Search results for "Stealth"
-
 3.4KMalware
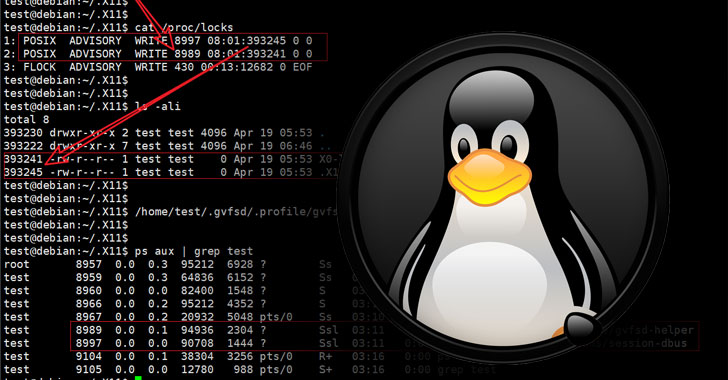
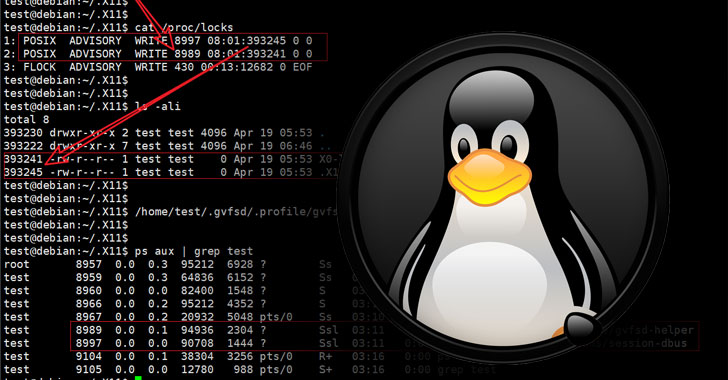
3.4KMalwareResearchers Uncover Stealthy Linux Malware That Went Undetected for 3 Years
A previously undocumented Linux malware with backdoor capabilities has managed to stay under the radar for about three years, allowing the threat...
-
 1.0KMalware
1.0KMalwareOperation StealthyTrident: corporate software under attack
LuckyMouse, TA428, HyperBro, Tmanger and ShadowPad linked in Mongolian supply-chain attack
-

 4.7KMalware
4.7KMalwareInsidious Android malware gives up all malicious features but one to gain stealth
ESET researchers detect a new way of misusing Accessibility Service, the Achilles’ heel of Android security
-

 1.8KNews
1.8KNewsNew Mac Malware Uses ‘Fileless’ Technique To Attack Stealthily
Notorious hacking group Lazarus which is also behind the widespread WannaCry ransomware is trying to infect Mac users with new malware that...
-
 3.5KData Breach
3.5KData Breach5 Places Where Hackers Are Stealthily Stealing Your Data In 2019
Skyrocketing data breaches bring incalculable losses to organizations and can cost cybersecurity executives their jobs. Here we examine the top five places...
-

