Search results for "Threat"
-
 341Viruses
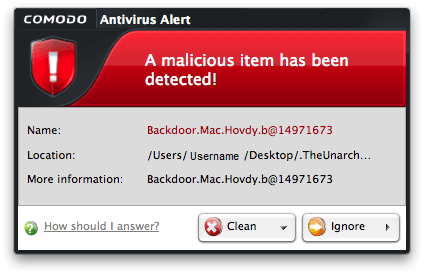
341VirusesGlobal Cyber Security Firm “Comodo Threat Research Labs” (CTRL) Detects New Family of Sophisticated Financial Malware
Comodo Threat Research Labs (CTRL) has announced that it has detected a new family of financial malware dubbed as “Gugi/Fanta/Lime”. It is...
-

 186Vulnerabilities
186VulnerabilitiesThreat actors leverage InPage Zero-Day in targeted attacks in Asia
Security researchers from Kaspersky Lab are warning of targeted attacks with InPage zero-day against a number of organizations in Asia. According to experts...
-

 256Hacked
256HackedChina Threatens To Destroy Apple And US Auto Sales, Donald Trump Is The Reason
Short Bytes: The heat waves have started to flow towards the US from the Chinese land. The credits should be given to...
-

 62Data Security
62Data SecurityAtomBombing, a new threat to your Windows
A few days ago Tal Liberman, a security researcher from the company enSilo revealed a new code injection technique that affects all...
-

 75Malware
75MalwareTrick or threat? How zombie IoT devices surprised the internet
It seems the current DDoS tactics from cybercriminals is to gain control over millions of IoT devices and direct their power towards...
-

 172Data Security
172Data SecurityNetflix Urging Subscribers to Change Passwords to Mitigate Possible Threat
Netflix is sending emails to its subscribers urging them to reset their passwords after discovering ”some” Netflix email addresses and passwords listed...
-

 171Data Security
171Data SecurityA New Linux Trojan Called NyaDrop Threatens the IoT Landscape
Malware author returns to IoT landscape following Mirai’s success and the wealth of vulnerable devices. The Krebs DDoS attacks have proven that the...
-

 223Data Security
223Data SecurityDNS traffic monitoring, a threat to Tor users’ anonymity
Tor Network Users May No Longer Enjoy Anonymity due to Exploitation of DNS Traffic Monitoring Karlstad University researchers in collaboration with KTH...
-
 115Incidents
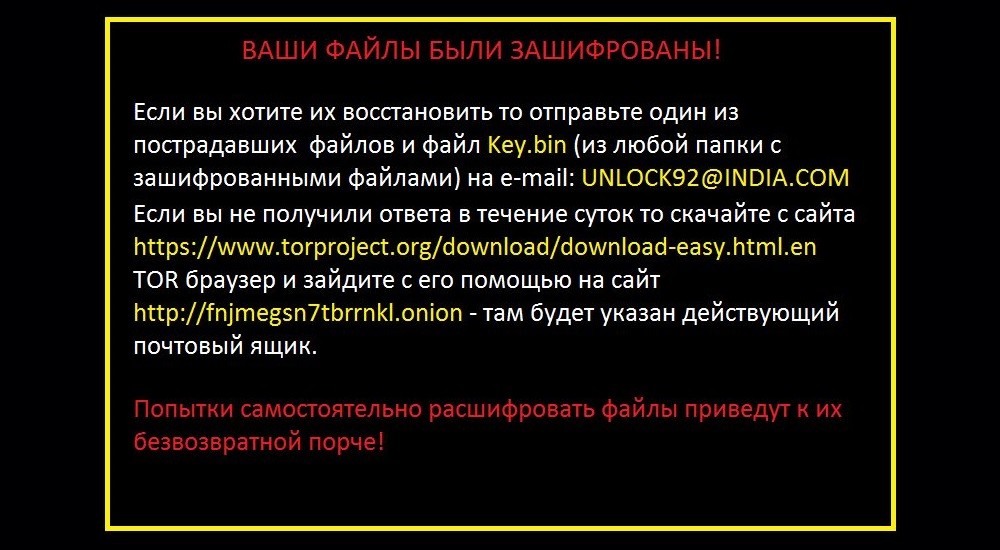
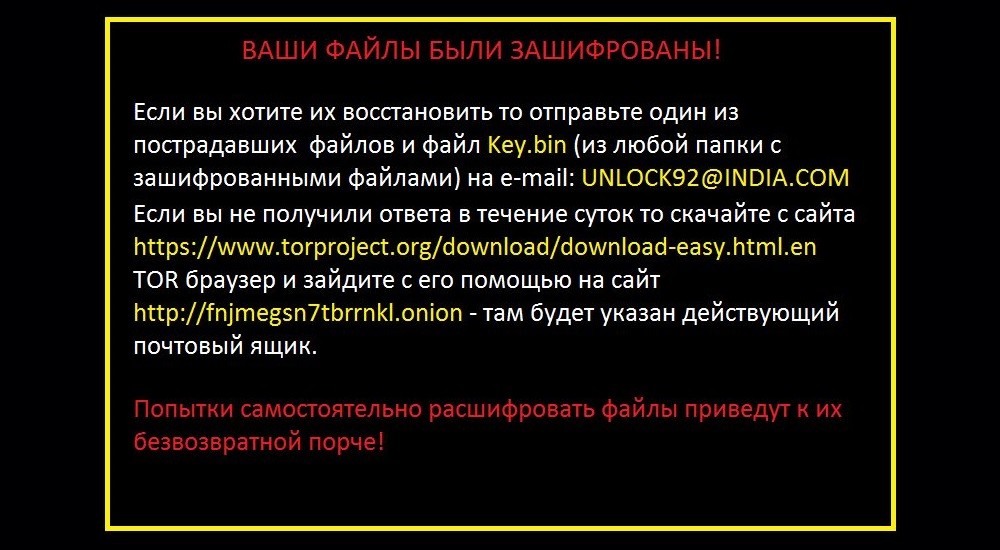
115IncidentsUnlock92 Ransomware Is the Quiet Threat That Nobody Heard About
Unlock92 infections going under the radar. A ransomware variant that appeared in early July this year and was initially cracked and decrypted...
-

