Search results for "Antivirus"
-

 1.9KMalware
1.9KMalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
A new malware campaign has been exploiting the updating mechanism of the eScan antivirus software to distribute backdoors and cryptocurrency miners like...
-

 3.9KIncidents
3.9KIncidentsHow to exploit Windows Defender Antivirus to infect a device with malware
Trend Micro’s recent threat hunting efforts have uncovered active exploitation of CVE-2023-36025, a vulnerability in Microsoft Windows Defender SmartScreen, by a new...
-

 4.3KData Breach
4.3KData BreachDiscover Why Proactive Web Security Outsmarts Traditional Antivirus Solutions
In a rapidly evolving digital landscape, it’s crucial to reevaluate how we secure web environments. Traditional antivirus-approach solutions have their merits, but...
-
 1.1KTutorials
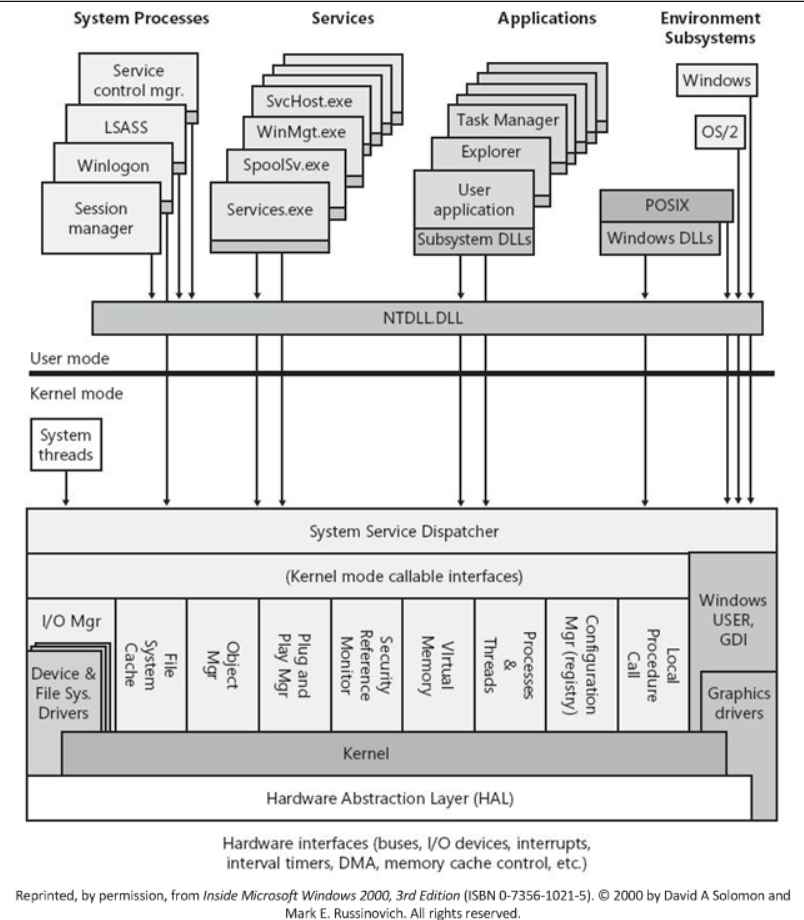
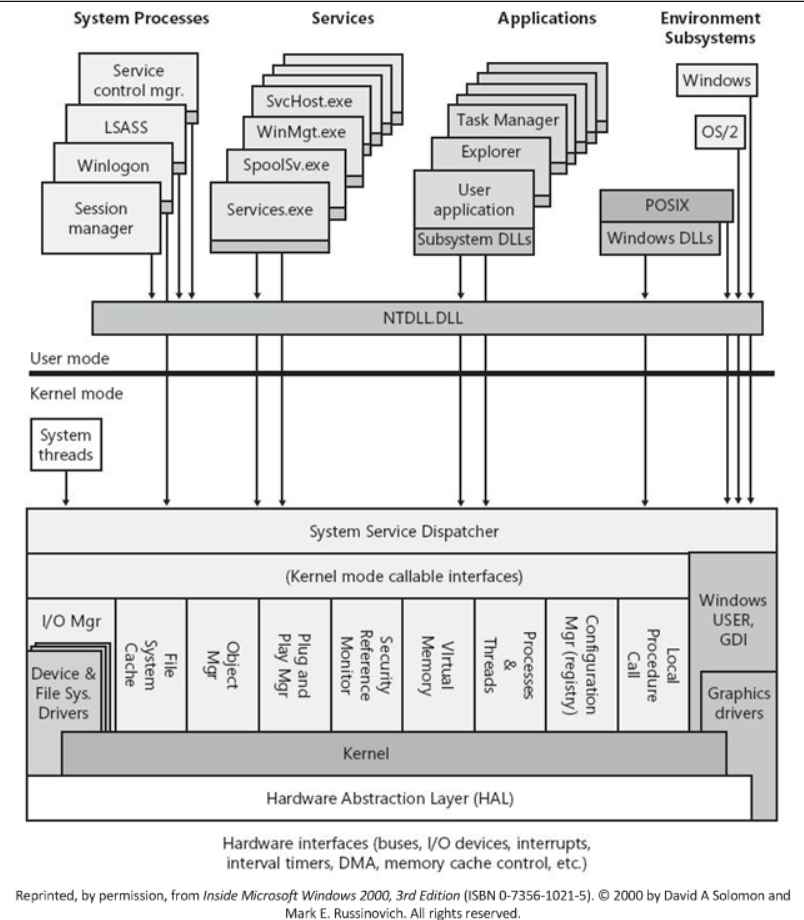
1.1KTutorialsNew Antivirus, EDR detection evading technique allows injecting code in trusted Windows process
Mockingjay is the name of an innovative process injection approach that has the potential to enable threat actors to avoid being detected...
-

