Search results for "Linux"
-
 3.5KMalware
3.5KMalwareCritical Flaws Discovered in Azure App That Microsoft Secretly Installed on Linux VMs
Microsoft on Tuesday addressed a quartet of security flaws as part of its Patch Tuesday updates that could be abused by adversaries...
-

 4.2KVulnerabilities
4.2KVulnerabilities4 critical vulnerabilities in Azure Linux VMs. Patch quickly
Microsoft Azure users running Linux virtual machines could be exposed to a severe security risk. According to a recent report, these implementations...
-
 3.8KMalware
3.8KMalwareLinux Implementation of Cobalt Strike Beacon Targeting Organizations Worldwide
Researchers on Monday took the wraps off a newly discovered Linux and Windows re-implementation of Cobalt Strike Beacon that’s actively set its...
-
 4.0KData Security
4.0KData SecurityHolesWarm crypto malware hits unpatched Linux, Windows servers
Researchers are calling the HolesWarm the “king of vulnerability exploitation” as the malware has already exploited 20 known Linux and Windows vulnerabilities...
-

 2.4KData Security
2.4KData SecurityOld crypto malware makes come back, hits Windows, Linux devices
LemonDuck was first discovered in China in 2019 as a cryptocurrency botnet that used affected systems for Monero mining. According to a...
-

 4.1KData Security
4.1KData SecurityGoogle issues patches for Chrome flaw for Windows, Mac and Linux
Along with a patch for a zero-day bug in the Chrome browser, Google has addressed seven other flaws in its recent update....
-
 5.1KNews
5.1KNewsNew variant of PRISM Backdoor ‘WaterDrop’ targets Linux systems
According to researchers, the PRISM backdoor has been on their radar for more than 3.5 years. Security researchers at AT&T Labs have...
-
 2.6KData Security
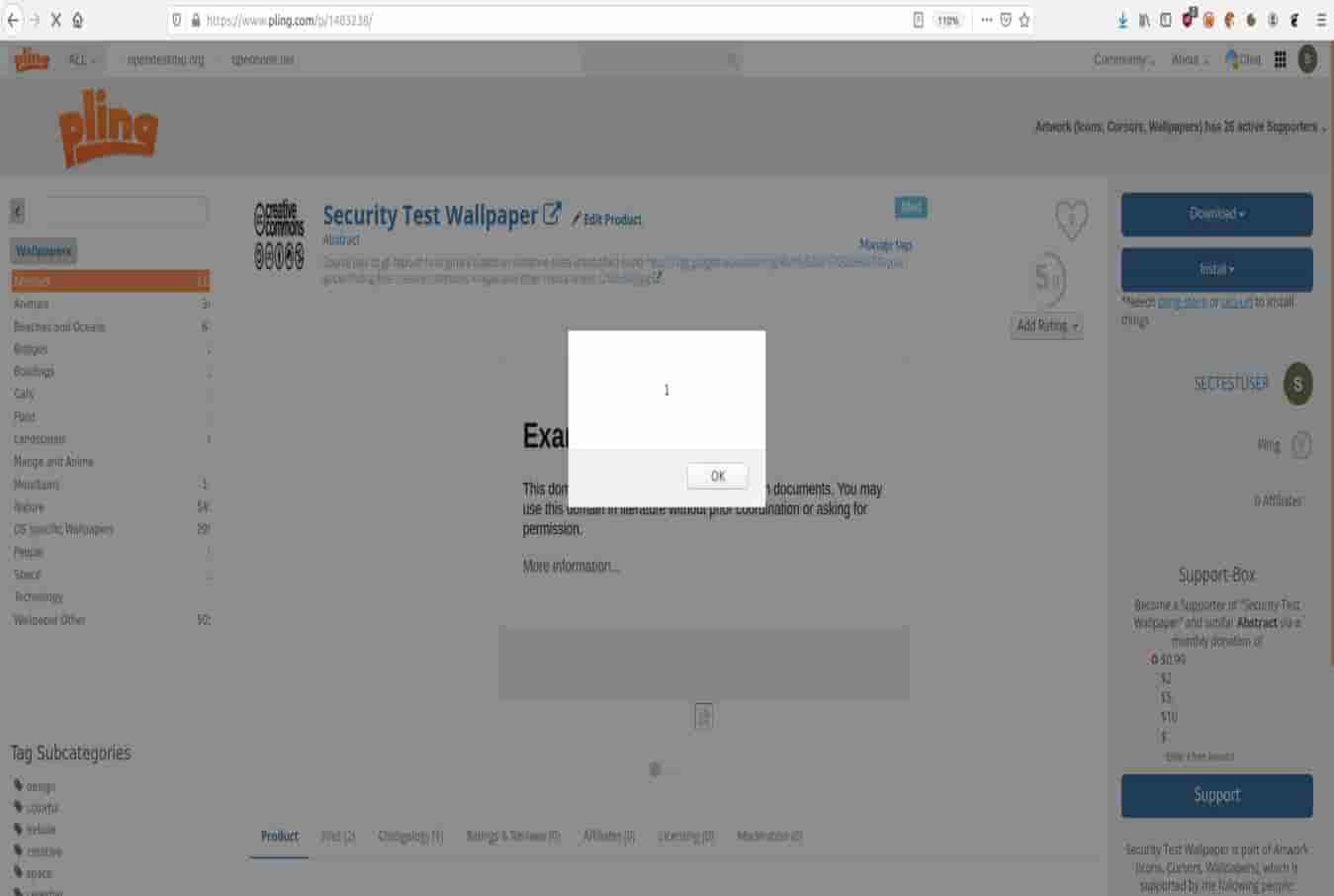
2.6KData SecurityUnpatched flaws exposing Linux marketplaces to remote attacks
Cybersecurity researchers at Berlin-based infosec company Positive Security have identified two serious zero-day vulnerabilities impacting Pling-based FOSS (free and open-source software) marketplaces...
-
 3.8KNews
3.8KNewsDarkRadiation ransomware targeting RedHat, Debian Linux distributions
The newly discovered DarkRadiation ransomware chain is unlike any other ransomware family. Trend Micro cybersecurity researchers have shared findings of a newly identified ransomware...
-
 5.0KVulnerabilities
5.0KVulnerabilitiesCritical vulnerability affects every Linux application including interpreters of other languages like PHP, Python and any language linked to glibc
Security issues in the GNU C library (gblic) can be disastrous for Linux users. An example of this is CVE-2021-33574, a vulnerability...
-

