Search results for "Malware"
-

 4.9KMalware
4.9KMalwareResearchers Uncover New Attempts by Qakbot Malware to Evade Detection
The operators behind the Qakbot malware are transforming their delivery vectors in an attempt to sidestep detection. “Most recently, threat actors have...
-

 4.8KMalware
4.8KMalwareBeware!! LNK Worm – A Raspberry Robin Malware Attacking Windows Devices
Researchers from Cybereason Global Security Operations Center (SOC) Team, one of the world’s leading cybersecurity companies, have discovered a new Windows worm...
-
 2.1KData Breach
2.1KData BreachSHI Hacked – IT Service Giant Breached Via Professional Malware Attack
SHI International Corp., formerly called Software House International, is a privately-owned provider of technology products and services, headquartered in Somerset, New Jersey....
-
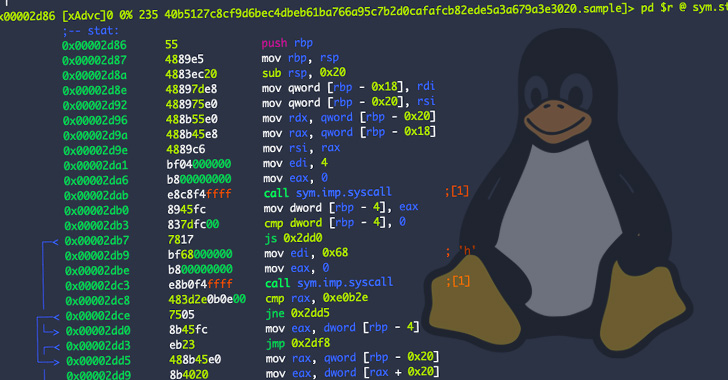
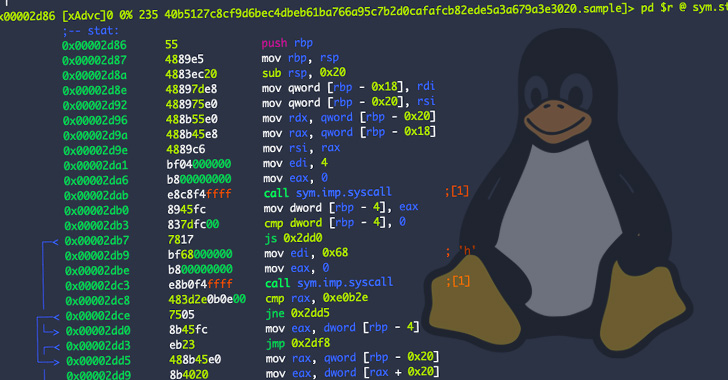 1.4KMalware
1.4KMalwareResearchers Warn of New OrBit Linux Malware That Hijacks Execution Flow
Cybersecurity researchers have taken the wraps off a new and entirely undetected Linux threat dubbed OrBit, signally a growing trend of malware...
-

 2.6KLeaks
2.6KLeaksThis New Malware Is Now a Favorite among Ransomware Gangs
According to cybersecurity researchers, the bumblebee loader is now a darling in the ransomware ecosystem. A new malware is now an important...
-

 479Malware
479MalwareNew Malware Dubbed SessionManager Targeting Microsoft IIS Servers in the Wild
Researchers from Kaspersky seek out more IIS backdoors after the discovery of ‘Owowa’, a malicious IIS module deployed by attackers on Microsoft...
-
Malware
Microsoft Warns of Cryptomining Malware Campaign Targeting Linux Servers
A cloud threat actor group tracked as 8220 has updated its malware toolset to breach Linux servers with the goal of installing...
-
 4.5KMalware
4.5KMalwareZuoRAT Malware exclusively designed for hacking ASUS, Cisco, DrayTek, and NETGEAR SOHO routers
A new malware has been discovered that actively attacks home and small business routers in Europe and North America. That malware attacks...
-

 888Malware
888MalwareRevive – An Android Malware Intercepting All SMS To Steal 2FA/OTP
Cybersecurity experts at Cleafy TIR team have recently discovered a new Android banking malware called Revive. It has been discovered that this...
-

 4.7KMalware
4.7KMalwareNew YTStealer Malware Aims to Hijack Accounts of YouTube Content Creators
Cybersecurity researchers have documented a new information-stealing malware that targets YouTube content creators by plundering their authentication cookies. Dubbed “YTStealer” by Intezer,...
-

 1.5KMalware
1.5KMalwareZuoRAT Malware Hijacking Home-Office Routers to Spy on Targeted Networks
A never-before-seen remote access trojan dubbed ZuoRAT has been singling out small office/home office (SOHO) routers as part of a sophisticated campaign...
-