 273Malware
273MalwareESET discovered an undocumented backdoor used by the infamous Stealth Falcon group
ESET researchers discovered a backdoor linked to malware used by the Stealth Falcon group, an operator of targeted spyware attacks against journalists,...
-
 266Firewall
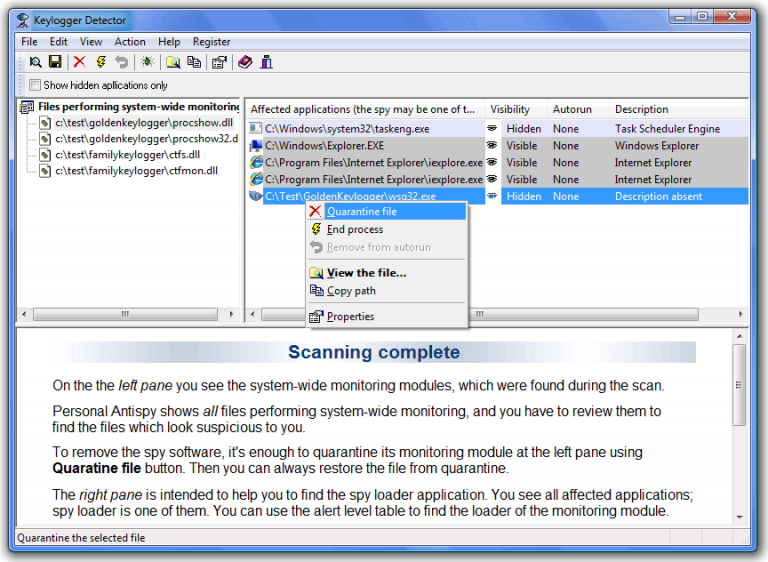
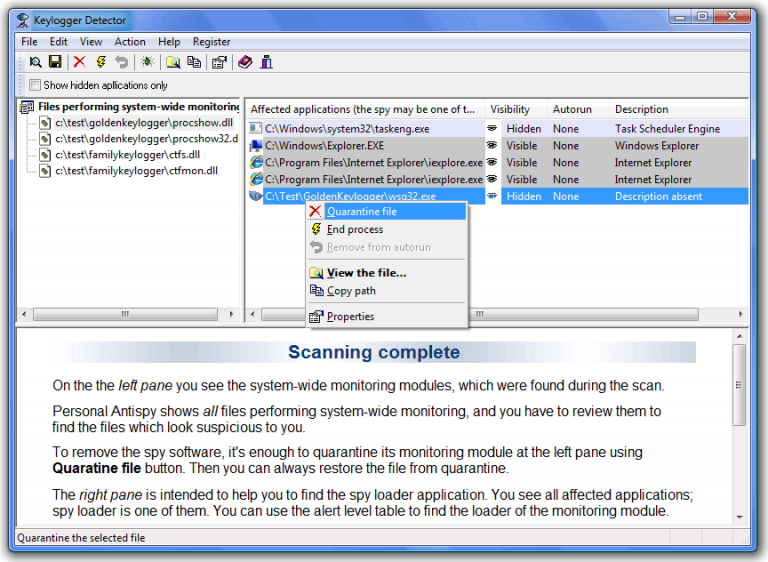
266FirewallKeylogger Detector – Detects Stealth Keyloggers
Keylogger Detector is an original solution, created to detect stealth monitoring software, both known and unknown. The intelligent algorithm of Keylogger Detector...
-
 270Malware
270MalwareStealthWorker Brute-force Malware Attack on Windows & Linux Platform Via Hacked E-commerce Websites
Researchers discovered a new brute-force malware called StealthWorker that attack Windows & Linux platform via compromised E-commerce websites to steals personal information...
-
 244News
244NewsResearchers Developed DeepLocker Artificial Intelligence- Powered Stealthy Malware
DeepLocker Artificial intelligence (AI) is seen as a potential solution to automatically detect malware and combat and stop cyber attacks before it...
-

