Search results for "Management"
-
 294Information Gathering
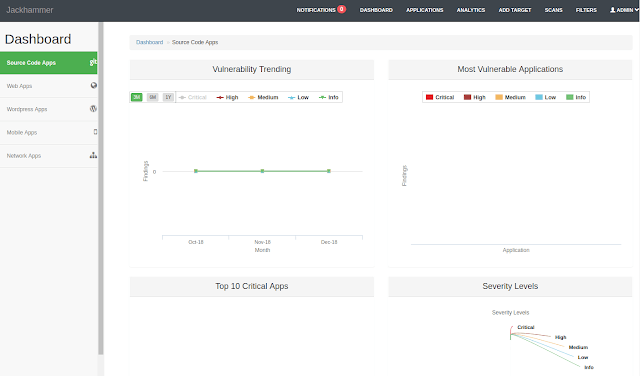
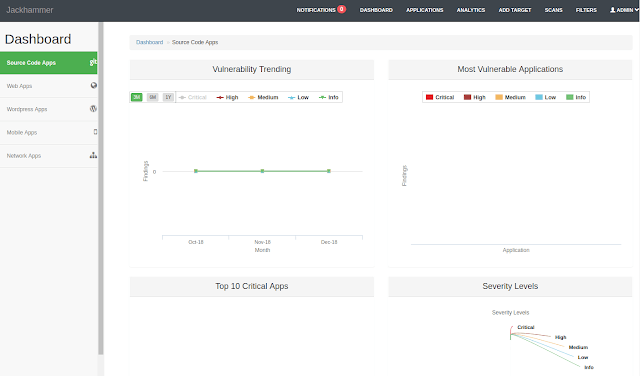
294Information GatheringJackhammer – One Security Vulnerability Assessment/Management Tool To Solve All The Security Team Problems
One Security vulnerability assessment/management tool to solve all the security team problems. What is Jackhammer? Jackhammer is a collaboration tool built with...
-
 179Articles
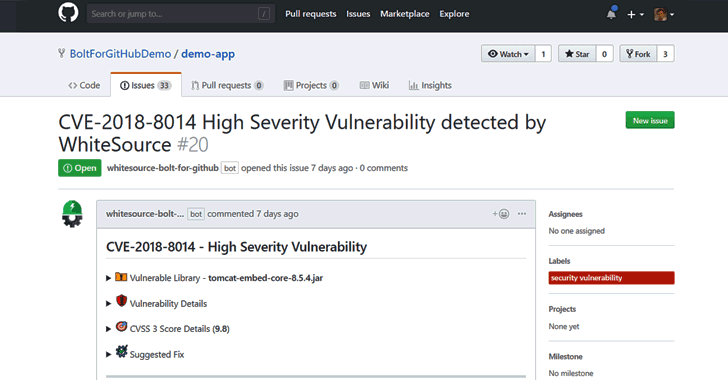
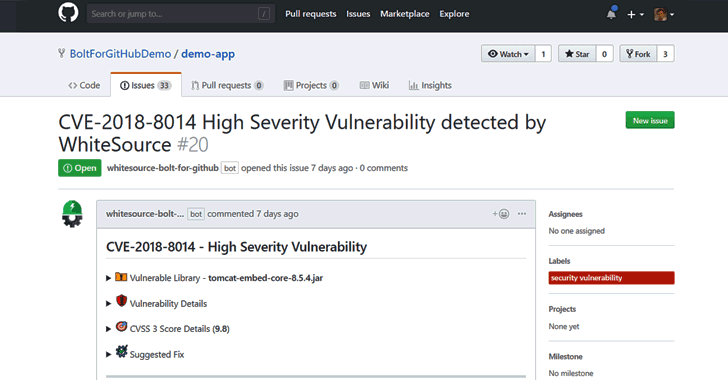
179ArticlesFree Open Source Vulnerability Management App for Developers
Developers around the world depend on open source components to build their software products. According to industry estimates, open source components account...
-

