Search results for "Malware"
-

 1.9KMalware
1.9KMalwareVidar Malware Using New Tactics to Evade Detection and Anonymize Activities
The threat actors behind the Vidar malware have made changes to their backend infrastructure, indicating attempts to retool and conceal their online...
-
 931Malware
931MalwareNew Golang-based Skuld Malware Stealing Discord and Browser Data from Windows PCs
A new Golang-based information stealer called Skuld has compromised Windows systems across Europe, Southeast Asia, and the U.S. “This new malware strain...
-

 4.7KMalware
4.7KMalwareCybercriminals Using Powerful BatCloak Engine to Make Malware Fully Undetectable
A fully undetectable (FUD) malware obfuscation engine named BatCloak is being used to deploy various malware strains since September 2022, while persistently...
-

 4.3KMalware
4.3KMalwareHackers Hijack Home Routers & Change The DNS Settings to Implant Infostealer Malware
Researchers discovered a new form of attack that targeted home routers and altered the DNS settings to redirect the victims to a...
-

 307Malware
307MalwareOver 60,000 Android Apps Silently Install Malware on Devices
Recently, cybersecurity researchers uncovered that over 60,000 Android applications had been stealthily disguised as genuine software for the past six months. It...
-

 506Malware
506MalwareNew PowerDrop Malware Targeting U.S. Aerospace Industry
An unknown threat actor has been observed targeting the U.S. aerospace industry with a new PowerShell-based malware called PowerDrop. “PowerDrop uses advanced...
-

 974Malware
974MalwareNew Malware Campaign Leveraging Satacom Downloader to Steal Cryptocurrency
A recent malware campaign has been found to leverage Satacom downloader as a conduit to deploy stealthy malware capable of siphoning cryptocurrency...
-
 3.4KMalware
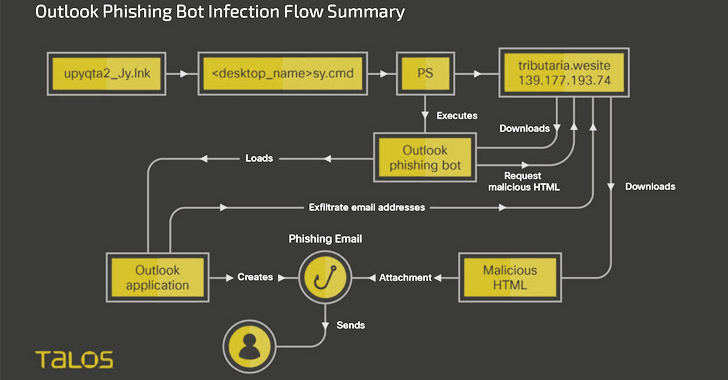
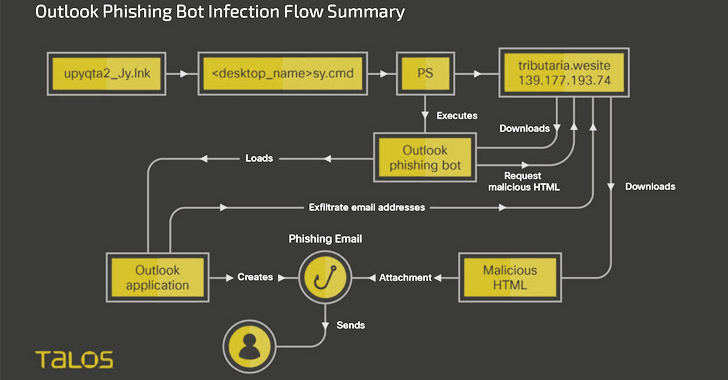
3.4KMalwareNew Botnet Malware ‘Horabot’ Targets Spanish-Speaking Users in Latin America
Spanish-speaking users in Latin America have been at the receiving end of a new botnet malware dubbed Horabot since at least November...
-
 1.3KMalware
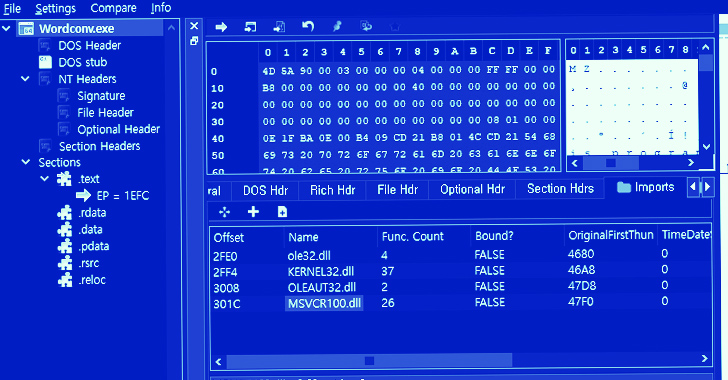
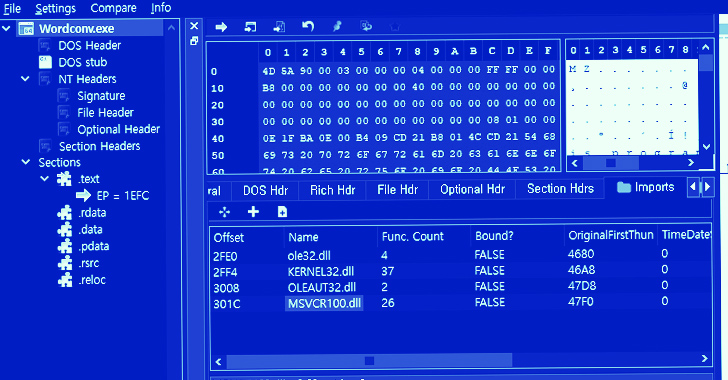
1.3KMalwareHow to Detect Obfuscated Malware on Your Server
Traditional malware detecting methods are ineffective against the hackers’ new techniques – deploying malware that is obfuscated. That’s why an innovative new...
-

