Search results for "Plugin"
-

 182Data Security
182Data SecurityWidely used WebEx plugin for Chrome will execute attack code—patch now!
Publicly known “magic string” lets any site run malicious code, no questions asked. The Chrome browser extension for Cisco Systems WebEx communications...
-

 159Vulnerabilities
159VulnerabilitiesWordPress Plugin Stop User Enumeration does not stop user enumeration
User Enumeration is the capacity to automatically figure out if a given account is valid on a system. By enumerating client accounts, you are at...
-
 192Malware
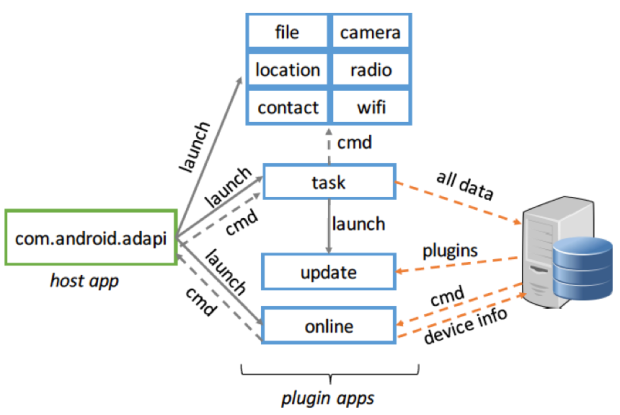
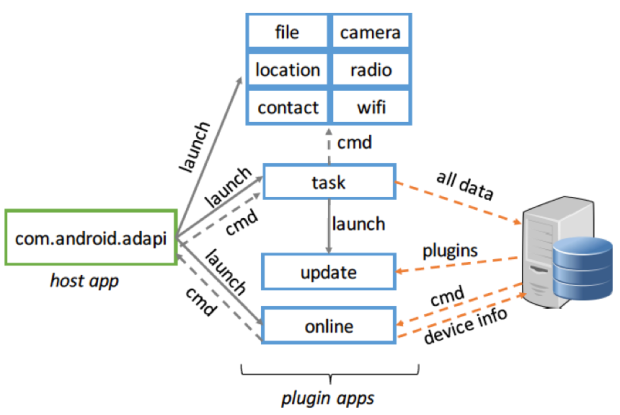
192MalwarePluginPhantom: New Android Trojan Abuses “DroidPlugin” Framework
Recently, we discovered a new Google Android Trojan named “PluginPhantom”, which steals many types of user information including: files, location data, contacts...
-

 241Data Security
241Data SecurityCrooks exploit a zero-day in WordPress eCommerce Plugin to upload a backdoor
Experts from the White Fir Design discovered cybe rcriminals exploited a zero-day flaw in an e-commerce plugin for WordPress to upload a...
-

 197Malware
197MalwareFake Social Button Plugin Redirects to Angler EK
Compromised websites remain one of the surefire ways to redirect innocent visitors to exploit kits. During the past few days we’ve started seeing...
-

 170Data Security
170Data SecurityPopular WordPress Plugin Comes With a Backdoor, Steals Site Admin Credentials
Last summer we shared a story about the SweetCaptcha WordPress plugin injecting ads and causing malvertising problems for websites that leveraged the plugin....
-

 193Vulnerabilities
193VulnerabilitiesWordPress Jetpack Plugin Patched Against Stored XSS Vulnerability
After a few critical bugs were recently discovered and patched in the core WordPress engine—a rarity with WordPress-related security issues—order has apparently...
-
 327Data Security
327Data SecurityKovter AdFraud Malware Updates Flash Plugin to Latest Version
We all know that one of the basic procedures to keep our computer system secure and free from viruses and malware is...
-

 335Data Security
335Data SecurityXSS Vulnerability Found in Famous WordPress Plugins
Researchers have identified a relatively “common” cross-site scripting flaw (XSS) in some famous WordPress plugins — A coordinated plugin update has been released to...
-
 290Data Security
290Data SecurityWordPress Google Analytics Plugin by Yoast Vulnerable to critical site-hijacking
Yet another vulnerability has been found in the Yoast WordPress plugin that can be exploited by attackers allowing them to control the...
-
 261Data Security
261Data SecurityWordPress SEO by Yoast’ Plugin Vulnerable to Hackers, Affecting Millions Worldwide
A number of websites have been put at risk due to a very popular plugin of the WordPress content management platform vulnerability...
-

 314Data Security
314Data SecurityVulnerability in WordPress Plugin Allows Hackers to take full control of website
WordPress’s MainWP Child Plugin has vulnerability… and it is very much exploitable. Researchers at Sucuri have identified a vulnerability in the MainWP...
-

 121Malware
121MalwareHow Theola malware uses a Chrome plugin for banking fraud
A deep dive into Win32/Theola, one of the most malicious components of the notorious bootkit family, Win32/Mebroot.FX. Theola uses malicious Chrome browser...
-

