Search results for "Leaks"
-

 252Security Tools
252Security ToolsGlobaLeaks – The Open-Source Whistleblowing Software
GlobaLeaks is open-source / free software intended to enable secure and anonymous whistleblowing initiatives developed by the Hermes Center for Transparency and...
-
 289Password Attacks
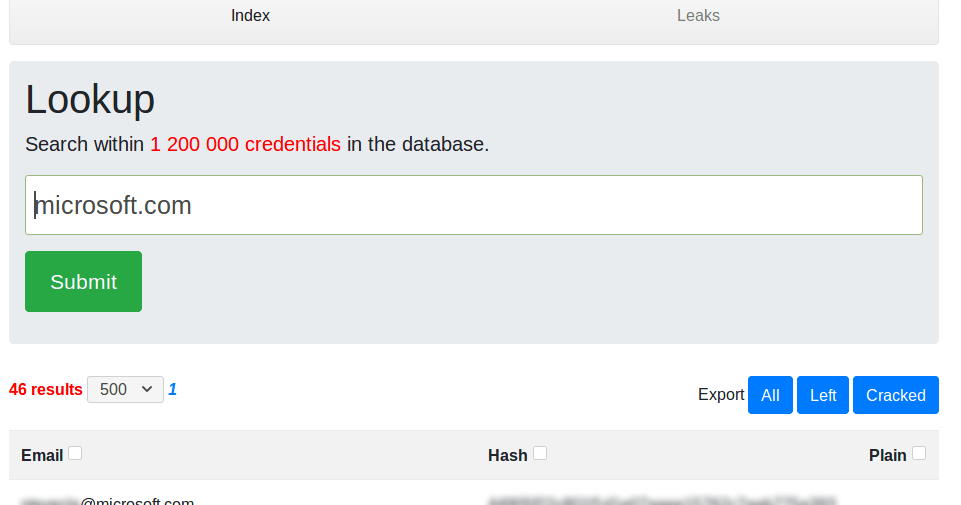
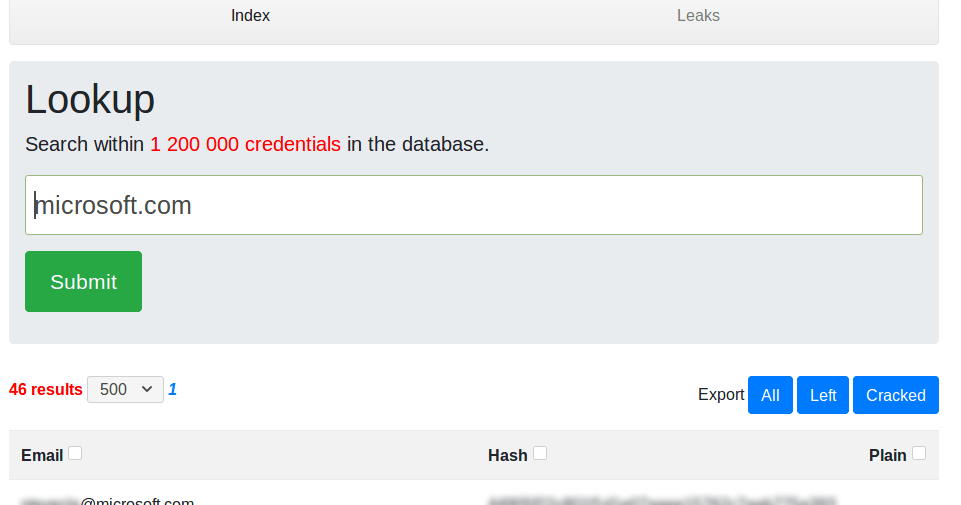
289Password AttacksLeakScraper – An Efficient Set Of Tools To Process And Visualize Huge Text Files Containing Credentials
LeakScraper is an efficient set of tools to process and visualize huge text files containing credentials. These tools are designed to help...
-

