Search results for "Cloud"
-
 361Data Security
361Data SecurityParrot Security 4.0 The new tool for Cloud and IoT Pentesting
After a fairly long development process and quite a few updates, the release is ready; Parrot 4.0 is now available for download....
-

 210Data Security
210Data SecurityMy Cloud EX2 device from Western Digital leaks files by default
According to research conducted by information security professionals at Trustwave, Western Digital’s My Cloud EX2 storage devices filter files to anyone in...
-

 276Geek
276GeekGerman Government Chooses Open Source For Its Federal Cloud Solution
It’s not hidden that apart from costing tons of money, the use of proprietary software also brings along hidden security caveats. These...
-
 291DDOS
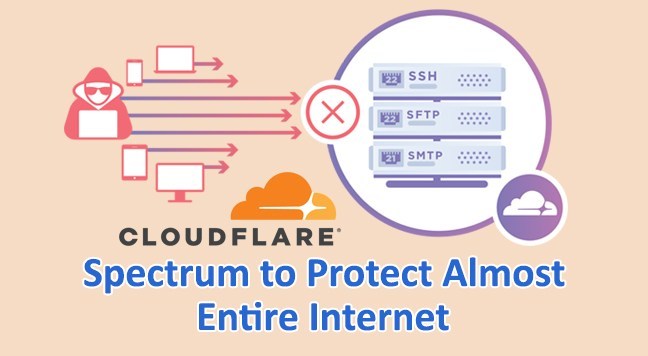
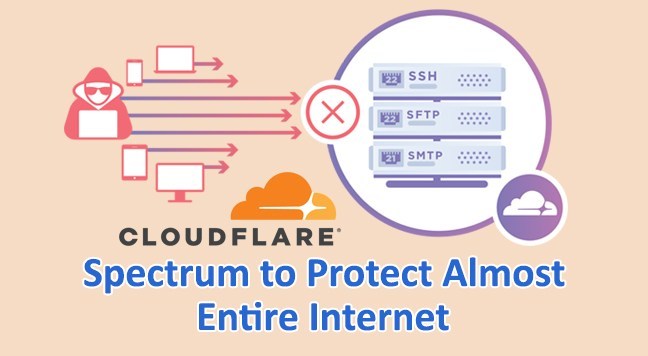
291DDOSCloudflare Launches Spectrum to Protect Almost Entire Internet
Cloudflare introduces Spectrum to protect any services that connected to the Internet. Spectrum works in the same way as the Cloudflare and it...
-

 247Incidents
247IncidentsInvestigators Hijack Over 2,000 Subdomains in CloudFront Experiment
Information security training experts from MindPoint Group, an information security firm, have hijacked over 2,000 subdomains from legitimate websites while researching possible...
-

 322Bruteforcing
322BruteforcingiCloudBrutter – AppleID Bruteforce
iCloudBrutter is a simple python (3.x) script to perform basic bruteforce attack againts AppleID. Usage of iCloudBrutter for attacking targets without prior...
-

 303Malware
303MalwareGozi Trojan Becomes Dark Cloud Botnet
The widely distributed Gozi ISFB banking Trojan has a new trick up its sleeve; it has been making use of the evasive...
-

 318Information Gathering
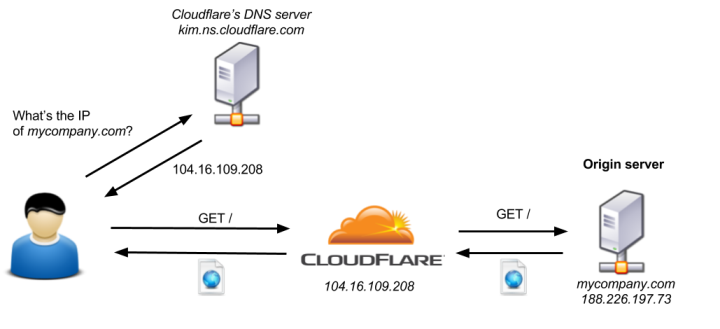
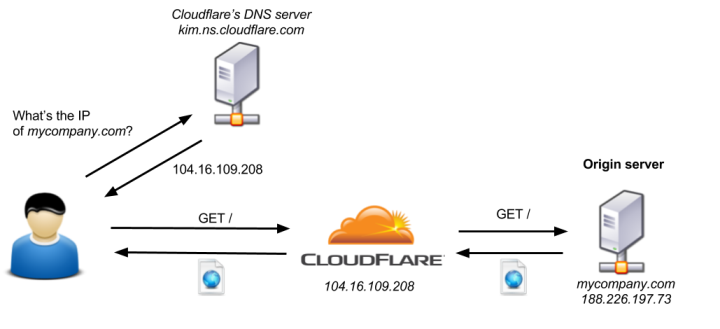
318Information GatheringHow to Bypass Cloudflare with HatCloud – Kali Linux 2018.1
HatCloud is built in Ruby. It tries to bypass CloudFlare and discover real IP. This can be useful if you need to...
-

 172Hacked
172HackedHackers Take Control of Tesla’s Cloud Account To Mine Cryptocurrency
While Elon Musk might be busy making plans to take humans to Mars and impress people with SpaceX’s upcoming internet satellite launch,...
-

