Search results for "Phishing"
-

 4.7KPhishing
4.7KPhishingTelegram – New Market Place for Selling Phishing Toolkits & Services
Telegram is becoming an increasingly popular platform for users as well as cyber-criminals. It has become a Mini Dark-web since 2021 when...
-
 722Cyber Attack
722Cyber AttackAttackers Flood NPM Repository with Over 15,000 Spam Packages Containing Phishing Links
In what’s a continuing assault on the open source ecosystem, over 15,000 spam packages have flooded the npm repository in an attempt...
-
 2.4KHow To
2.4KHow ToWriting like a boss with ChatGPT and how to get better at spotting phishing scams
It’s never been easier to write a convincing message that can trick you into handing over your money or personal data
-

 2.9KPhishing
2.9KPhishingNamecheap Emails Hacked To Send Phishing Email
The email account of domain registrar Namecheap was compromised which led to a flood of DHL and MetaMask phishing emails that sought...
-
 4.5KMalware
4.5KMalwareNew kind of phishing attacks are exploiting Microsoft OneNote to bypass disabled macro
OneNote is one of the most popular components of the Microsoft 365 package, which the firm is still working to improve even...
-
 2.0KMalware
2.0KMalwareThe Evolving Tactics of Vidar Stealer: From Phishing Emails to Social Media
The notorious information-stealer known as Vidar is continuing to leverage popular social media services such as TikTok, Telegram, Steam, and Mastodon as...
-

 594Malware
594MalwareBeware of Highly Sophisticated DarkTortilla Malware Distributed Via Phishing Sites
Cyble Research and Intelligence Labs (CRIL) detected threat Actors (TAs) distributing the malware DarkTortilla. Since 2015, the complex .NET-based malware known as DarkTortilla...
-

 3.6KPhishing
3.6KPhishingFacebook Infrastructure Used by Hackers in Phishing Attack Chain
A Meta-Phish attack that could lead to the loss of personally identifiable information (PII), login information, and a Facebook profile link was...
-

 2.7KData Security
2.7KData Security3 Techniques that allow bypassing phishing emails through Cisco Secure Email Gateway and are being actively used by ransomware gangs
The following techniques have been made public by a researcher who wishes to remain anonymous. They can be used to bypass certain of...
-

 3.4KMalware
3.4KMalwareLuna Moth Gang Invests in Call Centers to Target Businesses with Callback Phishing Campaigns
The Luna Moth campaign has extorted hundreds of thousands of dollars from several victims in the legal and retail sectors. The attacks...
-

