All posts tagged "malware"
-
 4.9KMalware
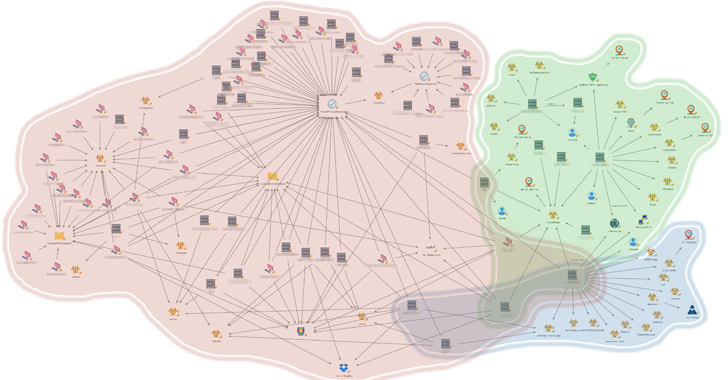
4.9KMalwareNew Report Uncovers 3 Distinct Clusters of China-Nexus Attacks on Southeast Asian Government
An unnamed Southeast Asian government has been targeted by multiple China-nexus threat actors as part of espionage campaigns targeting the region over...
-
 1.4KMalware
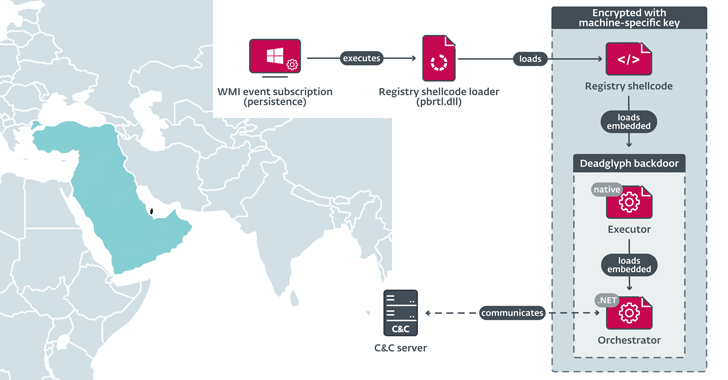
1.4KMalwareDeadglyph: New Advanced Backdoor with Distinctive Malware Tactics
Cybersecurity researchers have discovered a previously undocumented advanced backdoor dubbed Deadglyph employed by a threat actor known as Stealth Falcon as part...
-
 1.7KVulnerabilities
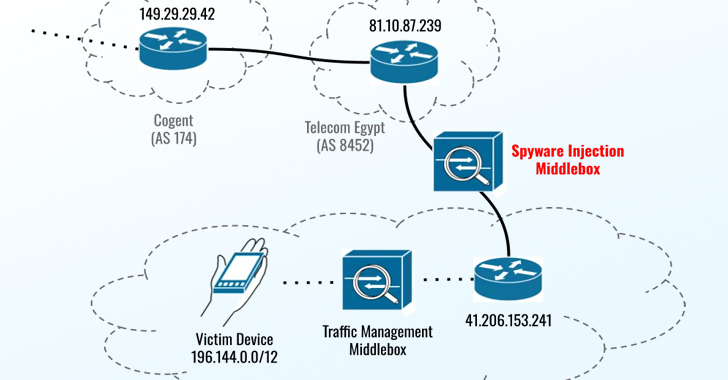
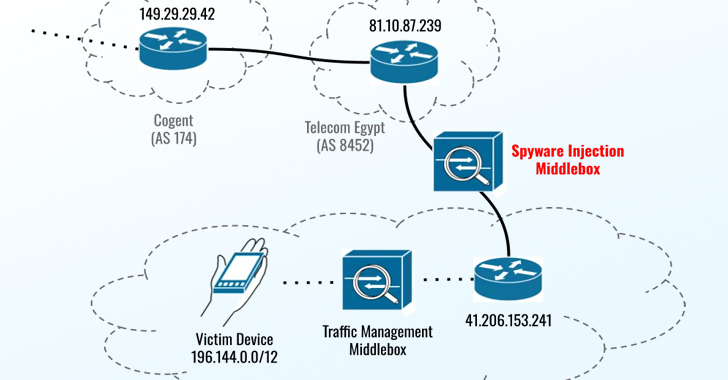
1.7KVulnerabilitiesNew Apple Zero-Days Exploited to Target Egyptian ex-MP with Predator Spyware
The three zero-day flaws addressed by Apple on September 21, 2023, were leveraged as part of an iPhone exploit chain in an...
