Search results for "Opera"
-

 378Vulnerabilities
378VulnerabilitiesCritical Vulnerability Alert: VMware Aria Operations Networks at Risk from Remote Attacks
VMware has released software updates to correct two security vulnerabilities in Aria Operations for Networks that could be potentially exploited to bypass...
-
 5.0KMalware
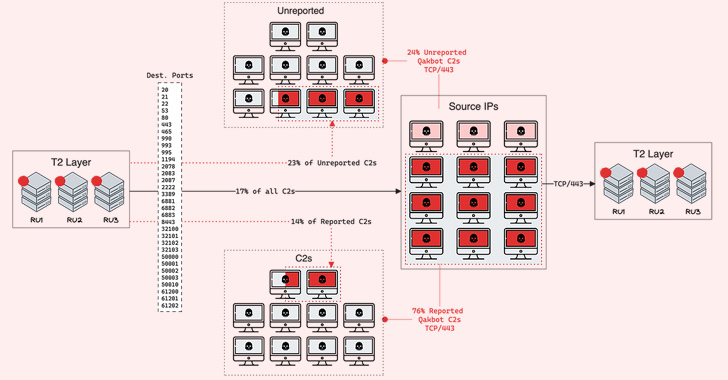
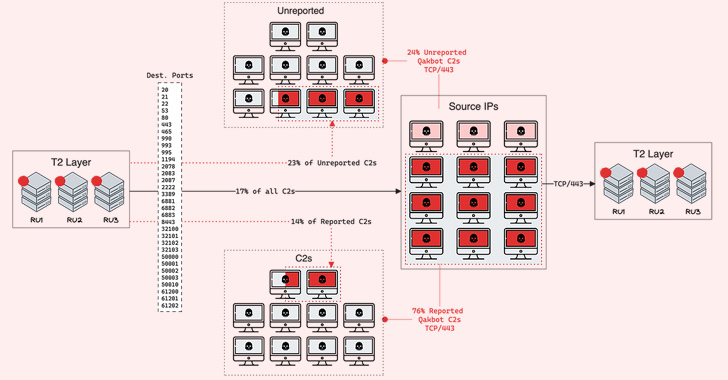
5.0KMalwareQakBot Malware Operators Expand C2 Network with 15 New Servers
The operators associated with the QakBot (aka QBot) malware have set up 15 new command-and-control (C2) servers as of late June 2023....
-

 2.3KMalware
2.3KMalwareBlackCat Operators Distributing Ransomware Disguised as WinSCP via Malvertising
Threat actors associated with the BlackCat ransomware have been observed employing malvertising tricks to distribute rogue installers of the WinSCP file transfer...
-

 856Vulnerabilities
856VulnerabilitiesAlert! Hackers Exploiting Critical Vulnerability in VMware’s Aria Operations Networks
VMware has flagged that a recently patched critical command injection vulnerability in Aria Operations for Networks (formerly vRealize Network Insight) has come...
-

 4.2KData Security
4.2KData SecurityYes it is possible to hack someone via Chrome, Brave, Opera browser using this zero day flaw
The most widely used web browser in the world, Google Chrome, has been found to have a critical zero-day vulnerability that has...
-

 2.2KScams
2.2KScamsTricks of the trade: How a cybercrime ring operated a multi‑level fraud scheme
A peek under the hood of a cybercrime operation and what you can do to avoid being an easy target for similar...
-
 2.8KMalware
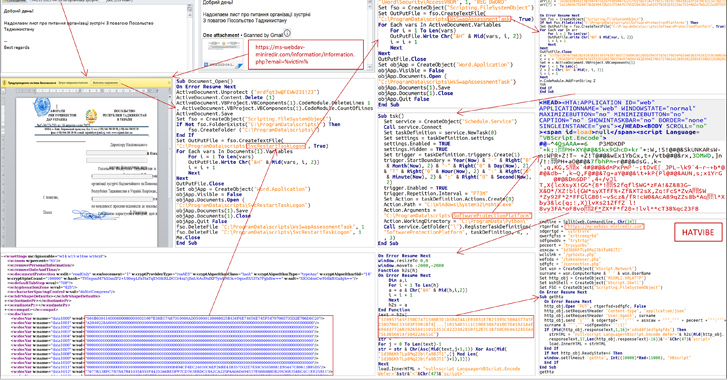
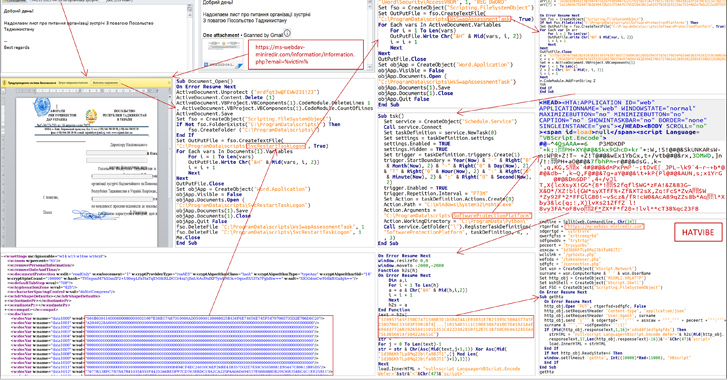
2.8KMalwareCyber Attacks Strike Ukraine’s State Bodies in Espionage Operation
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned of cyber attacks targeting state bodies in the country as part of...
-

