Search results for "Linux"
-

 3.9KMalware
3.9KMalwareResearchers Warn of Facefish Backdoor Spreading Linux Rootkits
Cybersecurity researchers have disclosed a new backdoor program capable of stealing user login credentials, device information and executing arbitrary commands on Linux...
-
 3.7KData Security
3.7KData SecurityStealthy RotaJakiro backdoor malware targeting Linux for 3 years
New RotaJakiro Stealthy Linux Malware With System Backdoor Capabilities Went Unnoticed for 3 Years. Qihoo 360’s Network Security Research Lab, aka 360...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesLinux kernel Bug Let Attackers Insert Malicious Code Into The Kernel Address Space
The cybersecurity researchers have detected that the Linux kernel bug is allowing the threat actors to implement some malicious code into the...
-
 3.4KMalware
3.4KMalwareResearchers Uncover Stealthy Linux Malware That Went Undetected for 3 Years
A previously undocumented Linux malware with backdoor capabilities has managed to stay under the radar for about three years, allowing the threat...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesCritical vulnerability in Linux kernel allows hackers to compromise affected systems
Cybersecurity specialists reported the finding of a critical information disclosure vulnerability in the Linux kernel, the successful exploitation of which would allow...
-
 4.4KVulnerabilities
4.4KVulnerabilitiesZero-click Linux Bluetooth vulnerability allows taking control remotely without even user clicking a link
After months of research and rumors, the technical details of BleedingTooth, a zero-click attack on the Linux Bluetooth subsystem that would have...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesTwo critical vulnerabilities in Linux allow hackers to obtain data from kernel memory
Cybersecurity specialists reported the finding of two severe vulnerabilities in Linux-based operating systems that could allow threat actors to bypass the mitigations...
-
 4.8KVulnerabilities
4.8KVulnerabilitiesNew Bugs Could Let Hackers Bypass Spectre Attack Mitigations On Linux Systems
Cybersecurity researchers on Monday disclosed two new vulnerabilities in Linux-based operating systems that, if successfully exploited, could let attackers circumvent mitigations for...
