Search results for "Phishing"
-

 4.0KSocial Media
4.0KSocial MediaTwitter breach: Staff tricked by ‘phone spear phishing’
The attackers exploited the human factor to gain access to Twitter’s internal systems and the accounts of some of the world’s most...
-

 1.6KLeaks
1.6KLeaksTop 5 Phishing Protection Solutions for 2022
A phishing email is one of the very first phases of a phishing attack. It is easy to deploy and monitor and...
-

 1.5KLeaks
1.5KLeaksTop 5 Phishing Protection Solutions for 2020
A phishing email is one of the very first phases of a phishing attack. It is easy to deploy and monitor and...
-
 3.7KPhishing
3.7KPhishingBeware of Zoom Phishing Campaign that Threatens Employees Contracts will be Suspended or Terminated
A new zoom phishing campaign observed asking recipients to join a zoom meeting that threatens employees that their contracts will be either...
-

 3.7KScams
3.7KScamsPayPal remains the most‑spoofed brand in phishing scams
WhatsApp also emerges as a favorite target for brand impersonation amid a general spike in social media phishing
-

 4.0KScams
4.0KScamsWould you get hooked by a phishing scam? Test yourself
As the tide of phishing attacks rises, improving your scam-spotting skills is never a bad idea
-
 5.5KPhishing
5.5KPhishing16Shop – Malware-as-a-service Phishing Toolkit Attack PayPal Users With Anti-Detection Techniques
A prolific phishing kit distribution network dubbed “16Shop” believed to be active since 2018 and developed by a hacking group called the...
-

 550Phishing
550PhishingCATPHISH – Phishing and Corporate Espionage
CATPHISH is a tool to generate similar-looking domains for phishing attacks. The program will check expired domains and if they are categorized...
-

 496Incidents
496IncidentsHackers invested only $160 USD in a phishing campaign that infected over 70k victims. How did they do it?
Information security specialists have revealed details about a recent cybercriminal campaign identified as “MasterMana Botnet”, related to multiple key concepts in the...
-

 300Vulnerability Analysis
300Vulnerability AnalysisPhishing-Simulation – Aims To Increase Phishing Awareness
Phishing Simulation mainly aims to increase phishing awareness by providing an intuitive tutorial and customized assessment (without any actual setup –...
-

 565Cyber Crime
565Cyber CrimeNew Amazon phishing scam stealing credit card data
A new Amazon phishing scam email is circulating, that tricks users into handing over their personal as well as financial information including...
-
 340Phishing
340PhishingPhishing Simulation – Phishing Assessment Tool
Phishing Simulation mainly aims to increase phishing awareness by providing an intuitive tutorial and customized assessment (without any actual setup – no...
-

 498Cyber Crime
498Cyber CrimeMicrosoft, PayPal & Facebook most targeted brands in phishing scams: Report
When it comes to phishing scams, Microsoft has turned out to be the most preferred target for hackers while PayPal, Facebook, and...
-

 333News
333NewsDetecting and Defending Against Phishing Attacks
One of the most persistent security challenges is phishing. This is true for both organizations and individuals. Whether gaining access to credit...
-

 306Phishing
306PhishingFiercePhish – Full-fledged Phishing Framework
FiercePhish is a full-fledged phishing framework to manage all phishing engagements. It allows you to track separate phishing campaigns, schedule sending of...
-

 318News
318NewsPhishing Attacks Still Trending And On The Rise
GreatHorn, an incident-response consulting firm has released their Email Security, Challenges, Trends and Benchmark Report 2019 revealing that the corporate world and...
-
 340Phishing
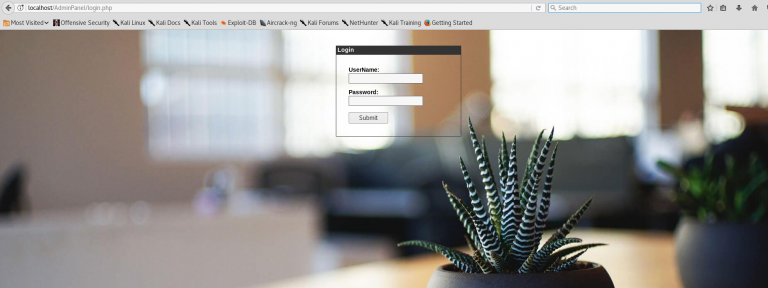
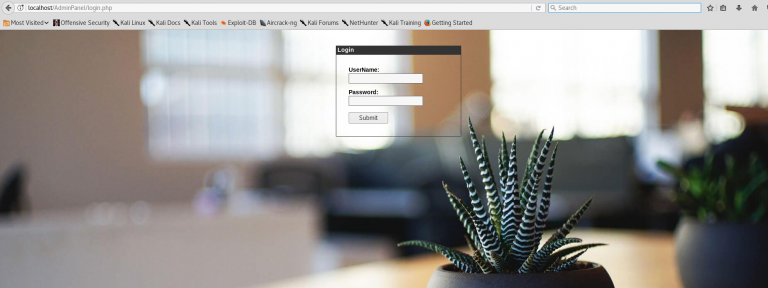
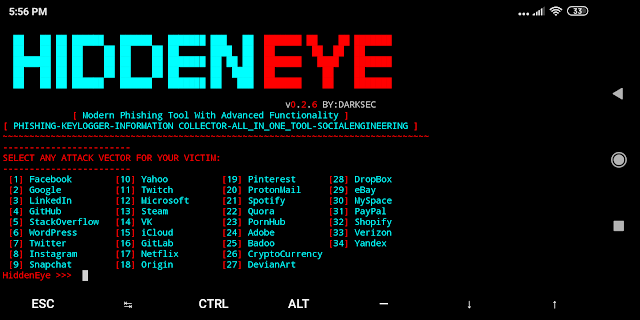
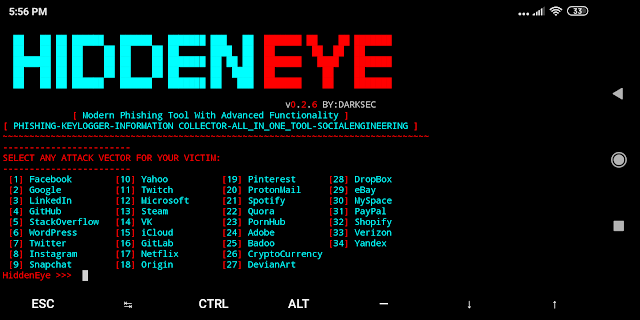
340PhishingHidden Eye – Modern Phishing Tool With Advanced Functionality
Ultimate Phishing tool with android support available comes with 34 attack vectors of the most popular used services. Hidden Eye Modern Phishing...
-

 424Malware
424MalwareIran retaliates against cyber warfare using dangerous malware and phishing attacks against LinkedIn users
The tension generated by the cyber warfare between the United States, and its allies, and Iran keeps growing. Although some information security...
-

 392News
392NewsSpear-Phishing: How to Protect Yourself From an Attack
Spear-Phishing Even with the number of messaging apps available now, companies still use email. On average, a person receives over a hundred...
-

 478News
478NewsYouTube Bans ‘Hacking And Phishing’ Videos; Pisses Off Infosec Guys
As the number of users on the platform has increased over the years, so has YouTube’s list of ‘banned content.’ Adding further...
-

 410How To
410How ToPhishing in 2019 – Still Working After All These Years
Phishing has been around a long time because it still works. No matter what companies do in terms of technology and security...






