Search results for "Chrome"
-

 1.7KVulnerabilities
1.7KVulnerabilitiesUnpatched zero-day vulnerability Affecting Current Versions of Google Chrome & Microsoft Edge Published Online
In a daily investigating routine, a security researcher, Rajvardhan Agarwal from India has noted a new zero-day vulnerability code execution affecting major...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesAnother zero day vulnerability along with POC exploit in Google Chrome published
Just one day ago an exploit was reported to abuse a critical vulnerability in the Chromium open source project, employed by some...
-

 888Vulnerabilities
888VulnerabilitiesPOC published for Zero day vulnerability in Chrome and edge browser
A team of cybersecurity experts revealed a proof of concept (PoC) for exploiting a severe vulnerability residing in Chrome, Edge and other...
-

 5.2KVulnerabilities
5.2KVulnerabilitiesGoogle Fixed yet Another Actively Exploited zero-day Vulnerability in the Chrome Browser
Once again Google has fixed another Zero-day vulnerability in the Chrome browser, and this is the second vulnerability that has been recently...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesAnother Google Chrome 0-Day Bug Found Actively Exploited In-the-Wild
Google has addressed yet another actively exploited zero-day in Chrome browser, marking the second such fix released by the company within a...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesNew Chrome 0-day Bug Under Active Attacks – Update Your Browser ASAP!
Exactly a month after patching an actively exploited zero-day flaw in Chrome, Google today rolled out fixes for yet another zero-day vulnerability...
-

 2.2KMalware
2.2KMalwareMalvertising campaign affects users of Safari and Chrome browsers
A malvertising campaign operator group known as ScamClub has long exploited an unpatched zero-day vulnerability in some WebKit-based web browsers in order...
-
 1.4KPassword
1.4KPasswordGoogle adds password breach alerts to Chrome for Android, iOS
The feature is part of the browser's security improvements that were first built into its desktop version
-

 2.6KWeb Hacking
2.6KWeb HackingWhy Google Put A Halt On The Chrome And OS Updates?
Whenever you come across a problem, Google it! Yes, this is what the 310 million people believe in when they want to...
-

 4.1KPrivacy
4.1KPrivacyGoogle to end support for third‑party cookies in Chrome
The company will also soon launch anti-fingerprinting measures aimed at detecting and mitigating covert tracking and workarounds
-

 2.6KNews
2.6KNewsKaspersky reveals hackers use both Windows 10 and Google Chrome zero-day vulnerabilities to launch attacks
Both Microsoft and Google have released software updates yesterday to fix some security vulnerabilities, including a zero-day vulnerability that has been exploited...
-

 908Password
908PasswordChrome now warns you if your password has been stolen
The browser’s latest version also aims to up the ante in phishing protection
-

 623News
623NewsChrome 79 Released With Tab Suspender To Fix ‘High CPU Usage’
Despite being the most popular browser on the planet, if there is one thing that Google hasn’t been able to fix, it’s...
-

 4.2KNews
4.2KNewsChrome, Edge, Safari were beaten by white hats in Chinese hacking contest
Last weekend, the Chinese hacking contest, Tianfu Cup officially began in Chengdu, and hackers from China won the championship in this war....
-

 3.7KMalware
3.7KMalwareNew Malware Attack Drops Double Remote Access Trojan in Windows to Steal Chrome, Firefox Browsers Data
Researchers discovered a new malware campaign that drops two different Remote Access Trojan(RAT) on targeted Windows systems and steal sensitive information from...
-

 2.1KReviews
2.1KReviewsBrave Browser 1.0: Why Switch To This Privacy-Focused Chrome Alternative?
If you would ask me what app do you use the most on your computer, then I’d quickly name a web browser....
-

