Search results for "Firewall"
-

 4.0KData Security
4.0KData SecurityNew phishing technique uses advanced obfuscation and Telegram channels to evade detection. Hackers can easily bypass your firewall
The specialized team FireEye Email Security has published a report on the detection of multiple phishing campaigns in which operators use source...
-
 2.9KHackers Repository
2.9KHackers RepositoryWindowsFirewallRuleset: Windows firewall ruleset powershell scripts
Windows Firewall Ruleset Windows firewall rules organized into individual powershell scripts according to: Rule group Traffic direction IP version (IPv4 / IPv6)...
-

 1.9KIncidents
1.9KIncidentsCheck Point firewall ZoneAlarm suffers data breach incident
According to information security specialists, ZoneAlarm, the firewall software produced by security firm Check Point, was the victim of a data breach...
-

 425Vulnerabilities
425VulnerabilitiesCritical Vulnerability in Cyberoam Firewall, by Sophos: Patch now available
Vulnerability testing specialists report the finding of a critical vulnerability in the Sophos hardware and software company’s firewall solutions. If exploited, this...
-
 376Enumeration
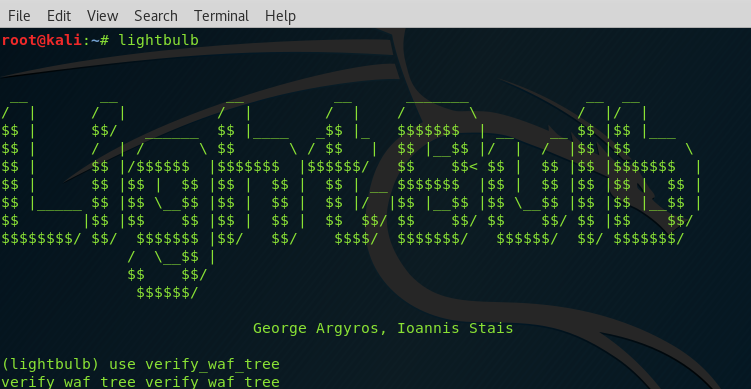
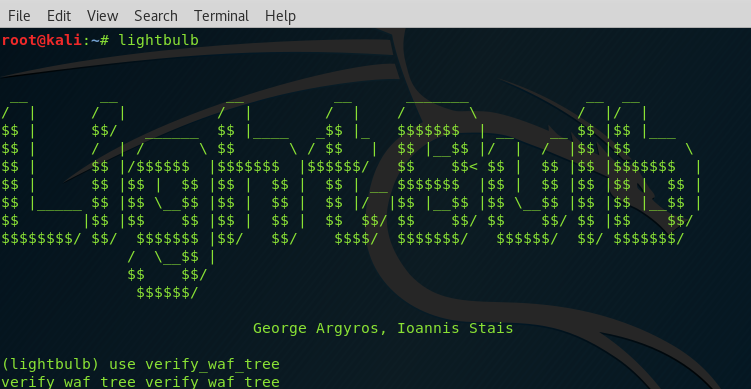
376EnumerationLightbulb – Framework for Auditing Web Applications Firewalls
LightBulb is an open source python framework for auditing web application firewalls and filters. Web Applications Firewalls (WAFs) are fundamental building blocks...
-
 504Malware
504MalwareHow CAPTCHA is being used to bypass anti malware security scans and firewalls
The Completely Automated Public Turing test to tell Computers and Humans Apart, most commonly known as CAPTCHA, is a system for creating...
-

 424Vulnerabilities
424VulnerabilitiesCritical vulnerability discovered in Check Point firewall
Web application security specialists report the discovery of a critical vulnerability in a Check Point software solution that, if exploited, would allow...
-