 2.1KMalware
2.1KMalwareChinese Hackers Using 42,000 Phishing Domains To Drop Malware On Victims Systems
An extensive phishing campaign targeting businesses in numerous upright markets, including retail, was discovered by Cyjax recently in which the attackers exploited...
-
 1.4KData Security
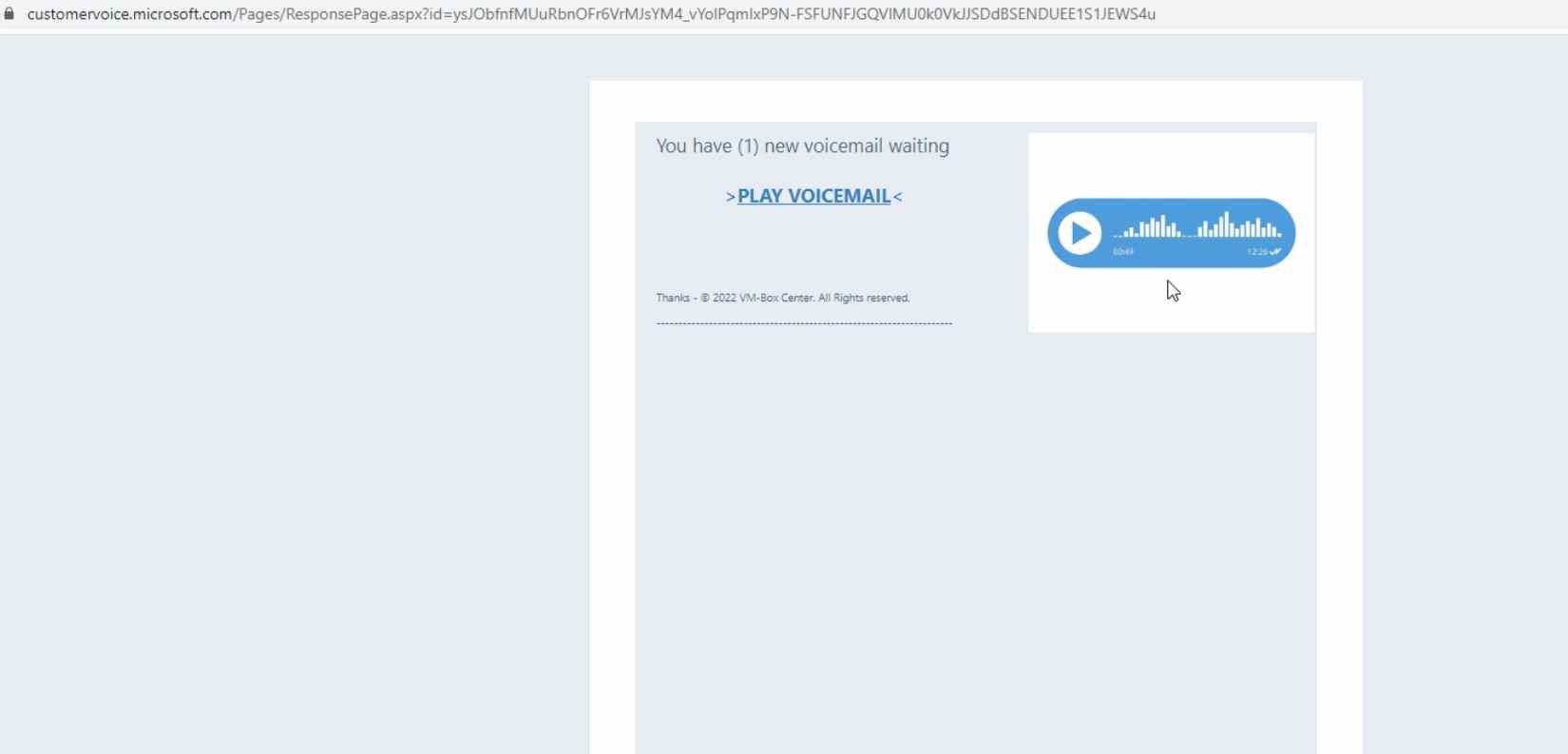
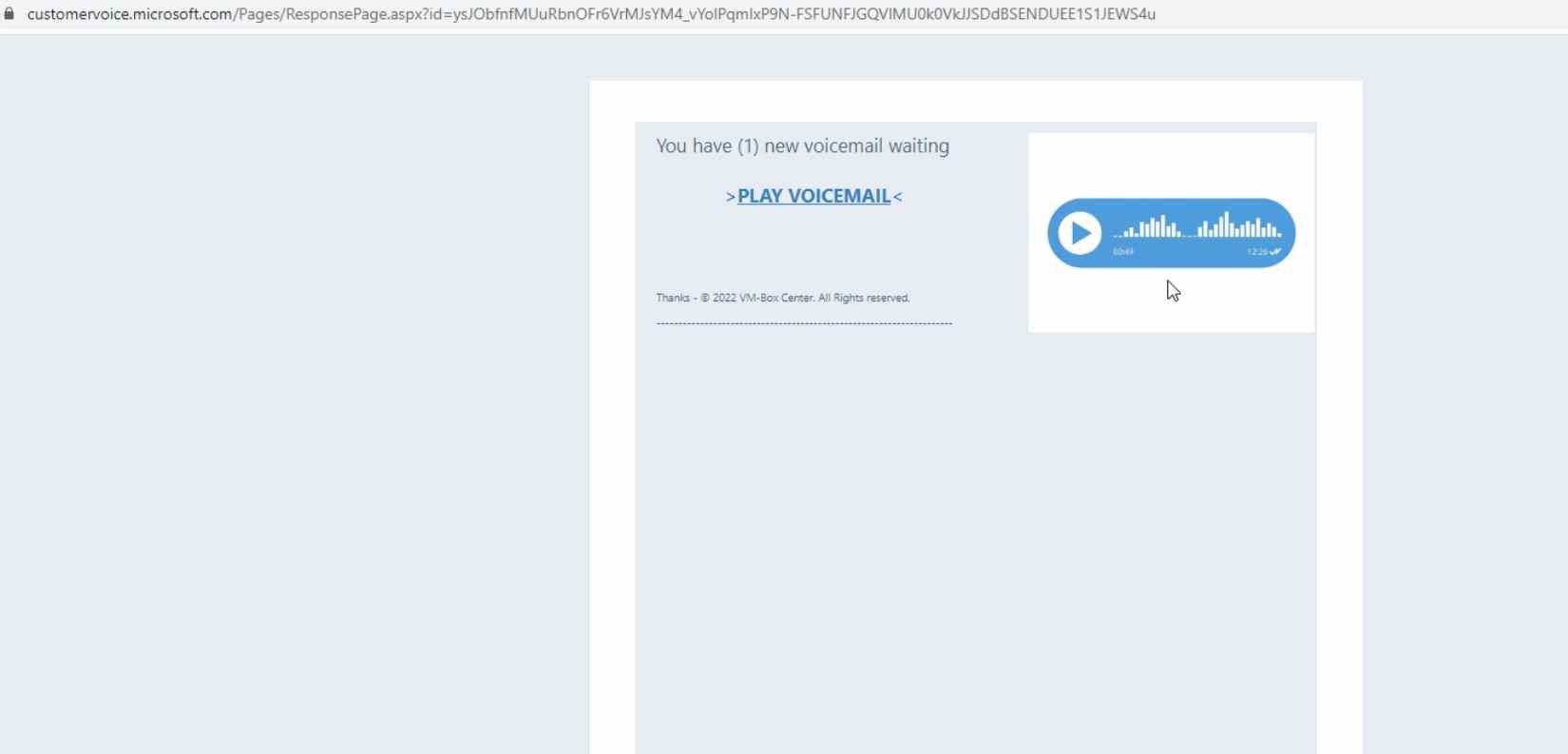
1.4KData SecurityDon’t open emails from Microsoft Dynamics 365. Threat actors are exploiting its flaws to send phishing emails with legitimate Microsoft links
Microsoft’s Dynamics 365 Customer Voice is a software that is primarily used to collect customer feedback.It may be utilized to gather data...
-

