Search results for "Threat"
-
 89Cyber Crime
89Cyber CrimeESET Trends for 2016: Threats keep evolving as security becomes part of our lives
ESET's Trends for 2016: (In)Security Everywhere report includes a review of the most important events of last year and outlines trends in...
-

 286Cyber Events
286Cyber EventsCyber Attacks Threatening Oil and Gas Sector Severely Now Than Ever Before
It is being reported that the oil and gas sectors have suddenly become more vulnerable to cyber threats. In 2013, we at...
-

 186Incidents
186IncidentsHackers back down on threats to attack PlayStation and Xbox networks on Christmas Day
A repeat of last year’s gaming outage looks to have been avoided after hacker group Phantom Group claimed it won’t target Sony...
-
 295Data Security
295Data SecurityResearcher Threatened with Infection For Exposing Flaw in HIV Dating App
Websites and apps around the world encourage researchers to find bugs in their system, but an Internet dating app for HIV positive...
-

 270Cyber Crime
270Cyber CrimeScammers Threatening Users with Apple ID Suspension Phishing Scam
New day, new phishing attack! This time, it’s the Apple id which has been used by the attackers to steal from the...
-

 143Hacked
143HackedMedical Devices Ransomware Is The Biggest Hacking Threat of 2016
Short Bytes: As we are making progress on the front of online security, the cybercriminals are competing head-to-head to target every device connected...
-

 274Hacked
274HackedHow Belgians Trolled And Confused ISIS Terror Threats With Cat Pictures On Twitter
Short Bytes: Belgian people have found a new weapon to deal with the terror threats in the form of cat pics. As...
-
 193News
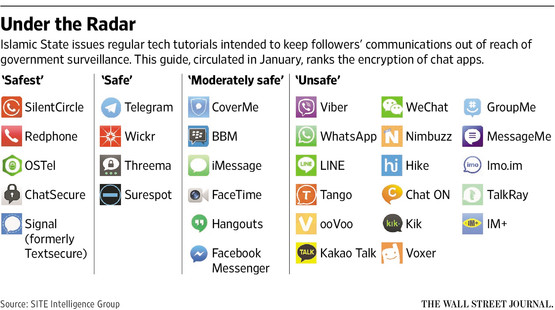
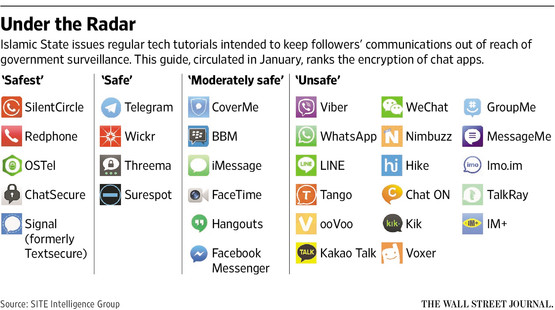
193NewsISIS issues anti-hacking guidelines for its online supports after Anonymous threats
After calling Anonymous ‘Idiots’ ISIS issues guidelines to its cronies to protect from hackers like Anonymous The Islamic State militant ISIL who...
-
 109Cyber Crime
109Cyber CrimeCourt Charges Kid with Bomb Threats and DDoS Attacks
A 15-year-old guy in Plymouth has been arrested by British police on the charges of launching DDoS attacks and for sending false bomb...
-

 549Banking
549BankingJean‑Ian Boutin: Banking trojan threat is not going anywhere
In an exclusive for We Live Security, Jean-Ian Boutin, a malware researcher at ESET, shares his thoughts on the past, present and...
-
 64Cyber Crime
64Cyber CrimeCybercrime ‘more threatening than ever’
Cybercrime is more aggressive and confrontational than it has ever been, Europol's latest Internet Organised Crime Threat Assessment (IOCTA) has stated.
-

 289Hacked
289HackedLaika BOSS: Lockheed Open Sources Secret Cyber Threat Detection Weapon
Short Bytes: Lockheed Martin has decided to open source its secret cyber threat detection tool Laika BOSS at the Black Hat Conference...
-

 109Opinion
109OpinionBlack Hat 2015 – Threats hit the road
This year at Black Hat, the focus was as much on hacking the intersections of data as on a specific computer platform.
-

 203News
203NewsKatie Hopkins Twitter Account Hacked, Threatens To Leak Sex Tape
Someone hacked the official Twitter account of UK based controversial Television personality, The Sun’s columnist Katie Hopkins and threatened to leak a sex...
-

 90Cyber Crime
90Cyber CrimeOnline threats only illegal if intentional, rules Supreme Court
The Supreme Court has reversed the decision to convict a Pennsylvania man who directed violent online threats at his ex-wife, citing intent...
-

 113Cyber Events
113Cyber EventsChina to beef up its cyber force to combat security threats
A military white paper said on Tuesday that China needs to take strong measures in order to speed up the development of...
-

 106Privacy
106PrivacyBluetooth fitness trackers ‘a threat to privacy’
Devices using Bluetooth Low Energy (BLE) to transmit their data can be intercepted by hackers, potentially exposing a trove of fitness data...
-

 448Malware
448MalwareAdvanced Persistent Threats: Using multi‑layered detection to defend against APTs
Advanced persistent threats (APTs) are a growing concern to the world's companies and networks. This recorded webinar looks at real-world data breaches...
-

 308Cyber Events
308Cyber EventsOp_Israel: Anonymous Threatens Israel with ‘Electronic Holocaust’
In a latest video footage from Anonymous, the notorious hacker group, a masked individual appears in a suit and delivers a well-structured...
-

 289Data Security
289Data SecurityHotel Wi-Fi Can Threaten Your Laptop with Malware
Following Kaspersky Labs’ identification of a unit issuing attacks on distinct high-end hotel guests in Asia and the US, ANTLabs, a technology...
-

 75Cyber Crime
75Cyber CrimeThreat sharing bill introduced to House of Representatives
The House of Representatives Intelligence Committee has introduced a new threat sharing bill designed to let businesses share details of security treats...