 445News
445NewsTicketfly website hacked & offline after hacker leaks customer data
Eventbrite-owned San Francisco, California based ticket distribution service Ticketfly’s website has been hacked and defaced – The company has acknowledged the hack...
-

 165Hacked
165HackedTeensafe, A Teen Phone Monitoring App, Leaks Thousands Of Apple ID Passwords
Teensafe is a monitoring app used by parents for keeping a check on the activities of their children. The app allows parents...
-

 600Data Security
600Data SecurityFormer CIA engineer leaked to WikiLeaks the hacking tools used by the Agency
A former CIA engineer is being accused of handing the documents from the Vault 7 series to WikiLeaks. The US government claims...
-
 254Data Breach
254Data BreachU.S Identified the Suspect Who Behind the major CIA Hacking Tools Leak and Provide to WikiLeaks
The U.S Finally identified the suspect who involved the CIA Vault 7 Hacking Tool leaks that contains the Powerful cyber weapons that...
-
 328News
328NewsFormer CIA engineer allegedly leaked Vault 7 documents to WikiLeaks
The suspect is CIA’s very own former engineer accused of handing over Vault 7 series documents to WikiLeaks. The government of United States...
-

 223Data Security
223Data SecurityMy Cloud EX2 device from Western Digital leaks files by default
According to research conducted by information security professionals at Trustwave, Western Digital’s My Cloud EX2 storage devices filter files to anyone in...
-

 214News
214NewsFacebook Is Offering $40,000 If You Find Evidence Of Facebook Data Leaks
Facebook launched a rewards program to reward users who report about Facebook Data Leaks after the Cambridge Analytica scandal.Facebook pays millions of...
-

 171Incidents
171IncidentsExplosive Facebook Memo Leaks: Top Exec Defended Growth Even If People Get Killed
Facebook Vice President Andrew “Boz” Bosworth is known for being blunt and direct at Facebook’s meetings. His Twitter description calls him “co-inventor...
-

 370Incidents
370IncidentsSgxSpectre Exploits Recent Intel CPU Flaw And Leaks “Enclave” Secrets
In modern Intel processors, there’s a hardware extension available named Software Guard Extension (SGX) to improve the security aspects. It provides a...
-

 258System Administration
258System AdministrationGlobaLeaks – Open-Source Whistleblowing Framework
GlobaLeaks is an open-source, free software intended to enable secure and anonymous whistleblowing initiatives developed by the Hermes Center for Transparency and Digital Human...
-

 311News
311NewsReddit user leaks alleged Game of Thrones Season 8 script pages
Game of Thrones season 7 was marred by hacks and leaks to such an extent that apart from seasonal spoilers, hackers managed...
-

