Search results for "Remote"
-

 5.1KMalware
5.1KMalwareIranian Hackers Using SimpleHelp Remote Support Software for Persistent Access
The Iranian threat actor known as MuddyWater is continuing its time-tested tradition of relying on legitimate remote administration tools to commandeer targeted...
-
 868Data Security
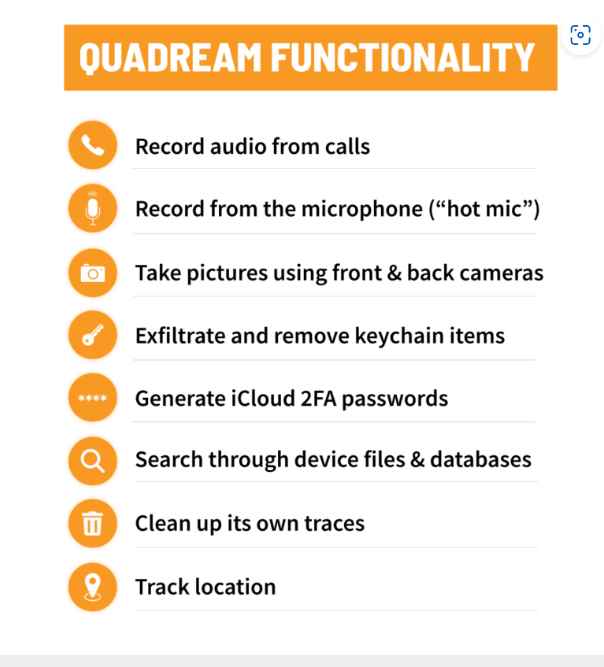
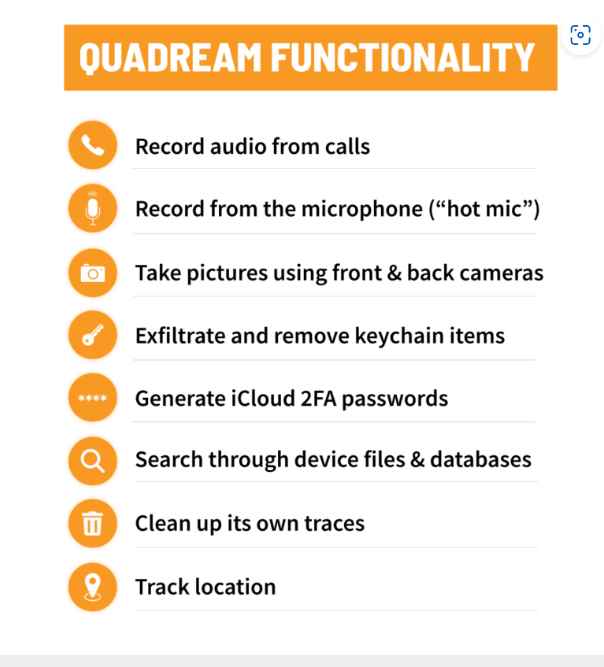
868Data SecurityNew spyware QuaDream is a replacement of Pegasus software used to hack iPhones remotely
Security researchers have uncovered fresh malware with hacking capabilities comparable to those of Pegasus, which was developed by NSO Group. The software,...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesResearchers Discover Critical Remote Code Execution Flaw in vm2 Sandbox Library
The maintainers of the vm2 JavaScript sandbox module have shipped a patch to address a critical flaw that could be abused to...
