Search results for "Linux"
-

 88Cyber Crime
88Cyber CrimeLinux Australia conference database hit by hackers
Organizers of the Linux Australia conference have revealed that personal data of delegates may have been exposed after a hacker was able...
-

 134Hacked
134HackedFirefox 37 Launched With Improved Security, Get it For Windows, Linux, OS X and Android
Mozilla has released the latest version of its Firefox browser with a brand new security feature by improving the way encryption is...
-
 296Geek
296GeekMozilla, Linux and Tor Not Accepted for Google Summer of Code 2015
The list of organizations mentoring this year’s GSoC- Google Summer of Code 2015 – has been released and this list is having...
-
 207Tricks & How To's
207Tricks & How To'sHow to Host your website by creating a Linux Server
Alright here is the method, on how to host your website on Linux server (vps). Since these days you can see hosting...
-

 276How To
276How ToLinux Tutorial – How To Host Your Website On Linux
Today I am going to show you on “How to host your website on Linux VPS (WordPress).” The reason why we are going...
-

 254How To
254How ToGetting Started With Kali Linux
This post is for so many of the people in the community asking for and having problems installing Kali Linux. Here is...
-

 420Data Security
420Data SecurityKali Linux 1.1.0 Released! Download Now
The developers at Offensive Security are back with yet another great version of Debian-derived Linux distribution Kali Linux version 1.10. Kali Linux 1.1.0 was...
-