 149Incidents
149IncidentsHow Memory Leaks Happen in a Java Application
Introduction to Memory Leaks In Java Apps One of the core benefits of Java is the JVM, which is an out-of-the-box memory management....
-
 341News
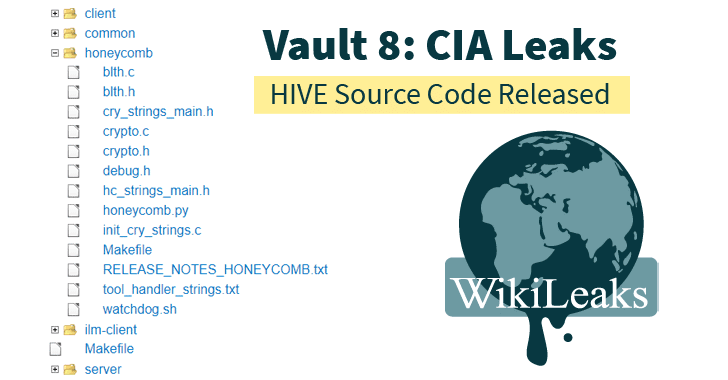
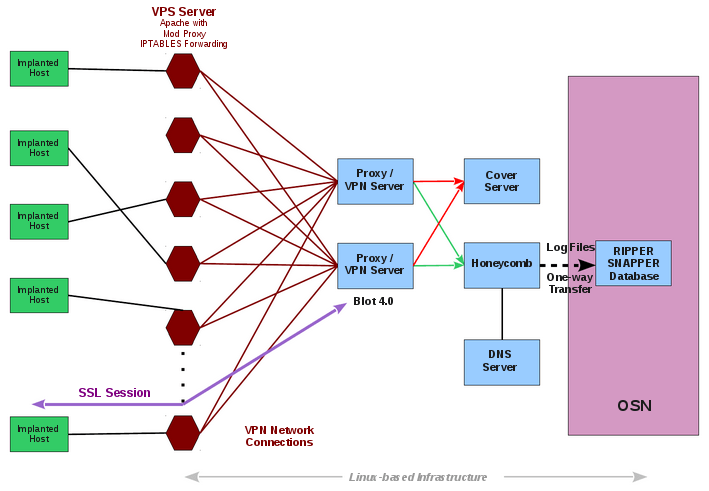
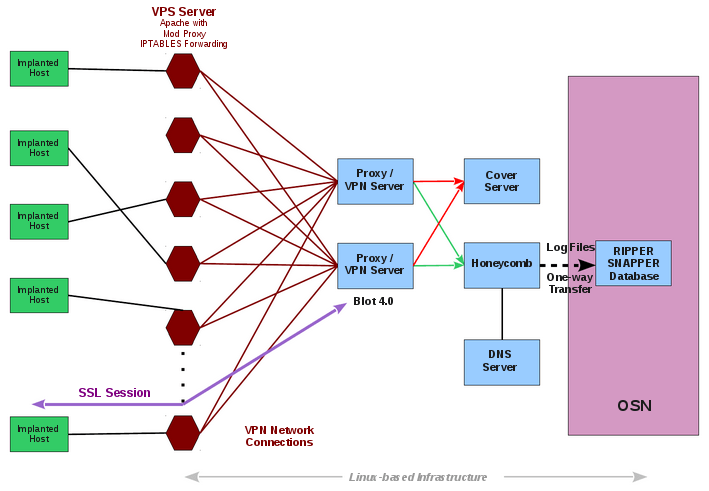
341NewsVault 8 – Cia Leaks Project Hive Source Code
Almost two months after releasing details of 23 different secret CIA hacking tool projects under Vault 7 series, Wikileaks today announced a...
-
 447Hacked
447HackedSource Code For CIA’s Spying Tool Hive Released By Wikileaks: Vault 8
As a part of its Vault 7 series, in mid-April, Wikileaks dropped a leak that contained six new documents revealing a CIA...
-
 332Malware
332MalwareVault 8 – WikiLeaks releases source code for CIA Hive malware control platform
Wikileaks released the first batch of documents starting with the source code and development logs of the Project Hive. Today the popular whistleblower organization Wikileaks...
-
 326News
326NewsWikiLeaks’ Vault 8 Leaks Show CIA Impersonated Kaspersky Lab
Wikileaks released the source code for Hive on Thursday, a CIA (Central Intelligence Agency) implants used in transferring exfiltrated information from target Windows...
-
 355Articles
355ArticlesWikiLeaks Publishes the Source Code and Development logs to Hive, a major component of the CIA infrastructure to Control its Malware
Today, 9 November 2017, WikiLeaks publishes the source code and development logs to Hive, a major component of the CIA infrastructure to...
-
 243News
243NewsCritical Tor Browser Vulnerability Leaks User’s Real IP Address
A critical Tor Browser vulnerability that could transmit their real IP addresses to possible attackers when they visit certain types of web...
-
 261Vulnerabilities
261VulnerabilitiesCritical Tor flaw leaks users’ real IP address—update now
TorMoil threatens Mac and Linux versions of Tor browser; Windows and Tails not affected. Mac and Linux versions of the Tor anonymity...






