Search results for "Malware"
-

 677Malware
677MalwareMalware Attack on CircleCI Engineer’s Laptop Leads to Recent Security Incident
DevOps platform CircleCI on Friday disclosed that unidentified threat actors compromised an employee’s laptop and leveraged malware to steal their two-factor authentication-backed...
-
 1.9KMalware
1.9KMalwareCybercriminals Using Polyglot Files in Malware Distribution to Fly Under the Radar
Remote access trojans such as StrRAT and Ratty are being distributed as a combination of polyglot and malicious Java archive (JAR) files,...
-

 2.5KCyber Attack
2.5KCyber AttackIcedID Malware Strikes Again: Active Directory Domain Compromised in Under 24 Hours
A recent IcedID malware attack enabled the threat actor to compromise the Active Directory domain of an unnamed target less than 24...
-

 485Malware
485MalwareAustralian Healthcare Sector Targeted in Latest Gootkit Malware Attacks
A recent wave of Gootkit malware loader attacks has targeted the Australian healthcare sector by leveraging legitimate tools like VLC Media Player....
-
 5.1KMalware
5.1KMalwareItalian Users Warned of Malware Attack Targeting Sensitive Information
A new malware campaign has been observed targeting Italy with phishing emails designed to deploy an information stealer on compromised Windows systems....
-

 4.7KMalware
4.7KMalwareRussian Turla Hackers Hijack Decade-Old Malware Infrastructure to Deploy New Backdoors
The Russian cyberespionage group known as Turla has been observed piggybacking on attack infrastructure used by a decade-old malware to deliver its...
-
 3.0KInfosec
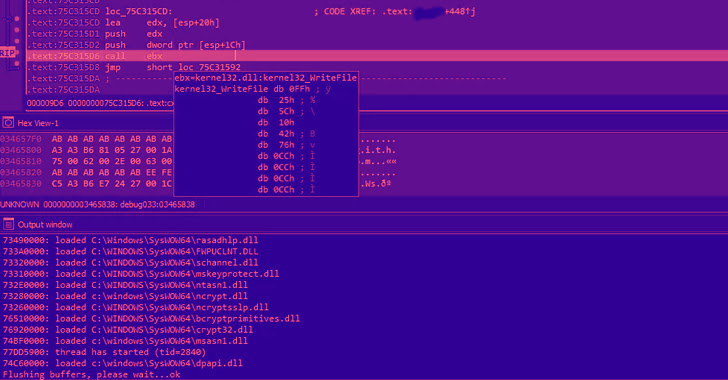
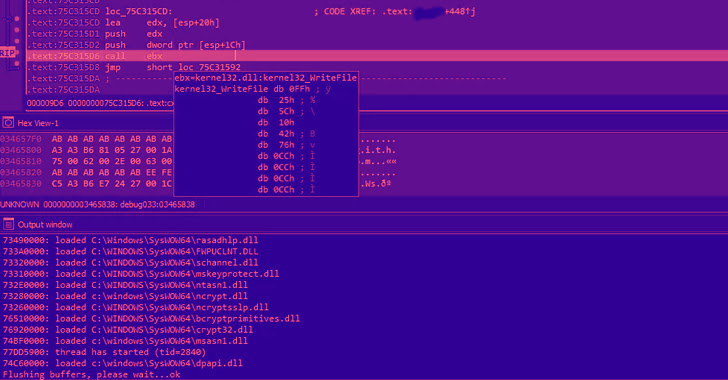
3.0KInfosecBest Malware Analysis Tools List For Security Researchers & Malware Analyst 2023
Malware analysis tools are highly essential for Security Professionals who always need to learn many tools, techniques, and concepts to analyze sophisticated...
-

 305Malware
305MalwareNew shc-based Linux Malware Targeting Systems with Cryptocurrency Miner
A new Linux malware developed using the shell script compiler (shc) has been observed deploying a cryptocurrency miner on compromised systems. “It...
-
 4.1KMalware
4.1KMalwareHackers Using Stolen Bank Information to Trick Victims into Downloading BitRAT Malware
A new malware campaign has been observed using sensitive information stolen from a bank as a lure in phishing emails to drop...
-
 3.9KMalware
3.9KMalwareLinux Malware Exploit Over 30 Vulnerabilities in WordPress Themes & Plugins
In an attempt to inject malicious JavaScript into WordPress plugins and themes that are outdated, a previously detected Linux malware that is...
-

