Search results for "Malware"
-

 598Malware
598MalwareSMSFactory Android Malware Trick Victims to Subscribes to Premium Services
There has been a warning from security experts about malware first identified as SMSFactory, an Android-based threat. Through the malware, the victims...
-

 4.8KMalware
4.8KMalwareResearchers Uncover Malware Controlling Thousands of Sites in Parrot TDS Network
The Parrot traffic direction system (TDS) that came to light earlier this year has had a larger impact than previously thought, according...
-

 4.3KMalware
4.3KMalwareEnemyBot: New IoT malware exploits one-day vulnerabilities to hack thousands of devices
Cybersecurity specialists from AT&T Alien Labs report the detection of an Internet of Things (IoT) malware variant targeting content management systems (CMS),...
-
 2.3KMalware
2.3KMalwareLatest Mobile Malware Report Suggests On-Device Fraud is on the Rise
An analysis of the mobile threat landscape in 2022 shows that Spain and Turkey are the most targeted countries for malware campaigns,...
-
 2.9KMalware
2.9KMalwareNew Windows Subsystem For Linux Malware Steals Credentials & Record Keystrokes
There has been an increasing amount of interest in targeting the Windows Subsystem for Linux (WSL), due to the fact that they...
-
 3.0KMalware
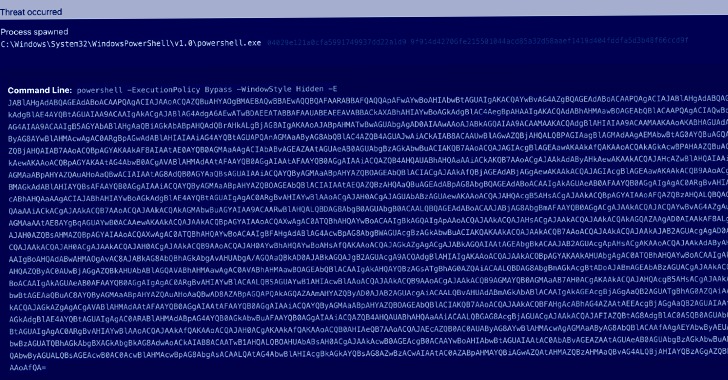
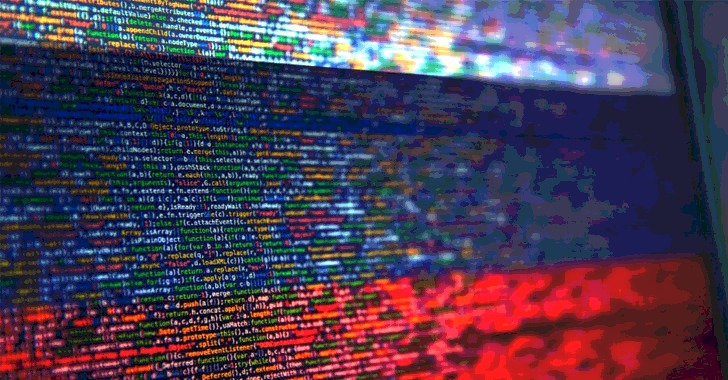
3.0KMalwareExperts Warn of Rise in ChromeLoader Malware Hijacking Users’ Browsers
A malvertising threat is witnessing a new surge in activity since its emergence earlier this year. Dubbed ChromeLoader, the malware is a...
-
 1.2KMalware
1.2KMalwareResearchers Find New Malware Attacks Targeting Russian Government Entities
An unknown advanced persistent threat (APT) group has been linked to a series of spear-phishing attacks targeting Russian government entities since the...
-

