Search results for "Remote"
-
 2.3KVulnerabilities
2.3KVulnerabilitiesLatest Apple iOS Update Patches Remote Jailbreak Exploit for iPhones
Apple on Monday released updates to iOS, macOS, tvOS, and watchOS with security patches for multiple vulnerabilities, including a remote jailbreak exploit...
-

 1.7KData Security
1.7KData SecuritySMA 100 flaws in SonicWall VPN expose devices to remote takeover
If exploited, an unauthenticated, remote attacker can execute code as a “nobody user” in the device meaning attacker would get root access...
-

 1.8KMalware
1.8KMalwareOver 300,000 MikroTik Devices Found Vulnerable to Remote Hacking Bugs
At least 300,000 IP addresses associated with MikroTik devices have been found vulnerable to multiple remotely exploitable security vulnerabilities that have since...
-

 2.1KCyber Crime
2.1KCyber CrimeRemote access tools abused to spread malware and steal cryptocurrency
The new campaign also involves replacing cryptocurrency addresses shared via clipboard and setting up fake cryptocurrency websites. Trend Micro researchers have shared...
-

 3.0KHow To
3.0KHow ToHow to Securely Access Remote Desktop?
Having secure remote access for employees and following best practices is essential to keep your data secure. In the past few months,...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesHardcoded SSH Key in Cisco Policy Suite Lets Remote Hackers Gain Root Access
Cisco Systems has released security updates to address vulnerabilities in multiple Cisco products that could be exploited by an attacker to log...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesCritical remote code execution vulnerability in Linux Kernel TIPC module affects millions of devices. Patch immediately
Cybersecurity specialists report the patching of a critical vulnerability in the Transparent Inter Process Communication (TIPC) module, implemented in the Linux kernel...
-
 1.5KData Security
1.5KData SecurityWinRAR vulnerability allowed attackers to remotely hijack systems
The vulnerability in WinRAR trialware could be abused by a remote attacker for executing arbitrary code on any system thus, getting an...
-

 5.2KVulnerabilities
5.2KVulnerabilitiesCritical remote code execution vulnerability in WinRAR demo version. Update quickly
A critical vulnerability in the trial version of WinRAR 5.70 would allow threat actors to intercept and modify responses from the RarLab...
-

 587Vulnerabilities
587VulnerabilitiesZero-click remote code execution exploit for fully patched iOS 15 running on iPhone 13 demonstrated by experts
During the latest version of the Tianfu Cup event for ethical hackers, a group of researchers demonstrated a method to successfully hack...
-
 3.8KVulnerabilities
3.8KVulnerabilitiesCVE-2020-17148: Critical remote execution vulnerability in Visual Studio Code’s Remote Development extension
Cybersecurity specialists report the detection of a remote code execution (RCE) vulnerability in Visual Studio Code Remote Development, a platform that allows...
-
 3.4KVulnerabilities
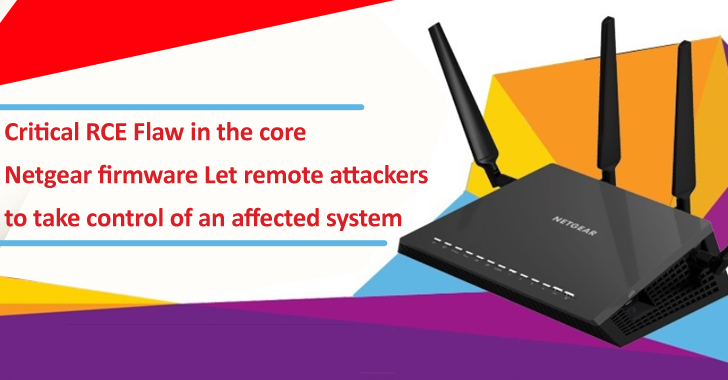
3.4KVulnerabilitiesCritical RCE Flaw in the core Netgear Firmware Let Remote Attackers to Take Control of an Affected System
The cybersecurity organization GRIMM has recently announced vulnerability research towards a series of Netgear SOHO devices. The vulnerability that has been discovered...
-
 1.2KRansomware
1.2KRansomwareCring Ransomware Gang Exploits 11 Years Old Adobe Bug & Take Over ColdFusion Server Remotely
Sophos researchers has uncovered an unusually clever ransomware gang, that is named as “Cring Ransomware” that Exploits Ancient ColdFusion Server. Here, the...
-