 224Data Security
224Data SecurityLinux Distributions at Risk due to Ghost Vulnerability
Security vendor Qualys announced on Tuesday that a flaw in the popular component of many Linux distributions which would ultimately allow hackers...
-
 211How To
211How To9 Linux Commands To Be Known To Secure Your Linux From Danger
Linux shell or terminal commands are very powerful and just a simple command could lead one to delete a folder, files or root folder,...
-
 246How To
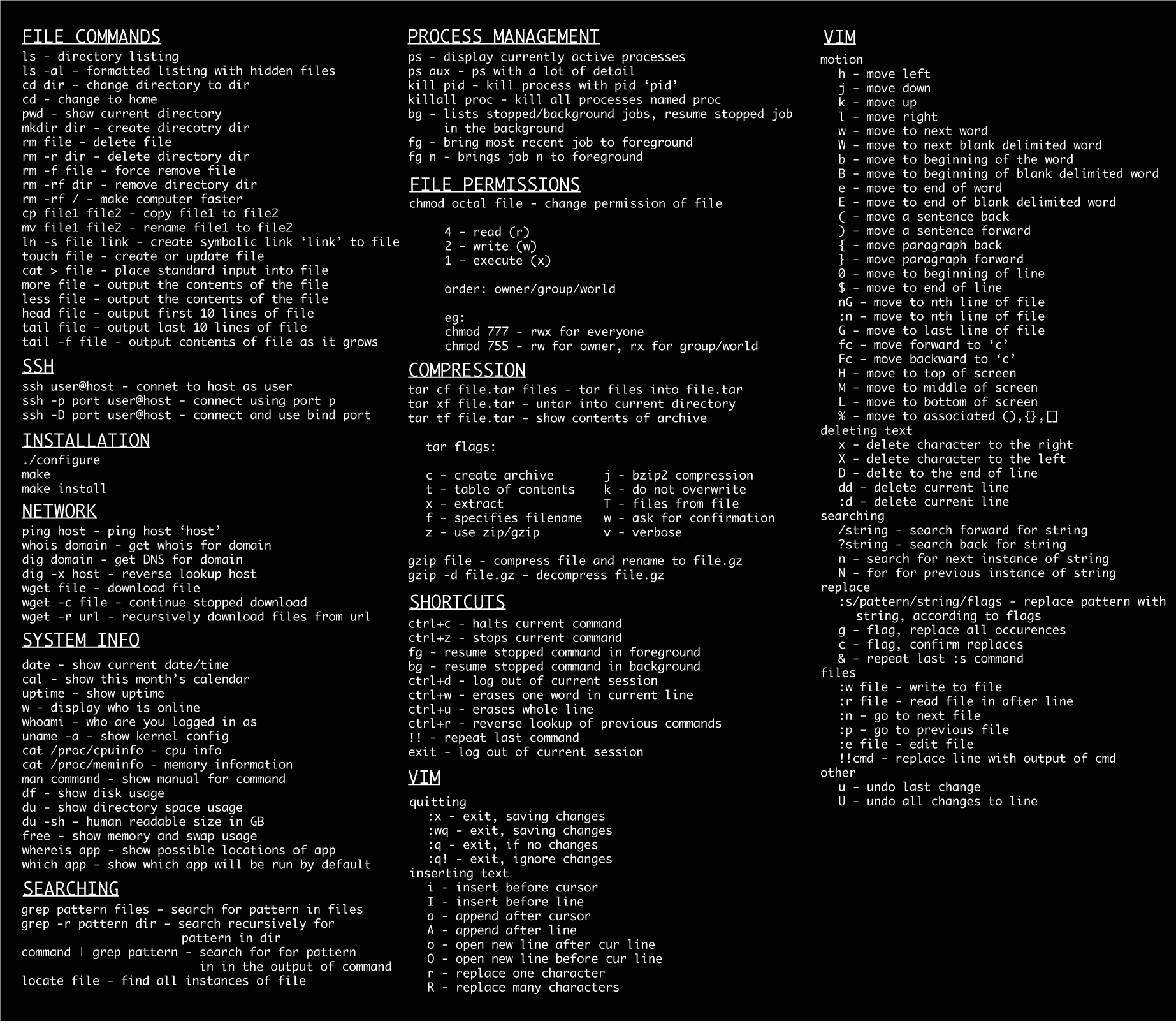
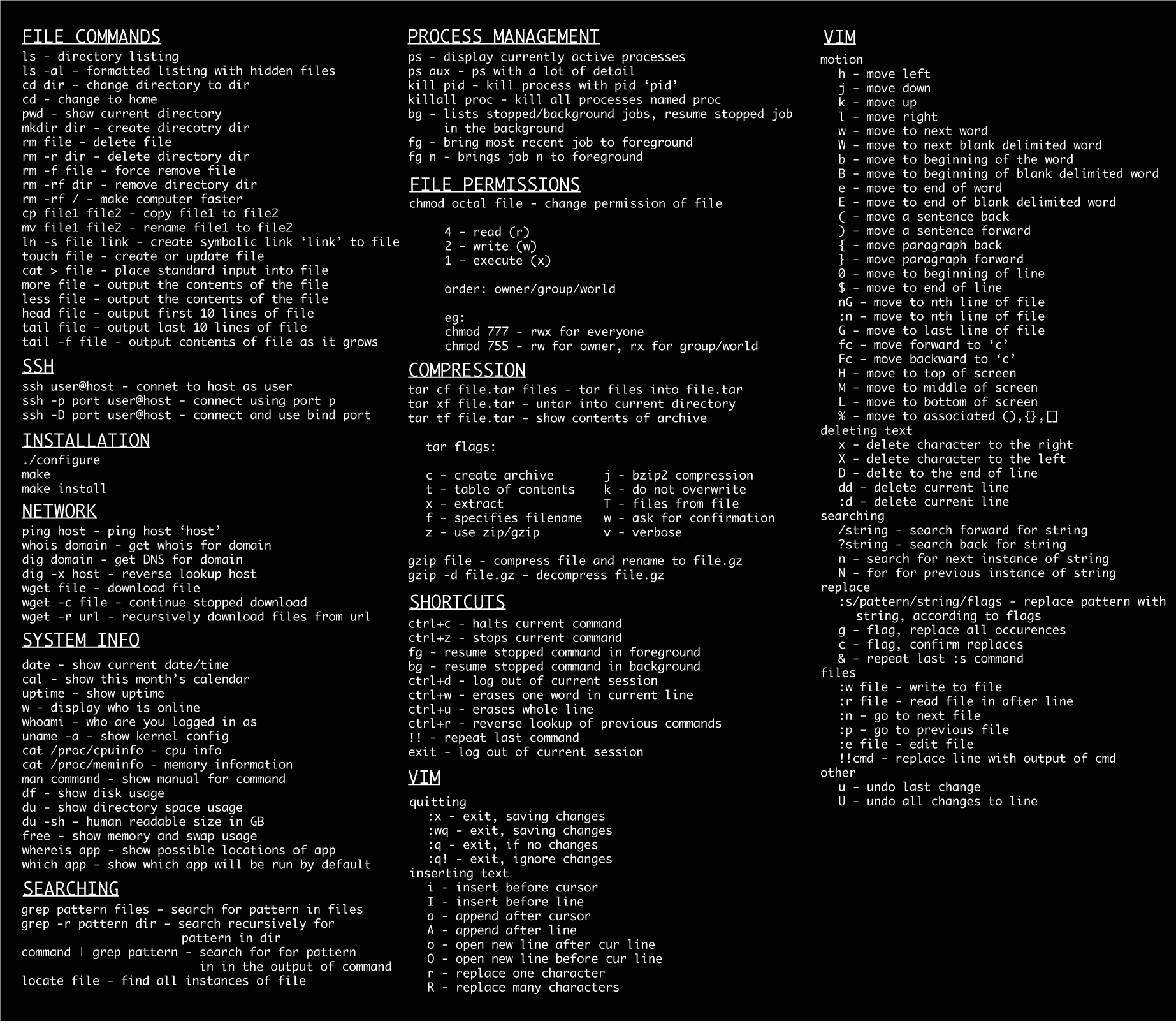
246How ToLinux Basic Commands
mkdir – make directories Usage: mkdir [OPTION] DIRECTORY… eg. mkdir lhn ls – list directory contents Usage: ls [OPTION]… [FILE]… eg. ls, ls l, ls lhn cd – changes directories Usage: cd [DIRECTORY] eg. cd lhn pwd - print name of current working directory Usage: pwd vim – Vi Improved, a programmers text editor Usage: vim [OPTION] [file]… eg. vim lhn.txt cp – copy files and directories Usage: cp [OPTION]… SOURCE DEST eg. cp sample.txt sample_copy.txt cp sample_copy.txt target_dir mv – move (rename) files Usage: mv [OPTION]… SOURCE DEST eg. mv source.txt target_dir...
-
 250Geek
250GeekSyrian Electronic Army releasing its Private Linux-based Distribution- SEANux
A majority of Linux distributions are sold by companies, individuals and many non-commercial entities for free on the Internet. And now, it has...
-
 132How To
132How ToLinux Kernel Local Privilege Escalation PoC
/** * CVE-2014-4014 Linux Kernel Local Privilege Escalation PoC * * Vitaly Nikolenko * http://hashcrack.org * * Usage: ./poc [file_path] * *...
-