 4.7KMalware
4.7KMalwareHow to use “bring your own vulnerable driver” (BYOVD) technique to kill/evade Antivirus or EDR
Threat actors have been relying on exploitable drivers an increasing amount in order to circumvent security measures. Drivers are low-level system components...
-

 3.6KMalware
3.6KMalwareMajority of the ransomware gangs used this packer to bypass antivirus and encrypt devices
Packers are becoming an increasingly important tool for cybercriminals to use in the commission of illegal acts. On hacker forums, the packer...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesNew Acer UEFI firmware vulnerability (CVE-2022-4020) makes Antivirus or EDR useless in Acer laptops
The security researchers at ESET found a new high-risk vulnerability in the UEFI firmware of Acer computers. Because to a security flaw...
-
Malware
Fake Antivirus and Cleaner Apps Caught Installing SharkBot Android Banking Trojan
The notorious Android banking trojan known as SharkBot has once again made an appearance on the Google Play Store by masquerading as...
-
 1.7KMalware
1.7KMalwareThis is how they use Windows Defender antivirus to encrypt your computer with LockBit Ransomware
Hackers are constantly looking for new ways to attack and infect PC users. And, for this, there is nothing better than taking...
-
 1.2KMalware
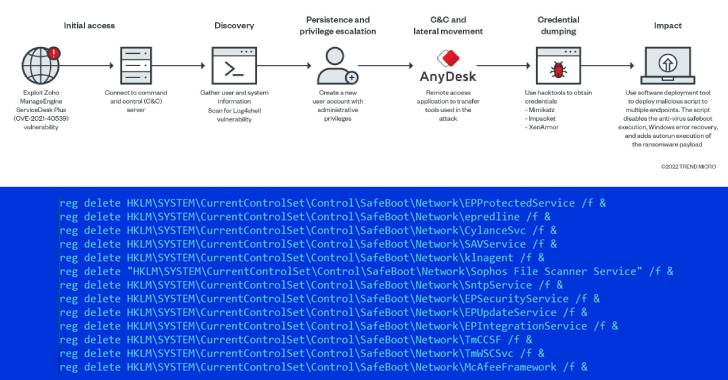
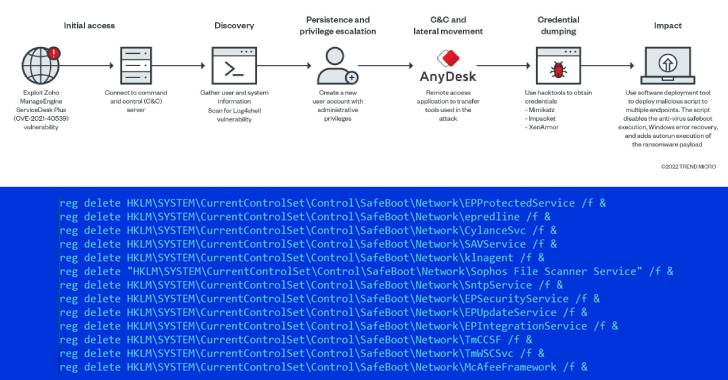
1.2KMalwareAvosLocker Ransomware Variant Using New Trick to Disable Antivirus Protection
Cybersecurity researchers have disclosed a new variant of the AvosLocker ransomware that disables antivirus solutions to evade detection after breaching target networks...
-
 1.3KMalware
