Search results for "Malware"
-
 4.5KMalware
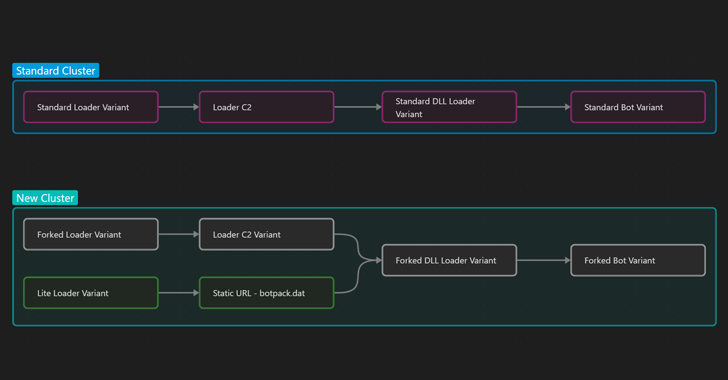
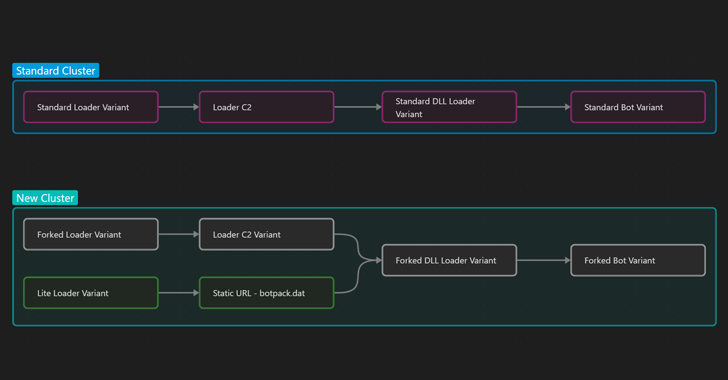
4.5KMalwareIcedID Malware Shifts Focus from Banking Fraud to Ransomware Delivery
Multiple threat actors have been observed using two new variants of the IcedID malware in the wild with more limited functionality that...
-

 1.5KMalware
1.5KMalwareStealthy DBatLoader Malware Loader Spreading Remcos RAT and Formbook in Europe
A new phishing campaign has set its sights on European entities to distribute Remcos RAT and Formbook via a malware loader dubbed...
-
 882Malware
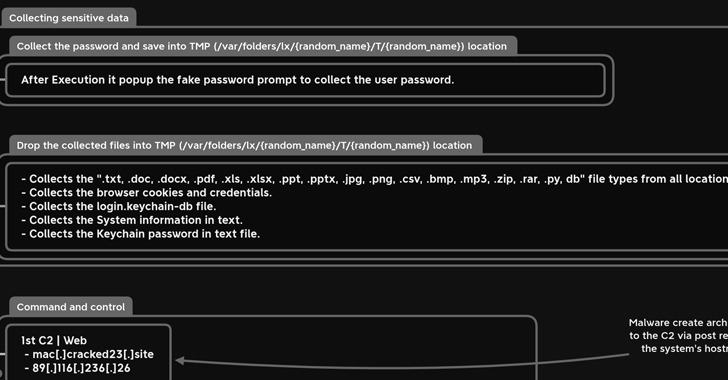
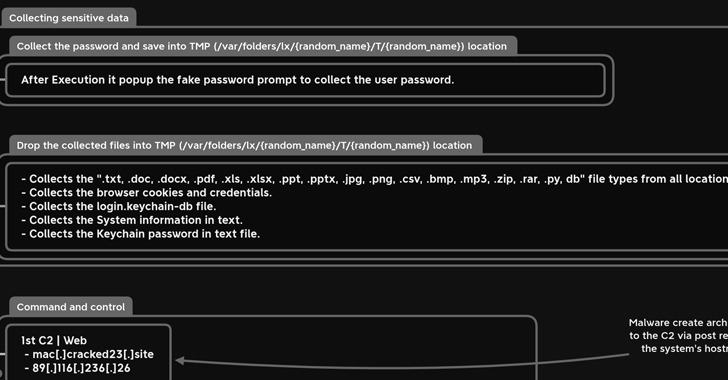
882MalwareNew MacStealer macOS Malware Steals iCloud Keychain Data and Passwords
A new information-stealing malware has set its sights on Apple’s macOS operating system to siphon sensitive information from compromised devices. Dubbed MacStealer,...