 1.6KMalware
1.6KMalwareMicrosoft Warns Rise in XorDdos Malware Targeting Linux Devices
A Linux botnet malware known as XorDdos has witnessed a 254% surge in activity over the last six months, according to latest...
-
 413Malware
413MalwareHackers Trick Users with Fake Windows 11 Downloads to Distribute Vidar Malware
Fraudulent domains masquerading as Microsoft’s Windows 11 download portal are attempting to trick users into deploying trojanized installation files to infect systems...
-
 3.9KMalware
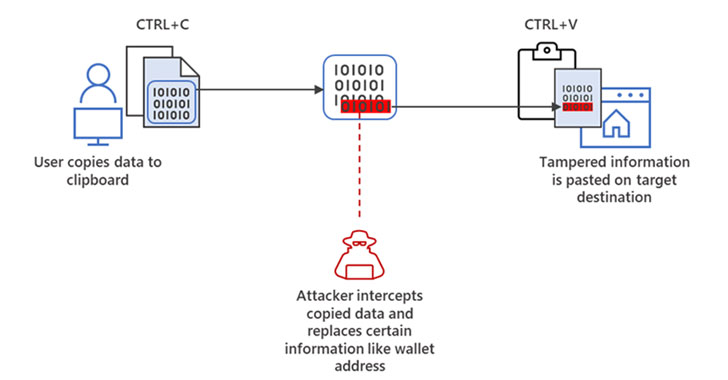
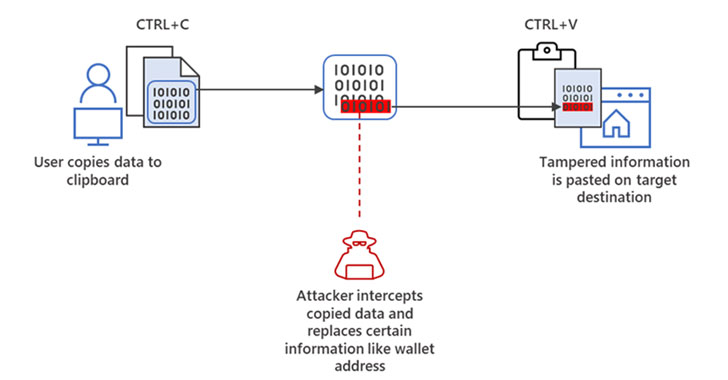
3.9KMalwareMicrosoft Warns of “Cryware” Info-Stealing Malware Targeting Crypto Wallets
Microsoft is warning of an emerging threat targeting internet-connected cryptocurrency wallets, signaling a departure in the use of digital coins in cyberattacks....
-

 5.0KMalware
5.0KMalwareUpdateAgent Returns with New macOS Malware Dropper Written in Swift
A new variant of the macOS malware tracked as UpdateAgent has been spotted in the wild, indicating ongoing attempts on the part...
-

 727Malware
727MalwareResearchers Find Potential Way to Run Malware on iPhone Even When it’s OFF
A first-of-its-kind security analysis of iOS Find My function has identified a novel attack surface that makes it possible to tamper with...
-
 1.5KMalware
1.5KMalwareResearchers Warn of “Eternity Project” Malware Service Being Sold via Telegram
An unidentified threat actor has been linked to an actively in-development malware toolkit called the “Eternity Project” that lets professional and amateur...
-

