All posts tagged "malware"
-

 298Data Security
298Data SecurityNew Adobe Flash 0-Day Using Dailymotion.com In Malvertising Campaign
Adobe Flash Player has again seen a zero-day exploit that has appeared in the field due to a critical vulnerability that enables...
-
 188Geek
188GeekBeware: Porn-based malware Infects 110K Facebook Users
Facebook appears to be infected with a porn-based malware that has affected about 110,000 Facebook users in just two days. The malware,...
-

 148Data Security
148Data Security#JeSuisCharlie Being Used by Hackers To Spread Malware
This news bit strengthens the presumption that hackers can make use of just about anything to fulfill their malicious motives. After the...
-

 221Data Security
221Data SecurityFake BBC Website lures victims with Charlie Hebdo misinformation
A website mimicking the official BBC News site has garnered immense traffic earlier this week through false information about Charley Hebdo massacre...
-

 258News
258NewsSouth Korean nuclear operator hacked, personal data, blueprints leaked
Unknown hackers have hacked the computer systems of South Korea’s nuclear plant operator and leaked noncritical data claim the officials. The targeted institution was Korea...
-
 373Data Security
373Data SecurityMost Sophisticated Malware Campaign Targeting Diplomats, iPhones, Android, and PC.
Researchers from Blue Cat Labs are calling it the Inception attack framework, in reference to the movie “Inception” where a thief entered...
-

 210Data Security
210Data SecurityWarning: Beware of Malware Planted In Chinese E-Cigarettes.
Electronic cigarette manufacturers may have highlighted its numerous benefits to letting you lead a healthy, stress-free life, what they certainly did not...
-

 233Data Security
233Data SecurityWireLurker: Apple Malware Infecting Mac and iPhone via USB
Apple is usually known for its top notch security but a US-based cyber security software developer Palo Alto Networks discovered a new...
-

 283News
283NewsRussian Hackers Allegedly Hacked White House Computers
Unclassified White House computers are latest in the list of security breaches this year and the prime suspects for the breach are...
-
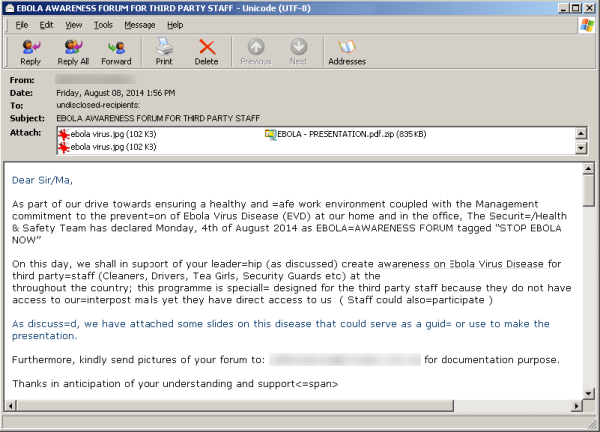
 388News
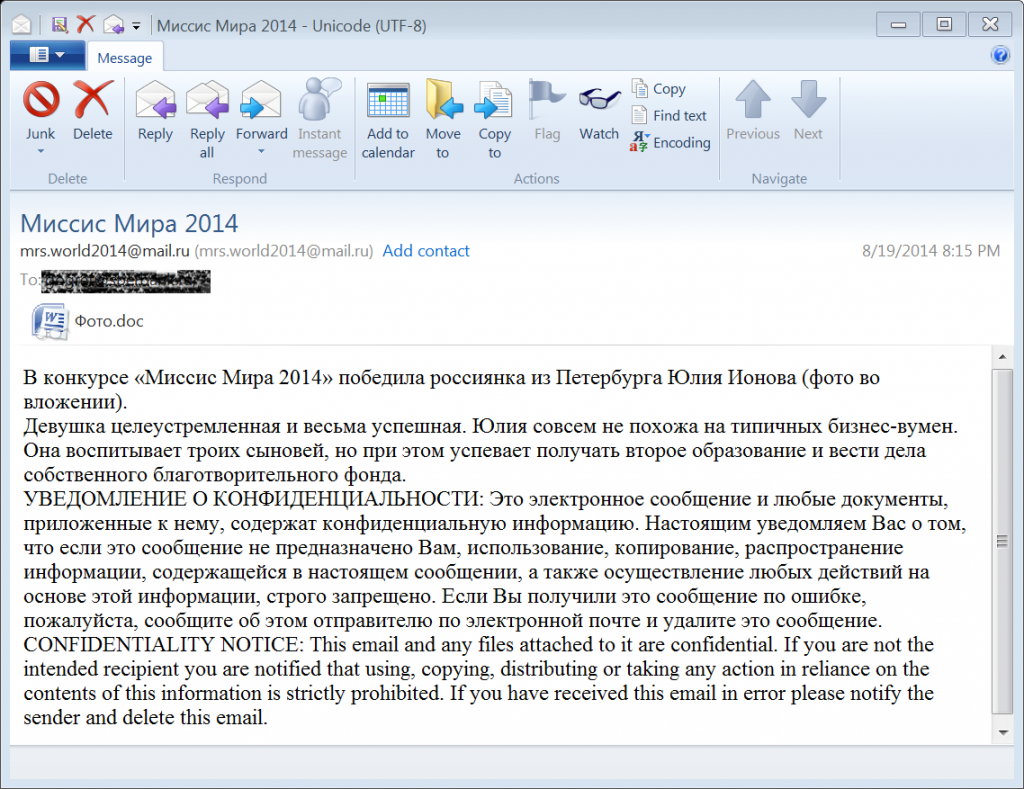
388NewsHackers Sending Fake Ebola Virus reports in emails with Malware and Phishing Links
A new malicious campaign has been identified by security researchers spreading fake news about the Ebola virus, in order to redirect users...
-