 350Vulnerability Analysis
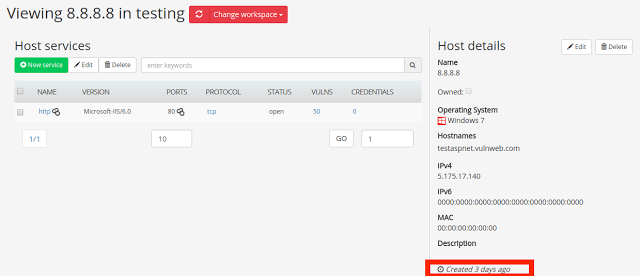
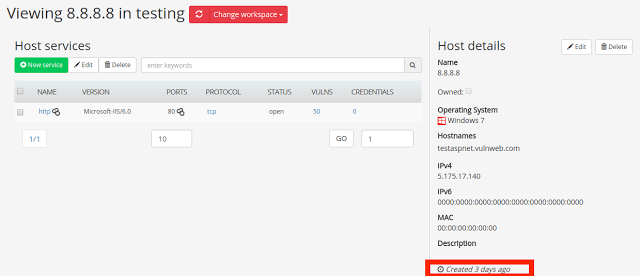
350Vulnerability AnalysisFaraday v3.3 – Collaborative Penetration Test and Vulnerability Management Platform
Here’s the main new features and improvements in Faraday v3.3: Workspace archive You are now able to make the whole workspace read...
-

 256How To
256How ToTop 10 Time Management Tips to Manage Your Time Effectively
How to manage time smartly? Looking for an answer? Read our top 10 time management tips to manage your time effectively &...
-

 225Data Security
225Data SecurityVeeam gets hacked: Data management enterprise exposes database with more than 400 million emails
The company did not operate with industry’s best practices It is very easy to assume that data management software companies are perfectly...
-

 155Malware
155MalwareHackers Abusing Windows Management Interface Command Tool to Deliver Malware That Steal Email Account Passwords
Cybercriminals are continuing to innovate and use legitimate tools to deliver the malicious file, with this new campaign attacker used WMIC (Windows Management...
-
 268Incident Response
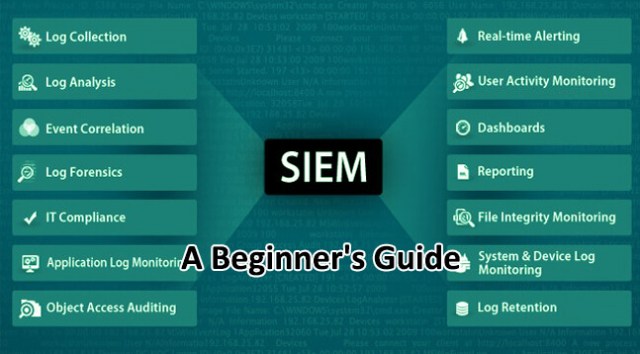
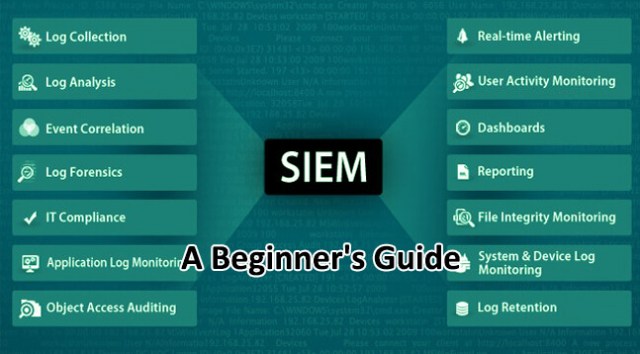
268Incident ResponseSIEM – A Beginner’s Guide to Security Information and Event Management Tools
As its name suggests, the main function of a SIEM is Event management. The SIEM solution once implemented completely & effectively will...
-

