Search results for "Cloud"
-
 248Vulnerabilities
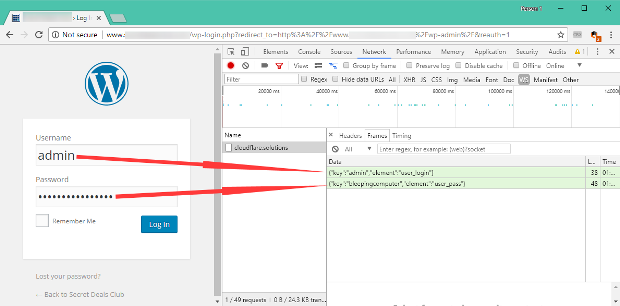
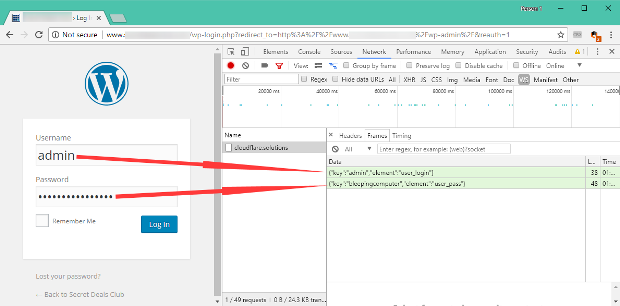
248VulnerabilitiesCloudflare[.]Solutions Keylogger on Thousands of Infected WordPress Sites
A few weeks ago, we wrote about a massive WordPress infection that injected an obfuscated script pretending to be jQuery and Google Analytics. In...
-

 370Data Security
370Data SecurityUnprotected S3 Cloud Bucket Exposed 100GB of Classified NSA Data
Another day another massive trove of sensitive NSA data exposed online – This time, security firm UpGuard’s Cyber Risk team has identified...
-

 187Cyber Crime
187Cyber CrimeCloud-Delivered Cybersecurity
When John Graham joined Jabil four years ago as its first Chief Information Security Officer (CISO), he found an IT environment that...
-

 389Phishing
389PhishingBeware!! Hackers Using New Tools to Break open Apple iCloud Accounts to Unlock Stolen iPhone’s
A New Phishing and scam tools are discovered that used by the cyber criminal to unlock the physically stolen iPhones by compromising...
-

 213Uncategorized
213UncategorizedHelios 4 NAS – Worlds First Open Source Personal Cloud 2017
Cloud file sharing provides end users with the ability to access files with any Internet-capable device from any location. But when larger...
-
 249Pentest Linux Distributions
249Pentest Linux DistributionsParrot Security 3.9 – Security GNU/Linux Distribution Designed with Cloud Pentesting and IoT Security in Mind
Security GNU/Linux distribution designed with cloud pentesting and IoT security in mind. It includes a full portable laboratory for security and digital...
-

 364TOR
364TORORC – Onion Routed Cloud
Onion Routed Cloud is a decentralized, anonymous, object storage platform owned and operated by allies in defense of human rights and opposition...
-
Security Tools
Cloud Security Suite – One stop tool for auditing the security posture of AWS infrastructure
One stop tool for auditing the security posture of AWS. Pre-requisites Python 2.7 pip git Installation git clone https://github.com/SecurityFTW/cs-suite.git cd cs-suite/ sudo...
-
 261Vulnerability Analysis
261Vulnerability AnalysisBlazy – Modern Login Bruteforcer Which Also Tests For CSRF, Clickjacking, Cloudflare and WAF
Blazy is a modern login page bruteforcer. Features Easy target selections Smart form and error detection CSRF and Clickjacking Scanner Cloudflare and...
-
 244Cryptography and Encryption
244Cryptography and EncryptionCryptomator – Cloud Client Side File Encryption
Multi-platform transparent client-side encryption of your files in the cloud. Cryptomator provides transparent, client-side encryption for your cloud. Protect your documents from...
-
 202Articles
202ArticlesWebsites using Cryptocurrency Miners will be banned by CloudFlare
Pirate Bay got this the hard way when users on Reddit lately complained regarding the site’s use of such miners. The website...
-

 362Data Security
362Data SecurityCloudFlare Boots Off Torrent Site For Using Cryptocurrency Miner
CloudFlare says sites running mining code without notifying users are considered to be malware. In the last couple of weeks, researchers discovered an increasing...
-

 474Data Security
474Data SecurityAzure confidential computing: Microsoft boosts security for cloud data
Microsoft is rolling out new secure enclave technology for protecting data in use. Microsoft has opened an early access program for a...
-

 246Trojan / Worms
246Trojan / WormsBeware !! Dangerous RAT’s Called “Adwind, Remcos, Netwire” Delivering via A360 Cloud Drive
Widely Used A360 Cloud Drive Platform Abuse for Delivering Adwind, Remcos, Netwire Remote Access Trojans and used as a Malware Distributing Platform...
-
 252Hacked
252HackedFappening 2017: Danielle Lloyd’s Private Pictures Leaked Online After iCloud Hack
British model Danielle Lloyd’s private pictures have leaked online on an X-rated website. As a result, Danielle, 33, had contacted police and...
-

