Search results for "hacking"
-

 343Password
343PasswordUSBStealer – Password Hacking Tool For Windows Applications to Perform Windows Penetration Testing
USBStealer is a Windows Based Password Hacker Tool that helps to Extract the password from Windows-Based Applications such as Chrome Password, FireFox...
-
 393Malware
393MalwareNew Variant of HawkEye Sold on Hacking Forums and Distributed via Excel and DOC Files
Threat actors advertised a new version of the information stealer malware kit HawkEye Reborn v9 that exfiltrates various information from the infected...
-

 272News
272NewsJulian Assange’s Hacking Charges, and Where It Go Wrong
Julian Assange’s lawyers want to see if hacking is protected by the First Amendment. London’s Metropolitan Police arrested Assange on Thursday at...
-

 338News
338NewsHacker Group Has Been Hacking DNS Traffic on D-Link Routers
Earlier, we had service provider playing tricks with your DNS traffic. Then, it was difficult for us to fathom unless you are...
-

 359Data Security
359Data SecurityBayer pharmaceutical company claims it was hacking targeted by Chinese groups
The German pharmaceutical company Bayer claims to have contained a cyberattack possibly carried out by Chinese hackers. According to the ethical hacking...
-

 254Hacking Tools
254Hacking ToolsCl0neMast3r – Install Your Hacking Tools With Ease
Cl0neMast3r is a Python script that was coded to make your life easier. It allows the user to choose their favorite tools from GitHub...
-

 2.3KSocial Media Hacking
2.3KSocial Media HackingShadowave: Hacking Facebook ID By Sending Link
Shadowave is a website that provides a “verified” phishing page to gain login details of the victim.Requirements PC or Mobile device with...
-

 447Automated Pentest
447Automated PentestCQTools: The New Ultimate Hacking Toolkit
On March 27 and 28, 2019, Paula presented Briefings and Arsenal sessions at Black Hat Asia 2019 in Singapore. CQURE Team has...
-
 403News
403NewsCommando VM Is A Windows-based Kali Alternative For Ethical Hacking
Fireye, a California-based public cybersecurity firm, launched a reverse engineering and malware analysis tool called FLARE VM in 2017. The tool allowed ethical...
-

 383Malware
383Malwareaka APT33 Hackers Attacked 50 Organizations by Launching a Variety of Malware & Free Hacking Tools
Relentless espionage Group also called as aka APT33 (Elfin) targeting various organization in Saudi Arabia and United States by deploying a variety...
-
 283Hackers Repository
283Hackers RepositoryKali Linux Micro Hacking Station Raspberry Pi
Kali Linux Micro Hacking Station Raspberry Pi Raspberry Pi is a small pocket sized low cost computer. Today we will be...
-

 395Incidents
395IncidentsHacking against IoT devices and cryptocurrency platforms in Japan increases 100%
The Japanese government claims that the vast majority of these attacks originated abroad According to network security and ethical hacking specialists from the International...
-
 380Malware
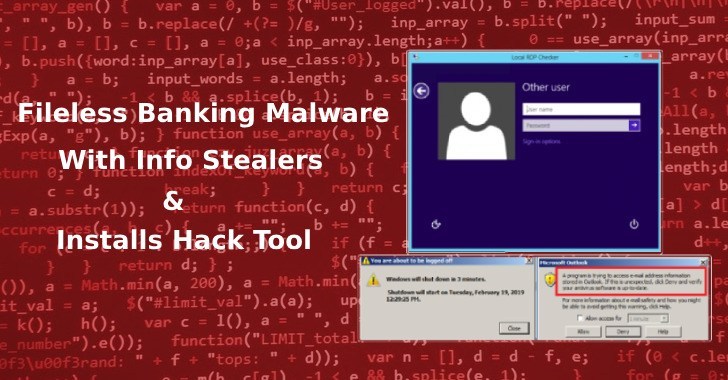
380MalwareFileless Banking Malware Steals User Credentials, Outlook Contacts, and Installs Hacking Tool
A new malware campaign focuses on stealing online banking credentials, to gather business email address and to gains remote access to the...
-

 530Hacked
530Hacked13 Best Hacking Tools Of 2019 For Windows, Linux, macOS
We have compiled a list of top hacking software and tools of 2019 with their best features and download links. This list...
-