 327Data Security
327Data SecurityUS Election 2016: 3 Privacy threats to voter data this campaign season
Today, politicians are tracking voters’ every move on social media, including Facebook “friends” and “likes,” YouTube views, LinkedIn activity, Pinterest pins and...
-

 117Vulnerabilities
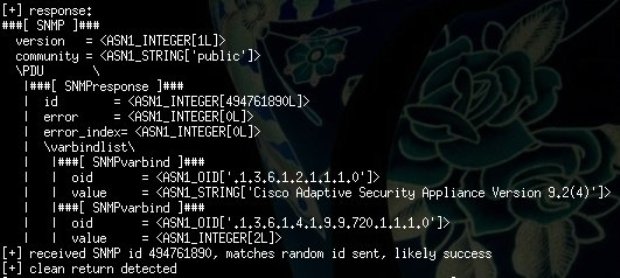
117VulnerabilitiesNSA EXTRABACON exploit still threatens tens of thousands of CISCO ASA boxes
Two security experts from the Rapid 7 firm revealed that tens of thousands of CISCO ASA boxes are still vulnerable to the...
-
 236Malware
236MalwareMirai DDoS Trojan Is the Next Big Threat for IoT Devices and Linux Servers
Mirai evolves from the source code of Gafgyt. A new trojan named Mirai has surfaced, and it’s targeting Linux servers and IoT devices,...
-

 1.2KHow To
1.2KHow ToTop 5 threats for online gamers and how to avoid them
This piece looks at the five threats online gamers face and what they can do to protect themselves. It's important to be...
-