-
Malware
ScarCruft’s Evolving Arsenal: Researchers Reveal New Malware Distribution Techniques
The North Korean advanced persistent threat (APT) actor dubbed ScarCruft is using weaponized Microsoft Compiled HTML Help (CHM) files to download additional...
-
 1.6KMalware
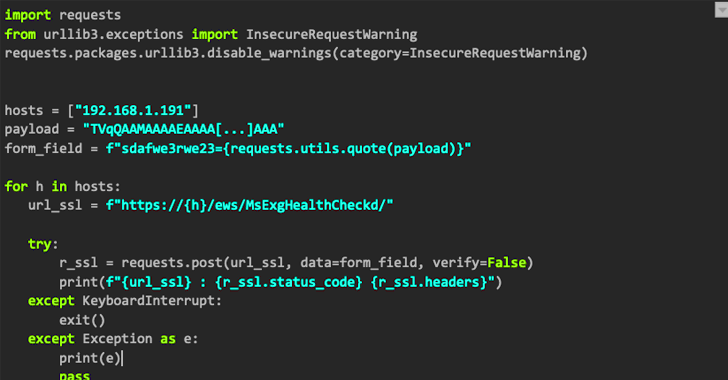
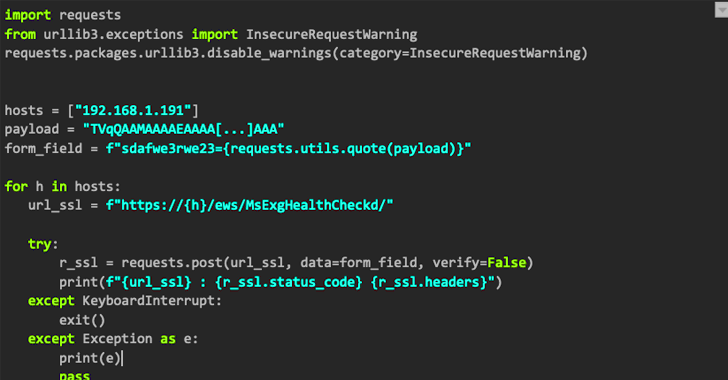
1.6KMalwareNAPLISTENER: New Malware in REF2924 Group’s Arsenal for Bypassing Detection
The threat group tracked as REF2924 has been observed deploying previously unseen malware in its attacks aimed at entities in South and...
-
 797Malware
797MalwareNew ShellBot DDoS Malware Variants Targeting Poorly Managed Linux Servers
Poorly managed Linux SSH servers are being targeted as part of a new campaign that deploys different variants of a malware called...
-
 4.4KMalware
4.4KMalwareNew DotRunpeX Malware Delivers Multiple Malware Families via Malicious Ads
A new piece of malware dubbed dotRunpeX is being used to distribute numerous known malware families such as Agent Tesla, Ave Maria,...
-

 3.0KMalware
3.0KMalwareFakeCalls Vishing Malware Targets South Korean Users via Popular Financial Apps
An Android voice phishing (aka vishing) malware campaign known as FakeCalls has reared its head once again to target South Korean users...
