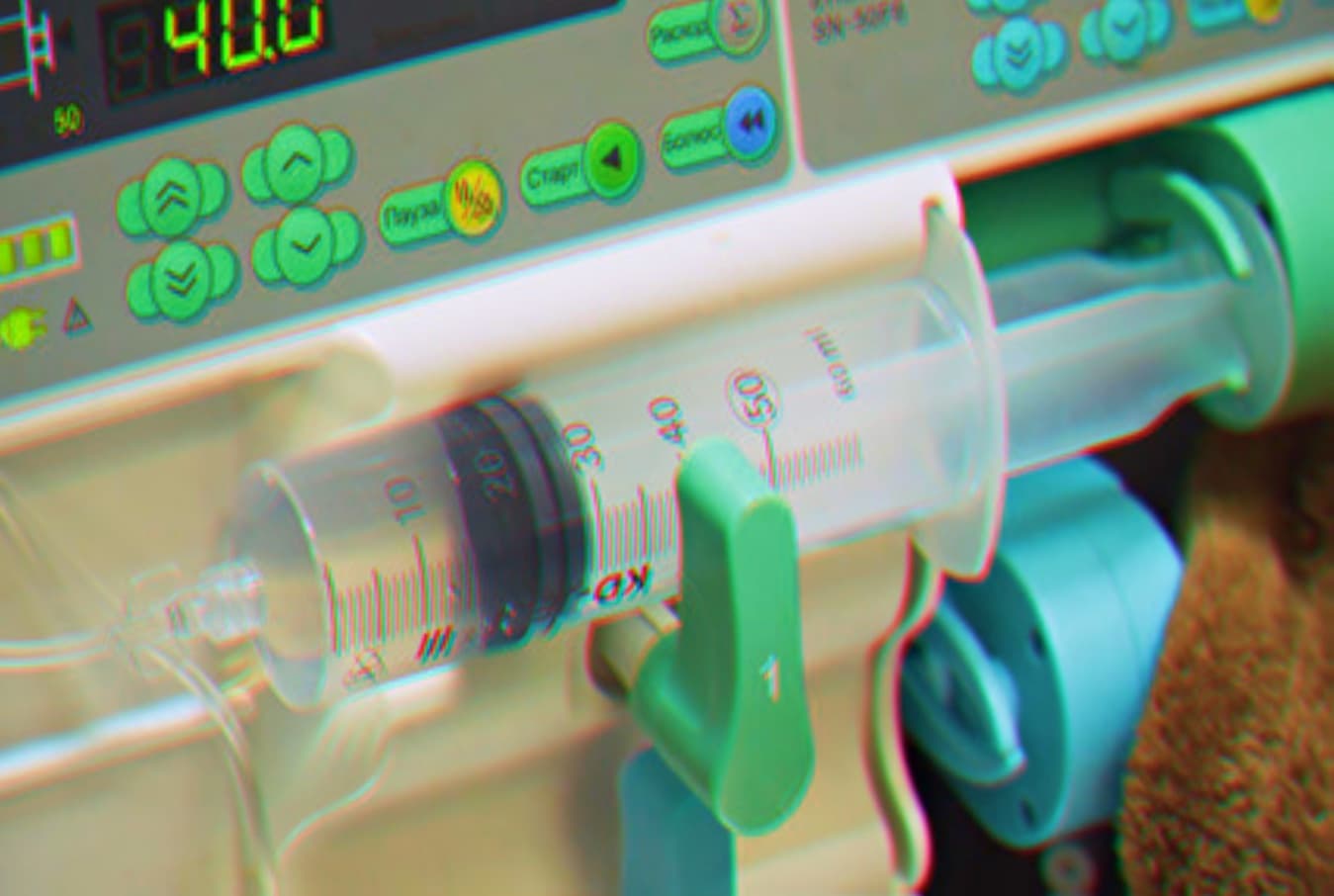
302Data SecurityVulnerable infusion pumps can be remotely accessed to change dosages
Critical Bug in Medical Infusion Pumps lets Attacker Remotely install Unauthorized Firmware to Change Medication Dosages. Researchers at CyberMDX, a healthcare security...
-
 332Malware
332MalwareHackers Use Linux Malware HiddenWasp to Attack Linux Systems for Gaining Remote Access
A new sophisticated, unique Linux malware dubbed HiddenWasp used in targeted attacks against victim’s who are already under attack or gone through...
-

 283Hack Tools
283Hack ToolsEvil Limiter – Limits Bandwidth of Devices on the same Network Without Access.
A tool to limit the bandwidth (upload/download) of devices connected to your network without physical or administrative access. Evil limiter employs ARP...
-

 294Vulnerabilities
294VulnerabilitiesCritical remote access vulnerability in Windows 10-prior versions
A couple of weeks ago Microsoft released a security patch to fix a remote-code execution vulnerability in its Remote Desktop Protocol (RDP)...