 3.1KMalware
3.1KMalwareWordPress Security Alert: New Linux Malware Exploiting Over Two Dozen CMS Flaws
WordPress sites are being targeted by a previously unknown strain of Linux malware that exploits flaws in over two dozen plugins and...
-
 3.2KMalware
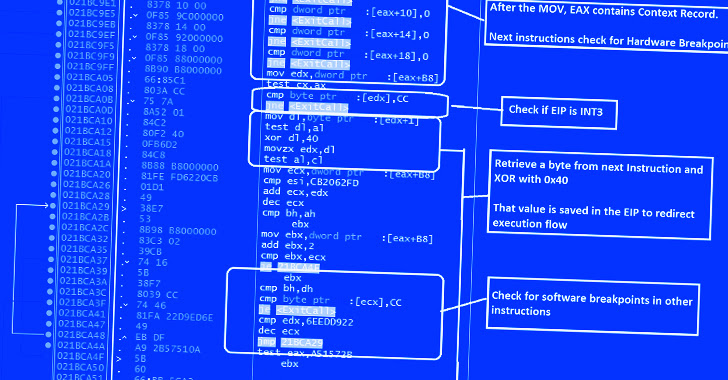
3.2KMalwareGuLoader Malware Uses Advanced Anti-Analysis Techniques to Evade Detection
An advanced malware downloader named GuLoader has recently been exposed by cybersecurity researchers at CrowdStrike. This advanced downloader has the capability to...
-

 2.7KMalware
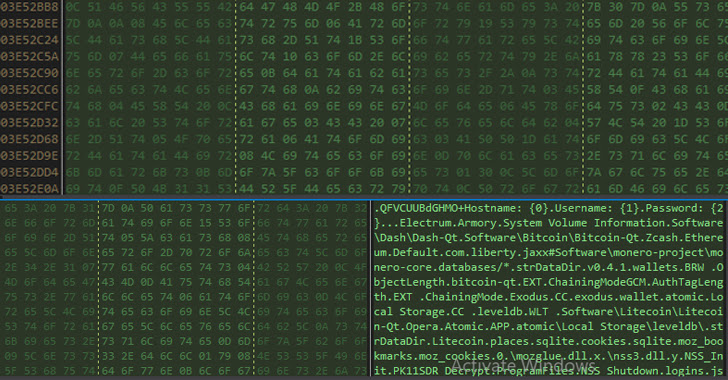
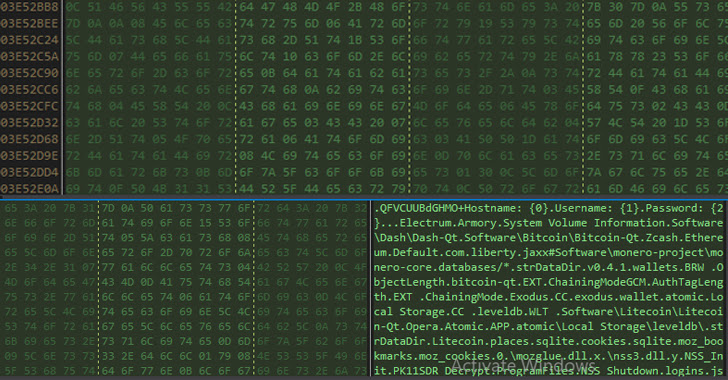
2.7KMalwareHackers Deploy New Information Stealer Malware onto Python Developers’ Machines
Researchers at Phylum recently discovered that hackers had been injecting information stealer malware into Python developers’ machines in order to steal their...
-
 3.4KMalware
3.4KMalwareGuLoader Malware Utilizing New Techniques to Evade Security Software
Cybersecurity researchers have exposed a wide variety of techniques adopted by an advanced malware downloader called GuLoader to evade security software. “New...
-

 1.3KMalware
1.3KMalwarePrivateLoader PPI Service Found Distributing Info-Stealing RisePro Malware
The pay-per-install (PPI) malware downloader service known as PrivateLoader is being used to distribute a previously documented information-stealing malware dubbed RisePro. Flashpoint...
-