-

 2.4KTutorials
2.4KTutorialsHow to test Linux commands on your server without actually running them. This tool can save you from lot of problems
On many occasions, developers and cybersecurity experts encounter very complex Linux programs and commands, so it is difficult to know what they...
-
 2.0KVulnerabilities
2.0KVulnerabilitiesLinux Kernel Vulnerability that Allows Local Attackers to Escalate Privileges
The Security Researcher Alexander Popov found vulnerabilities in the kernel of Linux operating systems that could allow an attacker to escalate local...
-

 4.1KMalware
4.1KMalwareKobalos – A complex Linux threat to high performance computing infrastructure
ESET researchers publish a white paper about unique multiplatform malware they’ve named Kobalos
-

 4.3KMalware
4.3KMalwareFreakOut, the new botnet that threatens thousands of vulnerable Linux systems
According to a recent report by cybersecurity experts, the operators of a botnet have been targeting non-patched applications running on Linux systems....
-
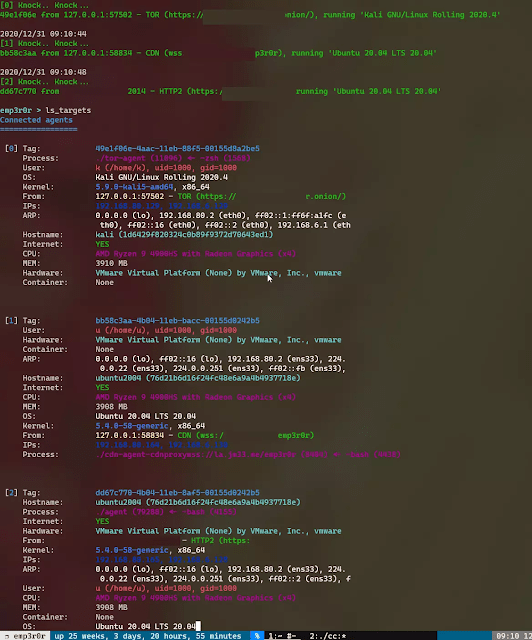
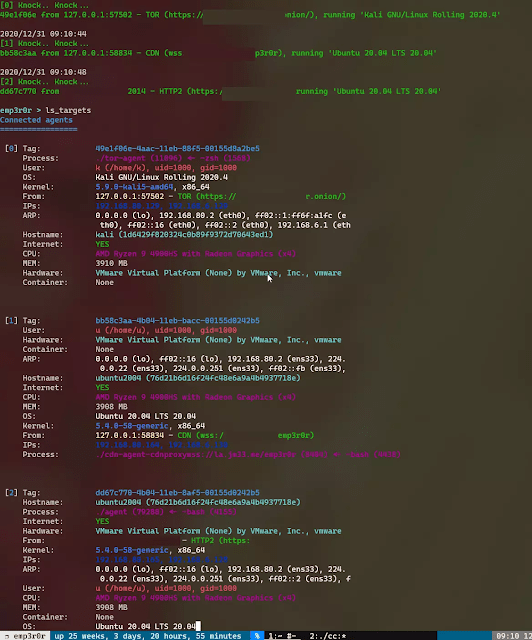 5.4KPost Exploitation
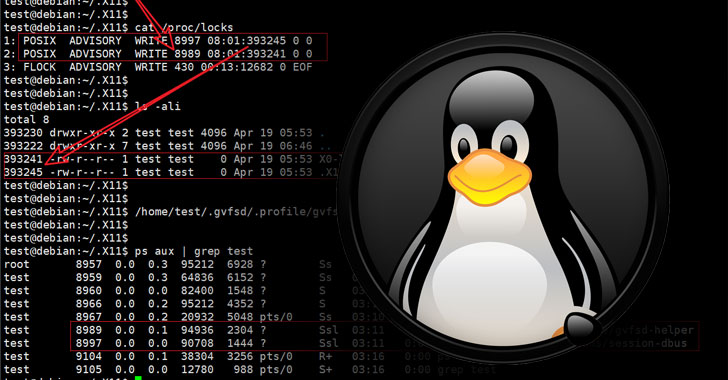
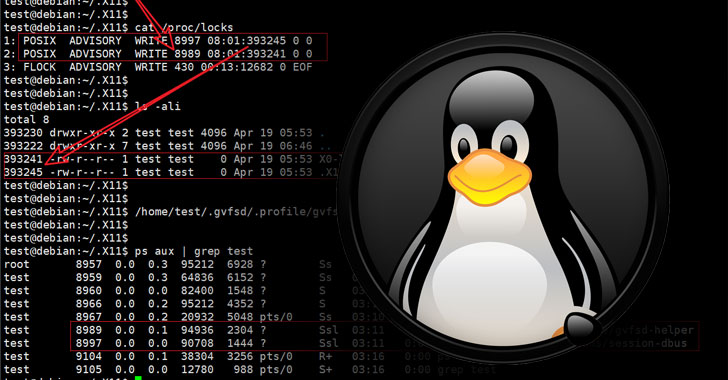
5.4KPost ExploitationEmp3R0R – Linux Post-Exploitation Framework Made By Linux User
linux post-exploitation framework made by linux user Still under active development 中文介绍 check my blog for updates how to use what...
-

 4.6KMalware
4.6KMalwareWho is calling? CDRThief targets Linux VoIP softswitches
ESET researchers have discovered and analyzed malware that targets Voice over IP (VoIP) softswitches
-

 1.1KHow To
1.1KHow ToNew Version of Parrot Ethical Hacking Linux Distro Released
Too Lazzzy to Read? Listen to this article👇 On Thursday, Parrot Security announced the release of Parrot 4.9, a new version of...
-

 4.6KLinux
4.6KLinuxUp close and personal with Linux malware
What are the main security threats facing Linux? A Q&A with ESET Senior Malware Researcher Marc‑Etienne M.Léveillé, whose work has been instrumental...
-

 4.4KLinux
4.4KLinuxLinux and malware: Should you worry?
Malicious code is nothing to worry about on Linux, right? Hold your penguins. How Linux malware has gone from the sidelines to...