 3.2KNews
3.2KNewsHow To Enable DNS-Over-HTTPS On Chrome, Firefox, Edge, Brave?
The DNS-over-HTTPS (DoH) protocol has been a hot topic for debate for a few months. The protocol encrypts DNS queries and adds...
-
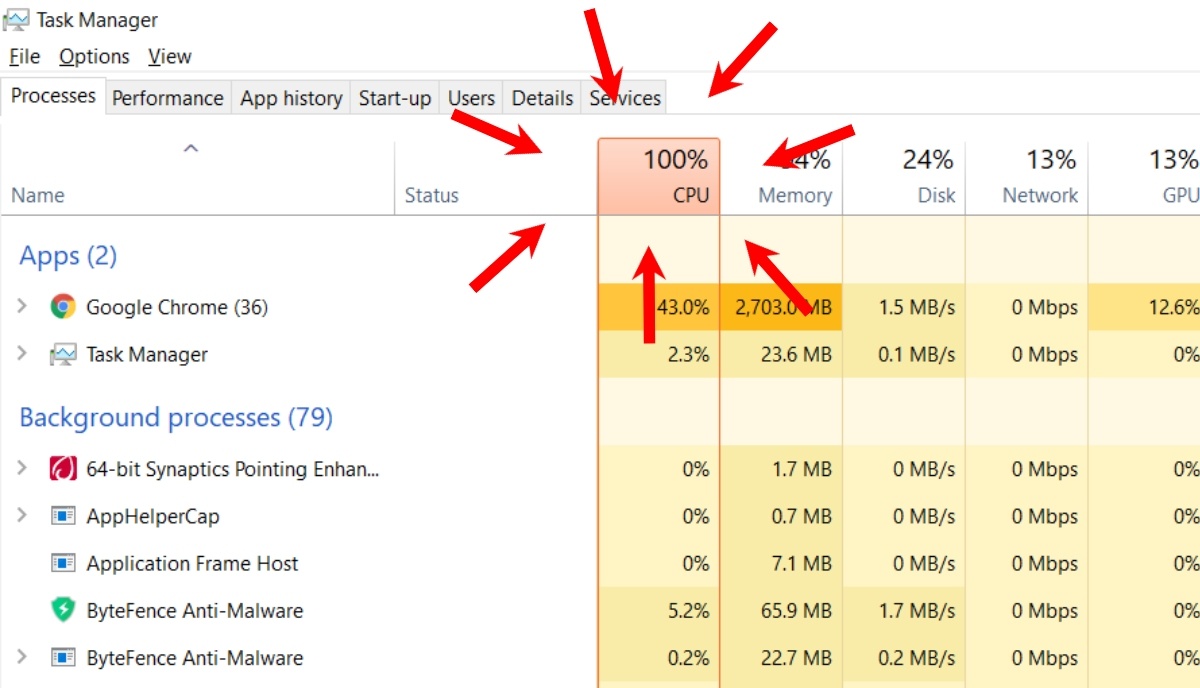
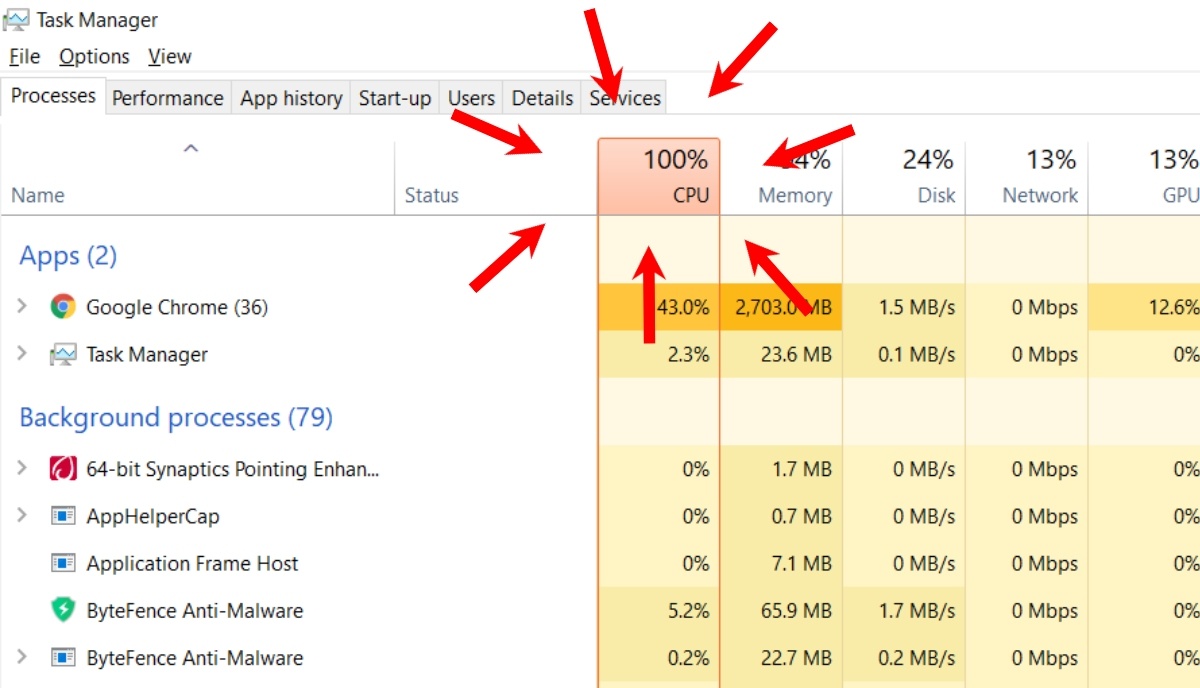 4.7KHow To
4.7KHow ToHow To Remove Software Reporter Tool To Fix Google Chrome High CPU Usage?
Google Chrome is one of the most popular browsers available right now. Since it includes all the necessary features, Chrome users tend...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesChrome zero-day vulnerability released; update as soon as possible
Web application security specialists reported the appearance of two dangerous vulnerabilities in the Chrome browser, in addition to the active exploitation of...
-