 276News
276NewsKALI Linux Website Hacked Using Heartbleed Bug
When it comes to hacking there is nothing like 100% security. Same has happened with the popular penetration testing and Security-related Linux...
-

 128Malware
128MalwareWindigo not Windigone: Linux/Ebury updated
There have been some interesting new developments since we published our report on Operation Windigo. In this blog post you will read...
-

 506Malware
506MalwareOperation Windigo – the vivisection of a large Linux server‑side credential‑stealing malware campaign
Our report titled “Operation Windigo – the vivisection of a large Linux server-side credential-stealing malware campaign" details our analysis of a set...
-

 447Malware
447MalwareAn In‑depth Analysis of Linux/Ebury
In this blog post, we provide an in-depth analysis of Linux/Ebury - the most sophisticated Linux backdoor ever seen by our researchers....
-

 132Malware
132MalwareLinux/Cdorked.A malware: Lighttpd and nginx web servers also affected
Some 400 web servers found infected with Linux/Cdorked.A. including 50 in Alexa’s top 100,000 websites. And this backdoor has been applied to...
-
 270Malware
270MalwareLinux Apache malware: Why it matters to you and your business
This comprehensive look at the problems of malware on Linux Apache web servers explains the threats to business and helps you figure...
-

 109Malware
109MalwareThe stealthiness of Linux/Cdorked: a clarification
We clarify that the Linux/Cdorked backdoor malware leaves no traces on the hard drive "other than its modified httpd binary" which can...
-

 271Malware
271MalwareLinux/Cdorked.A: New Apache backdoor being used in the wild to serve Blackhole
Analysis of a malicious backdoor serving Blackhole exploit pack found on Linux Apache webserver compromised by malware dubbed Linux/Cdorked.A, together with remediation...
-
 215Data Security
215Data SecurityDownload now Kali Linux (BackTrack 6) [Download Link & Password in the article]
Earlier I wrote about BackTrack renaming itself as Kali Linux or BackTrack 6 will be available for download soon, today is the day...






