Search results for "hacking"
-

 3.6KData Security
3.6KData SecurityAre Mobile Payments Safe from Hacking
Over a third of online retail payments are now made using a mobile device. This method can be used to easily pay...
-
 200Malware
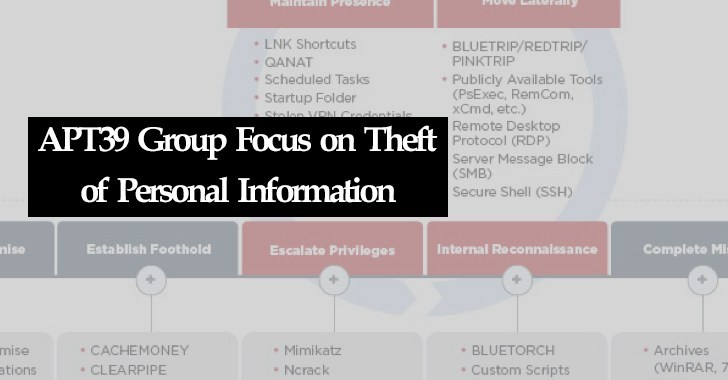
200MalwareAPT39 Hacking Group Launch Widespread Attack Focused on Personal Information
Iranian cyber espionage group APT39 focus on stealing on personal information o perform monitoring, tracking, or surveillance operations against specific individuals. The...
-
 256Hackers Repository
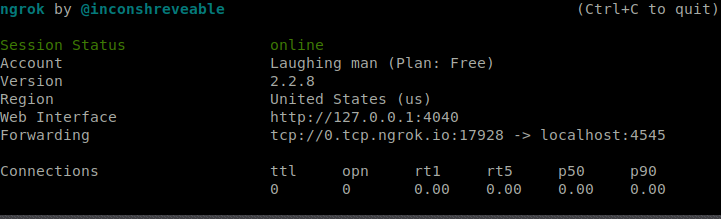
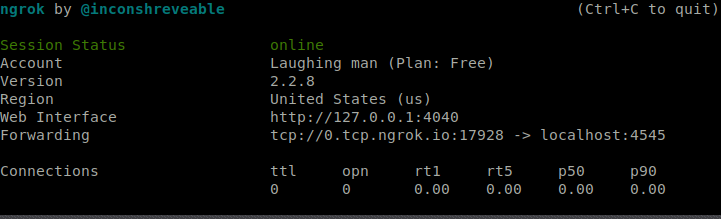
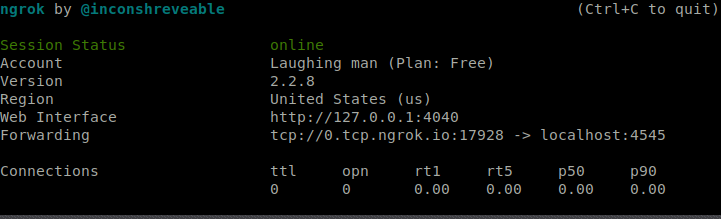
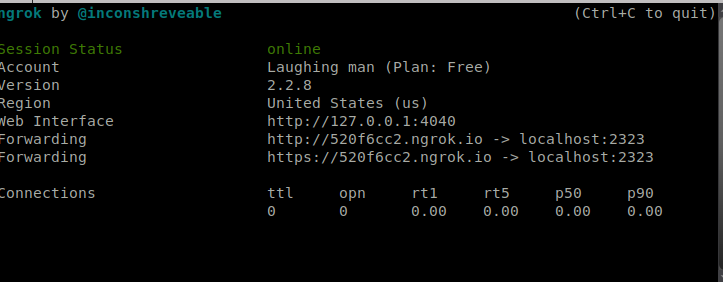
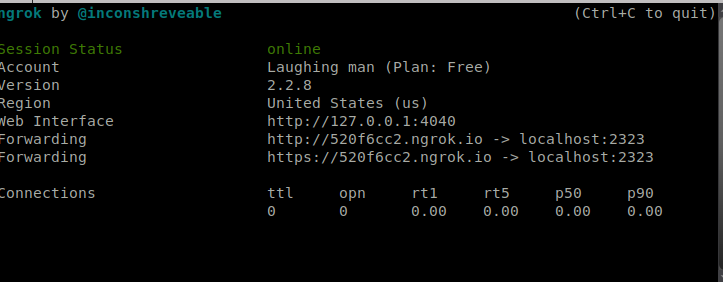
256Hackers RepositoryHacking with PHP payloads and ngrok – HackingVision
Hacking with PHP payloads and ngrok – HackingVision Welcome back to HackingVision. Today we will be hacking with PHP payloads, in this...
-
 252Hackers Repository
252Hackers RepositoryHacking with with php payloads and ngrok
Hey lads today were hacking with php we will be using msfvenom payload . lets start by downloading ngrok and installing it...
-
 421Hackers Repository
421Hackers RepositoryMsfvenom with ngrok Kali Linux Tutorial – HackingVision
How to use Msfvenom with ngrok Kali Linux Tutorial – HackingVision Hi welcome to Hacking Vision. Today lets get a little more...
-

