Search results for "Stealth"
-

 252Incidents
252IncidentsStealth Cell Tower, how to spy on workers with a harmless printer
Stealth Cell Tower, it is an antagonistic GSM base station concealed in an office printer that could be used for surveillance purposes....
-
 235Evasion & Obfuscation
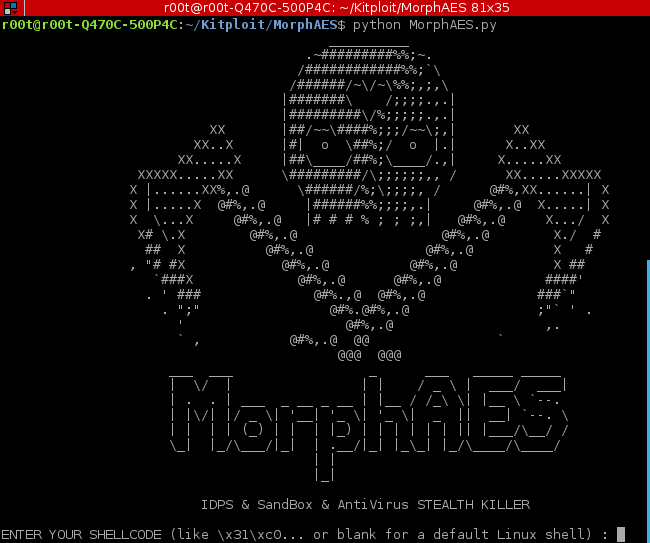
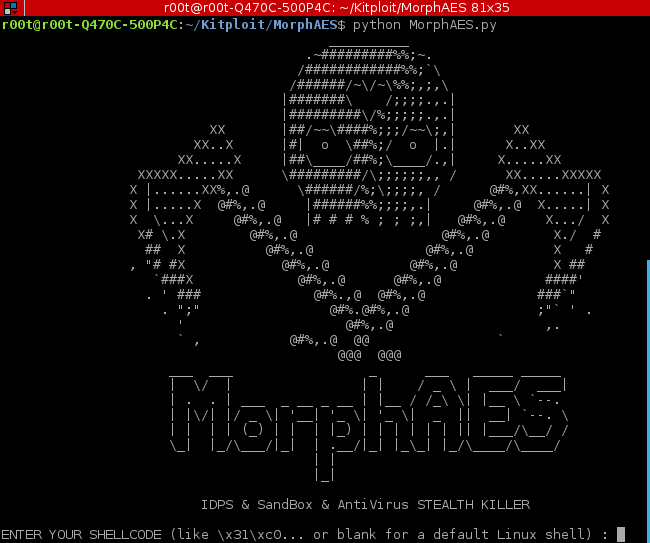
235Evasion & ObfuscationMorphAES – IDPS, SandBox & AntiVirus STEALTH KILLER
MorphAES is the world’s first polymorphic shellcode/malware engine, with metamorphic properties and capability to bypass sandboxes, which makes it undetectable for an...
-
 210Geek
210GeekLinux + Windows : Robolinux 8.5 LTS Arrives With Stealth VM For Running Windows
Short Bytes: Robolinux is a unique Linux distribution that comes with a stealth VM for deep Windows integration. The latest release of...
-
 286Hack Tools
286Hack ToolsGcat – A stealthy Backdoor that uses Gmail as the C&C server
A stealthy Python based backdoor that uses Gmail as a command and control server. Requirements A Gmail account (Use a dedicated account!...
-