-
 958Malware
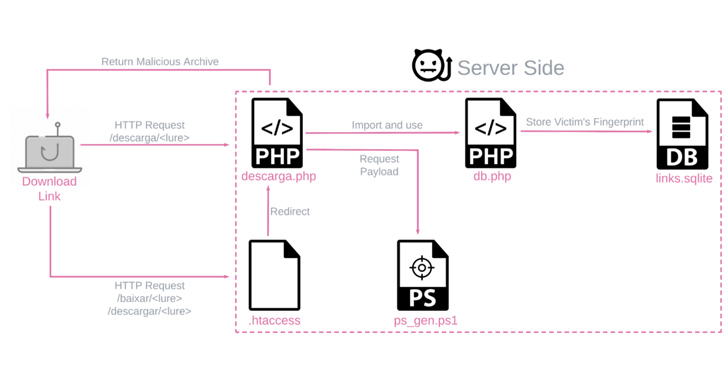
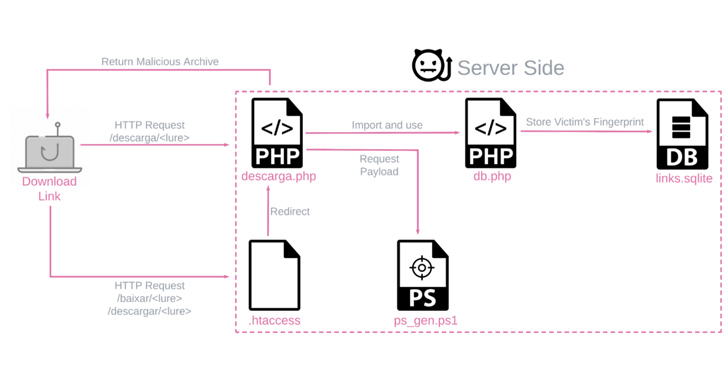
958MalwareNew Variant of Banking Trojan BBTok Targets Over 40 Latin American Banks
An active malware campaign targeting Latin America is dispensing a new variant of a banking trojan called BBTok, particularly users in Brazil...
-
 2.0KCyber Attack
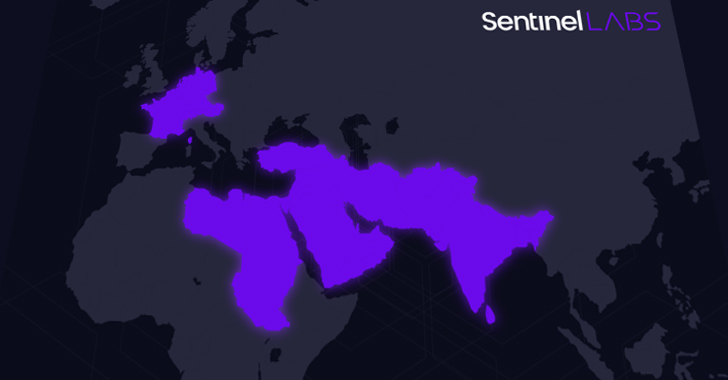
2.0KCyber AttackMysterious ‘Sandman’ Threat Actor Targets Telecom Providers Across Three Continents
A previously undocumented threat actor dubbed Sandman has been attributed to a set of cyber attacks targeting telecommunic koation providers in the...
-
Malware
The Rise of the Malicious App
Security teams are familiar with threats emanating from third-party applications that employees add to improve their productivity. These apps are inherently designed...
-

 302Malware
302MalwareChina Accuses U.S. of Decade-Long Cyber Espionage Campaign Against Huawei Servers
China’s Ministry of State Security (MSS) has accused the U.S. of breaking into Huawei’s servers, stealing critical data, and implanting backdoors since...
