All posts tagged "malware"
-

 297Data Security
297Data SecurityHackers Develop Android Malware Every 17 Seconds
By the first quarter of 2015, hacker/cyber-attackers have optimized their efforts to design Android Malware to such an extent that every seventeen...
-
 226Data Security
226Data SecurityDino Malware exposed: Found Spying on Iran and Syria
Links traced to “Animal Farm” group and State Sponsored cyber criminals who already have targeted Syrian and Iranian computers in 2013. Bratislava,...
-

 244Hacked
244HackedOne of the Best Anti-Virus Malwarebytes Offers Free 1-Year Premium Keys
“The Internet is full of pioneers and cowboys. It’s also got its fair share of pirates and trolls.” Piracy is the biggest...
-

 269Data Security
269Data SecurityFacebook Join Forces with Kaspersky to Spot Malware on Computers
The problem with Facebook is thousands of active phishing scams but the social media giant has partnered with popular security software developer firm...
-
 319Data Security
319Data SecurityHackers Used ‘Stolen Foxconn certs’ to Hack Kaspersky Via Duqu 2.0 Malware
‘Stolen Foxconn certs’ used for embedding Duqu 2.0 malware into Windows PC — The crafty super-sophisticated malware infiltrated Kaspersky Labs. Reportedly, Duqu...
-
 178Data Security
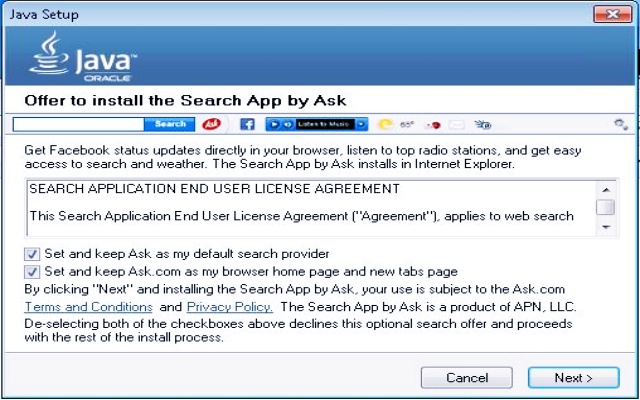
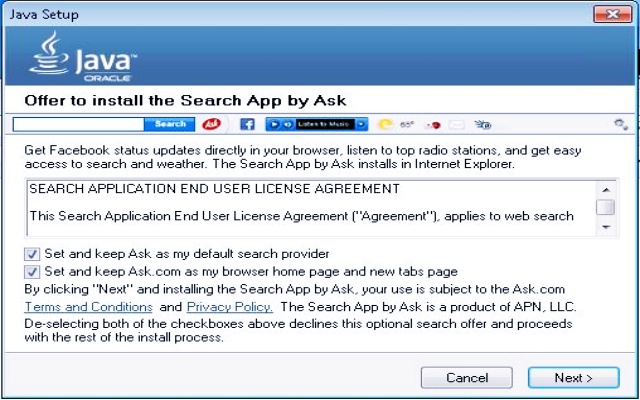
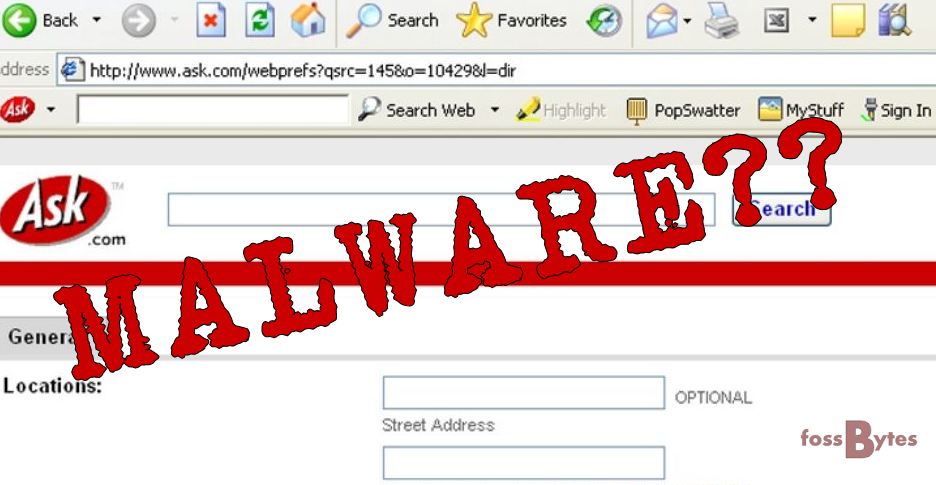
178Data SecurityMicrosoft Declares Ask toolbar as Dangerous Malware
In April 2015, we reported how Ask.com toolbar is working as a malware to hijack your computer. Now proving our claim right, previous...
-
 222Hacked
222HackedAsk Toolbar in Your Browser is a Malware: Microsoft
The vintage Ask toolbar that you can spot in your computer’s web browser has now been termed as threat to your PC...
-