 2.8KLeaks
2.8KLeaksCISA Urges Organizations to Implement Phishing-Resistant MFA
By deploying phishing-resistant multi-factor authentication (MFA) and number matching in MFA applications, organisations may defend themselves against phishing and other attacks, according...
-
 4.7KIncidents
4.7KIncidentsDropBox hacked again via simple phishing email. Is cybersecurity awareness training is important for employees ?
Threat actors used employee login information they had obtained through phishing to log into one of Dropbox’s GitHub accounts, where they stole...
-

 223Malware
223MalwareMitsu Malware Stealer Downloaded Through AnyDesk Phishing Site to Steal Passwords
Cybersecurity experts at Cyble Research and Intelligence Labs (CRIL) have recently identified a fake AnyDesk website (hxxp://anydesk[.]ml). They found this website was...
-

 3.9KMalware
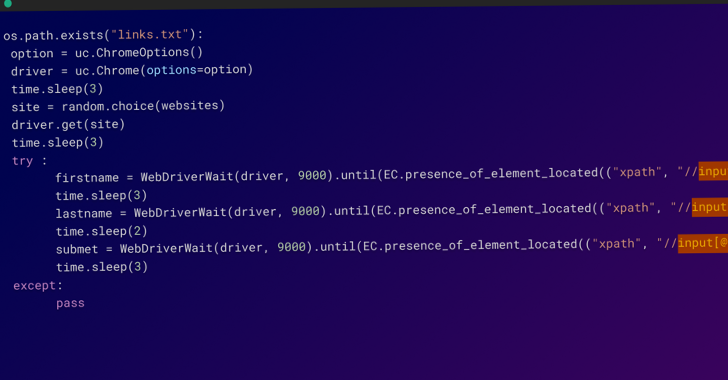
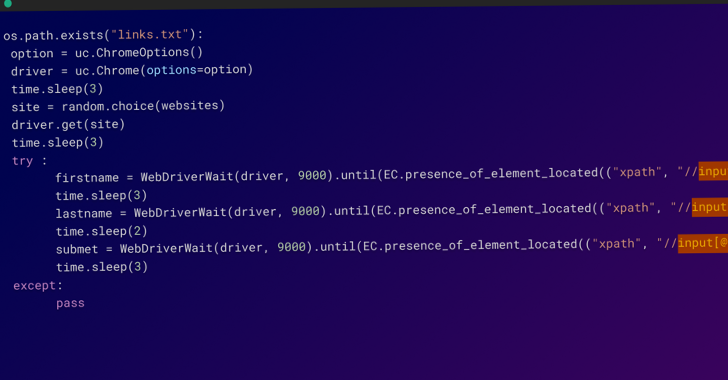
3.9KMalwarePhishing-as-a-Service Platform Lets Anyone Launch Own Phishing Campaigns
With the release of the PhaaS platform called ‘Caffeine’, threat actors can now easily launch their own sophisticated phishing attacks. Anyone who...
-

 1.3KData Security
1.3KData SecurityPhishing alert: Giving your condolences for Queen Elizabeth II can leave your data in the hands of cybercriminals
Cybercriminals are taking advantage of the death of Queen Elizabeth II to launch phishing attacks, specifically these scammers directing users to malicious...
-

 2.7KLeaks
2.7KLeaksnovoShield Emerges From Stealth With Mobile Phishing Protection App
With an enterprise-grade iPhone protection app, mobile phishing defense firm novoShield has come out of hiding. According to novoShield, the new solution...
-

 4.3KMalware
4.3KMalwareConti Cybercrime Cartel Using ‘BazarCall’ Phishing Attacks as Initial Attack Vector
A trio of offshoots from the notorious Conti cybercrime cartel have resorted to the technique of call-back phishing as an initial access...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesHackers Use Open Redirect Vulnerabilities in Online Services to Deliver Phishing Content
Researchers at Resecurity noticed threat actors leveraging Open Redirect Vulnerabilities which is popular in online services and apps to evade spam filters...
-
 1.2KMalware
1.2KMalwareResearchers Warns of Increase in Phishing Attacks Using Decentralized IPFS Network
The decentralized file system solution known as IPFS is becoming the new “hotbed” for hosting phishing sites, researchers have warned. Cybersecurity firm...






