Search results for "Memory"
-
 1.2KData Security
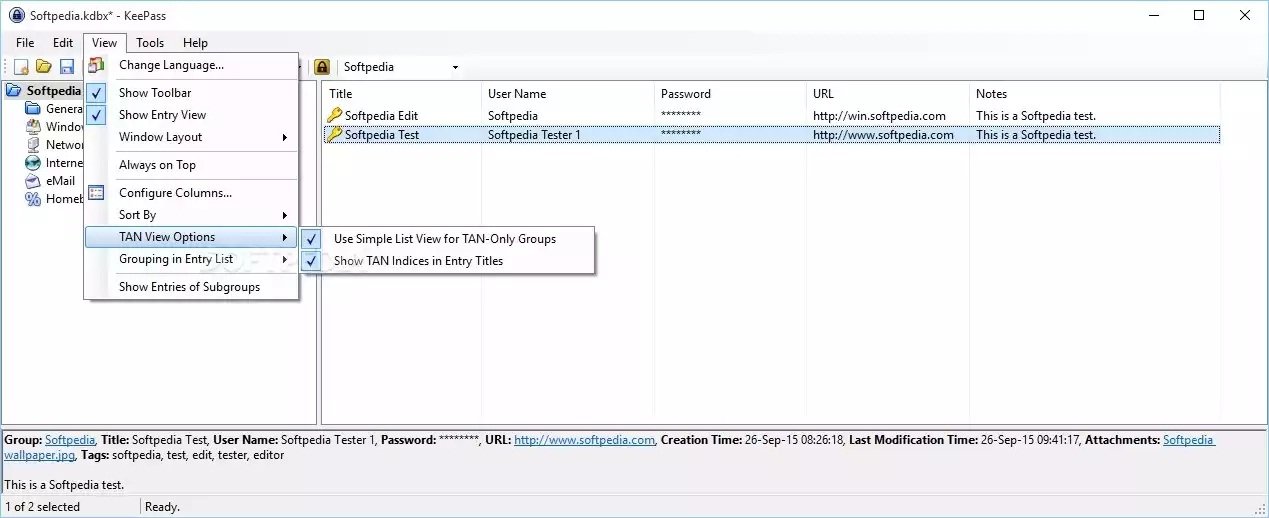
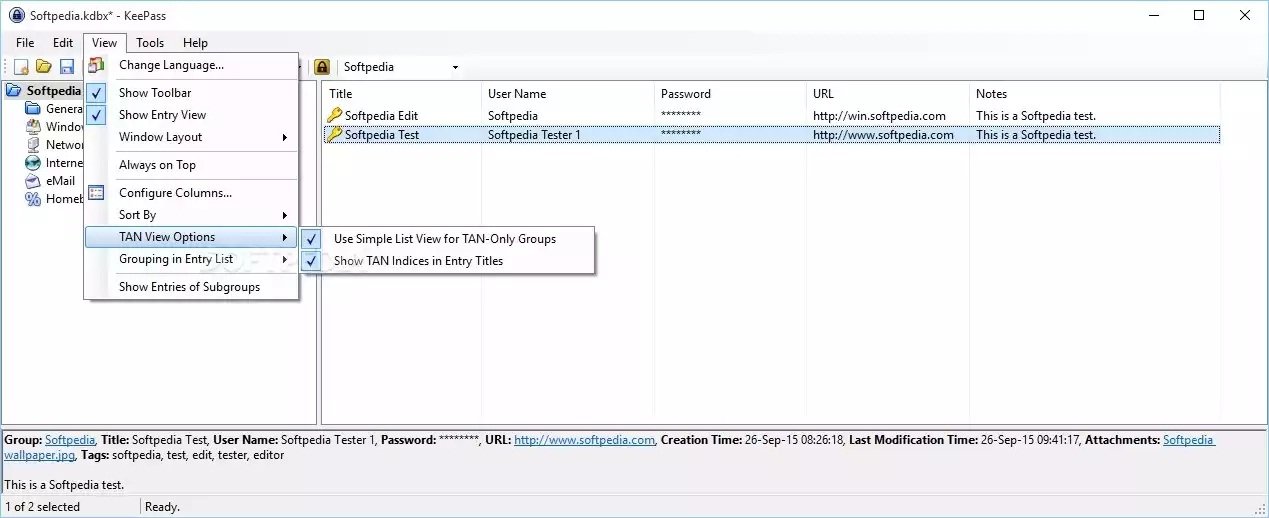
1.2KData SecurityHack KeePass – Extract KeePass master password from Memory using this tool
KeePass is a piece of software that is both open-source and free to use. It is a trusted companion for users of...
-
 1.9KVulnerabilities
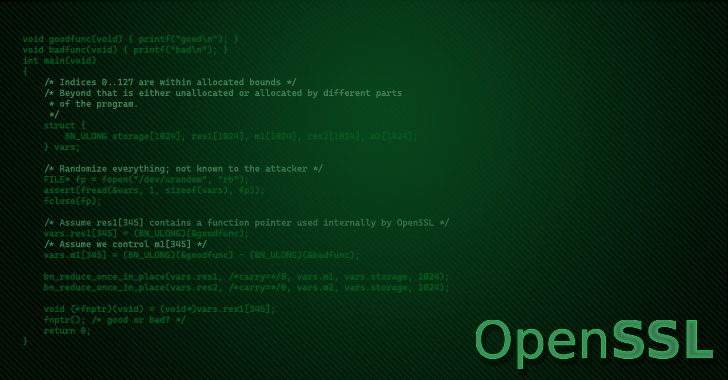
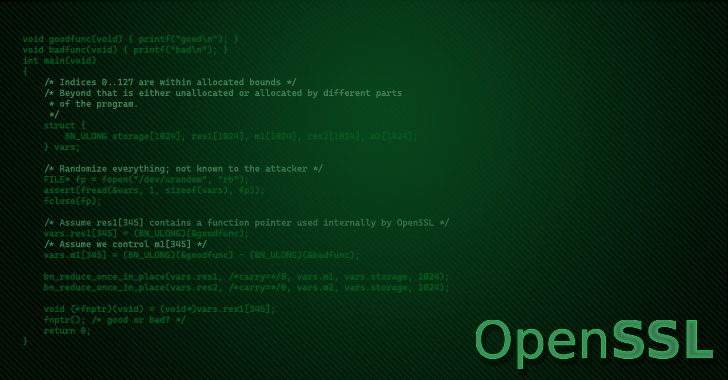
1.9KVulnerabilitiesOpenSSL to Release Security Patch for Remote Memory Corruption Vulnerability
The latest version of the OpenSSL library has been discovered as susceptible to a remote memory-corruption vulnerability on select systems. The issue...
-