 4.6KMalware
4.6KMalwareEvasive QBot Malware Leverages Short-lived Residential IPs for Dynamic Attacks
An analysis of the “evasive and tenacious” malware known as QBot has revealed that 25% of its command-and-control (C2) servers are merely...
-

 3.9KMalware
3.9KMalwareNew Zero-Click Hack Targets iOS Users with Stealthy Root-Privilege Malware
A previously unknown advanced persistent threat (APT) is targeting iOS devices as part of a sophisticated and long-running mobile campaign dubbed Operation...
-

 2.4KMalware
2.4KMalwareNew Bandit Malware Attacks Browsers to Steal Personal & Financial Logins
Bandit Stealer, a recently discovered information stealer by Trend Micro, effectively targets cryptocurrency wallets and web browsers while skillfully avoiding detection. The...
-

 3.3KMalware
3.3KMalwareNew COSMICENERGY Malware Exploits ICS Protocol to Sabotage Power Grids
A new strain of malicious software that’s engineered to penetrate and disrupt critical systems in industrial environments has been unearthed. Google-owned threat...
-

 3.4KMalware
3.4KMalwareData Stealing Malware Discovered in Popular Android Screen Recorder App
Google has removed a screen recording app named “iRecorder – Screen Recorder” from the Play Store after it was found to sneak...
-
 1.7KMalware
1.7KMalwareN. Korean Lazarus Group Targets Microsoft IIS Servers to Deploy Espionage Malware
The infamous Lazarus Group actor has been targeting vulnerable versions of Microsoft Internet Information Services (IIS) servers as an initial breach route...
-

 1.9KMalware
1.9KMalwareHackers Use Weaponized DOCX File to Deploy Stealthy Malware
CERT-UA has identified and addressed a cyber attack on the government information systems of Ukrainian governmental state bodies. Through investigation, it was...
-