 287Tutorials
287TutorialsJok3r, one tool to do all hacking
In most of the cases pentesting is done manually. Where pentester uses all the tools available over the internet to find bugs...
-

 2.1KCryptocurrency
2.1KCryptocurrencyCrypto Market Awaits More Hacking Attacks In The Coming Days
A couple of weeks back, the Coinbase security team noticed that someone had made a deep reorganization in the distributed ledger for...
-
 271Malware
271MalwareDarkHydrus Hacking Group Uses Macro-Enabled Excel Document that Delivers RogueRobin Malware
DarkHydruns APT Group targets government entities in the middle eats with weaponized excel documents that delivers a new variant of RogueRobin trojan...
-

 544Hacking
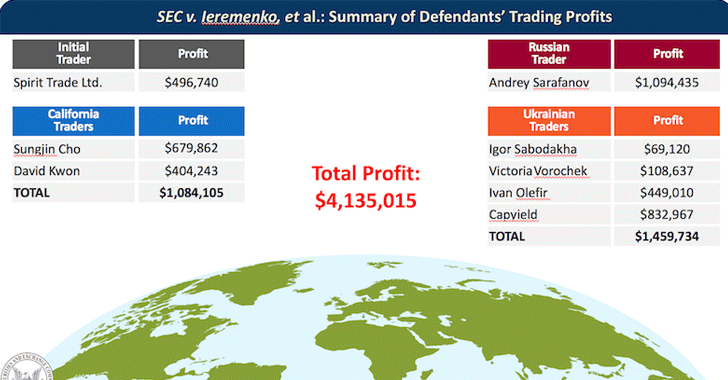
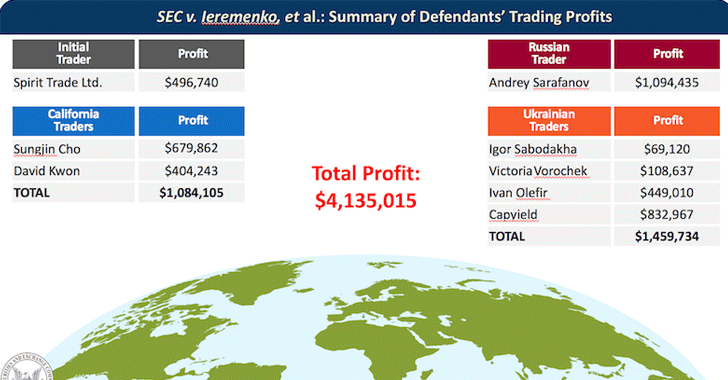
544HackingTwo men charged with hacking into SEC in stock‑trading scheme
The hacking duo is believed to have exploited a software flaw and compromised several SEC workstations with malware in order to take...
-
 307Tutorials
307TutorialsScan Github popular tools for hacking
Information gathering is a long process in pentesting. There are various tools which gather information from various social media platforms and many...
-
 171Articles
171ArticlesTwo Hackers Charged with Hacking SEC System in Stock-Trading Scheme
The U.S. authorities have charged two Ukrainian hackers for hacking into the Securities and Exchange Commission’s EDGAR filing system and stealing sensitive...
-
 251Data Security
251Data SecurityStart hacking with browser extension
Pentester always uses various tools to gather information of the target. And it is most crucial part before creating any further scenarios....
-