 388Incidents
388IncidentsNew York government paid $88k USD due to ransomware attack despite having firewall and antivirus solutions
Even though the complex cybersecurity solutions currently available on the market, a system, network, or computer will never be 100% protected against...
-
 320News
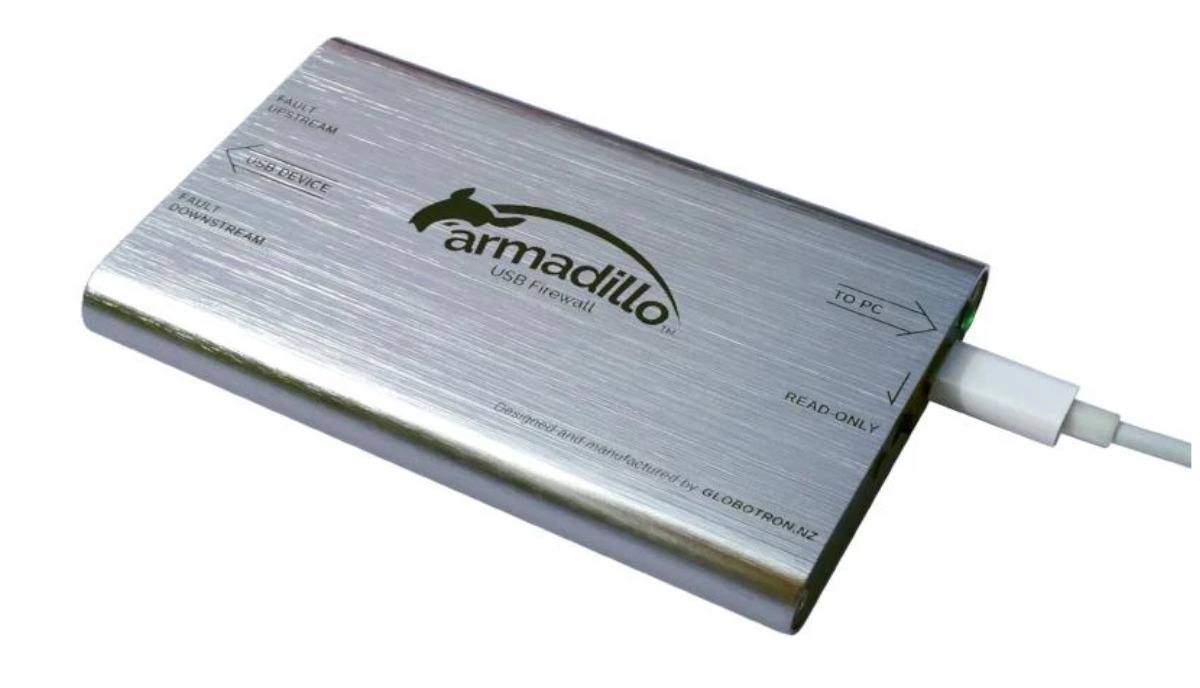
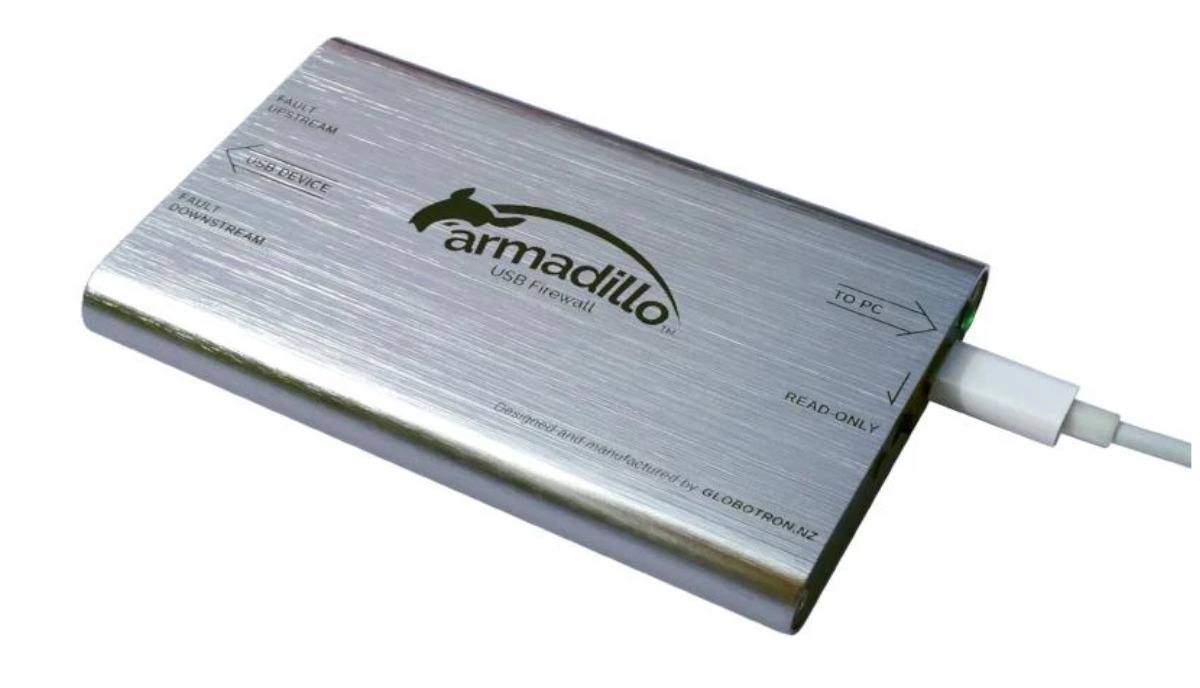
320NewsArmadillo Is An Open-Source “USB Firewall” Device To Protect You Against USB Attacks
Exchanging data using USB devices is something that we do on a daily basis. But how often do you think that the...
-