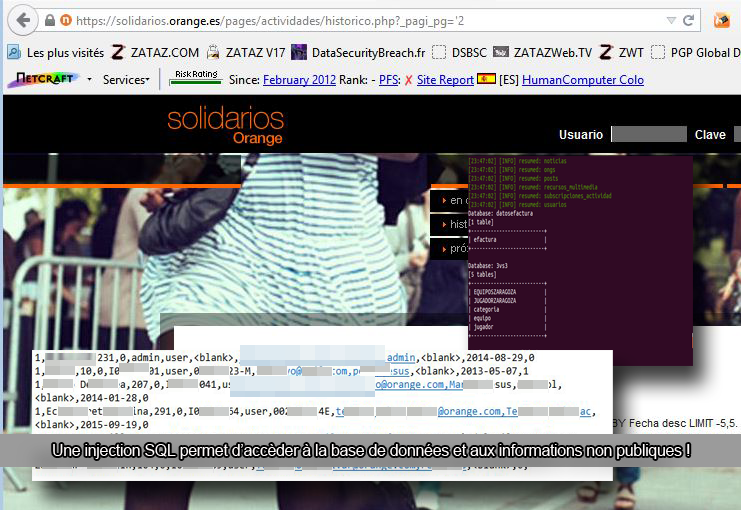
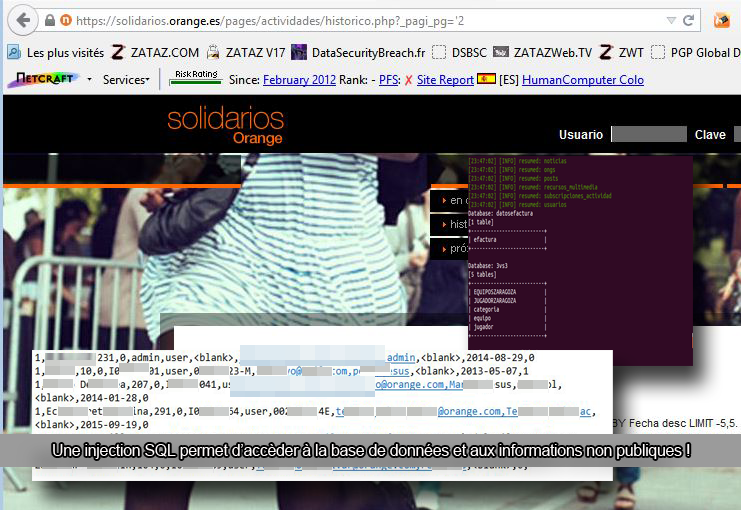
 95Cyber Crime
95Cyber Crime21st century cybercriminals: The threat landscape has evolved
21st century cybercriminals are more sophisticated, daring and organized than ever. The threat landscape has evolved.
-
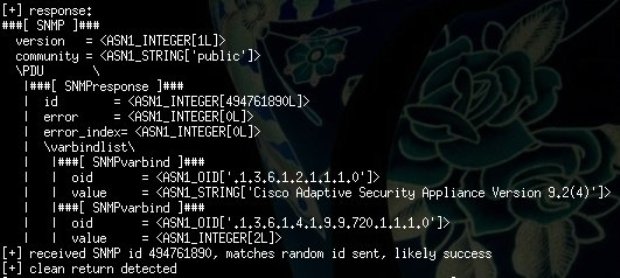 208Vulnerabilities
208VulnerabilitiesNSA-linked Cisco exploit poses bigger threat than previously thought
With only a small amount of work, ExtraBacon will commandeer new versions of ASA. Recently released code that exploits Cisco System firewalls and...
-
 255Data Security
255Data SecurityThreat intelligence report for the telecommunications industry
The telecommunications industry keeps the world connected. Telecoms providers build, operate and manage the complex network infrastructures used for voice and data...
-

 109Incidents
109IncidentsWith the looming threat of Ransomware, should companies stockpile Bitcoins?
With the threat of ransomware hanging over every company’s head, does it make sense for companies to stockpile a few bitcoins in the...
-
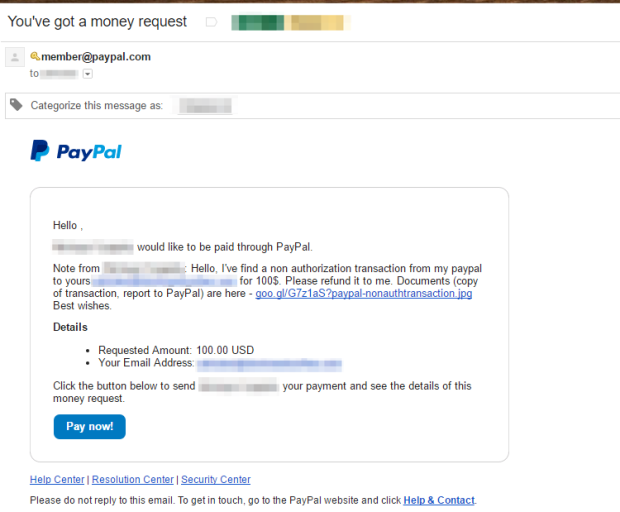
 212Incidents
212IncidentsThreat Actors Using Legitimate PayPal Accounts To Distribute Chthonic Banking Trojan
While many email providers, clients, and anti-spam engines have become adept at detecting spam, malicious messages sent via high-profile, legitimate providers are...
-

 188Malware
188MalwareAndroid Trojan Threatens 2.8 Million Users with Unwanted Ads
A new trojan potentially threatens as many as 2.8 million Android users with unwanted mobile advertisements. On 29 July, researchers at the...
-
 191News
191NewsDNC Emails from WikiLeaks Pose Massive Privacy Threat to Donors
WikiLeaks’ latest DNC email data dump is part one of organization’s new Hillary Leaks series — However, it also contains personal and financial...
-

 342Data Security
342Data SecurityHow to secure your cyber infrastructure from threats like ransomware?
The Internet is a great place to do business and cybercriminals are aware of that fact so how can you protect your networks,...