-
 5.0KMalware
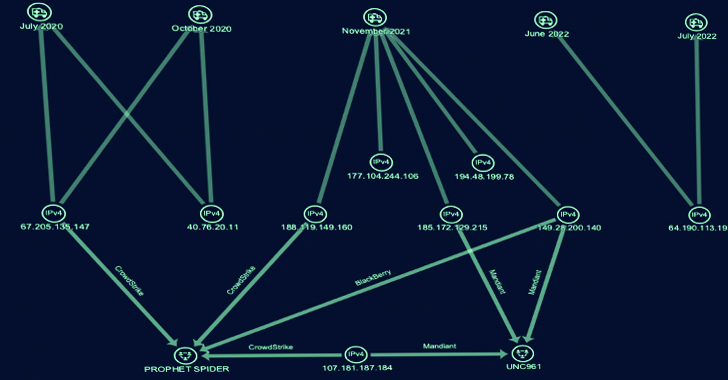
5.0KMalwareCyber Group ‘Gold Melody’ Selling Compromised Access to Ransomware Attackers
A financially motivated threat actor has been outed as an initial access broker (IAB) that sells access to compromised organizations for other...
-
 243Malware
243MalwareUkrainian Hacker Suspected to be Behind “Free Download Manager” Malware Attack
The maintainers of Free Download Manager (FDM) have acknowledged a security incident dating back to 2020 that led to its website being...
-
Malware
Sophisticated Phishing Campaign Targeting Chinese Users with ValleyRAT and Gh0st RAT
Chinese-language speakers have been increasingly targeted as part of multiple email phishing campaigns that aim to distribute various malware families such as...
-
Malware
Operation Rusty Flag: Azerbaijan Targeted in New Rust-Based Malware Campaign
Targets located in Azerbaijan have been singled out as part of a new campaign that’s designed to deploy Rust-based malware on compromised...
-
 1.1KMalware
1.1KMalwareEarth Lusca’s New SprySOCKS Linux Backdoor Targets Government Entities
The China-linked threat actor known as Earth Lusca has been observed targeting government entities using a never-before-seen Linux backdoor called SprySOCKS. Earth...
-
Malware
Transparent Tribe Uses Fake YouTube Android Apps to Spread CapraRAT Malware
The suspected Pakistan-linked threat actor known as Transparent Tribe is using malicious Android apps mimicking YouTube to distribute the CapraRAT mobile remote...
-
 817Malware
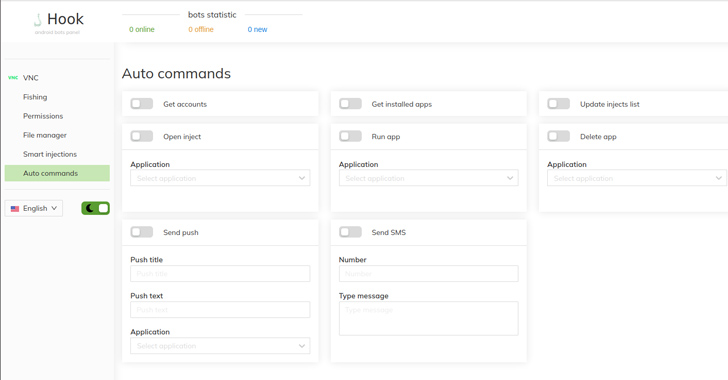
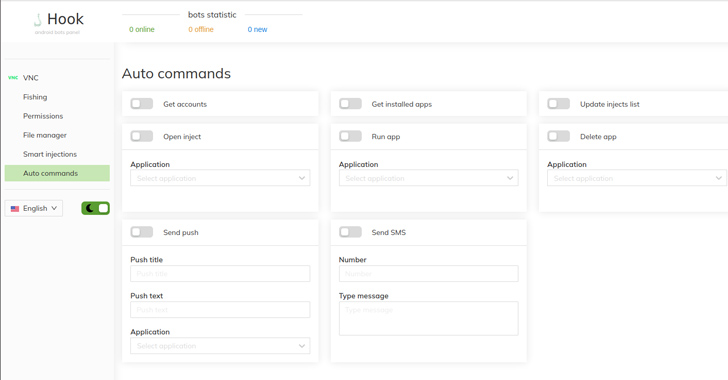
817MalwareHook: New Android Banking Trojan That Expands on ERMAC’s Legacy
A new analysis of the Android banking trojan known as Hook has revealed that it’s based on its predecessor called ERMAC. “The...