 273Hackers Repository
273Hackers RepositoryGoogle Dorks List 2019 SQLi Dorks – HackingVision
Google Dorks List 2019 SQLi Dorks Google Dorks List 2019, Google Dorks List, Find SQL Injectable Websites, Hack Websites using Google Dorks,...
-
 390eBooks
390eBooks25 Free eBooks to learn Python 2019 – HackingVision
Free eBooks list of free Python programming eBooks to learn Python programming. Download eBooks in PDF EPUB 2019 Python eBooks. List curated...
-
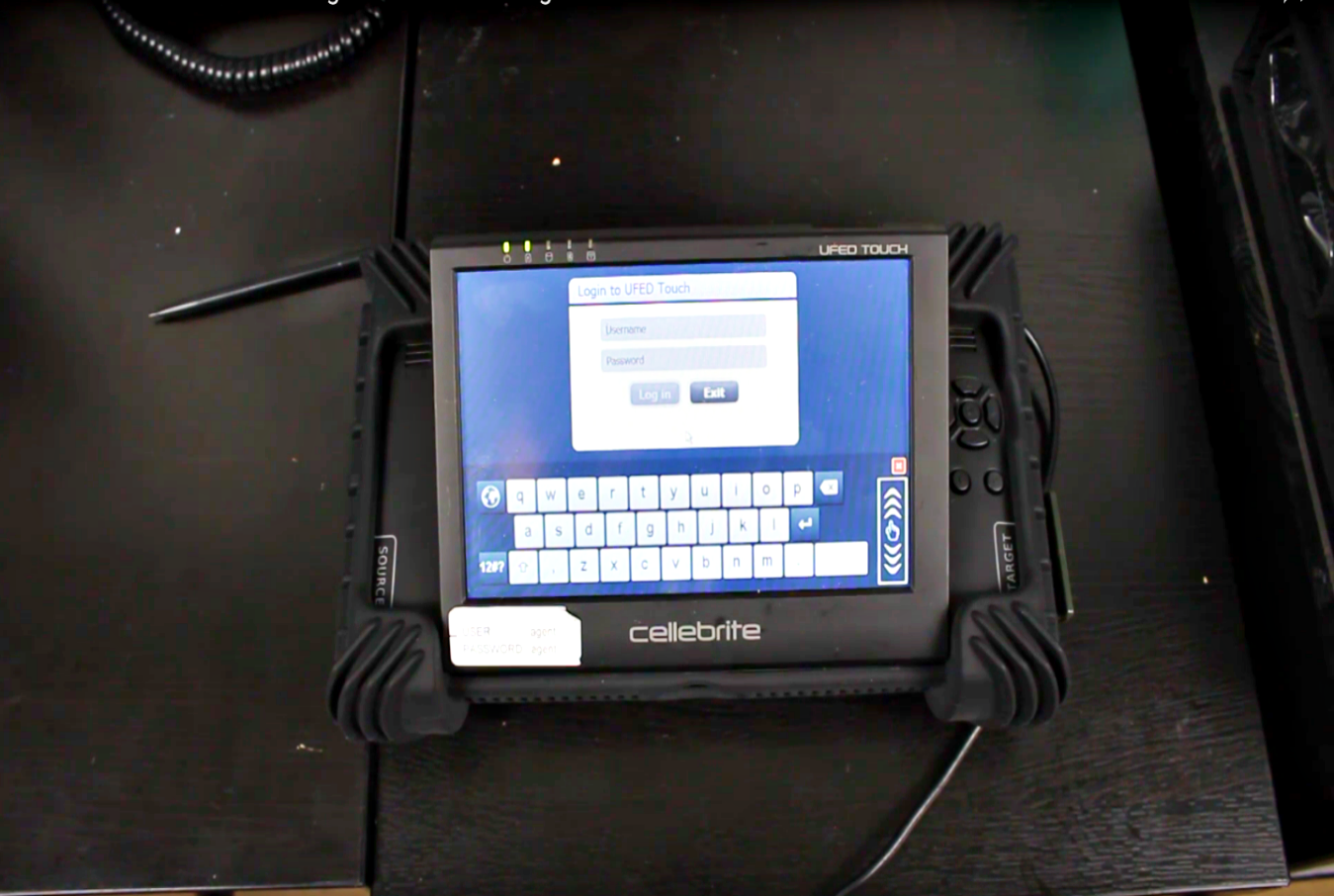
 290Data Security
290Data SecurityiPhone hacking tool Cellebrite being sold on eBay
Cellebrite UFED, an iPhone hacking tool made in Israel and widely used by the law enforcement authorities including the Federal Bureau of...
-

 209Articles
209ArticlesHacking Virtual Reality – Researchers Exploit Popular Bigscreen VR App
A team of cybersecurity researchers from the University of New Haven yesterday released a video demonstrating how vulnerabilities that most programmers often...
-

 324Cryptocurrency
324CryptocurrencyNew Hacking Tools launching Crypto-Malware by Exploit a Windows SMB Server Vulnerability
Cybercriminals now leveraging new hacking tools and remote access software to drop cryptocurrency malware by exploiting a Windows SMB Server Vulnerability . There are...
-

 186Data Security
186Data SecurityGovernment agencies, universities and political parties in Spain suffer hacking attack
A group of hackers claims to have compromised various public interest institutions in Spain The digitalization of administrative processes progresses little by...
-

 222Vulnerabilities
222VulnerabilitiesVulnerability allows hacking an Android smartphone using only a PNG image
Google claims that this vulnerability has not yet been exploited in the wild Ethical hacking and network security specialists from the International...