 781Vulnerabilities
781VulnerabilitiesCVE-2021-36260: Remotely hacking and spying on Hikvision CCTV systems with this zero-click vulnerability
Cybersecurity specialists report the detection of a dangerous “zero-click” vulnerability in a popular security camera model whose exploitation would allow threat actors...
-
 2.9KHow To
2.9KHow ToHow to Protect and Support a Remote Workforce
Remote working amid the COVID19 pandemic has become new normal but for cybercriminals, those working from home are a lucrative target. When...
-
 3.4KData Security
3.4KData Security$120 charging cable O.MG remotely steals data from Apple devices
Originally, O.MG Cable was introduced in 2019. In 2019, at DEFCON, an IT security researcher going by the online handle of MG...
-

 2.5KData Security
2.5KData SecurityWifiDemon – iPhone Wifi bug exposed devices to remote attacks
Dubbed WifiDemon by researchers; the attack required the victim’s wifi to be set on auto-join which is by default in iPhones. Just...
-
 4.6KData Security
4.6KData SecurityWestern Digital My Book Live hard drives remotely wiped by hackers
In recent news, people are shocked to find out all of their data stored on their Western Digital My Book Live hard...
-

 946Geek
946GeekWhy your remote employees may underperform? Top 10 problems
Organizing remote work is a challenge for any business owner. Read on to find workable strategies to maximize the output of your...
-
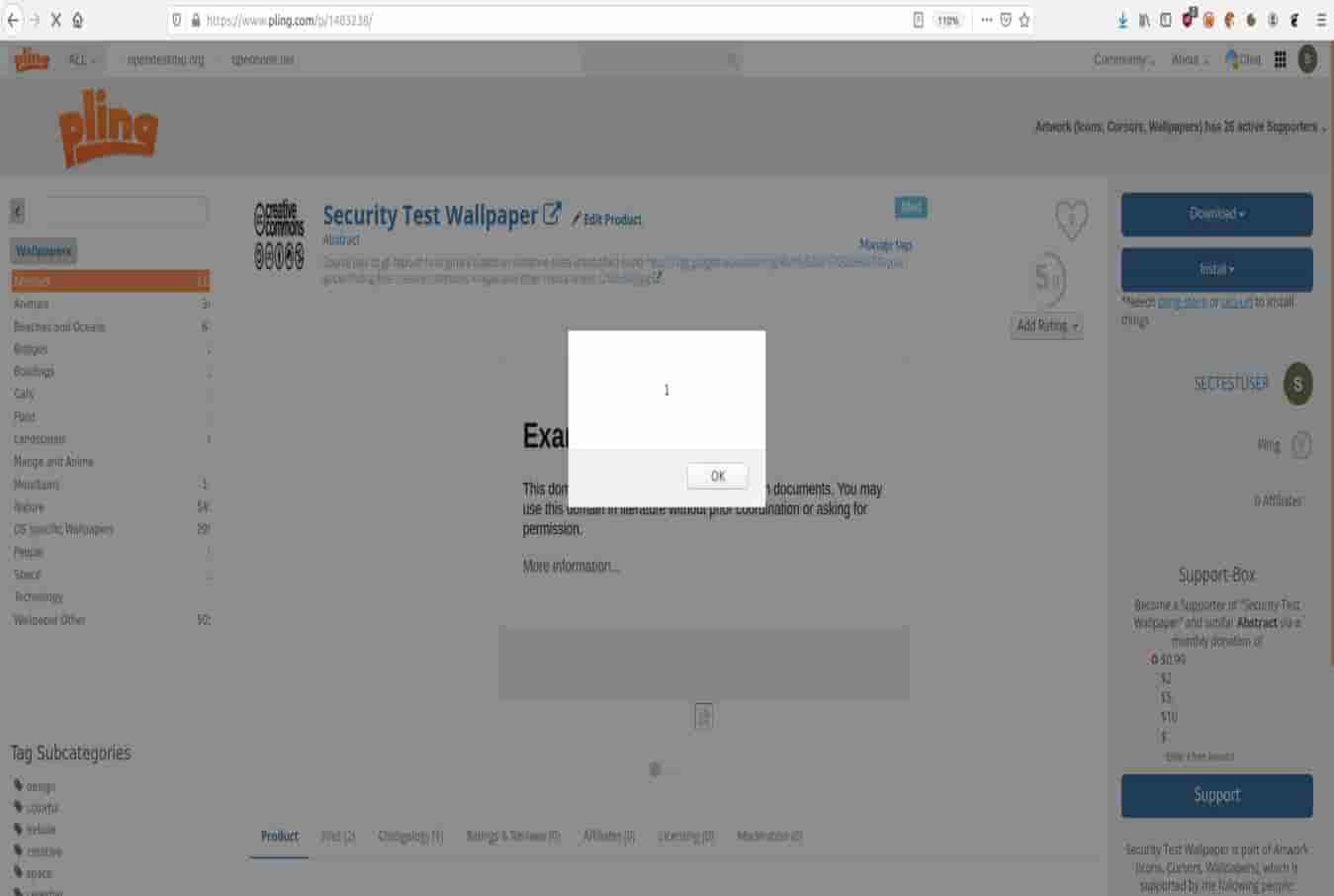
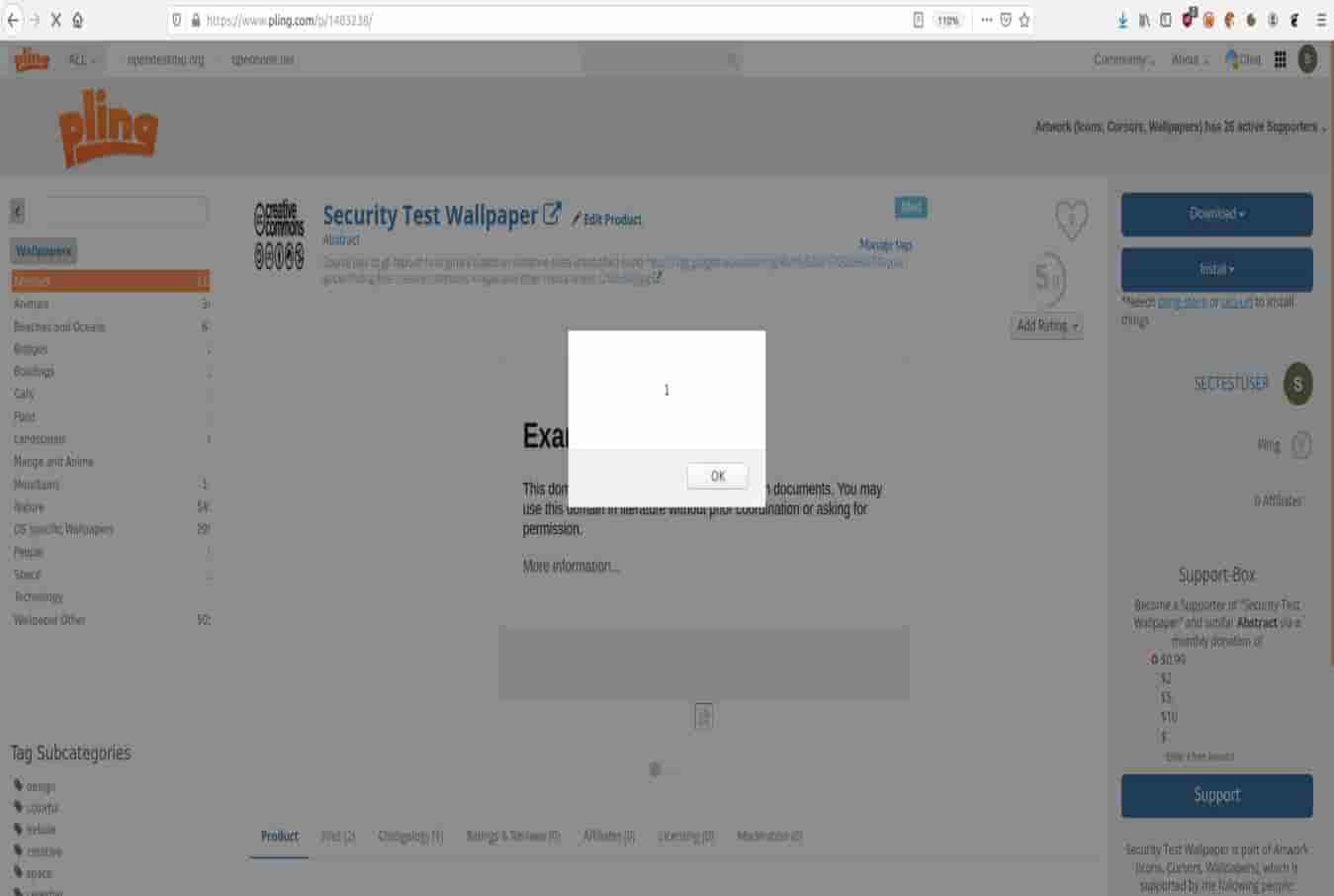 2.6KData Security
2.6KData SecurityUnpatched flaws exposing Linux marketplaces to remote attacks
Cybersecurity researchers at Berlin-based infosec company Positive Security have identified two serious zero-day vulnerabilities impacting Pling-based FOSS (free and open-source software) marketplaces...
-

 4.0KData Security
4.0KData SecurityProminent defibrillator management tool exposed to remote attacks
High-Risk Security Flaws Found and Patched in ZOLL Defibrillator Management Software. The Department of Homeland Security Cybersecurity and Infrastructure Security Agency (CISA)...