-
 2.0KMalware
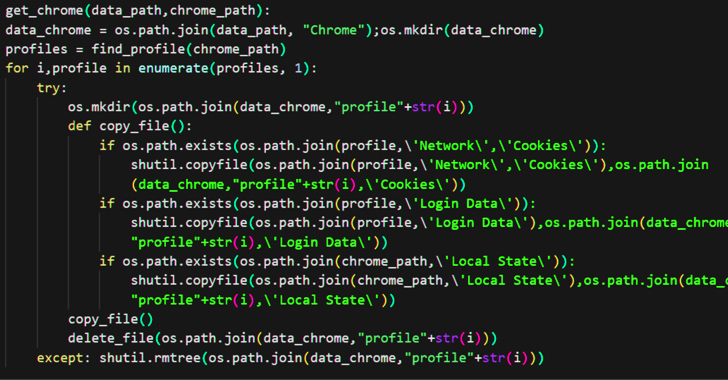
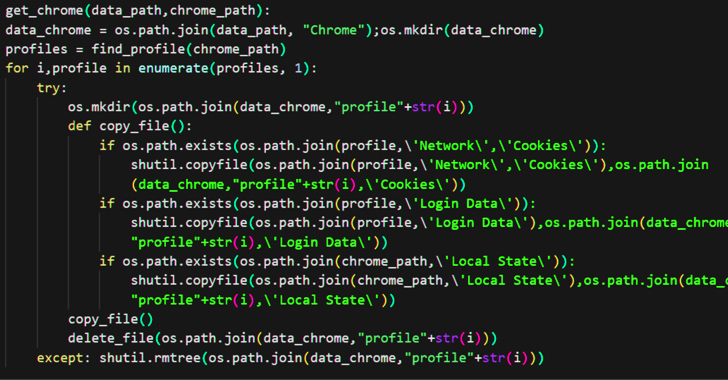
2.0KMalwareNodeStealer Malware Now Targets Facebook Business Accounts on Multiple Browsers
An ongoing campaign is targeting Facebook Business accounts with bogus messages to harvest victims’ credentials using a variant of the Python-based NodeStealer...
-
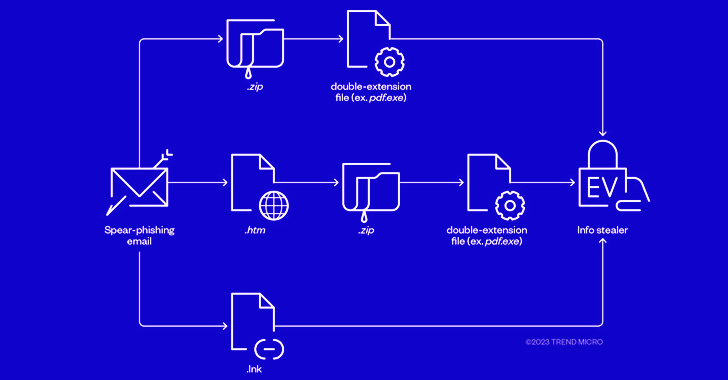
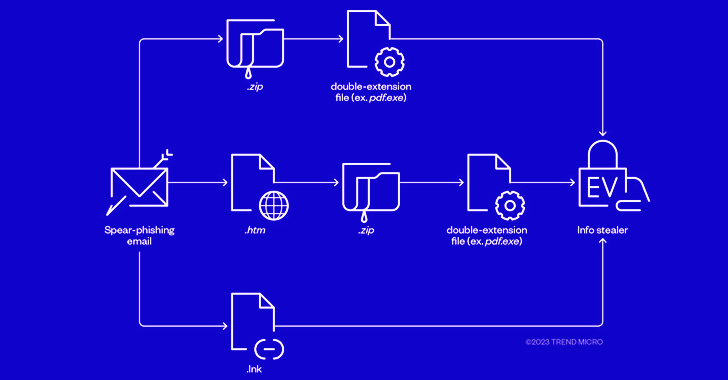 1.1KCyber Attack
1.1KCyber AttackCybercriminals Combine Phishing and EV Certificates to Deliver Ransomware Payloads
The threat actors behind RedLine and Vidar information stealers have been observed pivoting to ransomware through phishing campaigns that spread initial payloads...