 3.6KMalware
3.6KMalwareHackers Use New BrasDex Android Malware to Steal Users’ Banking Details
A new Android trojan called BrasDex has been identified as the work of the same threat actors responsible for the Casbaneiro malware...
-
 1.3KCyber Attack
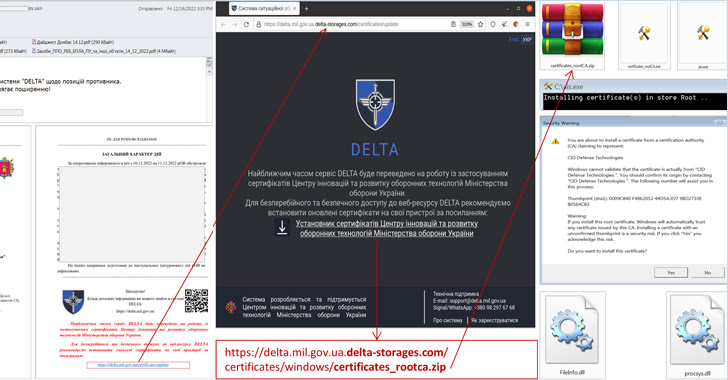
1.3KCyber AttackUkraine’s DELTA Military System Users Under Attack from Info Stealing Malware
The Computer Emergency Response Team of Ukraine (CERT-UA) this week disclosed that users of the Delta situational awareness program received phishing emails...
-

 364Malware
364MalwareBe careful of Risepro malware, a new version of Vidar Infostealer
The newly discovered information stealer known as “RisePro” is being delivered through the pay-per-install malware downloader service known as “PrivateLoader,”. RisePro is...
-

 615Malware
615MalwareBeware of Highly Sophisticated DarkTortilla Malware Distributed Via Phishing Sites
Cyble Research and Intelligence Labs (CRIL) detected threat Actors (TAs) distributing the malware DarkTortilla. Since 2015, the complex .NET-based malware known as DarkTortilla...
-

 2.5KMalware
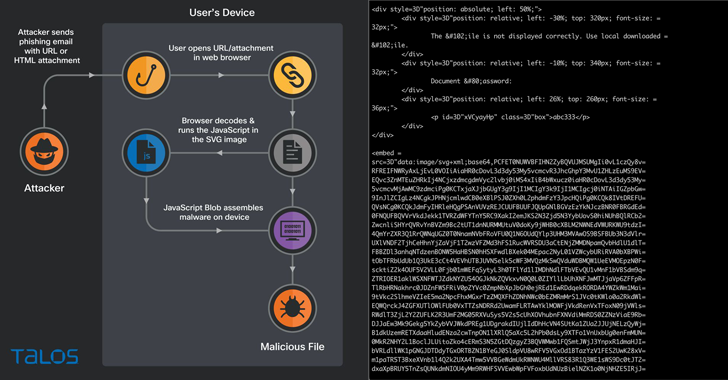
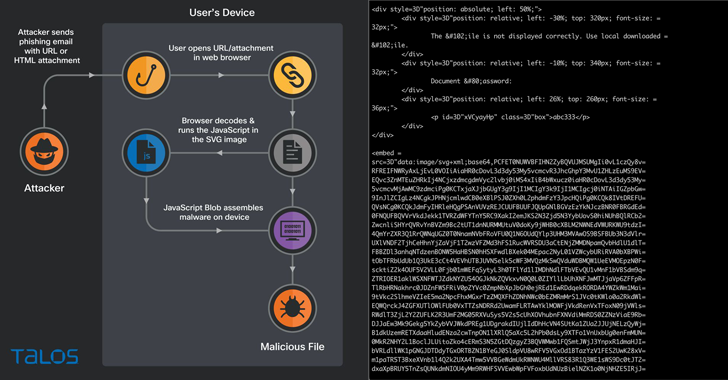
2.5KMalwareHackers Use SVG Images to Install QBot Malware on Windows Systems
To perform HTML smuggling, the QBot malware phishing campaigns utilize SVG image files as a method of distribution. This method creates a...
-
 4.1KMalware
4.1KMalwareHacking Using SVG Files to Smuggle QBot Malware onto Windows Systems
Phishing campaigns involving the Qakbot malware are using Scalable Vector Graphics (SVG) images embedded in HTML email attachments. The new distribution method...