 247Hacked
247HackedDeepLocker: Here’s How AI Could ‘Help’ Malware To Attack Stealthily
By this time, we have realized how artificial intelligence is a boon and a bane at the same time. Computers have become...
-
 291Bruteforcing
291BruteforcingCredCrack – A Fast and Stealthy Credential Harvester
CredCrack is a fast and stealthy credential harvester. It exfiltrates credentials recursively in memory and in the clear. Upon completion, CredCrack will...
-
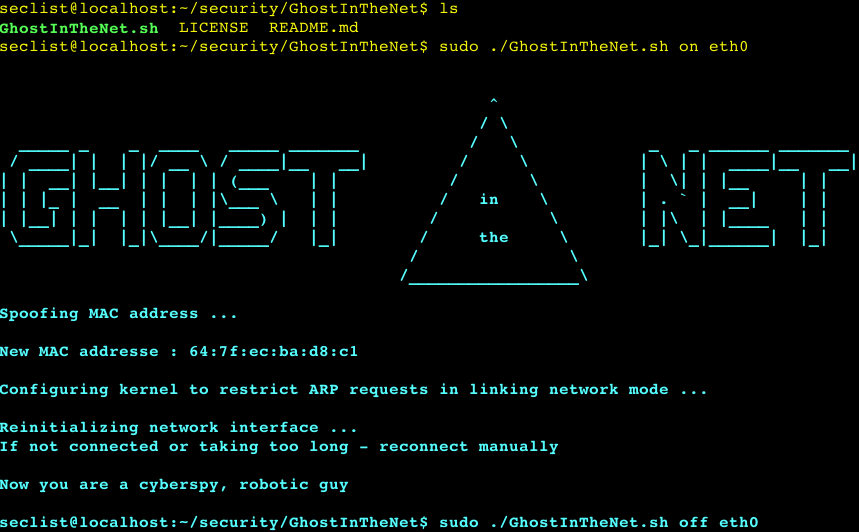
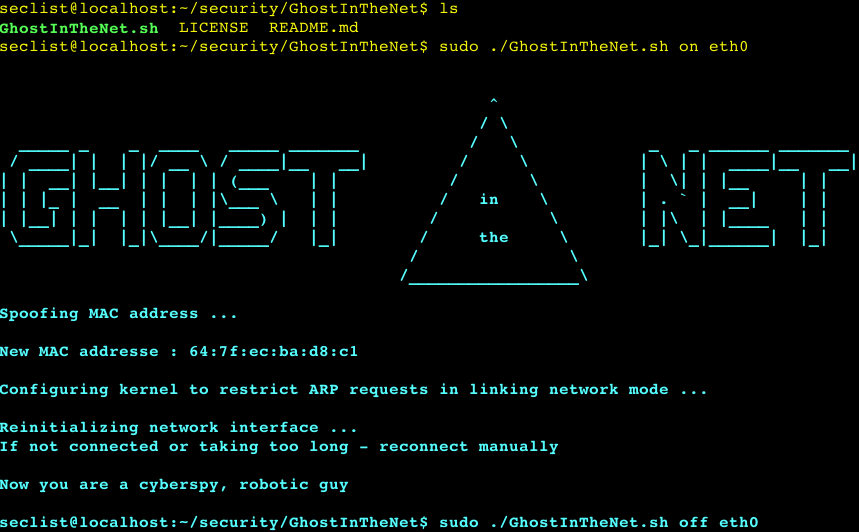 244Security Tools
244Security ToolsGhostInTheNet – Ultimate Network Stealther that makes Linux a Ghost In The Net and protects from MITM/DOS/scan
Ultimate Network Stealther that makes Linux a Ghost In The Net and protects from MITM/DOS/scan. Properties: Network Invisibility Network Anonymity Protects from...
-

 207Malware
207MalwareThis stealthy cat-and-mouse hacking campaign aims to steal diplomatic secrets
Felismus malware deployed to steal documents and carry out surveillance on government foreign policy in a previously unknown campaign. A previously unknown...
-

 323Hackers Repository
323Hackers RepositoryMorphAES – IDPS & SandBox & AntiVirus STEALTH KILLER
DPS & SandBox & AntiVirus STEALTH KILLER. MorphAES is the world’s first polymorphic shellcode engine, with metamorphic properties and capability to bypass...
-

 189Hack Tools
189Hack ToolsGhost In The Net – Network Stealther
Ultimate Network Stealther that makes Linux a Ghost In The Net and protects from MITM/DOS/scan How it works The basic and primary...
-
 171Malware
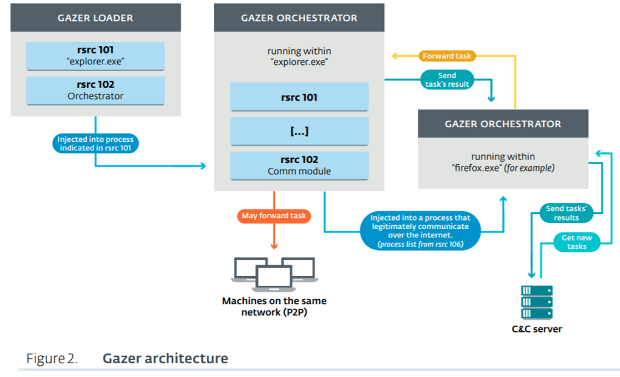
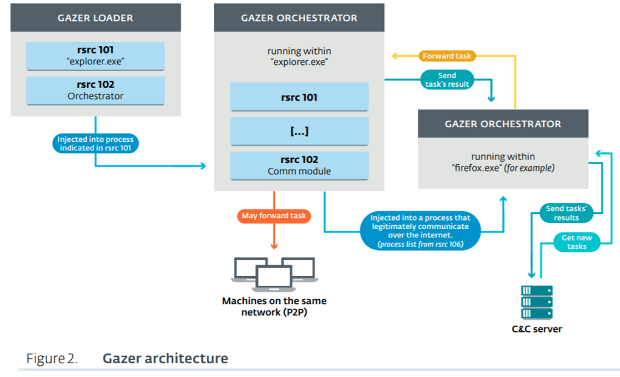
171MalwareNew ESET research uncovers Gazer, the stealthy backdoor that spies on embassies
Security researchers at ESET have released new research today into the activities of the notorious Turla cyberespionage group, and specifically a previously undocumented backdoor...
-