 2.4KMalware
2.4KMalwareNew LemonDuck Malware Attack Windows & Linux Systems for Mining & Stealing Activities
A new version of LemonDuck has been found by the security experts Microsoft and this new version can now steal data, put...
-
 3.6KMalware
3.6KMalwareMicrosoft Warns of LemonDuck Malware Targeting Windows and Linux Systems
An infamous cross-platform crypto-mining malware has continued to refine and improve upon its techniques to strike both Windows and Linux operating systems...
-
 2.3KVulnerabilities
2.3KVulnerabilitiesNew Windows and Linux Flaws Give Attackers Highest System Privileges
Microsoft’s Windows 10 and the upcoming Windows 11 versions have been found vulnerable to a new local privilege escalation vulnerability that permits...
-
 4.1KTutorials
4.1KTutorialsTop 10 utilities for your Linux server to check if it is hacked and monitoring activities
Users of Linux systems are sometimes not aware of all the tools and functions on the system. Thinking about this situation, digital...
-

 5.1KMalware
5.1KMalwareWorld’s richest hacker group now focusing on Linux and NAS devices with new ransomware variant
A recent report notes that REvil ransomware operators are now employing a Linux encryption tool to start attacking virtual machines like VMware...
-

 4.4KNews
4.4KNewsResearcher Discovers Susceptibility Affecting Numerous Linux Marketplaces
The cross-site scripting (XSS) susceptibility plus various supply chain operations greatly impact on the Linux marketplaces, which are located on the Pling...
-

 2.3KVulnerabilities
2.3KVulnerabilities3 critical vulnerabilities in Red Hat Linux virtualization. Patch now
Cybersecurity specialists report the detection of three critical vulnerabilities in virtualization solutions developed by the technology company Red Hat. According to the...
-

 1.8KMalware
1.8KMalwareWormable DarkRadiation Ransomware Targets Linux and Docker Instances
Cybersecurity researchers are sounding the alarm bell over a new ransomware strain called “DarkRadiation” that’s implemented entirely in Bash and targets Linux...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesCritical vulnerability in Linux distros would allow for full system compromise; update now
This Thursday morning it was announced the release of a security patch to address a dangerous root-level vulnerability in Linux polkit that...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesVulnerability in Linux distributions allows threat actors to escalate privileges
Cybersecurity specialists report the detection of an authentication bypass flaw in the polkit authentication system service, included by default in the most...
-
 4.1KMalware
4.1KMalwareFacefish Backdoor Steals Login Credentials & Execute Arbitrary Commands on Linux Systems
The cybersecurity researchers of the Qihoo 360 NETLAB team have recently uncovered a new Linux backdoor, that has been dubbed as, “Facefish.” ...






