All posts tagged "malware"
-
 4.0KMalware
4.0KMalwareNew Agent Tesla Malware Variant Using ZPAQ Compression in Email Attacks
A new variant of the Agent Tesla malware has been observed delivered via a lure file with the ZPAQ compression format to...
-

 3.1KMalware
3.1KMalwareMalicious Apps Disguised as Banks and Government Agencies Targeting Indian Android Users
Android smartphone users in India are the target of a new malware campaign that employs social engineering lures to install fraudulent apps...
-

 2.0KCyber Attack
2.0KCyber AttackMustang Panda Hackers Targets Philippines Government Amid South China Sea Tensions
The China-linked Mustang Panda actor has been linked to a cyber attack targeting a Philippines government entity amid rising tensions between the...
-
 3.0KMalware
3.0KMalwareNetSupport RAT Infections on the Rise – Targeting Government and Business Sectors
Threat actors are targeting the education, government and business services sectors with a remote access trojan called NetSupport RAT. “The delivery mechanisms...
-

 2.6KMalware
2.6KMalwareDarkGate and PikaBot Malware Resurrect QakBot’s Tactics in New Phishing Attacks
Phishing campaigns delivering malware families such as DarkGate and PikaBot are following the same tactics previously used in attacks leveraging the now-defunct...
-
 3.6KMalware
3.6KMalwareBeware: Malicious Google Ads Trick WinSCP Users into Installing Malware
Threat actors are leveraging manipulated search results and bogus Google ads that trick users who are looking to download legitimate software such...
-
 1.9KVulnerabilities
1.9KVulnerabilitiesNew PoC Exploit for Apache ActiveMQ Flaw Could Let Attackers Fly Under the Radar
Cybersecurity researchers have demonstrated a new technique that exploits a critical security flaw in Apache ActiveMQ to achieve arbitrary code execution in...
-

 1.4KCyber Attack
1.4KCyber AttackIran-Linked Imperial Kitten Cyber Group Targeting Middle East’s Tech Sectors
A group with links to Iran targeted transportation, logistics, and technology sectors in the Middle East, including Israel, in October 2023 amid...
-

 5.0KCyber Attack
5.0KCyber AttackStealthy Kamran Spyware Targeting Urdu-speaking Users in Gilgit-Baltistan
Urdu-speaking readers of a regional news website that caters to the Gilgit-Baltistan region have likely emerged as a target of a watering...
-

 4.7KCyber Attack
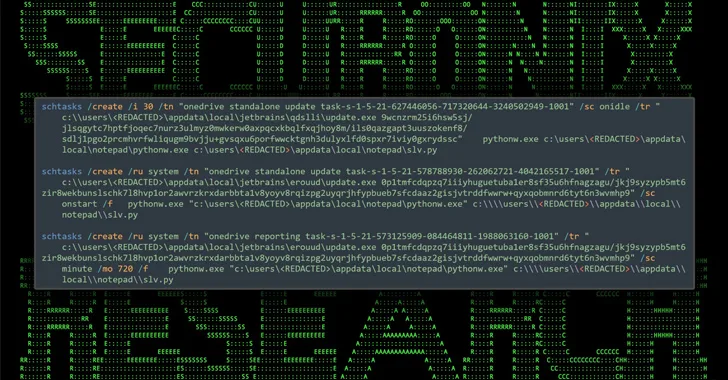
4.7KCyber AttackMuddyC2Go: New C2 Framework Iranian Hackers Using Against Israel
Iranian nation-state actors have been observed using a previously undocumented command-and-control (C2) framework called MuddyC2Go as part of attacks targeting Israel. “The...
-

 1.1KMalware
1.1KMalwareNew GootLoader Malware Variant Evades Detection and Spreads Rapidly
A new variant of the GootLoader malware called GootBot has been found to facilitate lateral movement on compromised systems and evade detection....
-

 2.7KVulnerabilities
2.7KVulnerabilitiesSideCopy Exploiting WinRAR Flaw in Attacks Targeting Indian Government Entities
The Pakistan-linked threat actor known as SideCopy has been observed leveraging the recent WinRAR security vulnerability in its attacks targeting Indian government...
-

 2.6KMalware
2.6KMalwareSecuriDropper: New Android Dropper-as-a-Service Bypasses Google’s Defenses
Cybersecurity researchers have shed light on a new dropper-as-a-service (DaaS) for Android called SecuriDropper that bypasses new security restrictions imposed by Google...
-

 4.5KMalware
4.5KMalwareGoogle Warns How Hackers Could Abuse Calendar Service as a Covert C2 Channel
Google is warning of multiple threat actors sharing a public proof-of-concept (PoC) exploit that leverages its Calendar service to host command-and-control (C2)...
-

 2.1KMalware
2.1KMalwareNodeStealer Malware Hijacking Facebook Business Accounts for Malicious Ads
Compromised Facebook business accounts are being used to run bogus ads that employ “revealing photos of young women” as lures to trick...
-
 4.5KMalware
4.5KMalwareResearchers Find 34 Windows Drivers Vulnerable to Full Device Takeover
As many as 34 unique vulnerable Windows Driver Model (WDM) and Windows Driver Frameworks (WDF) drivers could be exploited by non-privileged threat...
-

 4.2KMalware
4.2KMalwareNorth Korean Hackers Targeting Crypto Experts with KANDYKORN macOS Malware
State-sponsored threat actors from the Democratic People’s Republic of Korea (DPRK) have been found targeting blockchain engineers of an unnamed crypto exchange...
-

 2.1KMalware
2.1KMalwareTurla Updates Kazuar Backdoor with Advanced Anti-Analysis to Evade Detection
The Russia-linked hacking crew known as Turla has been observed using an updated version of a known second-stage backdoor referred to as...
-
 1.4KMalware
1.4KMalwareMalicious NuGet Packages Caught Distributing SeroXen RAT Malware
Cybersecurity researchers have uncovered a new set of malicious packages published to the NuGet package manager using a lesser-known method for malware...
-
 1.5KMalware
1.5KMalwarePro-Hamas Hacktivists Targeting Israeli Entities with Wiper Malware
A pro-Hamas hacktivist group has been observed using a new Linux-based wiper malware dubbed BiBi-Linux Wiper, targeting Israeli entities amidst the ongoing...
-

 960Malware
960MalwareN. Korean Lazarus Group Targets Software Vendor Using Known Flaws
The North Korea-aligned Lazarus Group has been attributed as behind a new campaign in which an unnamed software vendor was compromised through...