-
 2.4KMalware
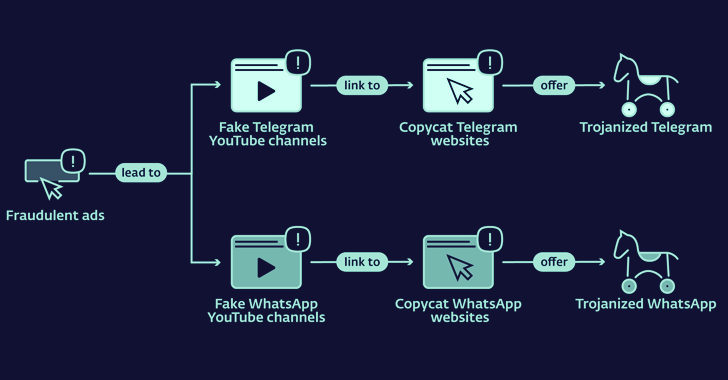
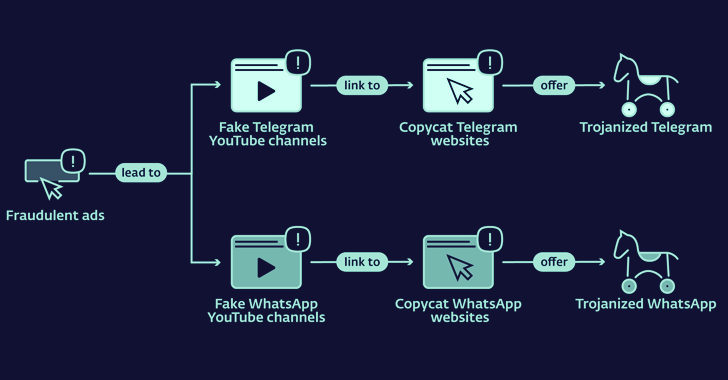
2.4KMalwareLookalike Telegram and WhatsApp Websites Distributing Cryptocurrency Stealing Malware
Copycat websites for instant messaging apps like Telegram and WhatApp are being used to distribute trojanized versions and infect Android and Windows...
-
 3.0KMalware
3.0KMalwareChinese and Russian Hackers Using SILKLOADER Malware to Evade Detection
Threat activity clusters affiliated with the Chinese and Russian cybercriminal ecosystems have been observed using a new piece of malware that’s designed...
-
 1.8KData Security
1.8KData SecurityNew cryptojacking malware can hack in Kubernetes clusters using this easy trick
Dero is a relatively new cryptocurrency that places a strong emphasis on privacy. It utilizes directed acyclic graph (DAG) technology, which allows...
-
 3.0KMalware
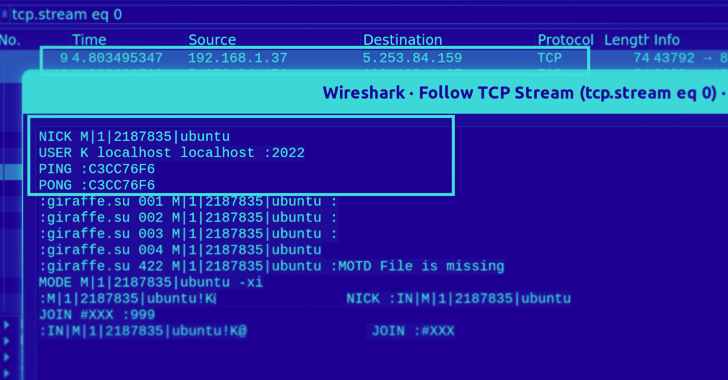
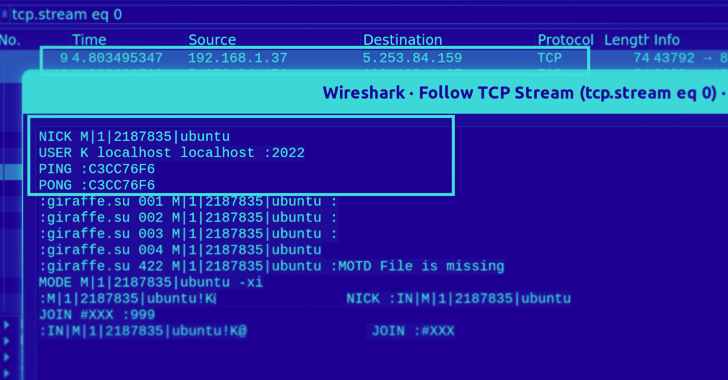
3.0KMalwareGoBruteforcer: New Golang-Based Malware Breaches Web Servers Via Brute-Force Attacks
A new Golang-based malware dubbed GoBruteforcer has been found targeting web servers running phpMyAdmin, MySQL, FTP, and Postgres to corral the devices...