 198News
198NewsBadUSB exploit hacks your computer
A common shortcoming that most of the USB devices possess is one which can be noiselessly made use of to introduce infection...
-

 340Data Security
340Data SecurityDangerous Malware steals credit card information from Android devices
Security experts at Dr. Web have warned Android users to be careful with a new Trojan that is stealing credit card details while...
-

 239Data Security
239Data SecurityAndroid Trojan Virus: iBanking Malware ‘Qadars’ Targets Facebook Users via Webinjects
Cyber criminals have targeted millions of Facebook users through a sophisticated Android Trojan app that can bypass the two-factor authentication shield used...
-

 327Surveillance
327SurveillanceGoogle admits it’s reading your emails, tells court Gmail users should not expect privacy
Google’s latest update on Monday only highlights how apathetic they are to the privacy of their users and consider every bit of...
-

 201Data Security
201Data SecuritySpammers using “No War on Syria” petitions to steal personal information
Spammers are taking advantage of the various online petitions against the recent news about the alleged arming of the Syrian rebels by...
-
 304Data Security
304Data SecurityHackers Target Monster Jobs Website with Gameover Zeus malware
A security firm has revealed that hackers are targeting companies utilizing services of Monster Jobs, a well-known job portal, through a new...
-

 188Data Security
188Data SecuritySMS Fake Installer tricking Android Users
Nathan Collier of Webroot ThreatVlog, talks about an old, but still active, SMS Fake Installer, a Russian based program used to trick...
-

 402Geek
402GeekZeus Trojan returns: Targets Facebook, Instagram, Twitter, YouTube and LinkedIn
During recent times, social media has by some distance defeated ordinary ways of trading. This has indeed directed many people towards social...
-

 226Data Security
226Data SecurityHighly Sophisticated Backdoor.AndroidOS Trojan Nearly Impossible to Remove
The “sophisticated” malware for Android has been “unleashed”. Identified by the company specializes in cyber security Kaspersky, the Trojan “Backdoor.AndroidOS.Obad.a” is a threat virtually impossible to be...
-

 293Data Security
293Data SecurityPhishing Attack that Replaces Android Banking Apps With Malware
Mobile phones are now also being utilized for the purpose of managing some important personal assets such as money. According to a...
-
 217Data Security
217Data SecurityWEBSENSE: Most of Java Enabled Browsers are Vulnerable to Java Exploits Which Have Been Spreading on a Vast Scale
MAJORITY OF THE JAVA ENABLED BROWSERS ARE ASSAILABLE TO JAVA EXPLOITS WHICH HAVE BEEN SPREAD ON A VAST SCALE: SAYS WEBSENSE Majority...