 279Malware
279MalwareTesla cloud resources are hacked to run cryptocurrency-mining malware
Crooks find poorly secured access credentials, use them to install stealth miner. Add Tesla to the legion of organizations that have been...
-
 335News
335NewsHackers Compromise Tesla Cloud Server to Mine Cryptocurrency
It is 2018 and the easiest way to make quick money at someones else’s expense is mining cryptocurrency. This time, however, researchers...
-

 389Incidents
389IncidentsPublic clouds like Dropbox, OneDrive or Google Drive do not protect our data properly from malware
Every day we hear news of more malware endangering the information security of users. Therefore, the main companies, such as Dropbox, Google...
-
 234Vulnerabilities
234VulnerabilitiesCloudFlair: Bypassing Cloudflare using Internet-wide scan data
Cloudflare is a service that acts as a middleman between a website and its end users, protecting it from various attacks. Unfortunately,...
-
 217Malware
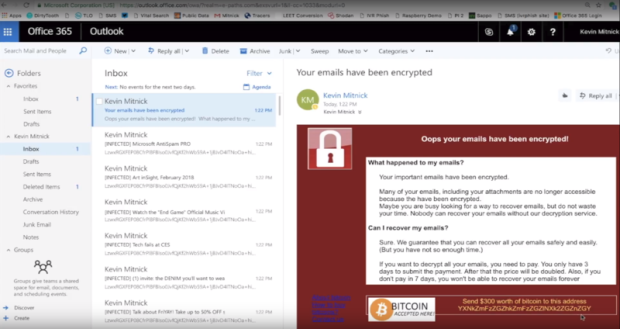
217Malware[Heads-up] Unusual Ransomware Strain Encrypts Cloud Email Real-time VIDEO
KnowBe4’s Chief Hacking Officer Kevin Mitnick called me with some chilling news. A white hat hacker friend of his developed a working “ransomcloud” strain, which...
-
 308News
308NewsFourth Fappening Hacker Admits to Stealing Celebrity Pics From iCloud Accounts
Almost three years after the massive leakage of high-profile celebrities’ nude photos—well known as “The Fappening” or “Celebgate” scandal—a fourth hacker has...
-
 246System Administration
246System AdministrationCloud Security Suite – AWS infrastructure Security Auditing
CS Suite is a one stop tool for auditing the security posture of the AWS infrastructure and does system audits as well....
-

 209Vulnerabilities
209VulnerabilitiesEMC, VMware security bugs throw gasoline on cloud security fire
Backups of virtual machines on some hosts could be accessed or altered by an attacker. While everyone was screaming about Meltdown and Spectre,...
-

 420Hacked
420HackedHardcoded Backdoor Found In WD My Cloud NAS With Username “MyDlink”
In yet another revelation of severe loopholes, a security researcher James Bercegay from Gulftech has discovered a backdoor in some models of...
-

 245Articles
245ArticlesA hard-coded vulnerability was discovered in WD my Cloud NAS Devices
It’s time to learn how to renew its OS because researcher James Bercegay has found a dozen models possess a hard-coded backdoor....
-

 116Geek
116GeekMeltdown and Spectre Flaws Collateral Damage to OS & Cloud Services Unavoidable
Meltdown and Spectre vulnerabilities haunting users and Tech Giants worldwide – Now the Giants have addressed the issue. Recently, we reported about...
-
 200Data Security
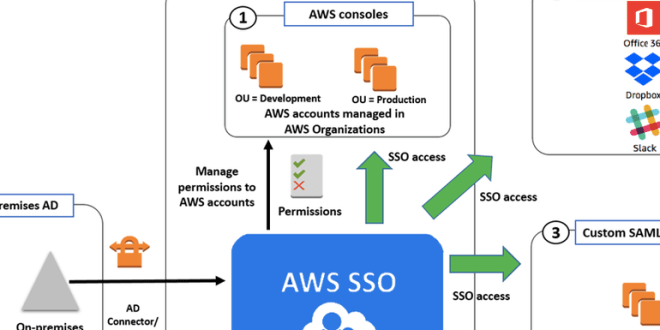
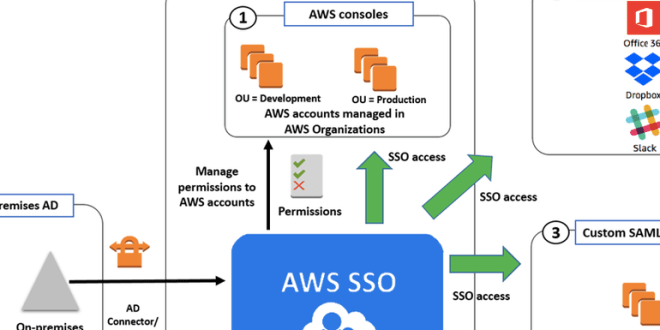
200Data SecurityAmazon launches single sign-on service for AWS cloud
AWS SSO will let users manage access to multiple AWS accounts and applications using their existing corporate credentials. Amazon Web Services’ re:Invent...