-
 226Data Security
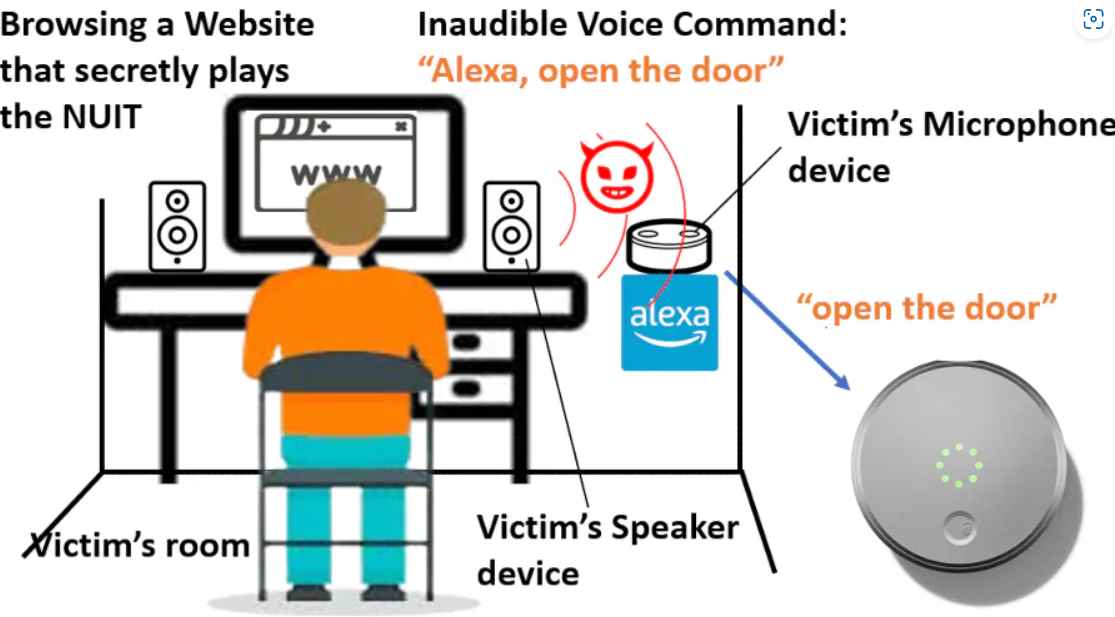
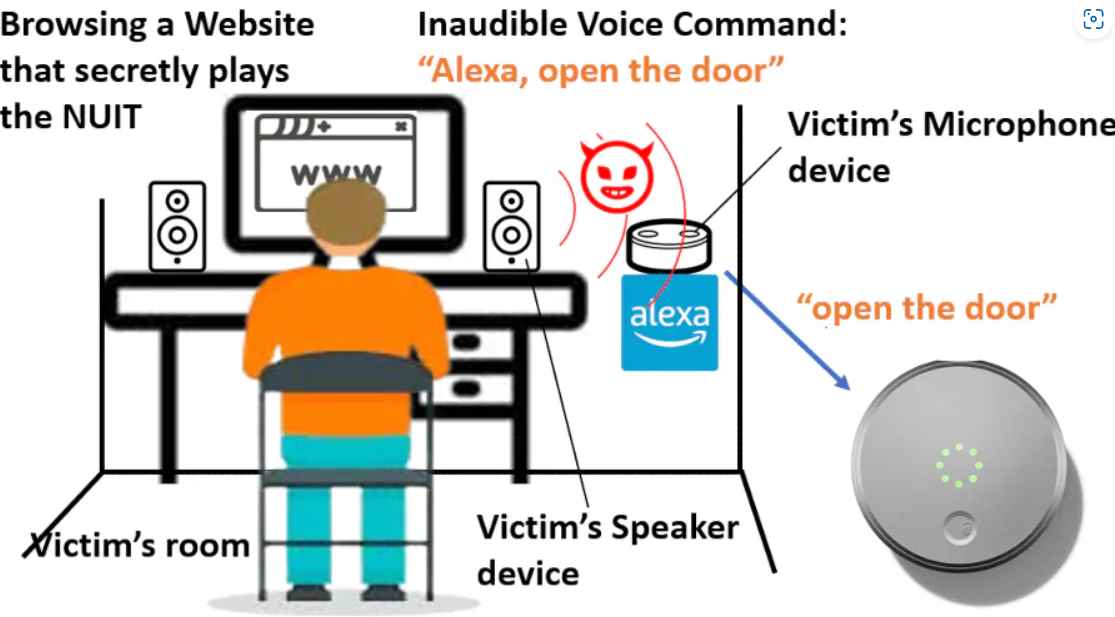
226Data SecurityHacking phones remotely without touching via new inaudible ultrasound attack
The Near-Ultrasound Invisible Trojan, or NUIT, was developed by a team of researchers from the University of Texas at San Antonio and...