-
 2.7KMalware
2.7KMalwareBusted! Netwire malware infrastructure used to illegally steal data from computers seized
This week, federal authorities in Los Angeles seized an internet domain that was being used to sell malicious software for computers. This...
-
 3.0KMalware
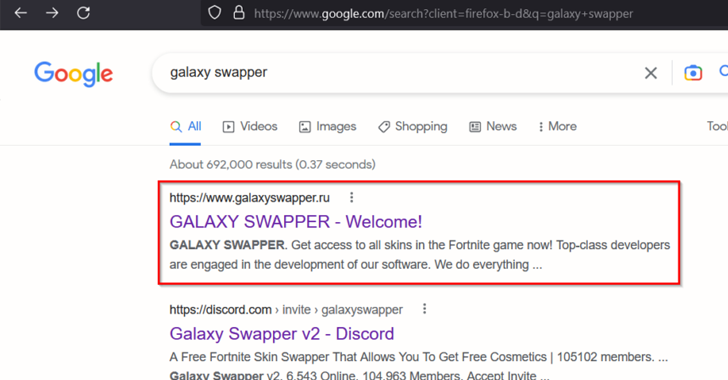
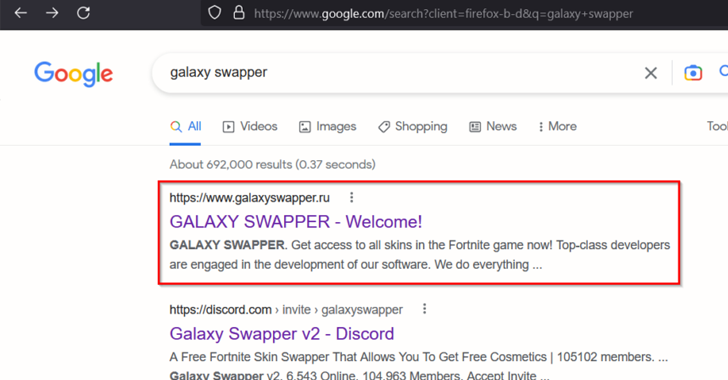
3.0KMalwareWarning: AI-generated YouTube Video Tutorials Spreading Infostealer Malware
Threat actors have been increasingly observed using AI-generated YouTube Videos to spread a variety of stealer malware such as Raccoon, RedLine, and...
-
 1.7KMalware
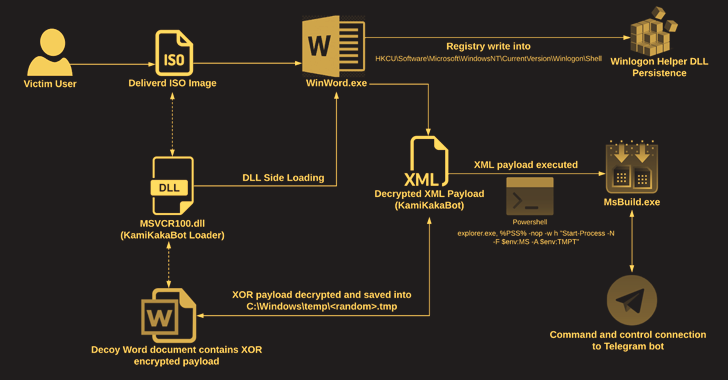
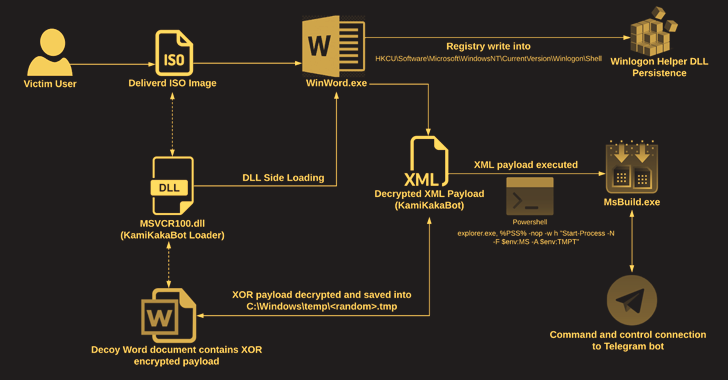
1.7KMalwareKamiKakaBot Malware Used in Latest Dark Pink APT Attacks on Southeast Asian Targets
The Dark Pink advanced persistent threat (APT) actor has been linked to a fresh set of attacks targeting government and military entities...
