Search results for "Threat"
-

 402Cyber Crime
402Cyber CrimeCyber‑threat to London 2012 Olympic opening ceremony revealed
The threat of cyber attack loomed over the opening ceremony for the London Olympics last year, officials have revealed.
-

 135Malware
135MalwareNeedles and haystacks – the art of threat attribution
ESET researchers explain the difficulties in attribution of targeted attacks; evidence is often circumstantial and the source never positively identified.
-

 281Data Security
281Data SecurityHuawei 3G and 4G USB Modems Vulnerable and a Security Threat
A Russian security researcher Nikita Tarakanov has found Huawei’s 3G and 4G devices vulnerable to the hackers. He has reported this matter...
-

 117Malware
117MalwareSinkholing of Trojan Downloader Zortob.B reveals fast growing malware threat
Malware infecting 25,000 computers, mostly in the United States, pumping out 80 million spam messages per hour? ESET researchers sinkhole to investigate...
-
 276Mac
276MacStraight facts about Mac malware, threats and responses
Does your Apple Mac need antivirus software, or any other kind of security software? This question has been asked repeatedly over the...
-

 98Cyber Crime
98Cyber CrimePentagon to boost cyber security force to combat increased global threat
The Washington Post reports that the Pentagon has approved a major expansion of its cyber security force which will result in a...
-

 341News
341NewsAnonymous Hacks Justice Department Website Threatens over Aaron Swartz’s Death
The Anonymous hackers have hacked and defaced the official website of U.S. Sentencing Commission (http://www.ussc.gov) working directly under the Justice Department for their operation #opLastResort. The...
-
 193Cyber Crime
193Cyber CrimeBotnet Threat: Over a Million Chinese Smartphones Infected with Trojan Horse Malware
In a shocking news reported by Chinese media, the security researchers have reveled that there are more than a million smartphones in...
-
 90Cyber Crime
90Cyber CrimeEuro security agency lists top ten cyber threats
The EU’s cyber security agency ENISA has published its Cyber Threat Landscape analysis of 2012 which puts drive-by-exploits as the top web...
-
 239Geek
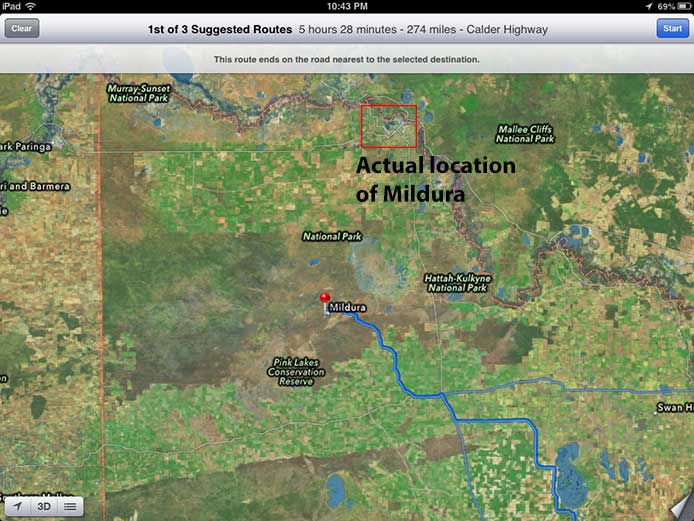
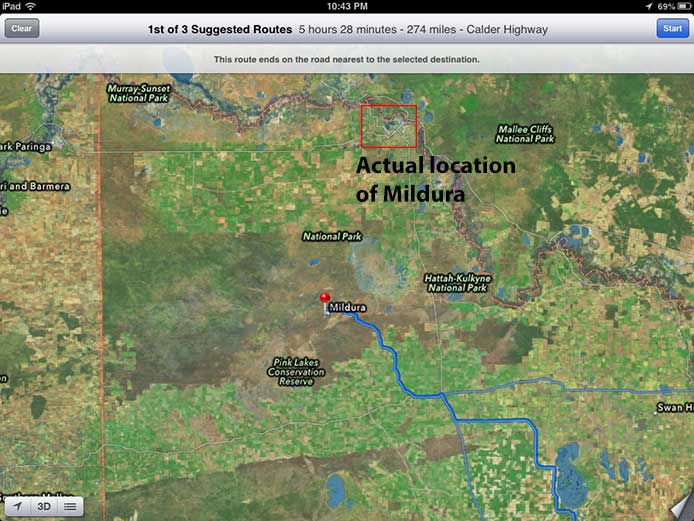
239GeekApple Updated Maps Found to be Life Threatening
Apple has been in news with concerns over it’s products since it’s iPhone 5 launch. But, those news aren’t the ones to...
-

 178Cyber Crime
178Cyber CrimePakistan On The Verge Of Serious Cyber Threat Yet No Rules
A country which is probably the 7th best amongst world’s top defense countries doesn’t have any legalized cyber crime laws in the...
-

 238News
238NewsIranian Group Hacks into Israel’s Military Database, Threatening Emails Sent to IDF Officials
A group of hackers who call themselves ”Islamic Jihad” has claimed to send thousands of emails in support of Gaza to 5000...
-
 185News
185NewsAnonymous Hackers to start #OpFuelStrike, threatens to attack International Oil Companies
Online hackavist group Anonymous has announced that they will now going one step further, this time the hackavist group will attack international...
-
 287News
287NewsAnonymous Threatens Turkey for Putting RedHack on the List of Terrorist Organizations
News.Softpedia came up with an interesting update on hackavist groups like Anonymous and RedHack, according to which Anonymous hackers have threatened Turkey for adding RedHack group on...
-
 251Cyber Crime
251Cyber CrimeAmerica’s infrastructure still exposed to cyber attacks despite recent threats
A common man when thinks about cyber terrorism or cyber crime, they think it may be just an illegal activity over some...
-

 132Malware
132MalwareChanging how people see the malware threat: images can make a difference
This is a just a short post to make available the security awareness slides that I was using at the RSA Conference...
-
Social Engineering
Boonana Threat Analysis
Our interim analysis of a version of the malware we detect as Java/Boonana.A or Win32/Boonana.A (depending on the particular component of this...
-
Scams
Social Media: 5 Unexpected Threats
...a piece at Discovery News about 5 Unexpected Threats of Online Social Networking...
-
Malware
Insider Threat: Malware on your ATM
Insider Threat – your ATM may now be hacked from the inside. According to Wired’s Threat Level Blog… A Bank of...
-
Cyber Crime
October Global Threat Report
As usual, ESET has released its monthly Global Threat Trends Report, which will be available in due course at http://www.eset.com/threat-center/index.php. There are...
-
Malware
September’s Global Threat Report
ESET released its Global Threat Report for the month of September, 2009, identifying the top ten threats seen during the month by...