 1.6KMalware
1.6KMalwareNorth Korean Kimsuky Hackers Strike Again with Advanced Reconnaissance Malware
The North Korean advanced persistent threat (APT) group known as Kimsuky has been observed using a piece of custom malware called RandomQuery...
-
 736Malware
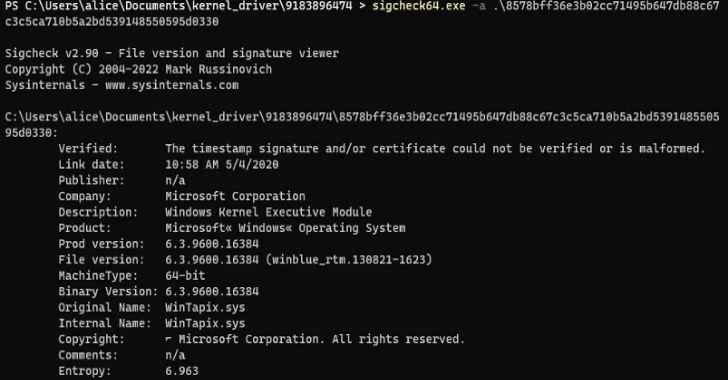
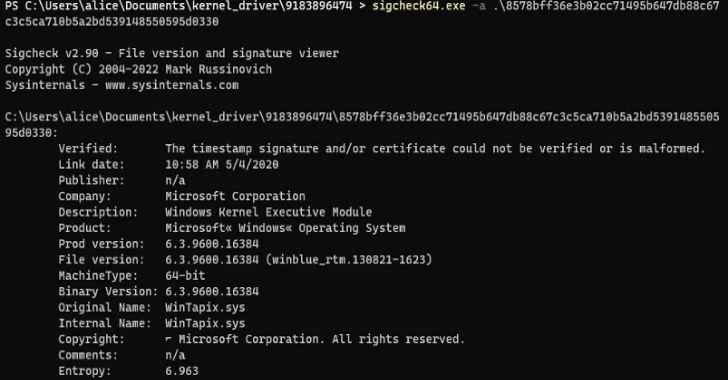
736MalwareNew WinTapix.sys Malware Engages in Multi-Stage Attack Across Middle East
An unknown threat actor has been observed leveraging a malicious Windows kernel driver in attacks likely targeting the Middle East since at...
-

 2.9KMalware
2.9KMalwareMeet ‘Jack’ from Romania! Mastermind Behind Golden Chickens Malware
The identity of the second threat actor behind the Golden Chickens malware has been uncovered courtesy of a fatal operational security blunder,...
-
 3.6KMalware
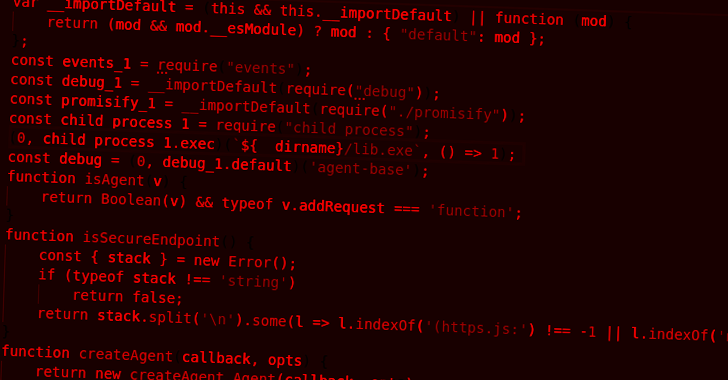
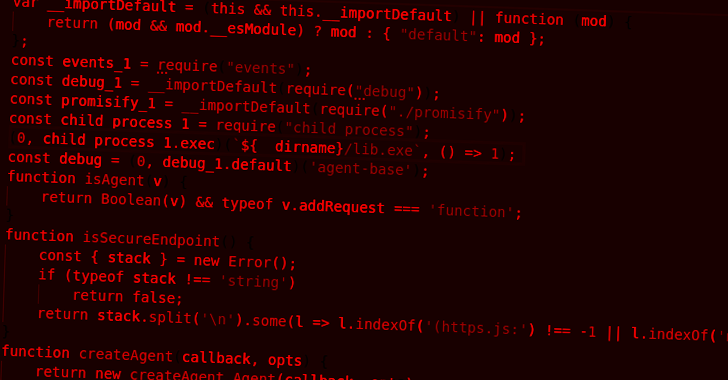
3.6KMalwareDeveloper Alert: NPM Packages for Node.js Hiding Dangerous TurkoRat Malware
Two malicious packages discovered in the npm package repository have been found to conceal an open source information stealer malware called TurkoRat....
-
 2.2KMalware
2.2KMalwareSearching for AI Tools? Watch Out for Rogue Sites Distributing RedLine Malware
Malicious Google Search ads for generative AI services like OpenAI ChatGPT and Midjourney are being used to direct users to sketchy websites...