-
 3.8KMalware
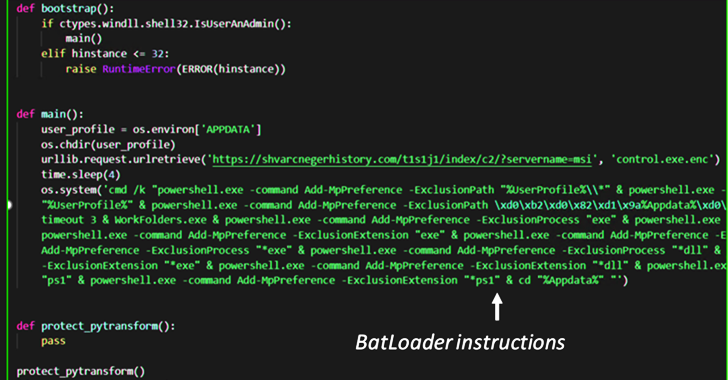
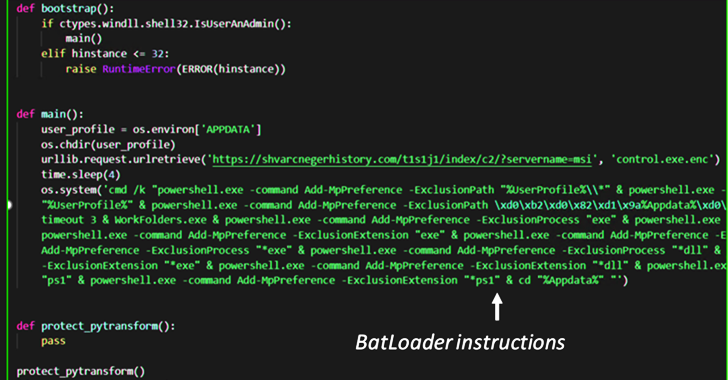
3.8KMalwareBATLOADER Malware Uses Google Ads to Deliver Vidar Stealer and Ursnif Payloads
The malware downloader known as BATLOADER has been observed abusing Google Ads to deliver secondary payloads like Vidar Stealer and Ursnif. According...