 332Hack Tools
332Hack ToolsWAFNinja – Tool to Bypass Web Application Firewalls
WAFNinja is a CLI tool written in Python and helps penetration testers to bypass a WAF by automating steps necessary for bypassing...
-

 213How To
213How ToHow to build a “human firewall” for your business
What is a human firewall? In cyber security, a firewall is software that is designed to prevent network intruders. Thus, a human...
-
 297Data Security
297Data SecurityHackers are using ‘network tunneling’ to bypass the firewall instead of RDP
Network tunneling technique is being increasingly used for attackers using RDP The Remote Desktop Protocol (RDP) is a Windows component designed to...
-

 348Tutorials
348TutorialsDetect Web Application Firewall (WAF) before you attack
WEB APPLICATION FIREWALL BASICS:- WAF (Web application firewalls) plays an important role in securing the websites. As they filter/monitor the traffic. Web...
-

 299News
299NewsThe Highly Competitive Web Application Firewall Market
The Internet continues to be a rich environment for vulnerability scans against weak websites and web hosting facilities. Businesses with a web...
-

 320Data Security
320Data SecurityMikroTik router vulnerability lets hackers bypass firewall to load malware undetected
Tenable Research’s cybersecurity researcher has released “By The way,” which is a new PoC (proof-of-concept) RCE attack after identifying a new attack...
-

 216Firewall
216FirewallLuLu v1.1.1 released: free open-source macOS firewall
LuLu is the free open-source macOS firewall that aims to block unauthorized (outgoing) network traffic unless explicitly approved by the user: Full...
-
 486Infosec
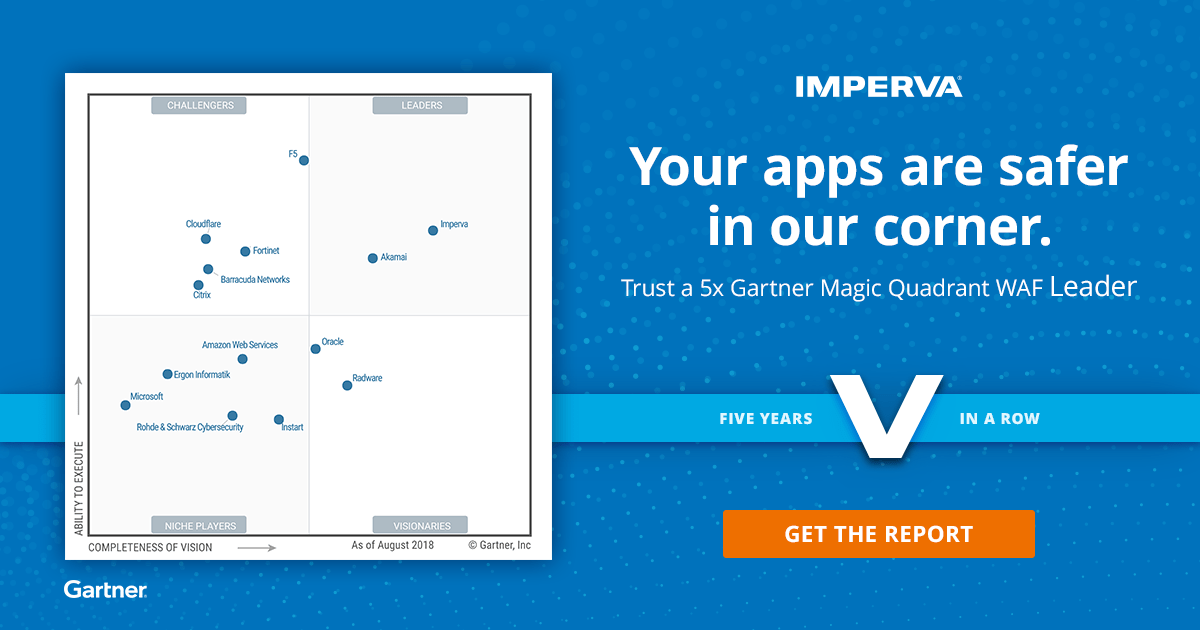
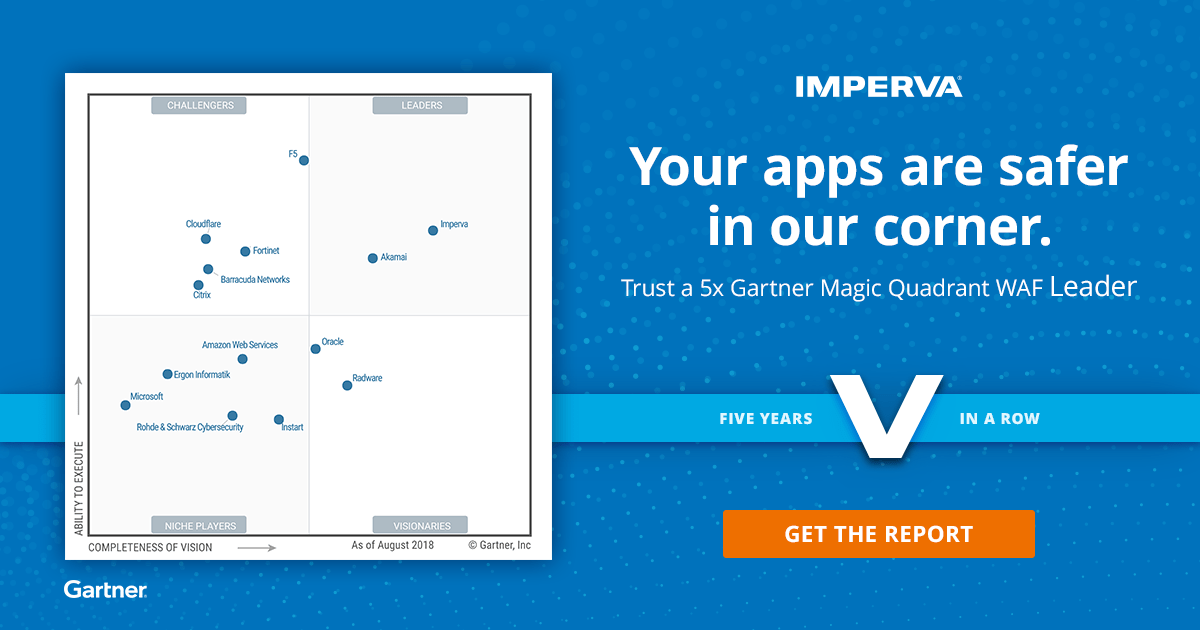
486InfosecGartner Released Magic Quadrant for Web Application Firewalls – Imperva WAF Selected as a #1 Best WAF
Currently Web Application Firewall performing a major role in Web application protection since the web applications are primary targets for cybercriminals and...
-