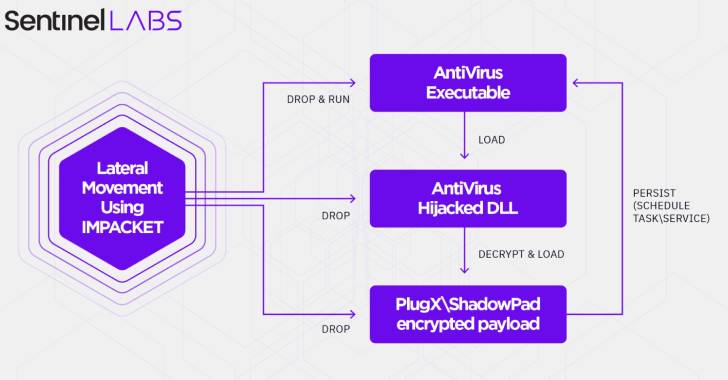
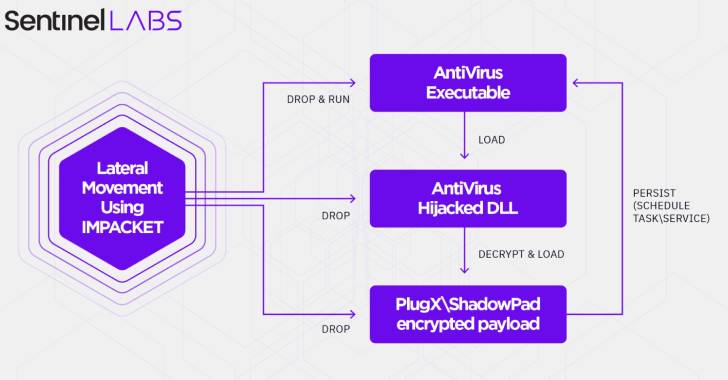
1.3KMalwareChinese Hackers Caught Exploiting Popular Antivirus Products to Target Telecom Sector
A Chinese-aligned cyberespionage group has been observed striking the telecommunication sector in Central Asia with versions of malware such as ShadowPad and...
-

 4.7KMalware
4.7KMalwareResearchers Takeover Unpatched 3rd-Party Antivirus Sandboxes via VirusTotal
Security researchers have disclosed a security issue that could have allowed attackers to weaponize the VirusTotal platform as a conduit to achieve...
-
 2.5KMalware
2.5KMalwareSharkBot – New Generation Malware on Google Play Distributed as Android Antivirus App
While malware distributors may have a harder time getting their malicious apps through Google’s automatic scanning and flagging system, but, SharkBot shows...
-

 4.6KVulnerabilities
4.6KVulnerabilitiesESET Antivirus Flaw Let Attackers to Escalate Privileges & Execute Arbitrary Code
ESET has recently published patches to fix a local privilege escalation vulnerability detected in all the clients of its Windows products that...
-
 1.4KMalware
1.4KMalwareBeware of Fake Amnesty International Antivirus for Pegasus that Hacks PCs with Malware
In yet another indicator of how hacking groups are quick to capitalize on world events and improvise their attack campaigns for maximum...
-

 637Malware
637MalwareThese 13 malware variants are used to hack and take control of Pulse Secure devices. Make sure your antivirus can detect them
In its most recent report, the Cybersecurity and Infrastructure Security Agency (CISA) alerted users of Pulse Secure devices to the discovery of...
-