 274Data Security
274Data SecurityBug Lets Chrome Stealthily Record Audio and Video
Chrome might have a lurking bug that lets websites record your audio and video content without you even knowing. That is, Chrome...
-
 225Malware
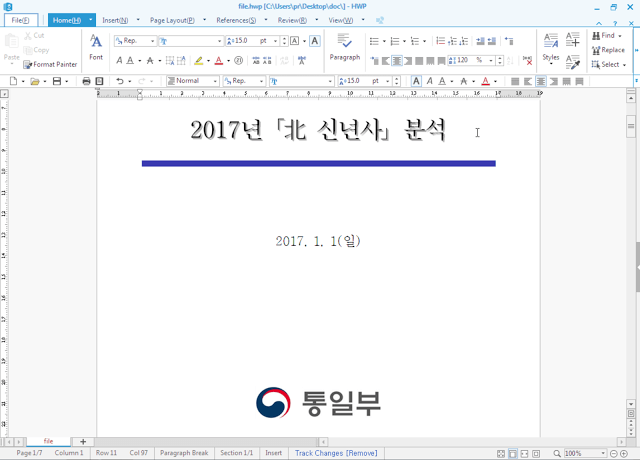
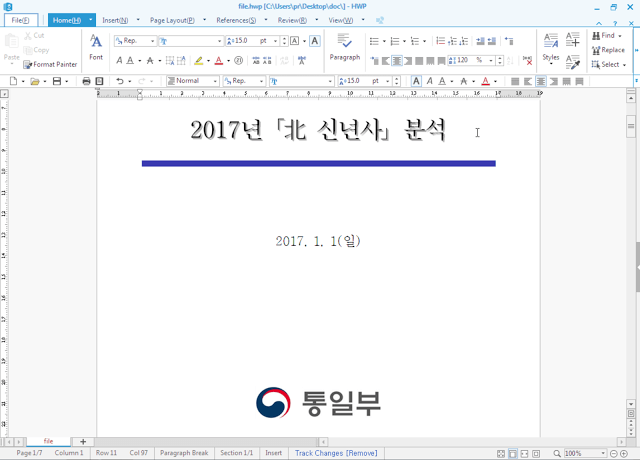
225MalwareSouth Korean users targeted with a new stealthy malware, the ROKRAT RAT
Security experts at CISCO Talos have spotted a new insidious remote access tool dubbed ROKRAT that implements sophisticated anti-detection measures. Security experts...
-

 189Vulnerabilities
189VulnerabilitiesRTM: Stealthy group targeting remote banking system
Today, we have released a white paper on RTM, a cybercrime group that has been relentlessly targeting businesses in Russia and neighboring...
-

 179Data Security
179Data SecurityReaders of popular websites targeted by stealthy Stegano exploit kit hiding in pixels of malicious ads
Millions of readers who visited popular news websites have been targeted by a series of malicious ads redirecting to an exploit kit...
-
 166Incidents
166IncidentsHow to compromise PLC systems via stealthy Pin control attacks
At the Black Hat Europe 2016 two security researchers devised undetectable attacks that could be used to hack PLC systems avoid being...