 313Cyber Crime
313Cyber CrimeRussia boots off DailyStormer and CloudFlare removes DDoS protection
It looks like the racist and neo-nazi website DailyStormer has no place left on the regular Internet. A few days ago the website...
-

 831Privacy
831PrivacyHuawei Roots for Cloud Computing to Ensure Data Protection
Huawei seems to be rooting for cloud computing as a strong measure to ensure better data protection, for governments as well as...
-
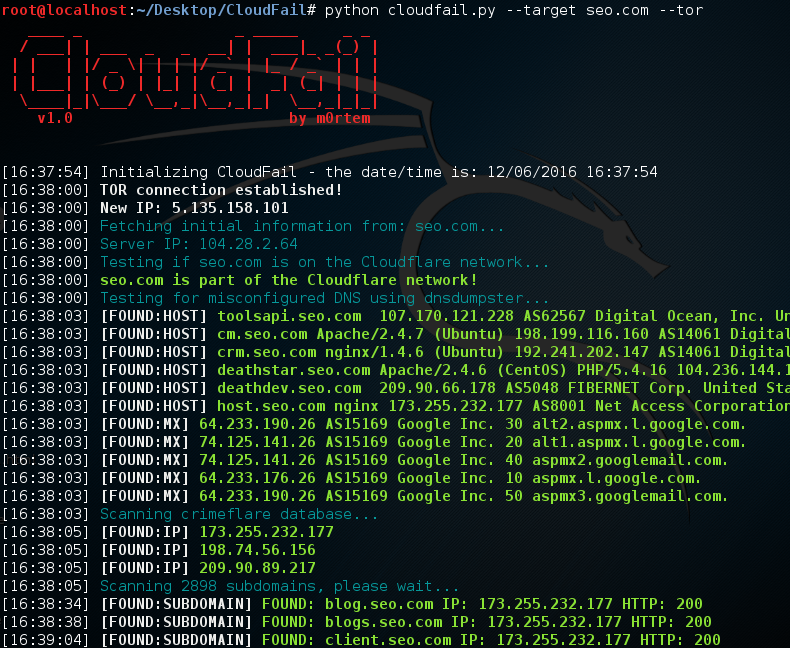
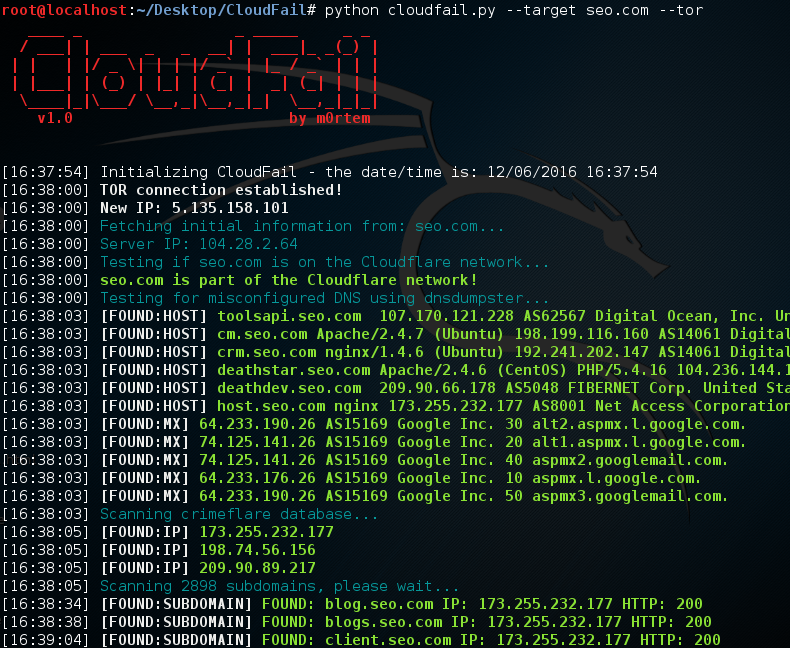 206Hackers Repository
206Hackers RepositoryCloudFail – Utilize misconfigured DNS Find hidden IP’s behind the CloudFlare network
CloudFail Credits: m0rtem CloudFail is a tactical reconnaissance tool which aims to gather enough information about a target protected by CloudFlare in...
-

 199Hackers Repository
199Hackers RepositoryHow to Grab a IP Address Using Fake Cloud Hosting Service
How to Grab IP Address Using Fake Cloud Hosting Service Welcome back today we will be looking in to grabbing IP address’s...
-

 123Vulnerabilities
123VulnerabilitiesApple iCloud, Android Nvidia driver N-day exploit details revealed
Kernels can be exploited and iCloud account user information leaked due to the security flaws. Zimperium has released the public details of...
-

 160Vulnerabilities
160VulnerabilitiesiCloud Keychain vulnerability allowed hackers to Steal sensitive data
Apple has recently fixed an iCloud Keychain vulnerability that could have been exploited by hackers to steal sensitive data from iCloud users....