 107Malware
107MalwareCaphaw attacking major European banks using webinject plugin
Analysis of malicious code dubbed Win32/Caphaw (a.k.a. Shylock) attacking major European banks, with ability to automatically steal money when the user is...
-
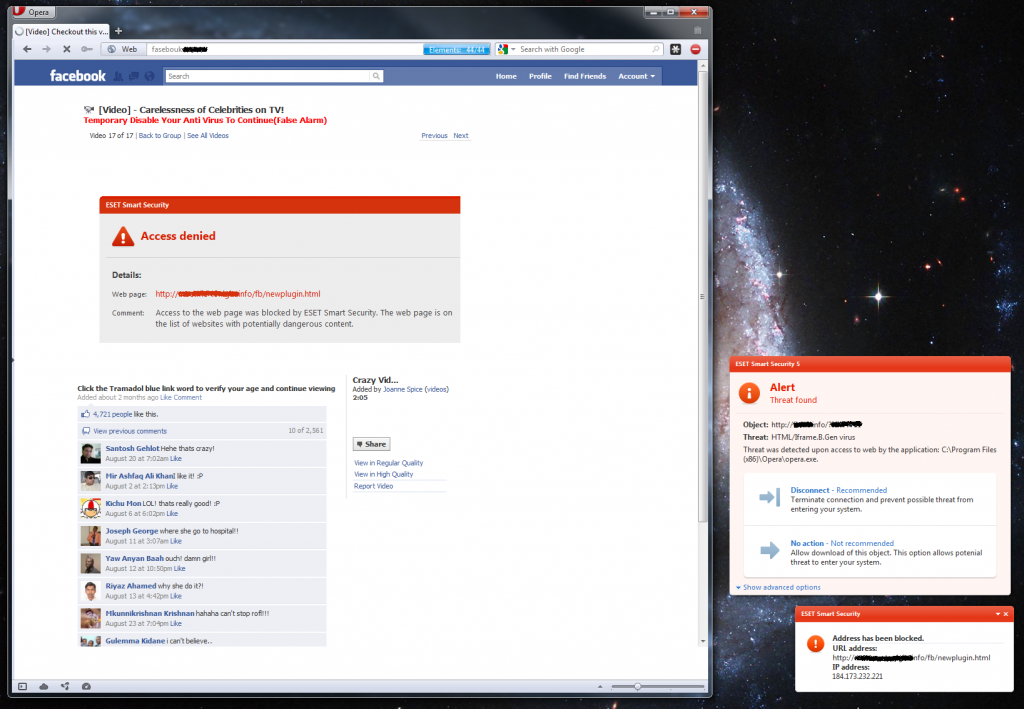
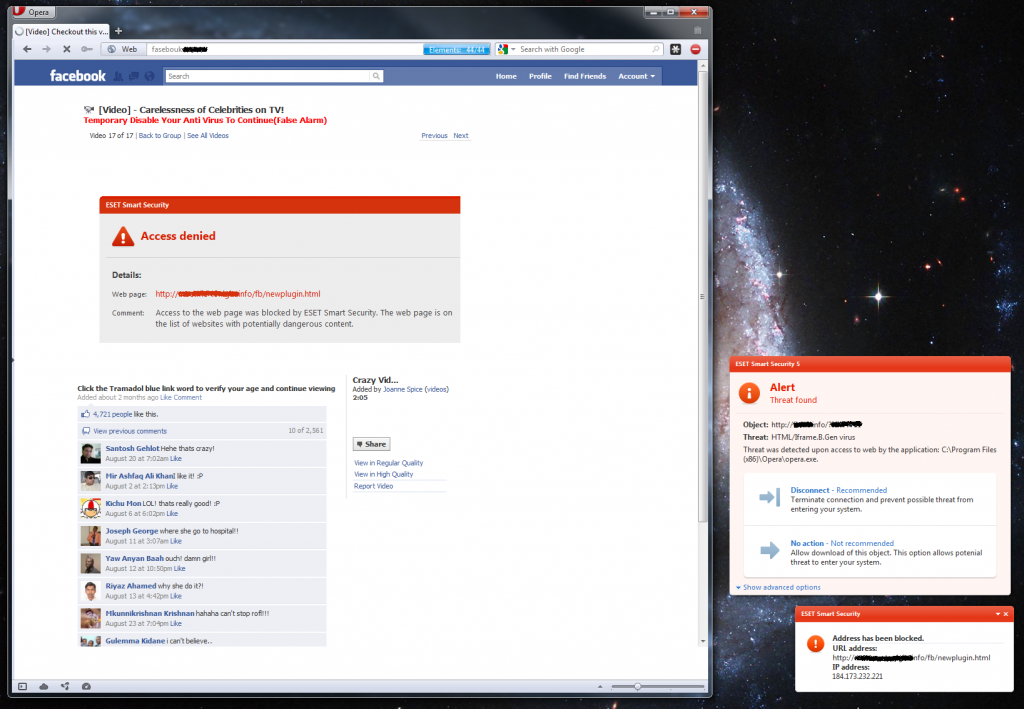 138Malware
138MalwareModern viral propagation: Facebook, shocking videos, browser plugins
Fraudsters continue to innovate their scam propagation methods. Again using Facebook and a pretense of a shocking video, they also utilize browser...