 286Data Security
286Data SecurityHacker Targets Pedophiles with TOX Ransomware
Tox is yet another example of cyber justice that has been meted out by cyber criminals. In this case, Tox sends a...
-

 239Data Security
239Data SecurityApps will Automatically Detect Malware in Windows 10
Software developers will have the opportunity to integrate their application to any antimalrware program (available on their computer) in windows 10. Microsoft...
-

 134Data Security
134Data SecurityFacebook Users Left Red-Faced After Porn Malware Attack
Hackers spammed Facebook timelines and newsfeeds with malicious malware that spread pornographic videos and images. The attack left hundreds of social media...
-

 317News
317NewsHackers Hiding Vawtrak Banking Malware Command Servers in Tor
Some versions of Vawtrak banking Malware or Neverquest have been discovered to be having hidden command and control servers at Tor anonymity...
-

 253Surveillance
253SurveillanceCanada’s New Anti-Terror Bill C-51 will Ruin Internet Privacy
Canada approves anti-terror law C-51 that weakens Internet privacy – NDP-Liberal coalition may get triggered as a result warn conservative critics. At...
-

 229Data Security
229Data SecurityFacebook Users Hit with Malware Disguised as Google Chrome Video Installer
Trend Micro researchers have identified a new scheme in which scammers have used Facebook again to distribute malware. This malware has been...
-

 186Data Security
186Data Security“Failure in Parcel Delivery” Fake Email Drops Malware on USPS Customers’ PC
Please note that the email that appears to be sent by USPS informing that due to incorrect address the firm has failed...
-

 288Cyber Crime
288Cyber CrimeRansomware attack forces animal porn collector to plead guilty to police
A UK man has been charged this week with a non-custodial sentence, after a ransomware infection on his computer made him confess...
-
 238Data Security
238Data SecurityWhatsApp users hit with ‘You Just Got an Audio Recording’ Email Malware
The email apparently is sent from the popular messaging service WhatsApp and claims that you have received an audio recording. A malicious...
-
 293Data Security
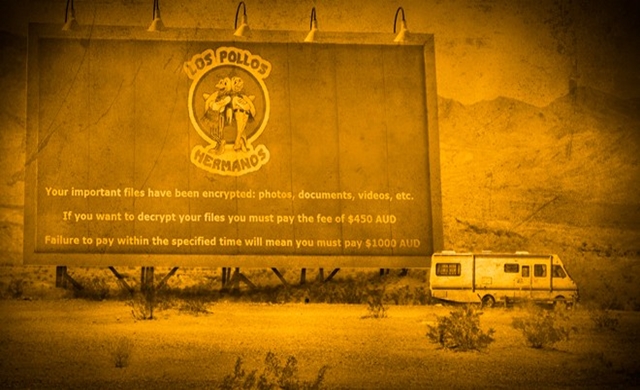
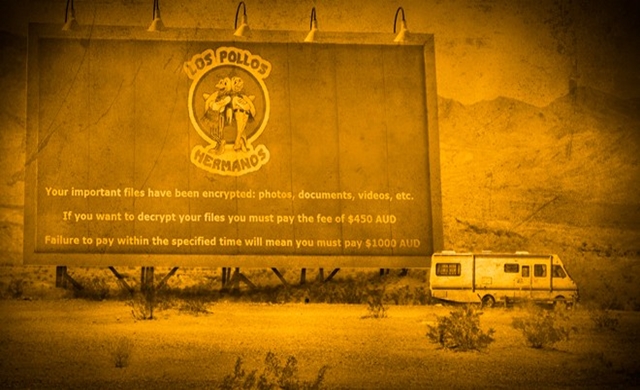
293Data SecurityInternet users hit with Breaking Bad Theme Crypto-Malware
To demonstrate their creativity cybercriminals have released a new ransomware equipped with file encryption abilities and this time they have chosen logo...
-

 223Data Security
223Data SecurityAnonymous team hides malware in Nvidia GPUs, can harm Mac, Linux, Windows
Summary: In a bid to raise awareness regarding the way malware can affect GPUs, a team of developers recently created a Linux...
-
 203Data Security
203Data SecuritySeemingly Legit Resume actually contains Crypto-Malware
The malicious email, targeted at a company’s resume screening department, is equipped with file encryption capabilities. A new ransomware having capabilities of...
-

 271Data Security
271Data SecurityLenovo accused of ‘massive security risk’ by researchers
The IOActive researchers reported that Lenovo devices software has serious security flaws and vulnerabilities that can be easily exploited by cyber criminals...
-
 133Hacked
133HackedGoogle Says Ad Injecting Malware Affecting Millions of Users
Google’s recent study shows the effect of the Ad Injection in our digital media. We already know and hate the ad frauds,...