 246How To
246How ToThe Two Biggest Disruptions To Cybersecurity Since The Invention Of The Firewall
Many feel that the firewall is the most major development in the past thirty years or so of cybersecurity history. Since its...
-
 350Security Tools
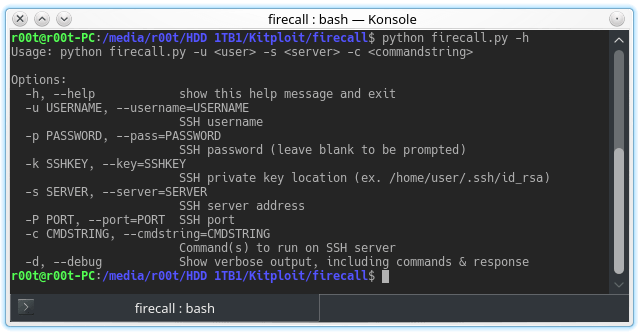
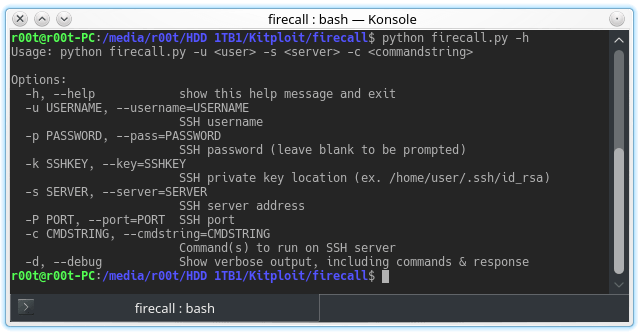
350Security ToolsFirecall – Automate SSH Communication With Firewalls, Switches, Etc.
Automate SSH communication with firewalls, switches, etc. Description These scripts are designed to automate sending commands to a Cisco ASA firewall. The...
-
 160Malware
160MalwareMyloBot – Highly Sophisticated Botnet Shutdown Windows Defender & Blocking Ports on the Firewall
Newly uncovered complex MyloBot Botnet incorporates different malicious techniques and ability to shut down the Windows Defender and Windows Updates. Basically, botnet do...
-
 459Data Security
459Data SecurityFirewalls: What They Are & Why You Need Them
There are some phrases that you hear bandied about, and you think that you know what they are. You have a basic...