-

 1.9KMalware
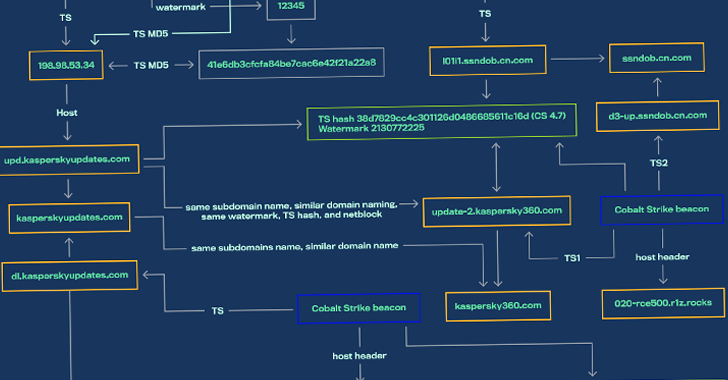
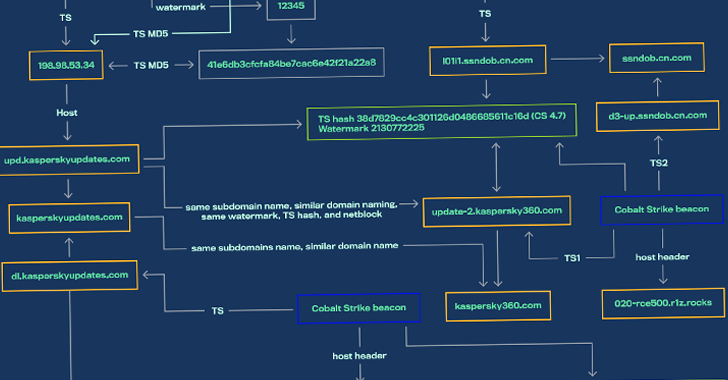
1.9KMalwareChina-linked Hackers Targeting Unpatched SonicWall SMA Devices with Malware
A suspecting China-linked hacking campaign has been observed targeting unpatched SonicWall Secure Mobile Access (SMA) 100 appliances to drop malware and establish...
-

 2.3KMalware
2.3KMalwareNorth Korean UNC2970 Hackers Expands Operations with New Malware Families
A North Korean espionage group tracked as UNC2970 has been observed employing previously undocumented malware families as part of a spear-phishing campaign...
-

 3.2KMalware
3.2KMalwareHackers Exploiting Remote Desktop Software Flaws to Deploy PlugX Malware
Security vulnerabilities in remote desktop programs such as Sunlogin and AweSun are being exploited by threat actors to deploy the PlugX malware....
-

 2.0KMalware
2.0KMalwareNew infostealer malware S1ideload infects systems of government & manufacturing companies
From the beginning of their existence, criminals have been abusing social networks, which have come to occupy an increasingly substantial piece of...
-
 3.2KMalware
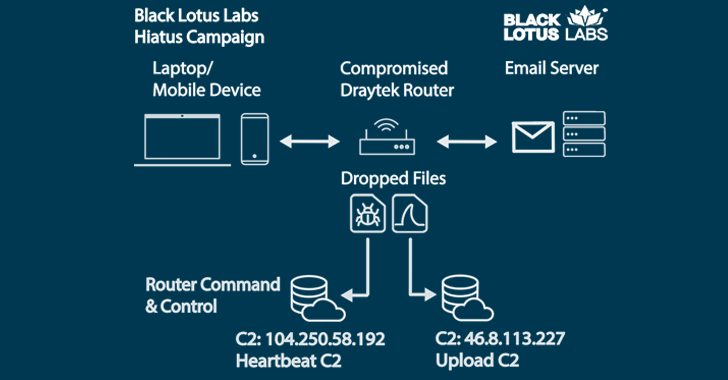
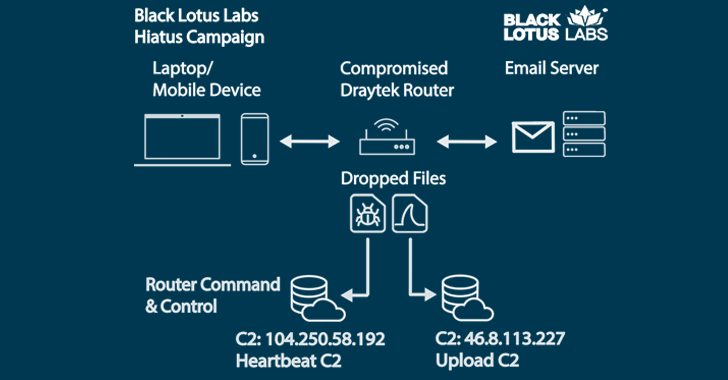
3.2KMalwareNew HiatusRAT Malware Targets Business-Grade Routers to Covertly Spy on Victims
A never-before-seen complex malware is targeting business-grade routers to covertly spy on victims in Latin America, Europe, and North America at least...