-
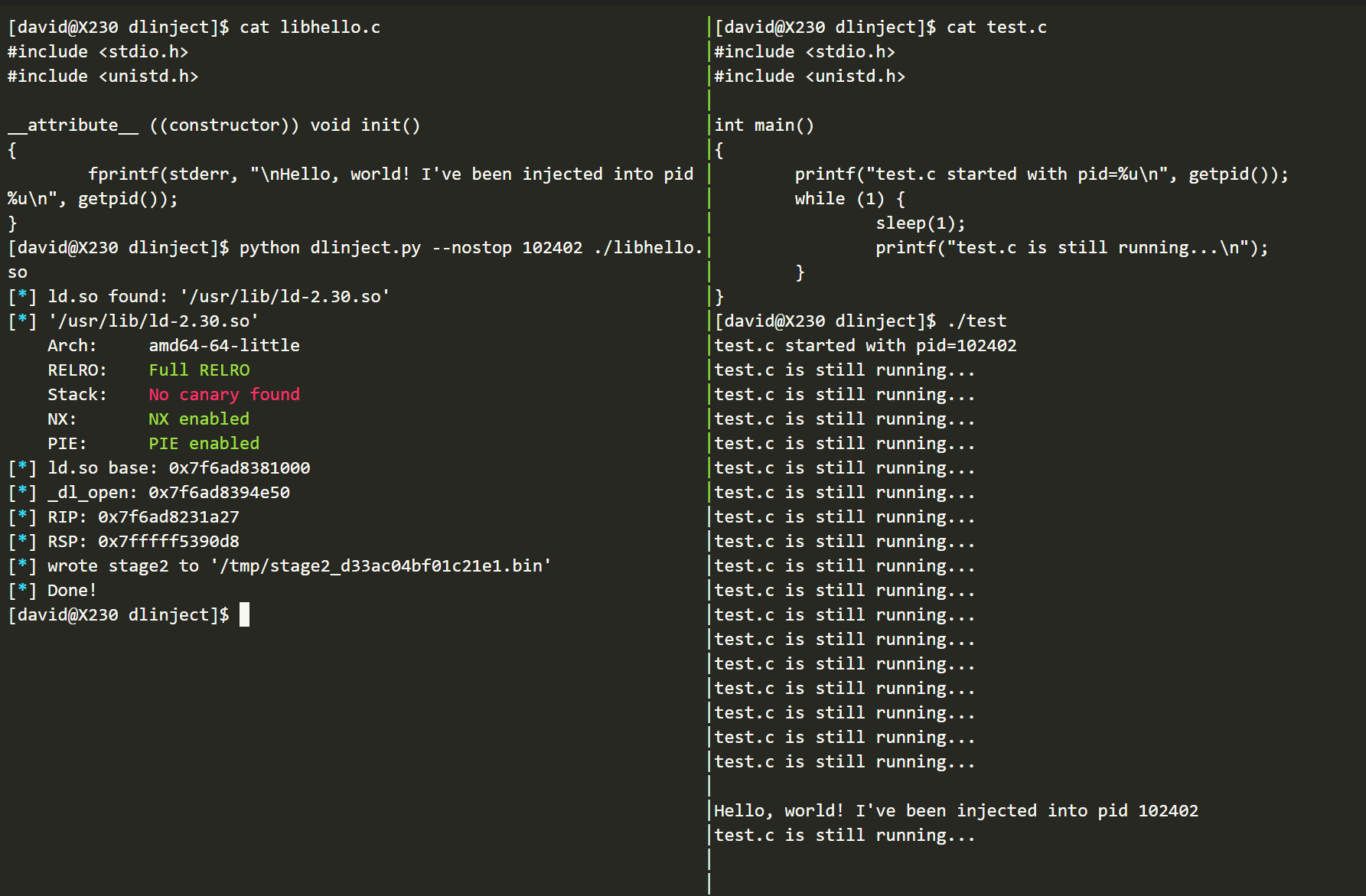
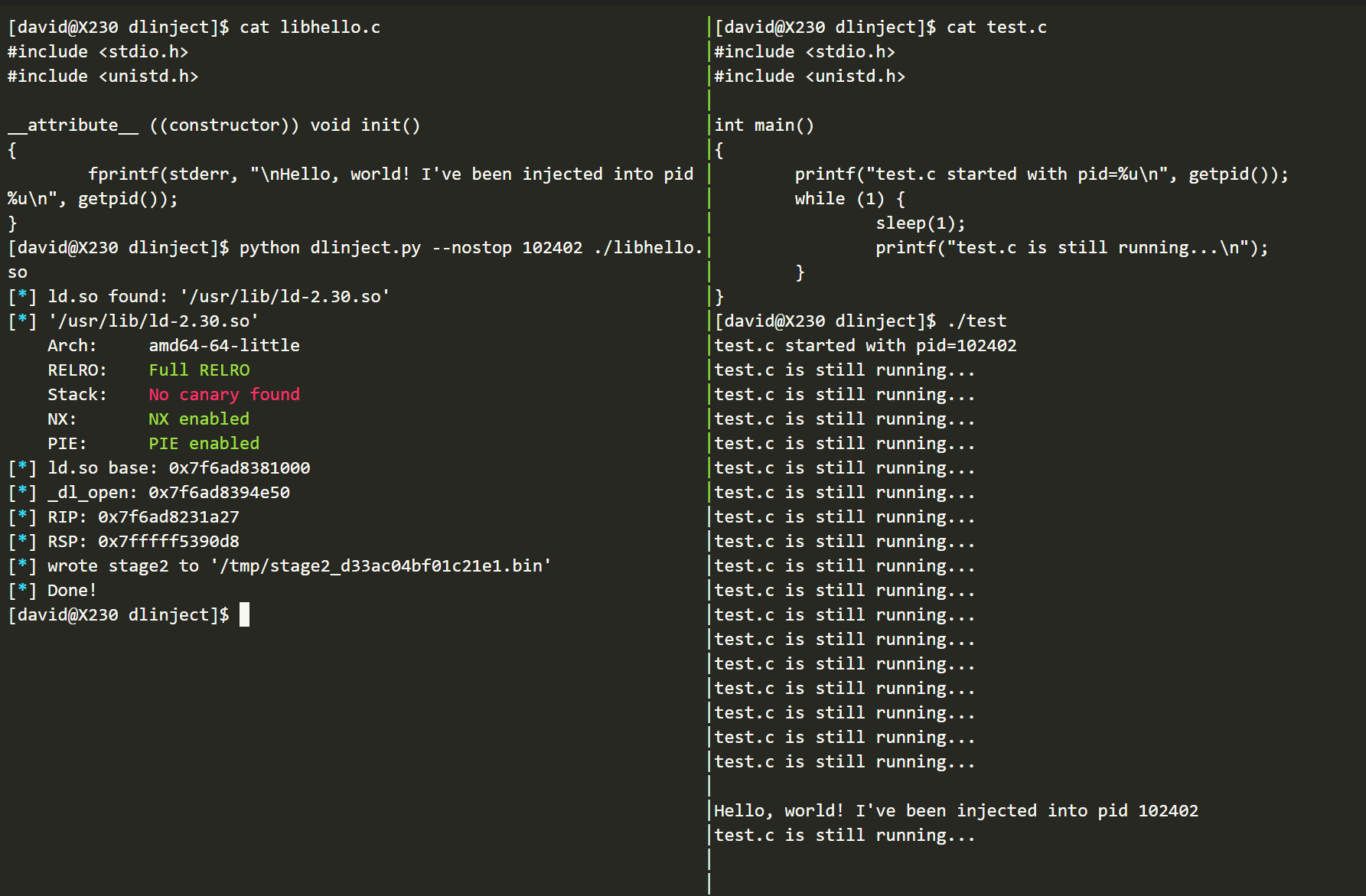 3.1KHackers Repository
3.1KHackers Repositorydlinject: Inject a shared library into a live linux process without ptrace
dlinject.py Inject a shared library (i.e. arbitrary code) into a live Linux process, without ptrace. Inspired by Cexigua and linux-inject, among other things. How...
-

 1.7KNews
1.7KNewsWireGuard VPN For Linux Is Finally Ready For Launch
For several years, developers have been working on WireGuard VPN for Linux and now it is finally ready to arrive on the...