 667Vulnerabilities
667VulnerabilitiesImportant memory leak vulnerabilities in F5 firewalls: Patch immediately
Information security specialists reported the detection of two security flaws affecting several firewall models developed by technology firm F5 Networks. According to...
-
 5.0KVulnerabilities
5.0KVulnerabilitiesCritical memory leak and authorization vulnerability in Bareos, a backup and archiving solution
Information security specialists report the detection of two vulnerabilities in Bareos open-source software to back up, archive and restore files on the...
-

 2.4KTutorials
2.4KTutorialsHow to collect only valid evidence during forensic investigation and incident response processes instead of creating images of system memory
The cybersecurity community understands as cyber forensics the procedures and methodological techniques to identify, collect, preserve, extract, interpret, document and present the...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesMemory corruption vulnerability affects all versions of Mozilla released since 2012
Mozilla security teams announced the detection of a critical memory corruption flaw residing in its Network Security Services (NSS) cryptography libraries. This...
-
 4.7KMalware
4.7KMalwareNew Wslink Malware Loader Runs as a Server and Executes Modules in Memory
Cybersecurity researchers on Wednesday took the wraps off a “simple yet remarkable” malware loader for malicious Windows binaries targeting Central Europe, North...
-
 5.0KData Security
5.0KData SecurityNew Linux kernel memory corruption bug causes full system compromise
Researchers dubbed it a “straightforward Linux kernel locking bug” that they exploited against Debian Buster’s 4.19.0.13-amd64 kernel. In 2017, MacAfee researchers disclosed a...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesTwo critical vulnerabilities in Linux allow hackers to obtain data from kernel memory
Cybersecurity specialists reported the finding of two severe vulnerabilities in Linux-based operating systems that could allow threat actors to bypass the mitigations...
-

 3.5KTutorials
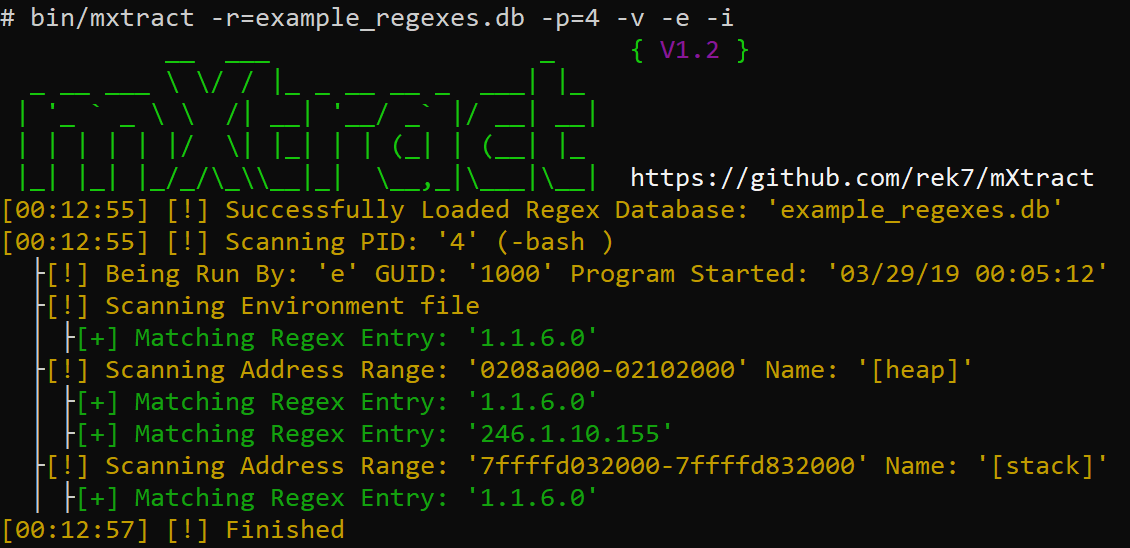
3.5KTutorialsSteps to do RAM memory forensics to recover passwords & confidential information with mXtract
The information stored on a computer does not always end up on permanent storage drives (hard drives, solid-state drives, removable storage, among...
-
 3.4KHack Tools
3.4KHack ToolsDonut – Generates X86, X64, Or AMD64+x86 Position-Independent Shellcode That Loads .NET Assemblies, PE Files, And Other Windows Payloads From Memory
Donut generates x86 or x64 shellcode from VBScript, JScript, EXE, DLL (including .NET Assemblies) files. This shellcode can be injected into an...
-