 331Tutorials
331TutorialsDo Hacking with Simple Python Script
Pentesting is all about showing and reporting problems in web/mobile applications. This is the most popular part of cyber security which every...
-
 241News
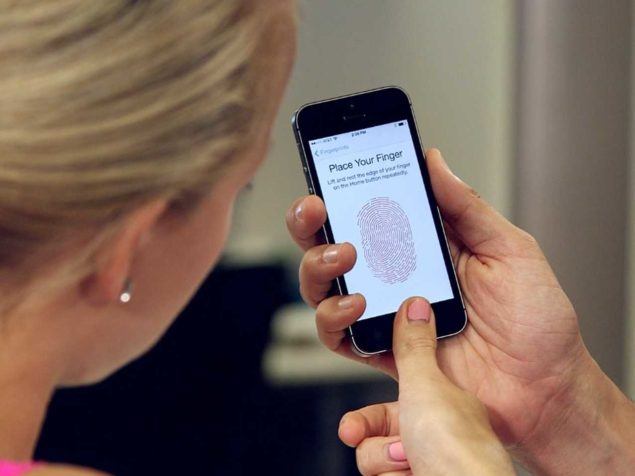
241NewsDeepMasterPrints Developed To Access Smartphones Via Hacking
Researchers at New York University and Michigan State University have invented new artificial fingerprints, which they call DeepMasterPrints for hacking fingerprint sensor-enabled...
-

 190Cyber Crime
190Cyber CrimeHackers steal Bitcoin worth $750,000 by hacking Electrum wallets
This year we have seen an unprecedented rise in malware attacks against cryptocurrency wallets whereas cryptomining incidents have increased by 4,000%, reports...
-
 181Articles
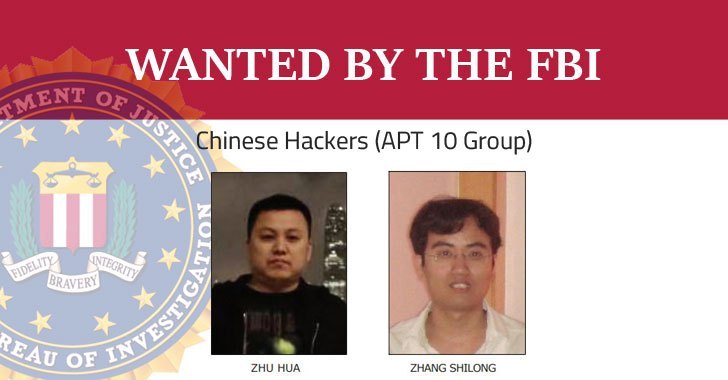
181ArticlesUS Indicts Two Chinese Government Hackers Over Global Hacking Campaign
The US Department of Justice on Thursday charged two Chinese hackers associated with the Chinese government for hacking numerous companies and government...
-
 327eBooks
327eBooksHacking for Dummies 6th Edition
Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to...
-
 363eBooks
363eBooksHacking Point of Sale
Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to...
-

 236Hackers Repository
236Hackers RepositoryAndroid hacking with sploitgen with no port forwarding
hi guys today im showing you how to hack a android using a tool we made sploitgen git clone https://github.com/Hackingvisionofficial/splotgen.git cd sploitgen...
-
 339eBooks
339eBooksHacking attacks and Examples Test
Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to...
-
 193eBooks
193eBooksHacking Basic Security, Penetration Testing and How to Hack
Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to...