-
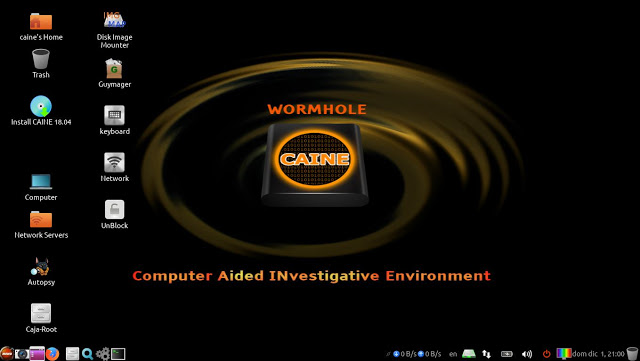
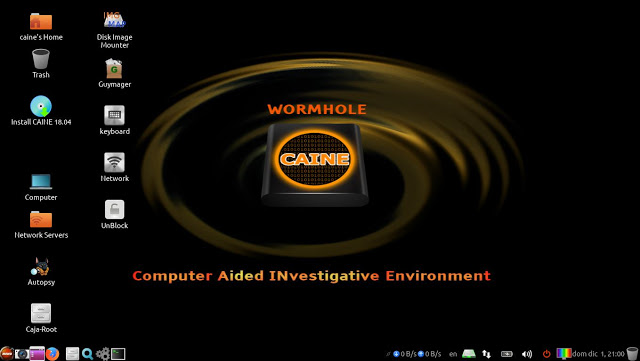 756Hack Tools
756Hack ToolsCAINE 11 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-
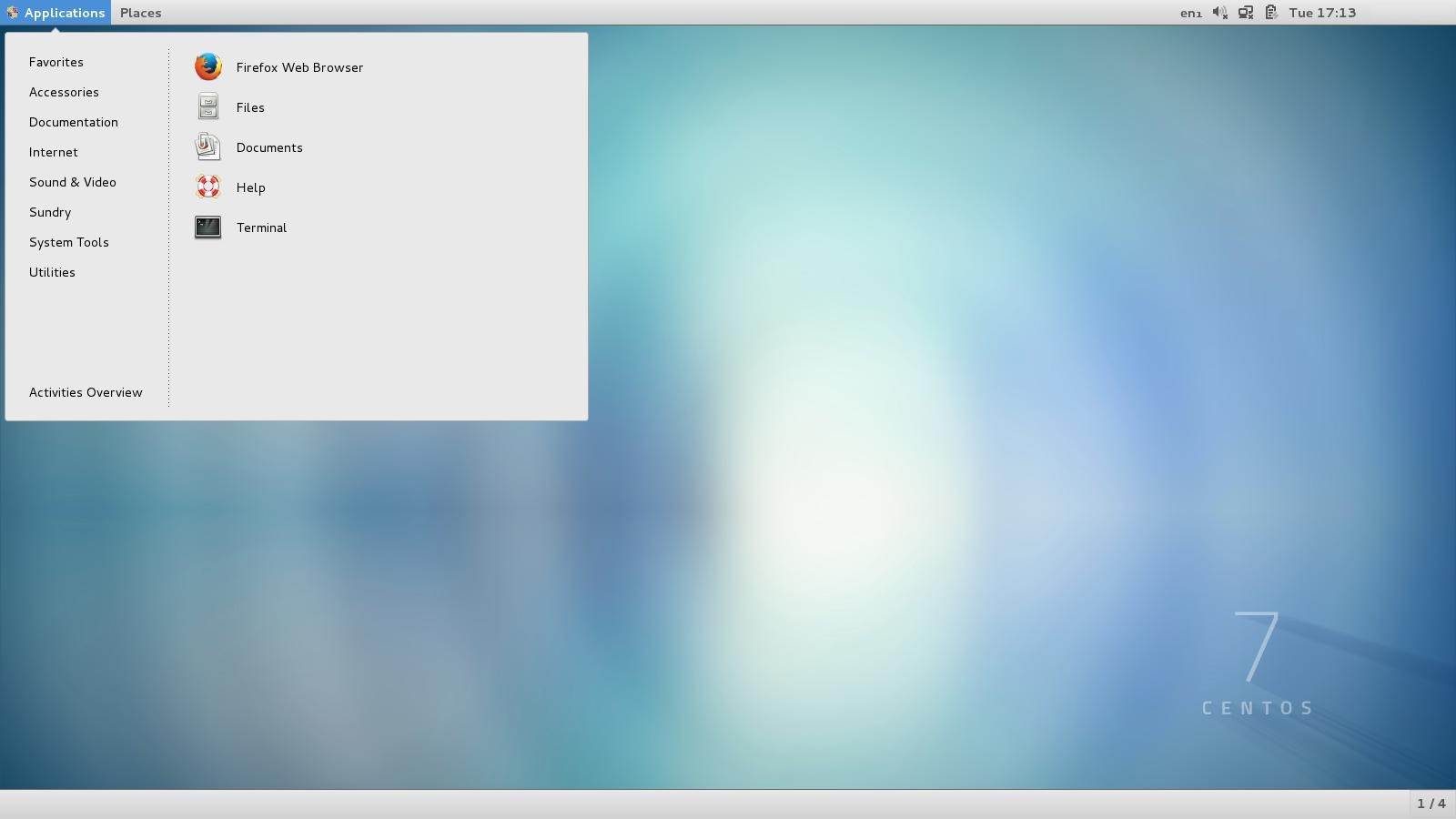
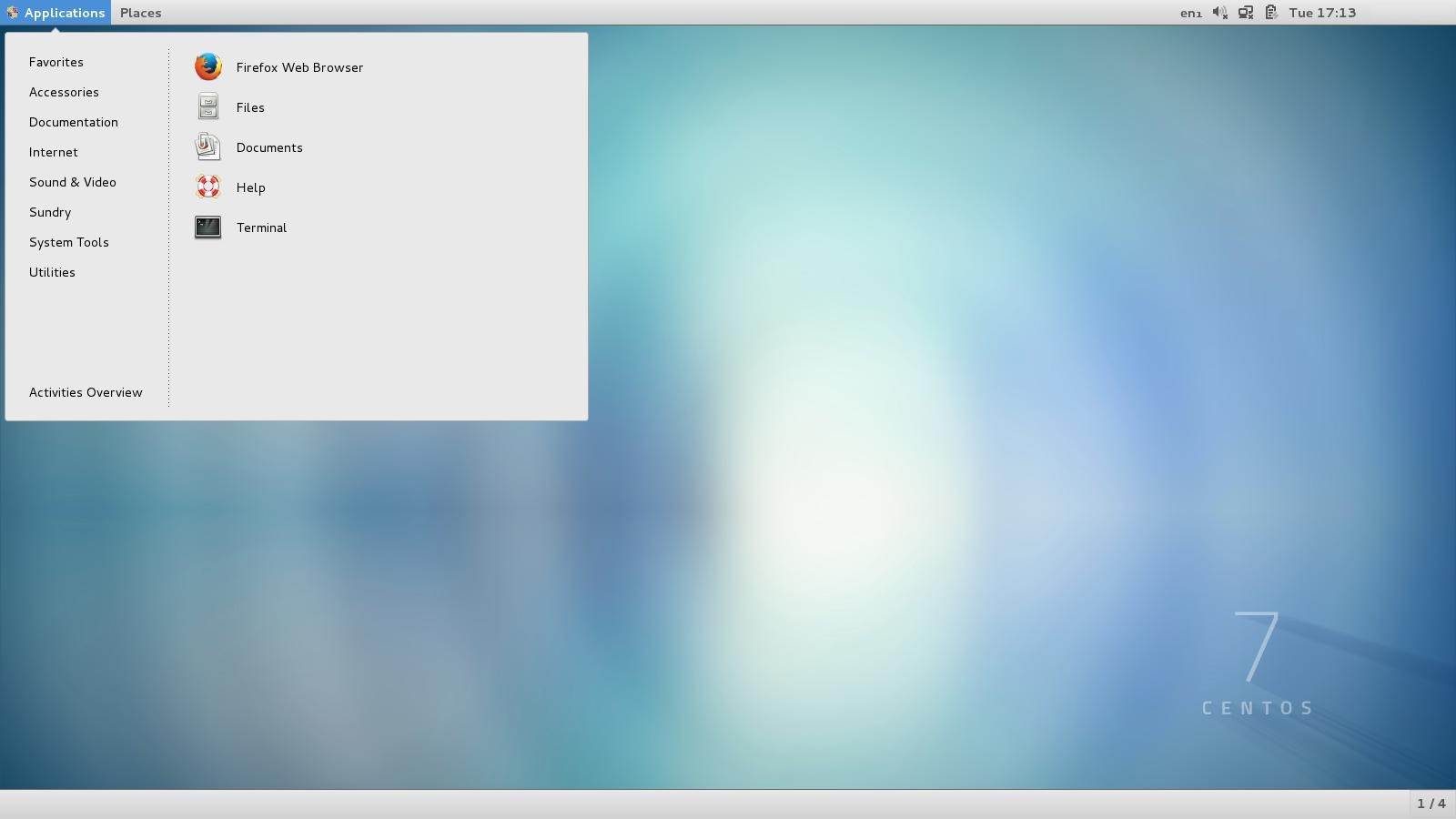 3.3KNews
3.3KNewsRed Hat Enterprise Linux 7 and CentOS 7 receive critical kernel security update
Red Hat and CentOS have announced the availability of important kernel security updates for their Red Hat Enterprise Linux 7 and CentOS...