 572Data Security
572Data SecurityHackers found tracking web traffic of Chrome and Firefox browsers
Two user favorite browsers are commonly known to be Google Chrome and Mozilla Firefox. Exploiting their demand, a Russian group by the...
-
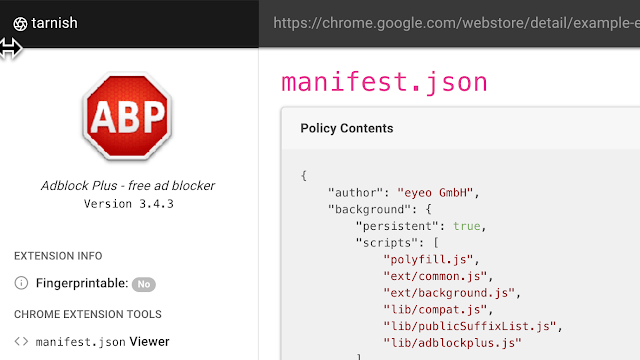
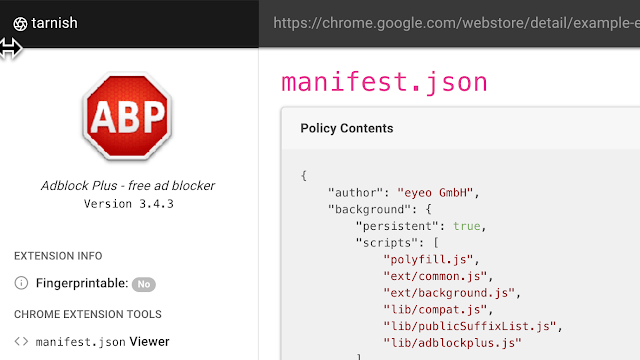 503Vulnerability Analysis
503Vulnerability AnalysisTarnish – A Chrome Extension for Static Analysis
tarnish is a static-analysis tool to aid researchers in security reviews of Chrome extensions. It automates much of the regular grunt...