 2.0KMalware
2.0KMalwareNerbian RAT: New malware with advanced anti-analysis and anti-reversing capabilities uses information about WHO and COVID-19 for its spreading
Proofpoint researchers report the detection of a new variant of remote access Trojan (RAT) characterized by the use of multiple techniques and...
-
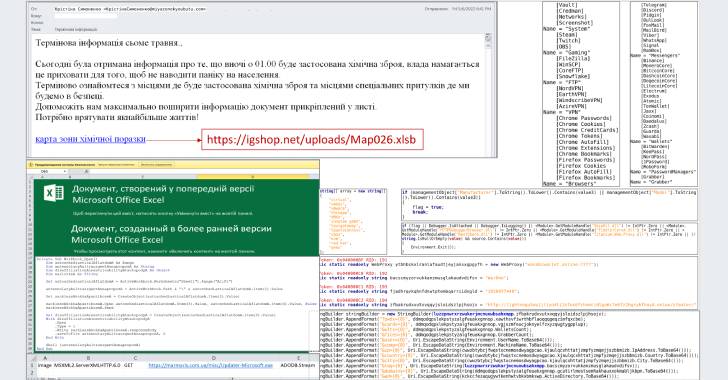
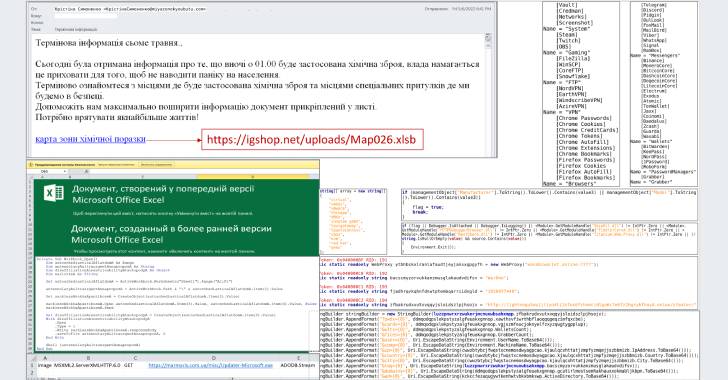 2.5KCyber Attack
2.5KCyber AttackUkrainian CERT Warns Citizens of a New Wave of Attacks Distributing Jester Malware
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of phishing attacks that deploy an information-stealing malware called Jester Stealer on...
-
 4.7KMalware
4.7KMalwareResearchers Warn of ‘Raspberry Robin’ Malware Spreading via External Drives
Cybersecurity researchers have discovered a new Windows malware with worm-like capabilities and is propagated by means of removable USB devices. Attributing the...
-
 3.7KMalware
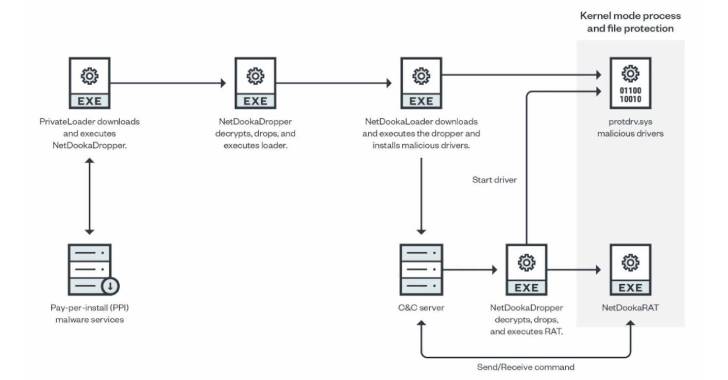
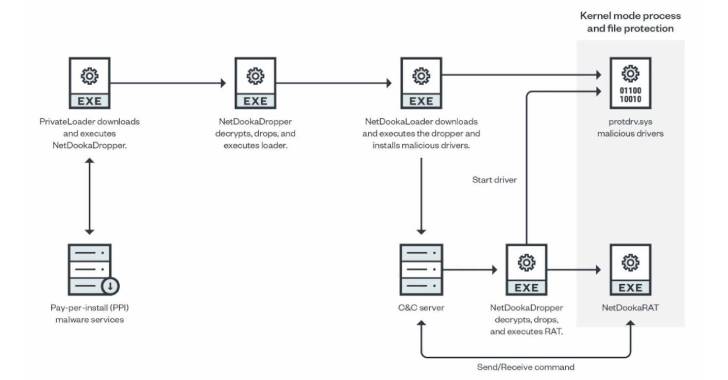
3.7KMalwareHackers Using PrivateLoader PPI Service to Distribute New NetDooka Malware
A pay-per-install (PPI) malware service known as PrivateLoader has been spotted distributing a “fairly sophisticated” framework called NetDooka, granting attackers complete control...
-

 2.9KAndroid
2.9KAndroid3 most dangerous types of Android malware
Here's what you should know about some of the nastiest mobile malware around – from malicious software that takes phones and data...
-

 2.1KMalware
2.1KMalwareCybercriminals Using New Malware Loader ‘Bumblebee’ in the Wild
Cybercriminal actors previously observed delivering BazaLoader and IcedID as part of their malware campaigns are said to have transitioned to a new...
-

 2.9KMalware
2.9KMalwareNPM Bug Allowed Attackers to Distribute Malware as Legitimate Packages
A “logical flaw” has been disclosed in NPM, the default package manager for the Node.js JavaScript runtime environment, that enables malicious actors...
-

 3.2KMalware
3.2KMalwareNorth Korean Hackers Target Journalists with GOLDBACKDOOR Malware
A state-backed threat actor with ties to the Democratic People’s Republic of Korea (DRPK) has been attributed to a spear-phishing campaign targeting...