 2.7KMalware
2.7KMalwareDroidMorph Shows Popular Android Antivirus Fail to Detect Cloned Malicious Apps
A new research published by a group of academics has found that anti-virus programs for Android continue to remain vulnerable against different...
-
 643Malware
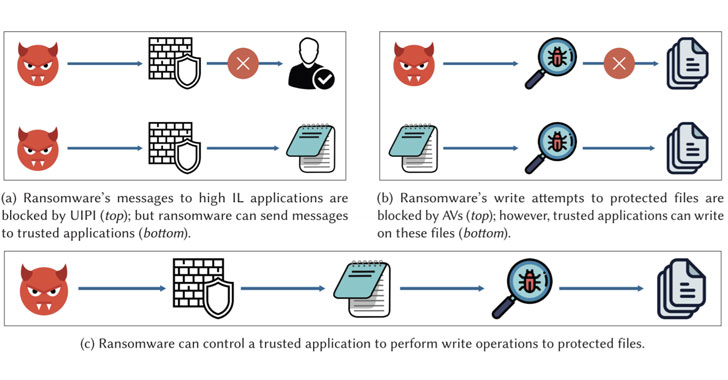
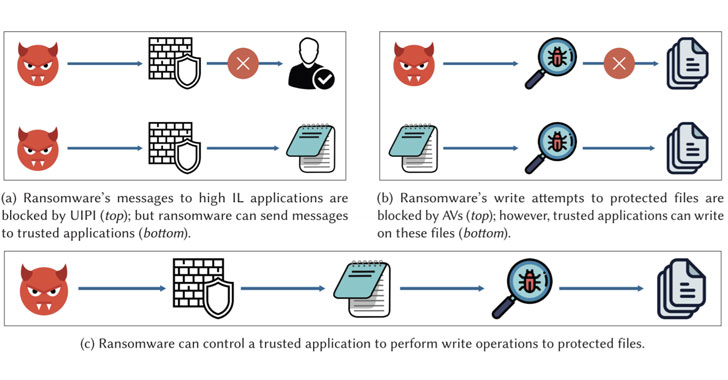
643MalwareMalware Can Use This Trick to Bypass Ransomware Defense in Antivirus Solutions
Researchers have disclosed significant security weaknesses in popular software applications that could be abused to deactivate their protections and take control of...
-

 802Data Breach
802Data BreachAntivirus Firm Exposed Internal Log data Generated by their Products
EMSISOFT, Antivirus Firm revealed a data breach on one of their test systems. The company used the system to evaluate and benchmark...
-

 3.3KTutorials
3.3KTutorialsHow to easily check if DOC, RTF, XLS, PPT, PPTX or PDF file has a malware without antivirus like a digital forensics expert
In most cyberattack variants threat actors use legitimate-looking documents loaded with malware, which is why researchers often say it all starts with...
-
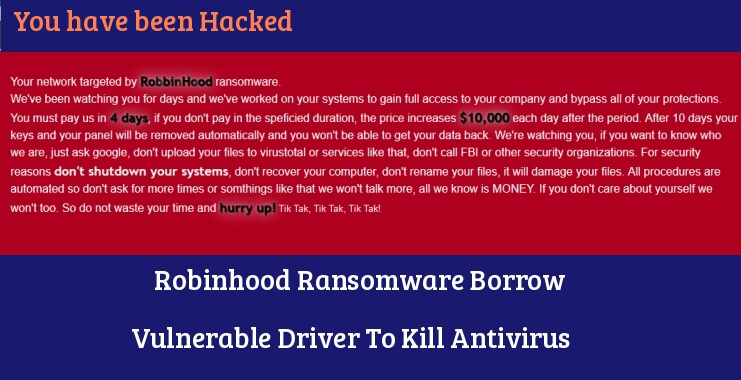
 2.6KRansomware
2.6KRansomwareRobinhood Ransomware Borrow Vulnerable Driver To Kill Antivirus and Encrypt Windows System Files
Researchers observed a new ransomware family called “Robinhood” that using a digitally signed vulnerable driver to bypass the protection by killing files...






