Search results for "Protocols"
-
 3.1KVulnerabilities
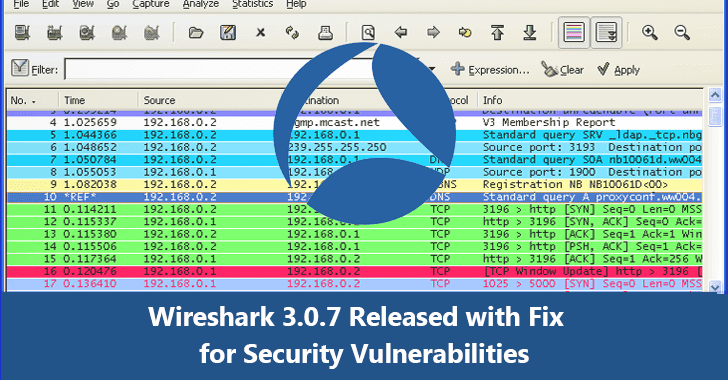
3.1KVulnerabilitiesWireshark 3.0.7 Released – Fixes for Security Vulnerabilities & Update for BGP, IEEE 802.11, TLS Protocols
Wireshark 3.0.7 released with a number of security updates and fixed several other bugs that reside in the Wireshark components. Wireshark also...
-

 312Infosec
312InfosecEmployees Actively Seeking Ways to Bypass Corporate Security Protocols in 95 % of Enterprises
Nowadays cyber incidents activities such as data theft, insider threat, malware attack most are significant security risks and some it caused by the...
-
 407Security Tools
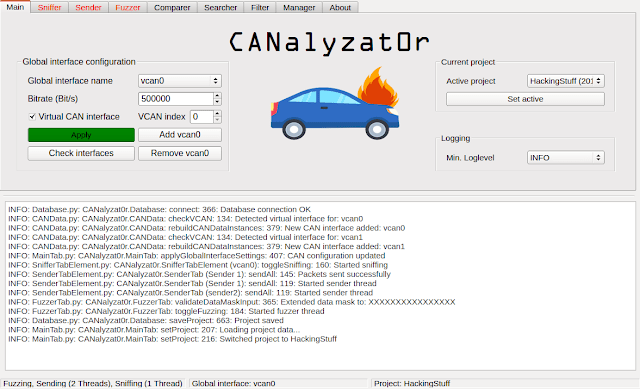
407Security ToolsCANalyzat0r – Security Analysis Toolkit For Proprietary Car Protocols
This software project is a result of a Bachelor’s thesis created at SCHUTZWERK in collaboration with Aalen University by Philipp Schmied.Please refer...
-
 354Geek
354GeekFlaws in RDP protocols leaving machines prone to remote code execution
Major Security Flaws Identified in RDP Protocols making Machines Prone to Remote Code Execution and Reverse RDP Attacks. Check Point researchers have...
-
 272Exploitation Tools
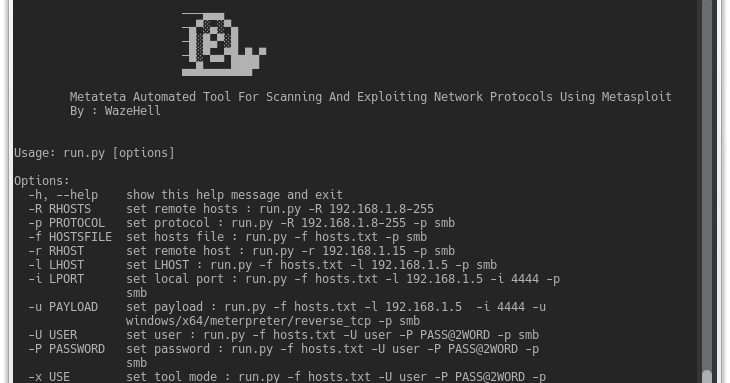
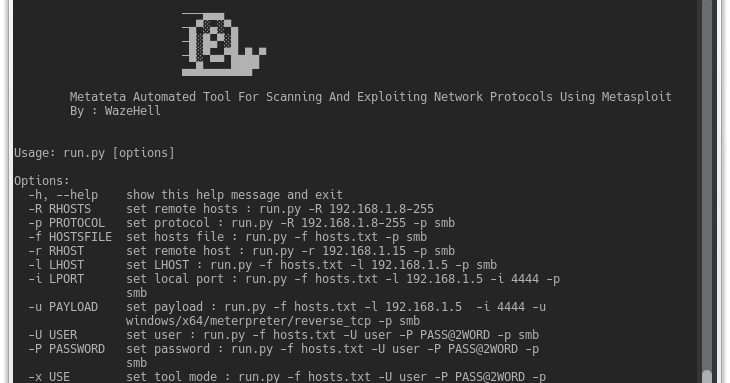
272Exploitation ToolsMetateta – Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit
Metateta Automated Tool For Scanning And Exploiting Network Protocols Using Metasploit For faster pen testing for large networks What You Can Do...