 335News
335NewsThis Newly Proposed Linux Memory Controller To Save Up To 42% RAM
Roman Gushchin, who is part of Facebook’s Linux kernel engineering team, has discovered a “serious flaw” in the way that the current...
-
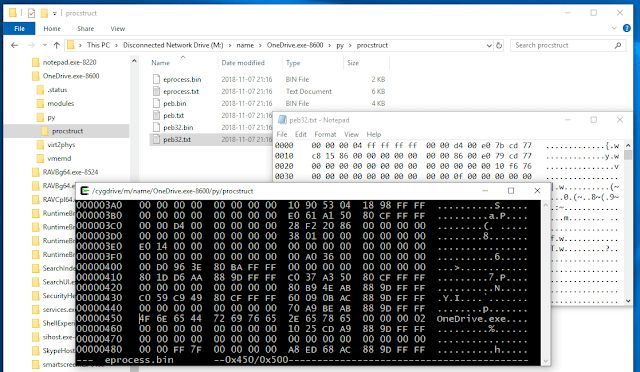
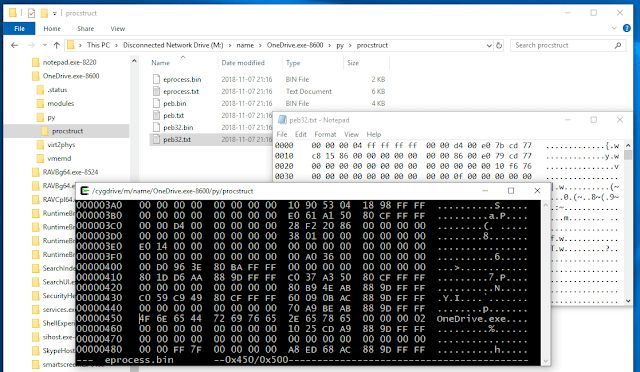 454Forensics Tools
454Forensics ToolsMemProcFS – The Memory Process File System
The Memory Process File System is an easy and convenient way of accessing physical memory as files a virtual file system....
-

 427Vulnerabilities
427VulnerabilitiesFacebook Patches “Memory Disclosure Using JPEG Images” Flaws in HHVM Servers
Facebook has patched two high-severity vulnerabilities in its server application that could have allowed remote attackers to unauthorisedly obtain sensitive information or...
-

 238News
238News‘Universal Memory’ Could Be The Perfect Data Storage Device For Your PC
Researchers have developed and patented a new type of computer memory that holds the key to solving the energy crisis that is...
-
 327Data Security
327Data SecurityRAMBleed attack steals sensitive data from computer memory
“RAMBleed Reading Bits in Memory Without Accessing Them.” A team of security researchers has published a report on a relatively advanced and...
-
 250News
250NewsMemory Corruption Zero-Day Bug Found In Windows Notepad App
Security researcher Tavis Ormandy, who is a part of the Google Project Zero team, has already unearthed some serious bugs and threats...
-
 317Hack Tools
317Hack ToolsmXtract – Offensive Memory Extractor & Analyzer
mXtract is an opensource linux based tool that analyzes and dumps memory. It is developed as an offensive pentration testing tool, its...
-
 313News
313NewsLinux 5.1 Might Add Support For Using Persistant Memory As System RAM
There are numerous differences when it comes to traditional RAM and flash storage. While both might be using solid state technologies, RAM is known to be...
-

 323News
323NewsSanDisk And Micron Unveil 1TB Memory Cards At MWC 2019
As 5G smartphones are becoming a thing (we have seen a couple of 5G phones at MWC 2019), memory cards with mammoth-sized...
-

 1.3KData Security
1.3KData SecurityMemory and Swap File Protection: Reforms Password Managers Need To Implement
If you are using passwords in multiple Web services etc., if that one-and-only password gets leaked, your entire Internet identity and access...