 4.6KMalware
4.6KMalwareResearchers Warn of ‘Matanbuchus’ Malware Campaign Dropping Cobalt Strike Beacons
A malware-as-a-service (Maas) dubbed Matanbuchus has been observed spreading through phishing campaigns, ultimately dropping the Cobalt Strike post-exploitation framework on compromised machines....
-

 4.6KMalware
4.6KMalwareChinese Hackers Distributing SMS Bomber Tool with Malware Hidden Inside
A threat cluster with ties to a hacking group called Tropic Trooper has been spotted using a previously undocumented malware coded in...
-

 2.0KMalware
2.0KMalwareBRATA Android Malware Gains Advanced Mobile Threat Capabilities
The operators behind BRATA have once again added more capabilities to the Android mobile malware in an attempt to make their attacks...
-
Malware
New Linux Rootkit Malware ‘Syslogk’ Triggers Backdoors With Magic Packets
In order to conceal malicious processes, a new Linux rootkit malware dubbed, ‘Syslogk’ has been hacking computers by using specially crafted “magic...
-
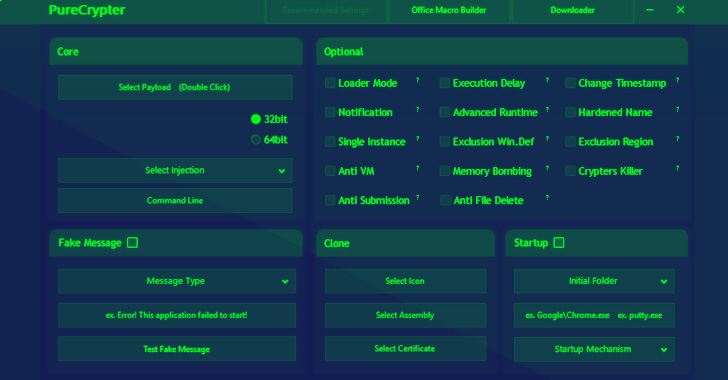
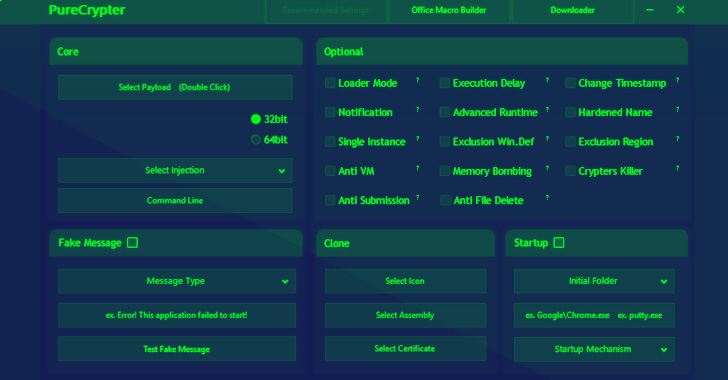 4.2KMalware
4.2KMalwareResearchers Detail PureCrypter Loader Cyber Criminals Using to Distribute Malware
Cybersecurity researchers have detailed the workings of a fully-featured malware loader dubbed PureCrypter that’s being purchased by cyber criminals to deliver remote...
-

 3.4KMalware
3.4KMalwareIranian Hackers Spotted Using a new DNS Hijacking Malware in Recent Attacks
The Iranian state-sponsored threat actor tracked under the moniker Lyceum has turned to using a new custom .NET-based backdoor in recent campaigns...
-

 3.0KMalware
3.0KMalwareNew rootkit malware for Linux is undetectable and is quickly spreading throughout Latin America. Protect your servers before it’s too late
BlackBerry ThreatVector researchers detailed the detection of a new malware strain for Linux systems capable of living at the expense of compromised...
-
 3.7KMalware
3.7KMalwareBeware of Fake CCleaner Search Results that Deliver Information-stealing Malware
The recently emerged ‘FakeCrack’ campaign has been disclosed by the researchers of Avast. The malware campaign tempts users into downloading fake cracked...
-
 4.3KMalware
4.3KMalwareSymbiote: A Stealthy Linux Malware Targeting Latin American Financial Sector
Cybersecurity researchers have taken the wraps off what they call a “nearly-impossible-to-detect” Linux malware that could be weaponized to backdoor infected systems....
-
 4.9KMalware
4.9KMalwareResearchers Warn of Spam Campaign Targeting Victims with SVCReady Malware
A new wave of phishing campaigns has been observed spreading a previously documented malware called SVCReady. “The malware is notable for the...






