All posts tagged "malware"
-

 367Data Security
367Data SecurityMalware can Convert your Headphones into Microphone for Hackers
We know that our computer or laptop’s webcam is quite vulnerable to hacking and usually hiding their webcam’s lens with a piece...
-

 277Cyber Crime
277Cyber CrimeThe First Ransomware to Exploit Telegram Cracked and Decryptor Published
A security researcher whose name is Nathan Scott managed to break the encryption model employed by the Telecrypt ransomware. The unusual characteristic that made this virus to stand out was the server-client connection method. This...
-

 217Hacked
217HackedFeel “Safe”, Your Headphones Can Be Used As A Microphone To Spy On You
Short Bytes: Researchers at the Ben Gurion University, Israel, have created a malware, called Speake(a)r, to exploit a feature on Realtek codec chips....
-

 70Data Security
70Data Security[ TECHNICAL TEARDOWN: EXPLOIT & MALWARE IN .HWP FILES ]
This article will focus on teaching analysts on analysing malicious JavaScript code within the HWP files and a walkthrough of how we...
-
 348Cyber Crime
348Cyber CrimeScammers Using Images on Facebook Messenger to Drop Locky Ransomware
Facebook Messenger has become a favorite target of cyber-criminals lately since the social network’s messenger service is continuously being targeted with malware...
-
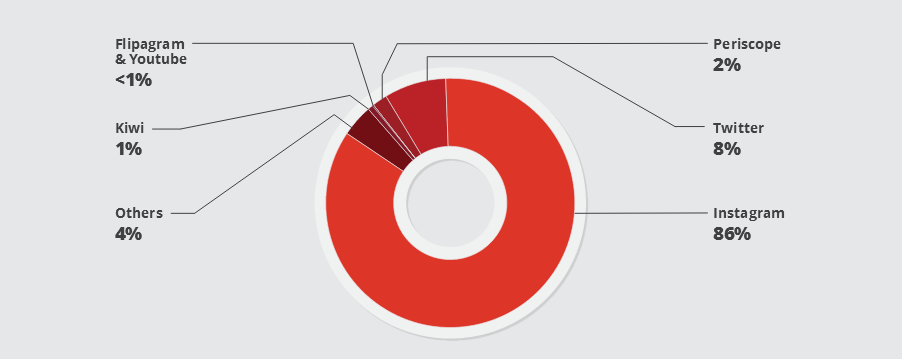
 92Data Security
92Data SecurityA Botnet of IoT Devices Is Behind Many Instagram Fake Profiles
A botnet of IoT (Internet of Things) devices created with the Linux/Moose malware is behind many bots that are plaguing social networks...
-

 160Incidents
160IncidentsOffice Depot caught claiming out-of-box PCs showed “symptoms of malware”
News investigations show office supply chain sold unneeded fixes for $180. Office Depot and its sister retailer OfficeMax have stopped using a...
-
 95Data Security
95Data SecurityAsk Toolbar Update Feature Hacked to Drop Malware
The infamous Ask Toolbar is back in the news again. In the past, it received backlash from security firms for pushing third-party...
-

 90Data Security
90Data SecurityMalware attack starts with a fake ccall
The hackers call hotels, then send email attachments that look like customer information Hotel and restaurant chains, beware. A notorious cybercriminal gang...
-
 108Malware
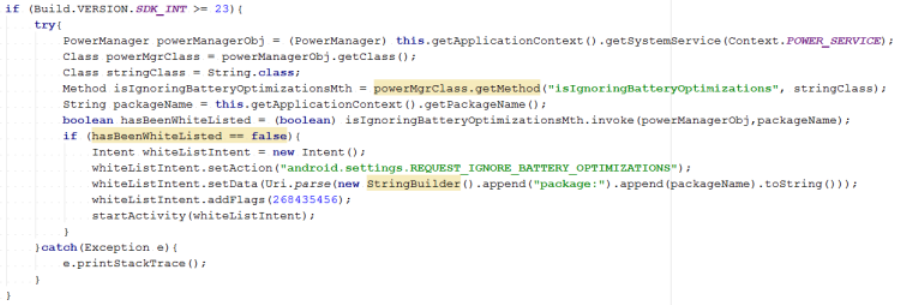
108MalwareAndroid banking malware whitelists itself to stay connected with attackers
New Android.Fakebank.B variants use social engineering to bypass a battery-saving process and stay active in the background. Recent variants of Android.Fakebank.B have...
-
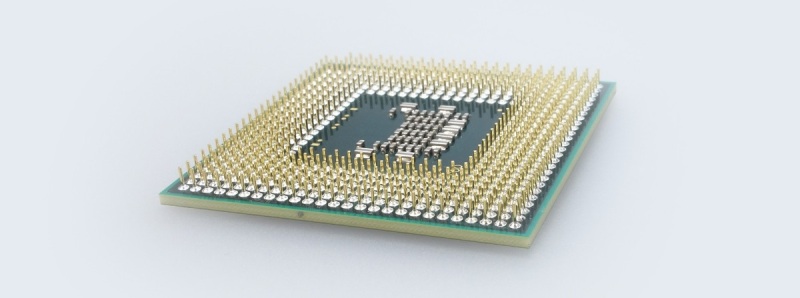
 187Data Security
187Data SecurityScientists Working on a CPU That Can Detect Malware at the Hardware Level
Researchers are working on a new CPU chip design that will extend the fight against malware at the hardware level in an...
-