-
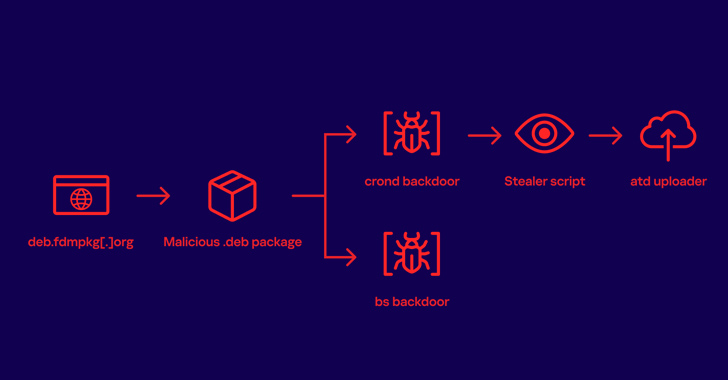
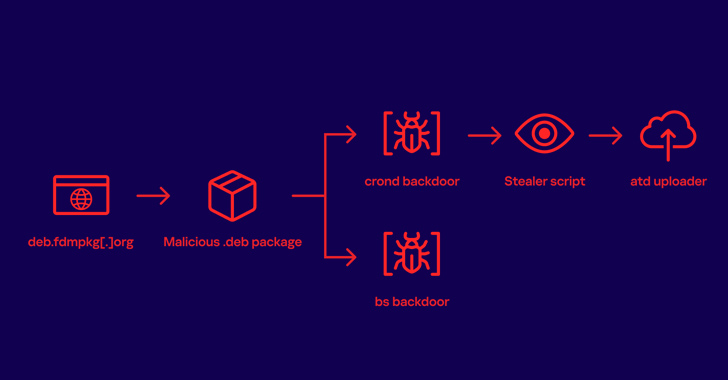 1.3KMalware
1.3KMalwareFree Download Manager Site Compromised to Distribute Linux Malware to Users for 3+ Years
A download manager site served Linux users malware that stealthily stole passwords and other sensitive information for more than three years as...
-

 4.1KMalware
4.1KMalwareRust-Written 3AM Ransomware: A Sneak Peek into a New Malware Family
A new ransomware family called 3AM has emerged in the wild after it was detected in a single incident in which an...
-

 2.9KMalware
2.9KMalwareHow Cyberattacks Are Transforming Warfare
There is a new battlefield. It is global and challenging to defend. What began with a high-profile incident back in 2007, when...
-
 5.1KMalware
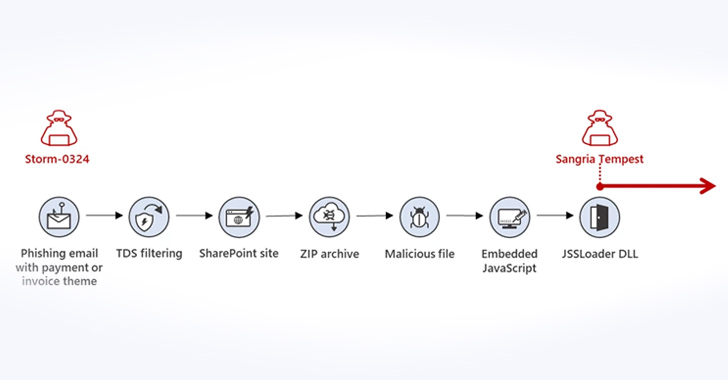
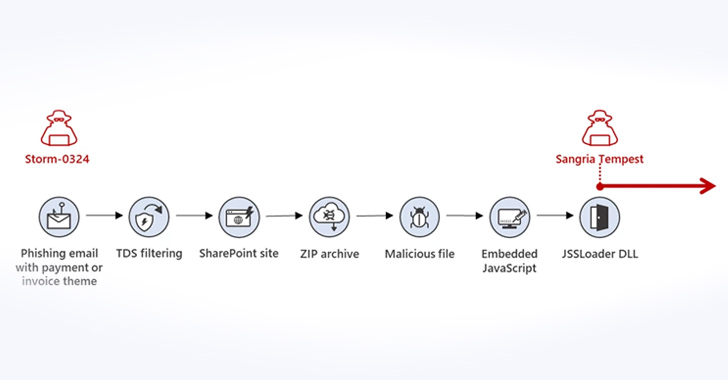
5.1KMalwareMicrosoft Warns of New Phishing Campaign Targeting Corporations via Teams Messages
Microsoft is warning of a new phishing campaign undertaken by an initial access broker that involves using Teams messages as lures to...
-
 3.3KMalware
3.3KMalwareSophisticated Phishing Campaign Deploying Agent Tesla, OriginBotnet, and RedLine Clipper
A sophisticated phishing campaign is using a Microsoft Word document lure to distribute a trifecta of threats, namely Agent Tesla, OriginBotnet, and...