-

 3.2KMalware
3.2KMalwareHackers Exploiting Remote Desktop Software Flaws to Deploy PlugX Malware
Security vulnerabilities in remote desktop programs such as Sunlogin and AweSun are being exploited by threat actors to deploy the PlugX malware....
-

 2.8KVulnerabilities
2.8KVulnerabilitiesNew Critical Flaw in FortiOS and FortiProxy Could Give Hackers Remote Access
Fortinet has released fixes to address 15 security flaws, including one critical vulnerability impacting FortiOS and FortiProxy that could enable a threat...
-

 2.8KMalware
2.8KMalware691 malicious npm packages and 49 PyPI components containing crypto-miners, remote access Trojans discovered
Security researchers have discovered yet another sizable haul of malicious packages on the open source registries npm and PyPI. These packages, which...
-

 3.6KData Security
3.6KData SecurityCentral Pro, Join.me, Hamachi, and RemotelyAnywhere services encrypted backups and keys hacked
GoTo, a company that provides software, said on Monday, January 23, that a hacker had stolen encrypted backups for its Central, Pro,...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesGit Users Urged to Update Software to Prevent Remote Code Execution Attacks
The maintainers of the Git source code version control system have released updates to remediate two critical vulnerabilities that could be exploited...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesHacking Nintendo Switch, 3DS, and Wii console. Vulnerability allows hacking remote console by simply engaging in an online gaming session with the victim
Nintendo has secretly released a fix for a security flaw that might have allowed hackers to access compromised Switch, 3DS, and Wii...
-
 1.6KVulnerabilities
1.6KVulnerabilitiesLinux Kernel has a Remote Code Execution Zero Day Vulnerability with CVSS score of 10
The use after free vulnerability, which is linked to ksmbd, affects computers running Linux distributions powered by kernels earlier than 5.15.61. This...
-
 2.4KVulnerabilities
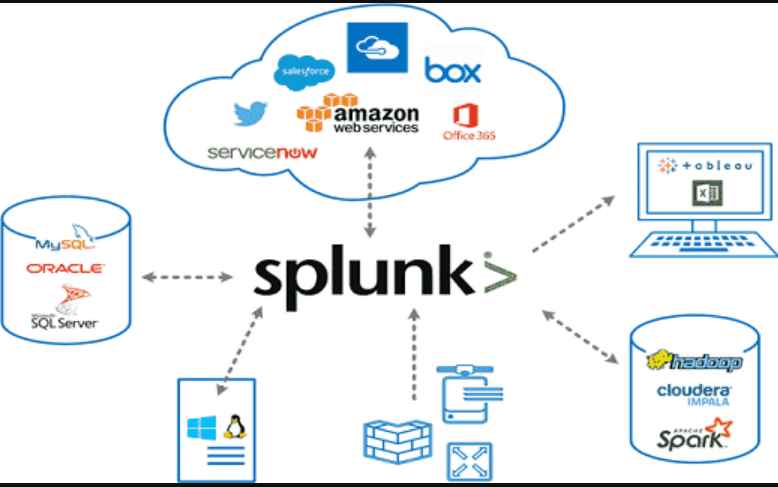