 342Cyber Events
342Cyber EventsStealth Falcon Spyware Used by UAE to Intimidate Dissidents, Journalists
Reports show that UAE was spying on journalists and activists through spyware called Stealth Falcon There have been a lot of stories...
-
 218Data Security
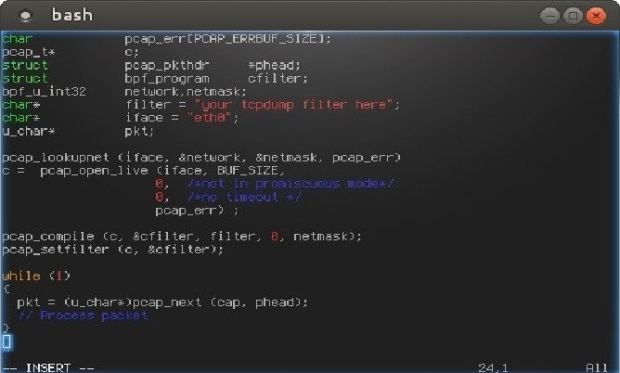
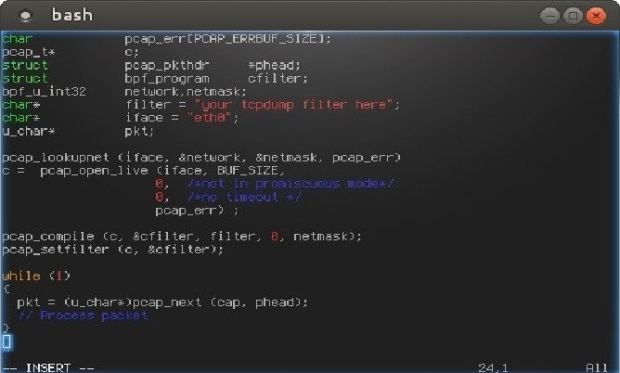
218Data SecurityHow to Build Stealth Backdoors
Today I’m going to tell you about a couple of techniques used to build stealth backdoors. Then, I will also show you...
-
 154Data Security
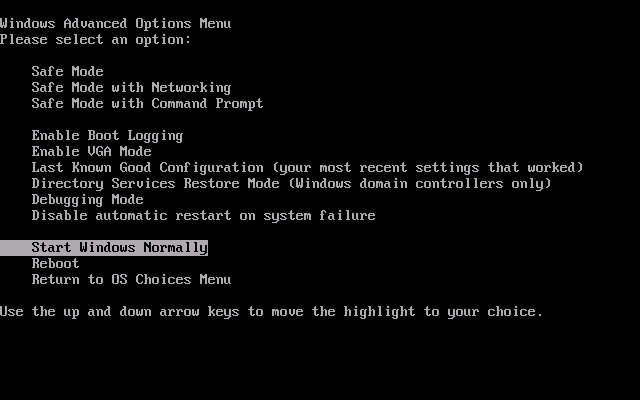
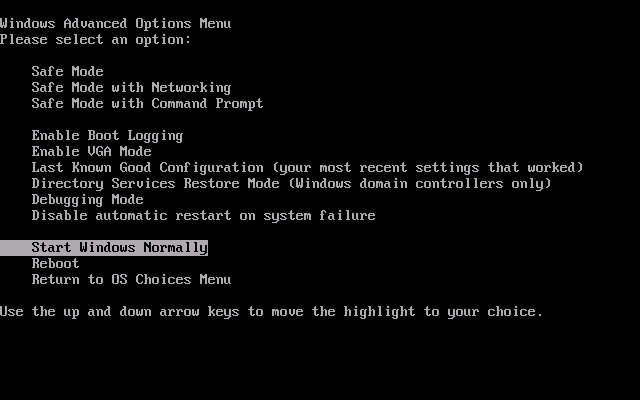
154Data Security“Nemesis” malware hijacks PC’s boot process to gain stealth, persistence
Bootkit targeting banks and payment card processors hard to detect and remove. Malware targeting banks, payment card processors, and other financial services...
-
 121Vulnerabilities
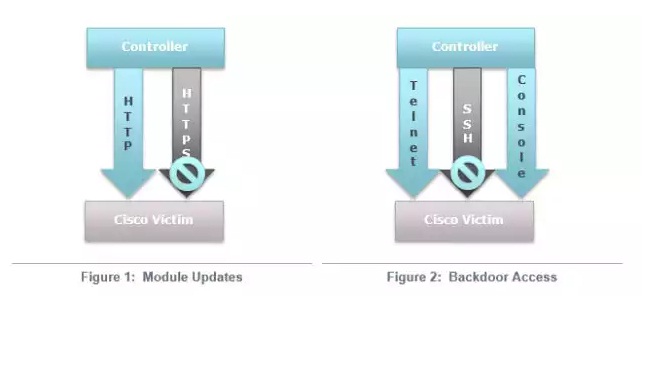
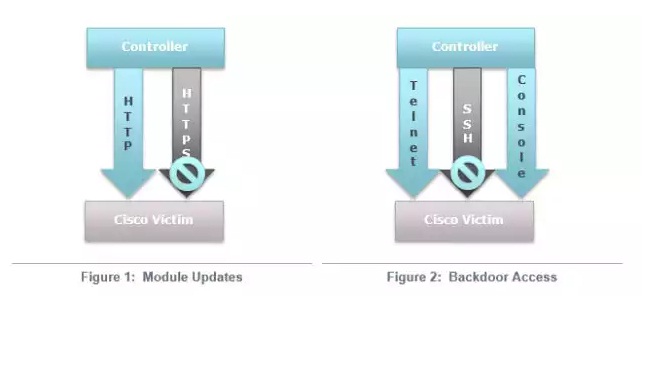
121VulnerabilitiesCisco routers in at least 4 countries infected by highly stealthy backdoor
More than a dozen routers in four countries infected with fully featured implants. Researchers have uncovered active and highly clandestine attacks that...
-

 90Malware
90MalwareStealthy malware uses Gmail drafts to steal data
A new strain of malware that uses Gmail drafts in an invisible Internet Explorer window, has been discovered. According to Network World,...
-

 70Cyber Crime
70Cyber CrimeStealthGenie CEO arrested for marketing ‘illegal stalking app’
The creator of an app that secretly allows you to monitor another person’s smartphone usage without their knowledge has been arrested in...
-

 175Malware
175MalwareInterview: Windigo victim speaks out on the ‘stealth’ malware that attacked his global company
Francois Gagnon is a Canadian business owner who was targeted because his company had lots of servers, and many customers - victims...
-
 205Android
205AndroidStealth malware sneaks onto Android phones, then “turns evil” when OS upgrades
A new form of Android malware could bypass one of the main warning systems built into Google’s smartphone and tablet OS -...
-

 103Malware
103MalwareThe stealthiness of Linux/Cdorked: a clarification
We clarify that the Linux/Cdorked backdoor malware leaves no traces on the hard drive "other than its modified httpd binary" which can...