-
 264Network Tools
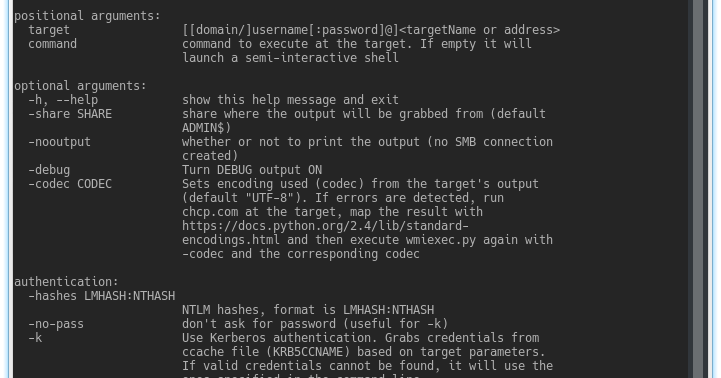
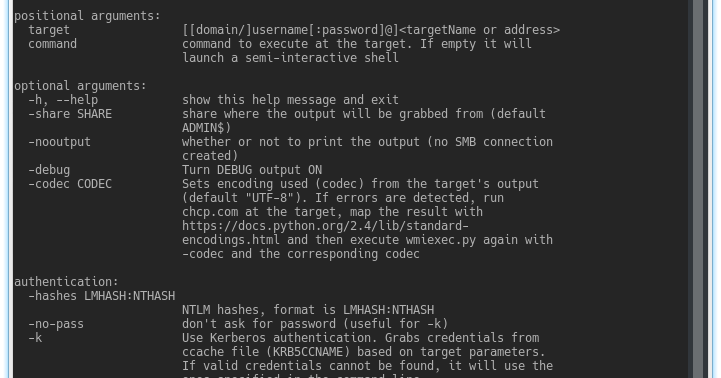
264Network ToolsImpacket – Collection Of Python Classes For Working With Network Protocols
Impacket is a collection of Python classes for working with network protocols. Impacket is focused on providing low-level programmatic access to the...
-
 210Hackers Repository
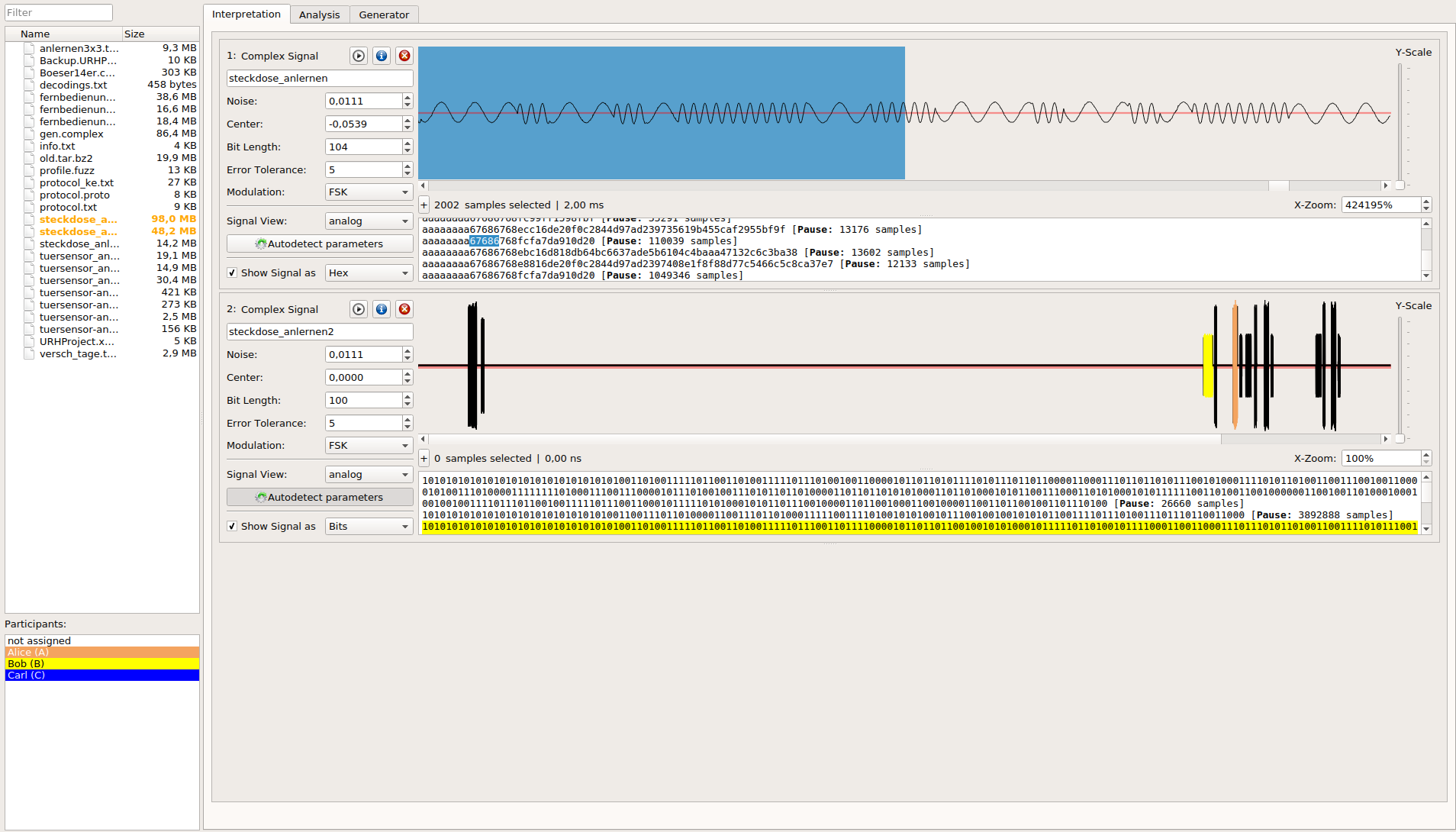
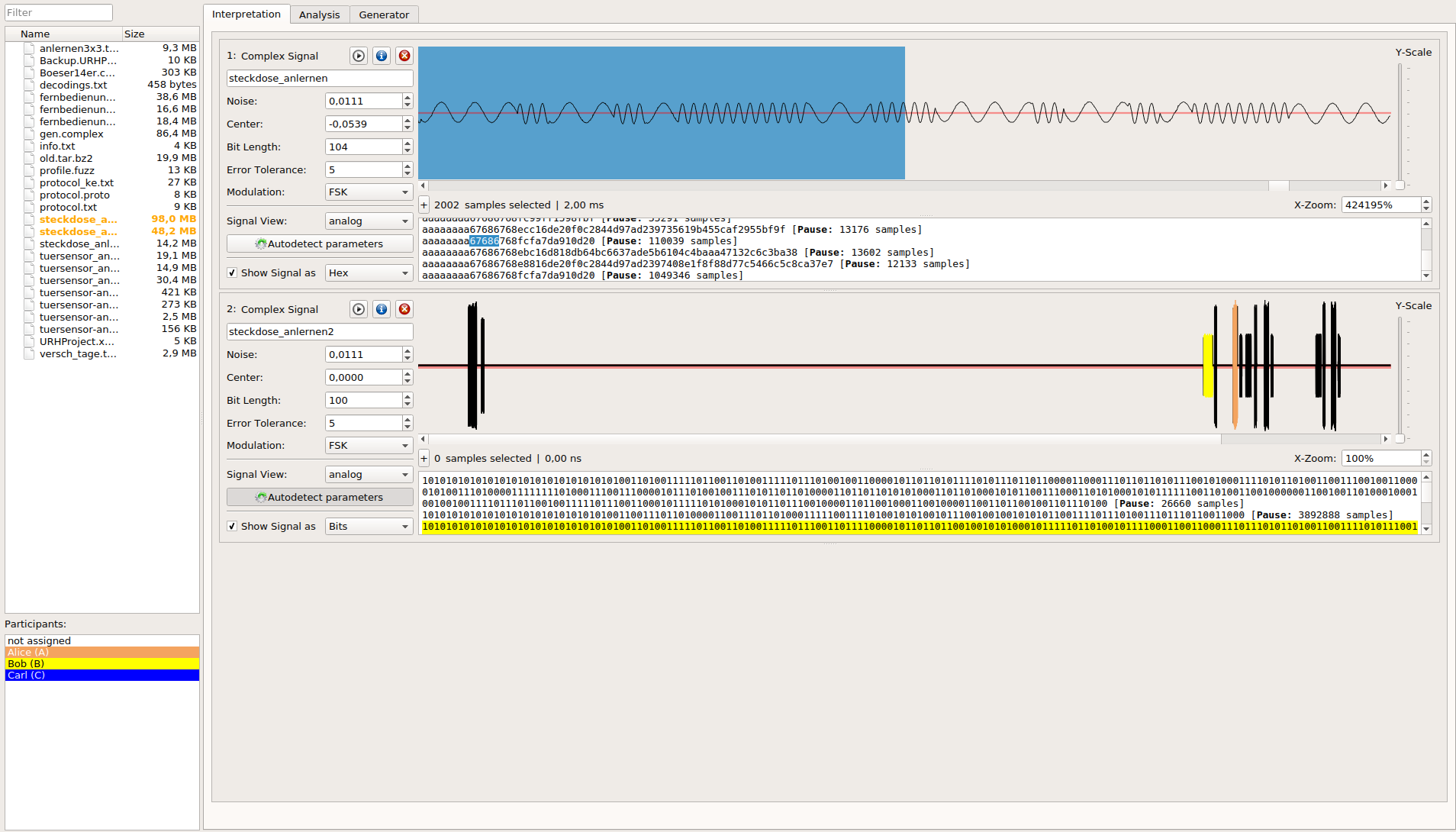
210Hackers RepositoryUniversal Radio Hacker: investigate wireless protocols like a boss
The Universal Radio Hacker is a software for investigating unknown wireless protocols. Features include hardware interfaces for common Software Defined Radios easy...
-
 386Geek
386GeekLDAP & RDP Relay Flaws Found in Windows Security Protocols