 275Vulnerabilities
275VulnerabilitiesNew Spectre variation allow attackers recover data from System Management Mode
A team of experts from Eclypsium presented a new variation of the Spectre attack, which allows attackers to recover the data hosted...
-
 356Pentest Linux Distributions
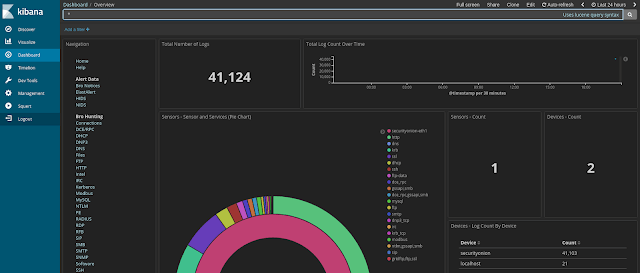
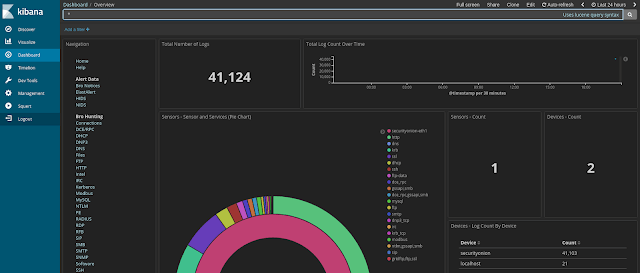
356Pentest Linux DistributionsSecurity Onion – Linux Distro For IDS, NSM, And Log Management
Security Onion is a free and open source Linux distribution for intrusion detection, enterprise security monitoring, and log management. It includes Elasticsearch,...
-

 271Incident Response
271Incident ResponseArchery – Open Source Vulnerability Assessment and Management
Archery is an opensource vulnerability assessment and management tool which helps developers and pentesters to perform scans and manage vulnerabilities. Archery uses...
-

 364Firewall
364FirewallSecurity Onion – Linux Distro for Intrusion Detection, Network Security Monitoring, and Log Management
Security Onion is a Linux distro for intrusion detection, network security monitoring, and log management. It’s based on Ubuntu and contains Snort,...
-
 274Incident Response
274Incident ResponseCyphon – Open Source Incident Management & Response Platform
Cyphon is a big data platform that aggregates, standardizes, and enhances data for easier analysis. Many businesses rely on emails to manage...
-
 182Articles
182ArticlesManagement Systems Of Buildings Waiting to Get Hacked
As per many security reports, managements systems of buildings all over the world have improved dramatically, however, their security is still at...
-

 185Articles
185ArticlesIntel Management Engine is being disabled by the Computer Vendors
These ME security holes affect millions of computers. ME continues Intel’s Active Management Technology (AMT). This is a great tool that allows admins...
-
 256Vulnerability Analysis
256Vulnerability AnalysisFaraday v2.7 – Collaborative Penetration Test and Vulnerability Management Platform
Faraday is the Integrated Multiuser Risk Environment you have always been looking for! It maps and leverages all the data you generate in real time,...
-
 311Data Security
311Data SecurityIntel’ Management Engine Tech Just Got Exposed Through USB Ports
Back in September 2017, Positive Technologies’ experts had expressed interest in the development of a technique that can attack the yet secretive...
-
 290Vulnerabilities
290VulnerabilitiesExperts can hack most CPUs since 2008 over USB by triggering Intel Management Engine flaw
Intel’s management engine – in most Positive Technologies plans to demonstrate at the next Black Hat conference how to hack over USB...
-
Articles
Another Vulnerability is found in Intel Management Engine which allows execution of Code with no Digital Fingerprint
Taking advantage of Intel ME technology, within which attackers can execute unsigned code on the target machine. This leads to a full...
-

 180Vulnerabilities
180VulnerabilitiesCLKSCREW Attack Can Hack Modern Chipsets via Their Power Management Features
A team of three scientists from Columbia University has discovered that by attacking the combo of hardware and software management utilities embedded...
-

 100Vulnerabilities
100VulnerabilitiesManagement bug can crash Cisco IOS, IOS XE
Nine SNMP MIBs vulnerable. Cisco’s been caught out by the venerable Simple Network Management Protocol, turning up nine bugs in IOS and...
-
 316Geek
316GeekA Malware That can Bypass Windows Firewall Using Intel’s Management Tech
A unique and perhaps a very practical way of injecting malware into an entire network has been discovered in which the hacking...