 156Data Security
156Data SecurityFBI operated 23 Tor-hidden child porn sites, deployed malware from them
Researcher: FBI was likely enabled to run half of all child porn sites on the servers. As Ars has reported, federal investigators temporarily...
-
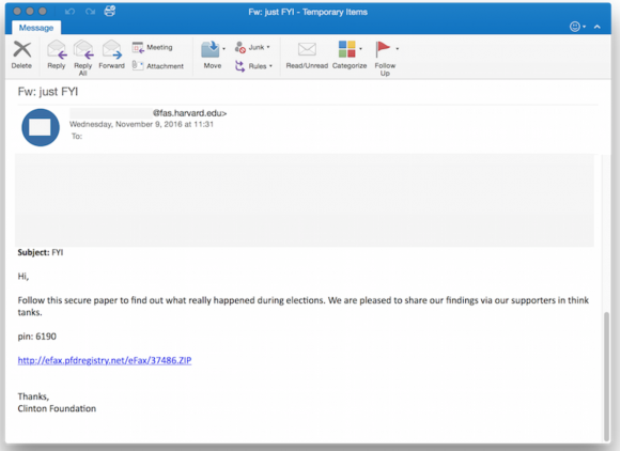
 82Data Security
82Data SecurityRussian ‘Dukes’ of Hackers Pounce on Trump Win
Less than six hours after Donald Trump became the presumptive president-elect of the United States, a Russian hacker gang perhaps best known...
-

 191Incidents
191IncidentsUnsealed Court Docs Show FBI Used Malware Like ‘A Grenade’
In 2013, the FBI received permission to hack over 300 specific users of dark web email service TorMail. But now, after the...
-

 313Malware
313MalwareAVG Wants Your Home Router to Fight Internet of Things Malware
The internet of things is totally broken. Amateur hackers have managed to build huge botnets of compromised devices, and many of these...
-
 73Malware
73MalwareFake Cain XPii Cleaner App Is Actually a Backdoor with Very Annoying Features
If you ask any malware analyst these days, they’ll tell you they come across countless of useless or unfinished malware variants on...
-

 80Vulnerabilities
80VulnerabilitiesBugging devices found at Iran nuclear talks hotel, say Swiss officials
A number of computers at a five-star Geneva hotel that has hosted sensitive talks, including Iranian nuclear negotiations, were found to be...
-
 186Data Security
186Data SecurityMajor Ransomware Attack Shuts Down Entire National Health Service System
National Health Service in the United Kingdom targeted by ransomware attack forcing the service to delay organ transplants. Cyber-criminals are hell bent on exploiting...
-
 90Data Security
90Data SecurityComputer Virus Cripples UK Hospital System
Citing a computer virus outbreak, a hospital system in the United Kingdom has canceled all planned operations and diverted major trauma cases...
-

 191Malware
191MalwarePHONY ANDROID FLASH PLAYER INSTALLS BANKING MALWARE
Security researchers warn that a bogus Flash Player app aimed at Android mobile devices has surfaced and is luring victims to download and install...
-

 191Data Security
191Data SecurityRansomware Disguised as Windows Update Causing Havoc among Users
After Samba ransomware that encrypts victims’ hard drives and CryPy ransomware known for encrypting each file individually here comes Fantom, a ransomware...