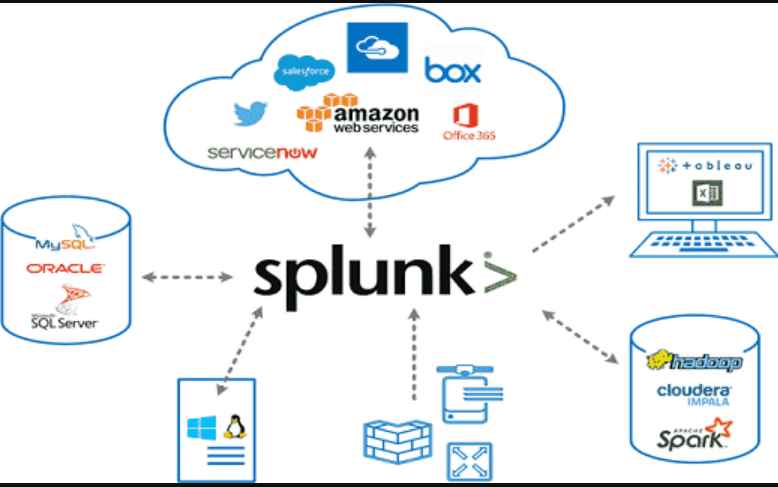
2.4KVulnerabilitiesExploit code for Splunk vulnerability published, allows remote code execution on the system
Splunk Inc. is a San Francisco, California-based American software firm that develops Web-based software for finding, monitoring, and analyzing machine-generated data. Splunk...
-
 4.3KData Security
4.3KData SecurityExploit code for remotely executing code on victim device exploiting Foxit PDF Reader Vulnerability
Researchers from HackSys Inc. have provided further information on a security issue in the code execution of Foxit PDF Reader. On vulnerable...
-

 463Vulnerabilities
463VulnerabilitiesCISA recommends to patch these two Veeam flaws that can be exploited by a remote attacker who is not authenticated to execute arbitrary code
On Tuesday, CISA updated its catalog with five new vulnerabilities, including those that affect products made by Veeam, Fortinet, Microsoft, and Citrix....
-

 3.8KVulnerabilities
3.8KVulnerabilitiesCisco IP Phones 7800 and 8800 series have a critical vulnerability could allow remote code execution or DoS attack
Customers were warned by Cisco on Thursday that fixes for a high-severity vulnerability that affects certain of the company’s IP phones are...
-

 5.1KVulnerabilities
5.1KVulnerabilitiesCVE-2022-23093 FreeBSD vulnerability allows remote execution of malware on devices including PlayStation, WhatsApp etc
A free operating system that is similar to Unix and Berkeley Unix is called FreeBSD. It is derived from Research Unix via...
-

 3.5KMalware
3.5KMalwareSiriusXM Vulnerability Lets Hackers Remotely Unlock and Start Connected Cars
Cybersecurity researchers have discovered a security vulnerability that exposes cars from Honda, Nissan, Infiniti, and Acura to remote attacks through a connected...
-
 3.5KVulnerabilities
3.5KVulnerabilitiesCritical Ping Vulnerability Allows Remote Attackers to Take Over FreeBSD Systems
The maintainers of the FreeBSD operating system have released updates to remediate a security vulnerability impacting the ping module that could be...