 2.8KMalware
2.8KMalwareMeta Uncovers Massive Social Media Cyber Espionage Operations Across South Asia
Three different threat actors leveraged hundreds of elaborate fictitious personas on Facebook and Instagram to target individuals located in South Asia as...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesAnyone can hack into VMware Aria Log Operations servers using these vulnerabilities
On Thursday, the firm issued urgent fixes to resolve serious security flaws in the VMware Aria Operations for Logs product line (which...
-
 3.9KMalware
3.9KMalwareLazarus Group Adds Linux Malware to Arsenal in Operation Dream Job
The notorious North Korea-aligned state-sponsored actor known as the Lazarus Group has been attributed to a new campaign aimed at Linux users....
-

 4.1KData Breach
4.1KData BreachFBI Cracks Down on Genesis Market: 119 Arrested in Cybercrime Operation
A joint international law enforcement operation has dismantled Genesis Market, an illegal online marketplace that specialized in the sale of stolen credentials...
-

 4.1KCyber Attack
4.1KCyber AttackNorth Korean APT43 Group Uses Cybercrime to Fund Espionage Operations
A new North Korean nation-state cyber operator has been attributed to a series of campaigns orchestrated to gather strategic intelligence that aligns...
-

 3.1KCyber Attack
3.1KCyber AttackOperation Soft Cell: Chinese Hackers Breach Middle East Telecom Providers
Telecommunication providers in the Middle East are the subject of new cyber attacks that commenced in the first quarter of 2023. The...
-

 2.2KMalware
2.2KMalwareNorth Korean UNC2970 Hackers Expands Operations with New Malware Families
A North Korean espionage group tracked as UNC2970 has been observed employing previously undocumented malware families as part of a spear-phishing campaign...
-

 5.0KMalware
5.0KMalwareResearchers Share New Insights Into RIG Exploit Kit Malware’s Operations
The RIG exploit kit (EK) touched an all-time high successful exploitation rate of nearly 30% in 2022, new findings reveal. “RIG EK...
-
 2.8KMalware
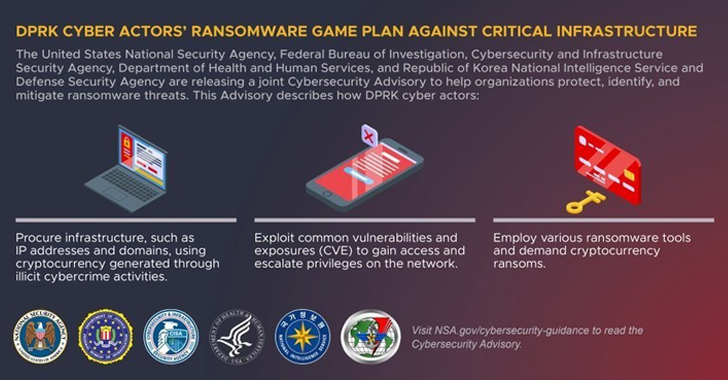
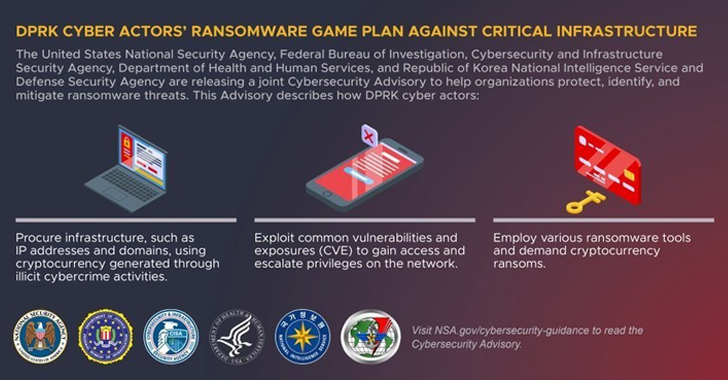
2.8KMalwareNorth Korean Hackers Targeting Healthcare with Ransomware to Fund its Operations
State-backed hackers from North Korea are conducting ransomware attacks against healthcare and critical infrastructure facilities to fund illicit activities, U.S. and South...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesCritical XSS flaw in phpMyAdmin allows malicious database operations
phpMyAdmin is a web-based application that is both open-source and free, and it was developed for the purpose of administering MySQL and...
-

 1.4KIncidents
1.4KIncidentsRansomware attack stalls operations of big mining company
The CMMC is owned by Mitsubishi Materials Corporation. It generates an average of 100 million pounds of copper per year and has an...
-

 872Incidents
872IncidentsElectric automaker Nio hacked. Ransomware operators are demanding bitcoin worth $2.25 million for not leaking customer data
Nio Inc., which is located in China, said on Tuesday that hackers had broken into its computer systems and acquired data on...
-

 4.9KIncidents
4.9KIncidentsRansomware attack shuts down operations of firefighters at 85 Australian fire stations
Fire Rescue Victoria’s (FRV) emails, phones, and emergency dispatch systems that automate firefighters’ tasks, such as opening station doors as soon as...
-
 1.2KMalware
1.2KMalwareDucktail Malware Operation Evolves with New Malicious Capabilities
The operators of the Ducktail information stealer have demonstrated a “relentless willingness to persist” and continued to update their malware as part...