Security researchers at behavioral firewall specialist firm Preempt have discovered two critical security flaws in the Microsoft Windows NT LAN Manager (NTLM)...
-
 194Malware
194MalwareIndustroyer: ICS protocols were developed decades ago with no security in mind
Senior ESET malware researcher Robert Lipovsky discusses Industroyer, the biggest threat to Industrial Control Systems (ICS) since Stuxnet.
-

 223Data Security
223Data SecurityHackers Using Unmonitored System Tools, Protocols for Malicious Goals
The IT security researchers at Cisco’s security intelligence and research group Talos have discovered a malware that can fully hide its origins. The sample that...
-
 252How To
252How Todedsploit – Framework For Attacking Network Protocols
dedsploit is an open source software use for attacking network protocols and network exploitation. This framework aims to exploit and attack some common...
-

 199Vulnerabilities
199VulnerabilitiesVulnerability Exploitable via Printer Protocols Affects All Windows Versions
Introducing vulnerability of the year: CVE-2016-3238. Microsoft patched today a critical security vulnerability in the Print Spooler service that allows attackers to take...
-

 228Data Security
228Data SecurityCommon payment processing protocols found to be full of flaws
Stealing PINs and pillaging bank accounts are both trivial. Credit card users could have their PINs stolen, and merchants could have their bank...
-

 200Malware
200MalwareThe role of proxies and protocols in malware investigations
What is a proxy and what types of proxies exist? What protocol are used in the anonymization process? How does anonymity help...