-
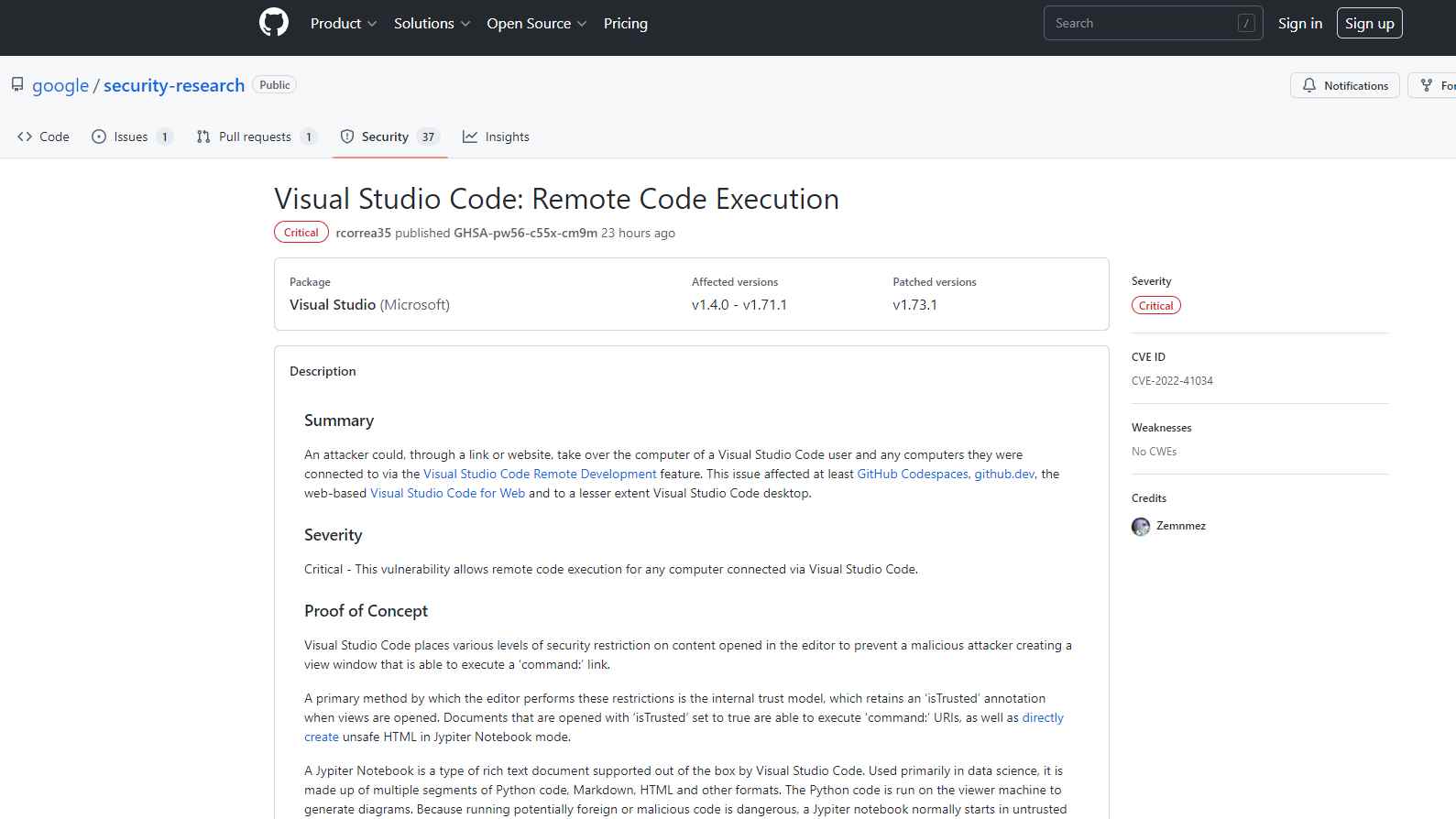
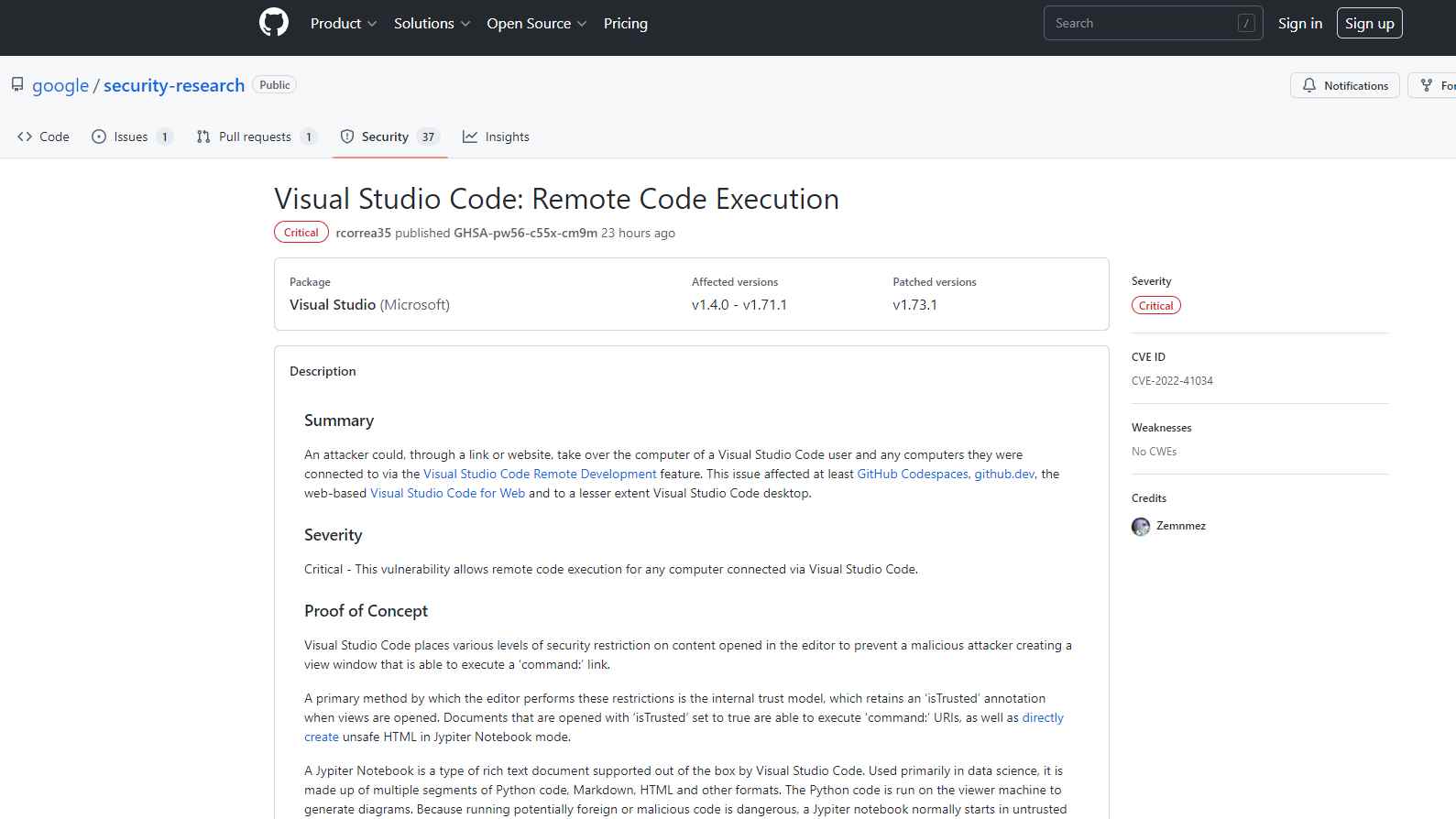 3.0KData Security
3.0KData SecurityExploit PoC for Remote code execution flaw in Visual Studio Code released
The remote code execution vulnerability that affected Visual Studio Code and was fixed by Microsoft in October was the subject of a...
-
 3.4KDDOS
3.4KDDOSMalicious Chrome Plugin Let Remote Attacker Steal keystroke and Inject Malicious Code
Researchers at Zimperium zLabs recently identified a new Chrome browser botnet called ‘Cloud9’ that is intent on stealing the following information using...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesVULNERABILITY IN GALAXY STORE ALLOWS ATTACKERS TO EXECUTE MALWARE REMOTELY ON SAMSUNG PHONES WITHOUT USER INTERACTION
A flaw in the Galaxy Store enables remote adversaries to trigger the installation and/or start of an application, resulting in the execution...






